When your enterprise runs separate Alibaba Cloud accounts for different teams, projects, or environments, purchasing an Anti-DDoS Origin instance for each account is costly and operationally fragmented. Multi-account management lets you buy one Anti-DDoS Origin instance and use it to protect assets across all member accounts in your organization—consolidating protection under a single console with no extra charge for subscription instances.
Multi-account management requires approval. Contact your business manager before proceeding.
When to use this feature
Consider multi-account management if your organization:
Runs separate Alibaba Cloud accounts per team, environment (dev/staging/prod), or business unit and wants centralized DDoS protection
Wants to reduce costs by covering all accounts with one subscription instance instead of purchasing separate instances
Needs a unified view of attack events, mitigation logs, and protection settings across accounts
If your organization uses a single Alibaba Cloud account or each account independently manages its own protection, this feature is not needed.
Supported instance types
Anti-DDoS Origin 2.0 Enterprise (Subscription)
Anti-DDoS Origin 2.0 (Pay-as-you-go)
How it works
Multi-account management uses Alibaba Cloud Resource Directory to organize accounts into three roles:
| Account type | Role |
|---|---|
| Management account | Enables and administers the resource directory. Has full control over the directory, folders, and members. |
| Delegated administrator account | Designated by the management account. Handles day-to-day protection tasks and can access organization and member account information. |
| Member account | An account whose assets are protected by the management or delegated administrator account's instance. Can be a new account or an existing Alibaba Cloud account invited to join. |
Use the management account for organization structure tasks and the delegated administrator account for protection management. This separation improves operational flexibility.
A member account can be associated with either the management account or the delegated administrator account—not both. Each association grants the managing account's instance access to that member account's assets.
Billing
Subscription instance (Anti-DDoS Origin 2.0 Enterprise): Protecting member account assets costs nothing extra—one subscription covers the entire organization.
Pay-as-you-go instance: Fees from protecting member account assets are charged to the account that owns the instance, not to the member accounts.
To minimize costs, subscribe with a single account and use multi-account management to extend coverage across your organization.
Limits
All accounts must belong to the same resource directory and have the same enterprise identity verification.
Each management or delegated administrator account can add a maximum of 50 member accounts.
A member account can be associated with either the management account or the delegated administrator account—not both.
Member accounts can also purchase their own Anti-DDoS Origin instances. However, an asset that is assigned a public IP address can be protected by only one Anti-DDoS Origin instance at a time. Remove an asset from its current instance before adding it to the organization-level instance.
Disassociating a member account in the Traffic Security console automatically removes protection from all of that member account's assets.
Console visibility
When a delegated administrator or management account protects a member account's assets, the visibility of data in the Traffic Security console varies by page:
| Console page | Management/Delegated administrator account | Member account |
|---|---|---|
| Overview | Not supported | Supported |
| Asset Center | Not supported | Supported |
| Event Center | Not supported | Not supported |
| Statistical Report | Supported | Not supported |
| Business Monitoring | Supported | Not supported |
| Protected Object | Supported | Not supported |
| Mitigation Settings | Supported | Not supported |
| Attack Analysis | Supported | Not supported |
| Mitigation Logs | Supported | Not supported |
| Operation Logs | Supported | Not supported |
| CloudMonitor Alerts | Supported | Not supported |
| Billing Center | Supported | Not supported |
Set up multi-account protection
The following steps use the delegated administrator account for protection management. If you do not configure a delegated administrator account, use the management account to perform all steps.
Prerequisites
Before you begin, make sure that you have:
A management account with Resource Directory enabled, or permission to enable it
At least one member account to add to the directory
Approval to use the multi-account management feature (contact your business manager if not yet approved)
Step 1: Enable a resource directory and build an organizational structure
Add your enterprise's Alibaba Cloud accounts to a resource directory.
Log on to the Resource Management consoleResource Management consoleResource Management console with your management account and enable a resource directory. For more information, see Enable a resource directory.
Build your organization's account structure. Create new member accounts or invite existing Alibaba Cloud accounts to join. For more information, see Create a folder, Create a member, and Invite an Alibaba Cloud account to join a resource directory.
Designate a member account as the delegated administrator account. For more information, see Manage a delegated administrator account.
Step 2: Associate member accounts with the delegated administrator account
Associate member accounts so the delegated administrator account's instance can protect their assets.
A member account can be associated with either the management account or the delegated administrator account—not both. Plan your account associations before proceeding.
Log on to the Traffic Security consoleTraffic Security consoleTraffic Security console with the delegated administrator account.
In the left-side navigation pane, choose Network Security > Anti-DDoS Origin > Multi-account Management.
Click Add Member. Read the information in the dialog box, then click Next.
ImportantAfter you add a member account, the delegated administrator account is authorized to access the assets of that member account.
Select the member accounts to add, click the
 icon, then click OK.
icon, then click OK.
Step 3: Add member account assets as protected objects
Add the member account's assets to the protected objects of the delegated administrator account's instance.
New EIPs with Anti-DDoS (Enhanced) that belong to a member account are automatically added to the protected objects of the delegated administrator account. If a member account already has its own pay-as-you-go instance with existing EIPs with Anti-DDoS (Enhanced), those EIPs remain protected by the member account's own instance. To migrate their protection to the delegated administrator account: 1. Release the EIP with Anti-DDoS (Enhanced). 2. Disable the pay-as-you-go instance of the member account. 3. Purchase a new EIP with Anti-DDoS (Enhanced) for the member account. It is automatically added to the delegated administrator account's protected objects.
Log on to the Traffic Security consoleTraffic Security consoleTraffic Security console with the delegated administrator account.
In the left-side navigation pane, choose Network Security > Anti-DDoS Origin > Protected Objects.
Select the target Anti-DDoS Origin instance, click Add Object for Protection, then click the Add Assets of Members tab.
Step 4: Configure mitigation policies for member account assets
After adding member account assets as protected objects, the Mitigation Policy defaults to Default, which applies Anti-DDoS Origin's standard mitigation capabilities.
To allow or block traffic with specific characteristics, attach a custom scenario-specific template to the assets. Log on to the Traffic Security console with the delegated administrator account and follow the instructions in Mitigation Settings.
Step 5: View attack events on member account assets
Log on to the Traffic Security consoleTraffic Security consoleTraffic Security console with the delegated administrator account.
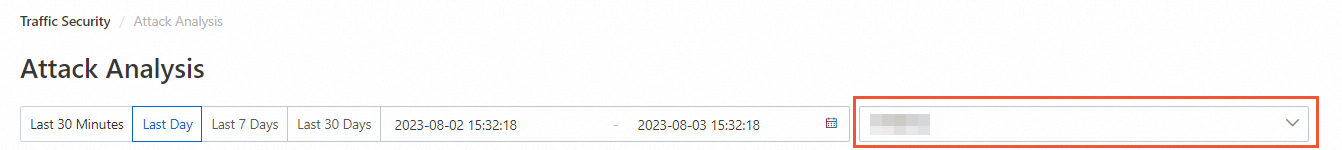
In the left-side navigation pane, choose Network Security > Anti-DDoS Origin > Attack Analysis.
On the Attack Analysis page, select an account scope:
All accounts: Shows assets from the management account and all associated member accounts that are assigned public IP addresses.
Delegated administrator account: Shows only assets in this account.
Member account: Shows only assets in the selected member account.
What's next
To adjust protection settings for member account assets, see Mitigation Settings.
To learn more about Resource Directory, see What is Resource Directory?.