Alibaba Cloud DNS PrivateZone maps private domain names in one or more virtual private clouds (VPCs) to IP addresses, blocking access from outside those VPCs. ACK Serverless integrates with PrivateZone to give each Service in your cluster a stable DNS name — no IP tracking required.
PrivateZone-based service discovery supports three Service types: intranet Services, headless Services, and ClusterIP Services.
If you prefer a CoreDNS-based approach, see How DNS resolution works in ACK Serverless clusters.
Prerequisites
Before you begin, ensure that you have:
Alibaba Cloud DNS PrivateZone activated in the Alibaba Cloud DNS console
NotePrivateZone is not available in the UAE (Dubai) region.
An ACK Serverless cluster created with the PrivateZone component enabled. Use one of the following methods:
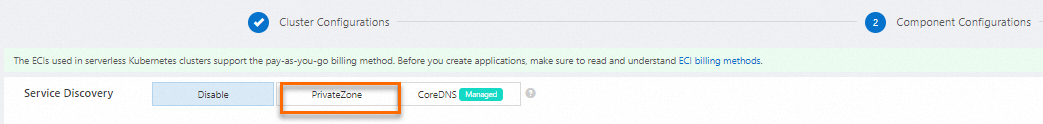
New cluster: Select PrivateZone for the Service Discovery parameter when creating the cluster.
Existing cluster: Set the
enablePrivateZoneparameter in theeci-profileConfigMap totrue.
A kubectl client connected to the cluster
Billing
For PrivateZone pricing details, see Pricing.
How it works
PrivateZone creates DNS records in the $svc.$ns format. Each Service type maps to a different DNS record structure:
| Service type | Number of records | Resolves to |
|---|---|---|
| LoadBalancer (intranet) | 1 | IP address of the SLB instance |
| ClusterIP | 1 | Cluster IP address |
| Headless | Multiple | IP addresses of all backend pods |
Once records are created, pods in the VPC can reach any Service using its private domain name.
Domain name formats:
| Format | Scope | Example |
|---|---|---|
$svc | Same namespace | nginx |
$svc.$ns | Different namespace | nginx.prod |
$svc.$ns.svc.cluster.local.$clusterId | Current cluster (full name); also works for cross-cluster access | nginx.prod.svc.cluster.local.c1a2b3 |
Enable service discovery with PrivateZone
Step 1: Deploy a Deployment and create Services
Save the following YAML to nginx-service.yaml, then run kubectl create -f nginx-service.yaml.
apiVersion: v1
kind: Service
metadata:
name: nginx-headless-service
spec:
ports:
- port: 80
protocol: TCP
selector:
app: nginx
clusterIP: None
---
apiVersion: v1
kind: Service
metadata:
name: nginx-clusterip-service
spec:
ports:
- port: 80
protocol: TCP
selector:
app: nginx
type: ClusterIP
---
apiVersion: v1
kind: Service
metadata:
name: nginx-intranet-service
annotations:
service.beta.kubernetes.io/alicloud-loadbalancer-address-type: intranet
spec:
ports:
- port: 80
protocol: TCP
selector:
app: nginx
type: LoadBalancer
---
apiVersion: apps/v1
kind: Deployment
metadata:
name: nginx-deployment
labels:
app: nginx
spec:
replicas: 3
selector:
matchLabels:
app: nginx
template:
metadata:
labels:
app: nginx
spec:
containers:
- name: nginx
image: nginx:alpine
ports:
- containerPort: 80Step 2: Verify the resources are running
kubectl get svc,pod,deploymentConfirm that all three Services and the Deployment pods appear with the expected status before proceeding.
Step 3: View PrivateZone records in the console
Log on to the Alibaba Cloud DNS console.
In the left-side navigation pane, click Private DNS (PrivateZone).
In the upper-right part of the page, click Configuration Mode.
Click the Built-in Authoritative Module tab, then click User Defined Zones.
In the Actions column for the domain you want to inspect, click Resource Records Settings.
The console shows the DNS records that PrivateZone created for your Services. Verify that each Service has the correct number of entries and target IP addresses based on the table in How it works.
What's next
For additional examples and advanced configurations, see serverless-k8s-examples.