MSE Ingress gateways provide Layer 7 load balancing for managing external access to Services in a Kubernetes cluster. Built on deep integration between Microservices Engine (MSE) cloud-native gateways and Container Service for Kubernetes (ACK), MSE Ingress gateways extend standard Kubernetes Ingress with canary releases, service governance, and comprehensive security protection for cloud-native distributed applications.
This topic assumes you are familiar with core Kubernetes concepts, including pods, Services, and Ingress resources.
Prerequisites
Before you begin, make sure you have:
An ACK or ACK Serverless cluster
MSE Ingress controller installed in your cluster (see Manage components)
An MSE cloud-native gateway provisioned via an MseIngressConfig Custom Resource Definition (CRD)
How it works
The diagram below shows the full request flow, from an external client to a backend pod, and how each component fits in.
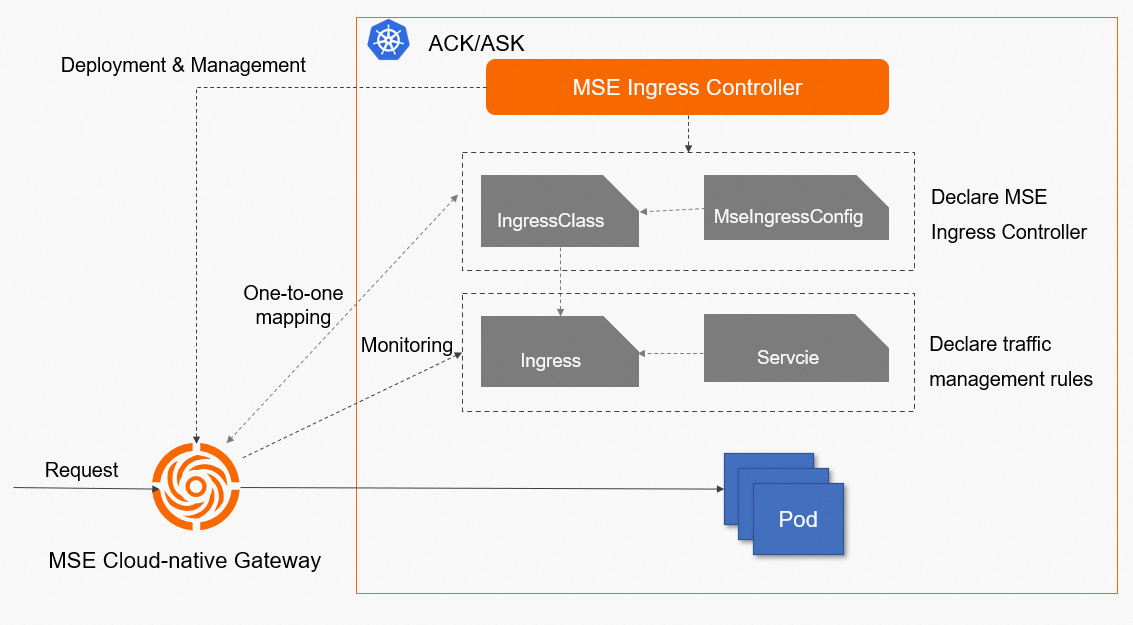
At a high level:
The MSE Ingress controller watches MseIngressConfig CRDs in your ACK cluster and manages the lifecycle of the corresponding MSE cloud-native gateways.
The control plane of each cloud-native gateway monitors Ingress resources, Ingress classes, and Services via the ACK cluster's API server. When Ingress resources change, the control plane pushes updated routing rules to the data plane in real time.
When an external request arrives, the data plane matches the request against the routing rules and forwards it to the pod that corresponds to the backend Service.
Key concepts
| Concept | Description |
|---|---|
| Service | An abstraction of an application deployed across a group of replicated pods. |
| Ingress | A set of reverse proxy rules that specify how HTTP or HTTPS requests are routed to Services — for example, by hostname or URL path. |
| Ingress class | Declares which Ingress processor handles a given Ingress resource. Associate an MseIngressConfig CRD with the IngressClass parameters field to enable MSE-based traffic management. |
| MseIngressConfig | A CRD provided by the MSE Ingress controller. Defines basic configuration for an MSE cloud-native gateway. |
| MSE Ingress controller | The control plane component installed in your ACK cluster. Manages MSE cloud-native gateway configurations. |
| MSE cloud-native gateway | The gateway provisioned from an MseIngressConfig CRD. Consists of a control plane (routing rule management) and a data plane (traffic processing). |
Why use MSE Ingress instead of standard Kubernetes Ingress or NGINX Ingress
Standard Kubernetes Ingress resources only support HTTP routing rules. Advanced features like load balancing algorithms and session affinity require an Ingress controller — such as NGINX Ingress or MSE Ingress — to implement them.
MSE Ingress gateways extend standard Kubernetes Ingress compatibility with additional capabilities that NGINX Ingress does not provide out of the box:
| Capability | Standard Kubernetes Ingress | NGINX Ingress | MSE Ingress |
|---|---|---|---|
| HTTP routing rules | Yes | Yes | Yes |
| Load balancing algorithms | No | Yes | Yes |
| Session affinity | No | Yes | Yes |
| Canary releases | No | — | Yes |
| Service governance (rate limiting, circuit breaking, retries) | No | — | Yes |
| Comprehensive security protection | No | — | Yes |
| NGINX Ingress annotation compatibility | — | — | 50+ annotations, 90%+ of use cases |
If you are migrating from NGINX Ingress, MSE Ingress gateways are compatible with more than 50 NGINX Ingress annotations and cover more than 90% of NGINX Ingress use cases.
MSE Ingress components
MSE Ingress controller
The MSE Ingress controller does not process any service traffic. It only configures MSE cloud-native gateways. All traffic flows through the gateway's data plane, not through the controller.
The MSE Ingress controller is a control plane component — not a network data plane. Install it in your ACK or ACK Serverless cluster. It:
Monitors the resources defined by MseIngressConfig CRDs in an ACK cluster and maintains the lifecycle of the corresponding cloud-native gateways.
Uses MseIngressConfig CRDs to manage cloud-native gateway configurations based on annotations.
Configures Ingress resource monitoring for the gateways.
For installation instructions, see Manage components.
MSE cloud-native gateways
Each MSE cloud-native gateway is created from an MseIngressConfig CRD and consists of two planes:
Control plane: monitors resources such as Ingresses, Ingress classes, and Services in the associated ACK cluster. Sends parsed routing configurations to the data plane in real time.
Data plane: processes external requests based on routing rules from the control plane, and routes each request to the appropriate backend Service pod.