Disk encryption protects data stored on AnalyticDB for MySQL cluster disks using Elastic Block Storage (EBS). If a disk is compromised, the data remains inaccessible without the encryption key.
Disk encryption must be enabled at cluster creation. It cannot be enabled for an existing cluster or disabled after it is enabled.
What gets encrypted
When disk encryption is enabled, the following data is encrypted:
Hot data of Enterprise Edition, Basic Edition, Data Lakehouse Edition, and Data Warehouse Edition in elastic mode
All data of Data Warehouse Edition in reserved mode
Data transmitted between disks and clusters
All snapshots created from the encrypted disk
Cold data is stored outside of disks and is not encrypted.
Constraints
| Constraint | Details |
|---|---|
| Enablement timing | Must be enabled at cluster creation; cannot be added to an existing cluster |
| Disablement | Cannot be disabled after enabled |
| Performance impact | Read and write performance is reduced by approximately 10% |
| Application changes | None required |
| Snapshot inheritance | For reserved-mode clusters, snapshots and clusters created from those snapshots inherit disk encryption |
| Supported KMS keys | Manually created keys only; Rotation Period must be set to Disabled |
Billing
AnalyticDB for MySQL云盘加密功能开启后,您在磁盘上的任何读写操作都不会产生额外费用。
Disk encryption requires Key Management Service (KMS). Charges apply for key management and API calls. For pricing details, see Billing of KMS.
Enable disk encryption
Enable disk encryption on the buy page when creating a cluster. To enable disk encryption for an existing cluster, create a new cluster with disk encryption enabled and migrate your data to it.
Prerequisites
Before you begin, ensure that you have:
A KMS customer master key (CMK) created manually with Rotation Period set to Disabled
If no keys exist in your account, create one first. For instructions, see Create a CMK.
Steps
On the buy page, select Disk Encryption.
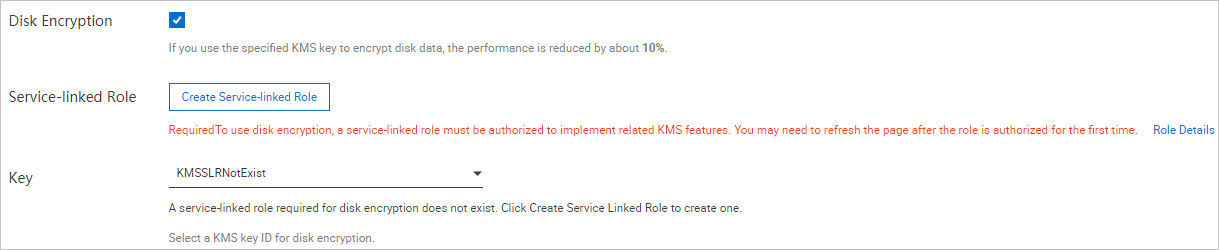
If this is the first time you are enabling disk encryption, click Create Service-linked Role.
This step is required only once. If Created is displayed, a service-linked role already exists and you can skip this step. The service-linked role allows AnalyticDB for MySQL to use KMS features. For details, see Manage the service-linked role for disk encryption.
From the Key drop-down list, select a key.
After KMS authorization, ActionTrail records all operations performed on KMS resources. For details, see Use ActionTrail to query KMS event logs.
Complete the remaining cluster creation steps. For details, see Create a cluster.
Verify that disk encryption is enabled
Log on to the AnalyticDB for MySQL console. In the upper-left corner, select a region. In the left-side navigation pane, click Clusters. On the Clusters page, click an edition tab, find the cluster, and click its cluster ID.
In the left-side navigation pane, choose Cluster Management > Cluster Information or click Cluster Information.
In the Configuration Information section, check whether KMS Key ID for Disk Encryption is displayed.
If KMS Key ID for Disk Encryption is not displayed, disk encryption is not enabled for the cluster.