An MseIngressConfig is a CustomResourceDefinition (CRD) provided by MSE Ingress Controller. It controls the full lifecycle of an MSE cloud-native gateway — from creation to deletion — and configures Ingress listening options and gateway-level global settings such as IP access control and observability.
How it works
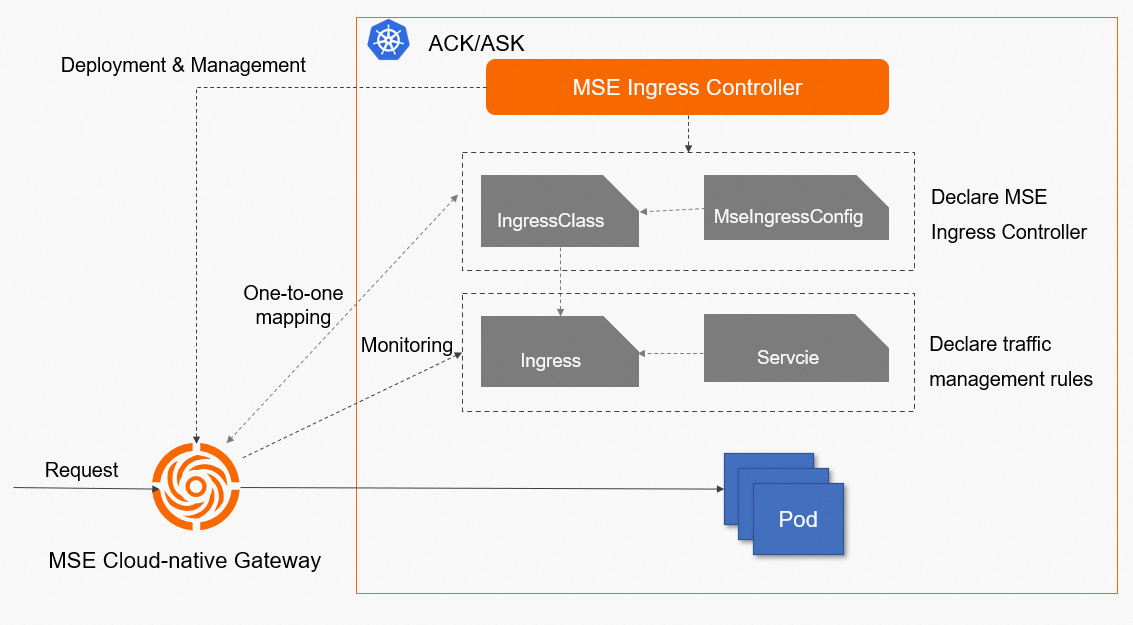
MSE Ingress Controller watches MseIngressConfig resources in your cluster and keeps the associated MSE cloud-native gateway in sync. The cluster can be a Container Service for Kubernetes (ACK) managed cluster, ACK Serverless cluster, or ACS cluster.
Once a cloud-native gateway is linked to the cluster's API server, its control plane receives Ingress resource changes and updates routing rules dynamically. When the gateway receives a request, it matches the request against Ingress routing rules and forwards traffic to the corresponding backend pod.
The following components work together in this setup:
Service: An abstraction over a group of replicated backend pods.
Ingress: Defines reverse proxy rules that route HTTP or HTTPS traffic to services based on hostnames and URL paths.
IngressClass: Declares which Ingress controller handles a set of Ingress resources. Associate an MseIngressConfig with the
parametersfield of an IngressClass to apply MSE routing logic to those Ingress resources.MseIngressConfig: A CRD that defines gateway configuration — specs, network settings, global policies, and observability options.
MSE Ingress Controller: The control plane that manages cloud-native gateways based on MseIngressConfig definitions. It does not handle network data plane traffic directly.
MseIngressConfig reference
Complete configuration
apiVersion: mse.alibabacloud.com/v1alpha1
kind: MseIngressConfig
metadata:
name: test
spec:
name: mse-ingress
common:
pay:
payType: POSTPAY
instance:
spec: 4c8g
replicas: 3
network:
vSwitches:
- "vsw-1"
- "vsw-2"
publicSLBSpec: slb.s2.small
securityGroupType: normal
global:
tls:
enableHardwareAcceleration: true
ipAccessControl:
whitelist:
- 1.1.XX.XX
- 2.2.XX.XX
monitor:
logging:
sls:
reuseProject: "xxx" # Leave blank to use the default project.
tracing:
openTelemetry:
sampleRate: "100"
ingress:
local:
ingressClass: mse
watchNamespace: "" # Leave blank to listen to all namespaces.Parameters
| Parameter | Type | Description | Default |
|---|---|---|---|
name | string | Gateway name. | mse-ingress |
common.pay.payType | string | Billing method. Only POSTPAY (pay-as-you-go) is supported. | POSTPAY |
common.instance.spec | string | Gateway specifications. Valid values: 2c4g, 4c8g, 8c16g, 16c32g. | 4c8g |
common.instance.replicas | integer | Number of gateway replicas. Valid range: 0–30. | 3 |
common.network.vSwitches | []string | Primary and secondary vSwitches. Specify the primary vSwitch first. Accepts 1–2 entries. If not set, the vSwitch of the node running the MSE Ingress Controller pod is used. | None |
common.network.publicSLBSpec | string | Specifications of the Internet-facing Server Load Balancer (SLB) instance. Valid values: slb.s1.small, slb.s2.small, slb.s2.medium, slb.s3.small, slb.s3.medium, slb.s3.large. | slb.s2.small |
common.network.privateSLBSpec | string | Specifications of the internal-facing SLB instance. Same valid values as publicSLBSpec. | slb.s2.small |
common.securityGroupType | string | Security group type. Valid values: enterprise (advanced security group), normal (basic security group). | normal |
global.tls.enableHardwareAcceleration | boolean | Enables Transport Layer Security (TLS) hardware acceleration to improve HTTPS processing performance. | true |
global.ipAccessControl.whitelist | []string | Global IP address whitelist. Only source IP addresses or CIDR blocks in this list can access the gateway. | Not configured |
global.ipAccessControl.blacklist | []string | Global IP address blacklist. Source IP addresses or CIDR blocks in this list are denied access to the gateway. | Not configured |
monitor.logging.sls | object | Enables Simple Log Service (SLS) for access log delivery. Requires granting SLS permissions to MSE Ingress Controller first. | Disabled |
monitor.logging.sls.reuseProject | string | SLS project to deliver access logs to. Leave blank to use the default project; specify an existing project name to use a custom project. | Blank |
monitor.tracing.openTelemetry | object | Enables Managed Service for OpenTelemetry. Cannot be activated together with open source OpenTelemetry. | Disabled |
monitor.tracing.openTelemetry.sampleRate | string | Sampling rate for Managed Service for OpenTelemetry, as a percentage string (e.g., "100"). | "100" |
monitor.tracing.xTrace.sampleRate | string | Sampling rate for xTrace. | "0" |
ingress.local.ingressClass | string | IngressClass resource the gateway listens to. See valid values below. | Not configured (no Ingress resources listened to) |
ingress.local.watchNamespace | string | Namespace whose Ingress resources the gateway listens to. Leave blank to listen to all namespaces; specify a single namespace to restrict scope. | Blank (all namespaces) |
Valid values for `ingress.local.ingressClass`:
| Value | Effect |
|---|---|
| Not configured | No Ingress resources are listened to. |
mse | Listens to Ingress resources with IngressClass mse. |
"" (blank) | Listens to all Ingress resources. |
nginx | Listens to Ingress resources with IngressClass nginx, or Ingress resources with no IngressClass associated. |
| Other values | Listens to Ingress resources associated with the specified IngressClass. |
The IngressClass resource associated with the MseIngressConfig viaspec.parameterstakes precedence over the value set iningress.local.ingressClass.
Status
After creating an MseIngressConfig, check its status with:
kubectl get mseingressconfigThe status transitions in this order: Pending → Running → Listening
| Status | Description |
|---|---|
Pending | The cloud-native gateway is being created. This typically takes about 3 minutes. |
Running | The gateway is created and running. |
Listening | The gateway is running and listening to Ingress resources in the cluster. |
Failed | The gateway is invalid. Check the Message field in the Status section for the cause. |
A successful deployment looks similar to:
NAME STATUS AGE
test Listening 5mResource tags
MSE Ingress Controller automatically adds the following tags to cloud-native gateways it creates or reuses. View these tags in the MSE console under the gateway's basic information.
Do not edit these tags in the MSE console. Editing them may cause unexpected gateway behavior.
| Tag | Description |
|---|---|
ack.aliyun.com | Identifies that an ACK cluster's Ingress traffic is managed by this MSE cloud-native gateway. |
ingress.k8s.alibaba/MseIngressConfig | Identifies the MseIngressConfig associated with the gateway. |
kubernetes.reused.by.user | Indicates whether the gateway is reused. If set, deleting the associated MseIngressConfig does not delete the gateway. |
Create an MSE cloud-native gateway
Apply an MseIngressConfig. The following example creates a gateway named
mse-ingresswith 3 replicas and 2 vCPUs / 4 GB memory. Adjust other fields as needed.apiVersion: mse.alibabacloud.com/v1alpha1 kind: MseIngressConfig metadata: name: test spec: name: mse-ingress common: instance: spec: 2c4g replicas: 3Create an IngressClass resource and associate it with the MseIngressConfig. This declares MSE Ingress Controller in the cluster, so Ingress resources linked to this IngressClass are handled by the corresponding cloud-native gateway.
apiVersion: networking.k8s.io/v1 kind: IngressClass metadata: name: mse spec: controller: mse.alibabacloud.com/ingress parameters: apiGroup: mse.alibabacloud.com kind: MseIngressConfig name: testVerify the gateway status:
kubectl get mseingressconfigThe status should progress from
PendingtoRunningand finally toListening. AListeningstatus confirms the gateway is active and watching Ingress resources.
Reuse an existing MSE cloud-native gateway
To reuse an existing gateway, set spec.id to the gateway ID (in gw-xxx format) and configure spec.override to control whether to overwrite the gateway's existing settings.
apiVersion: mse.alibabacloud.com/v1alpha1
kind: MseIngressConfig
metadata:
name: reuse
spec:
id: gw-xxxx
override: false
ingress:
local:
ingressClass: mse| Parameter | Type | Description |
|---|---|---|
spec.id | string | ID of the existing gateway to reuse. Must be in gw-xxx format. |
spec.override | boolean | Controls whether the MseIngressConfig overwrites the gateway's existing settings. |
Behavior based on `spec.override`:
`false` (recommended for reuse): The gateway's existing Ingress listening options, TLS hardware acceleration, IP access control, and observability settings are preserved. If the gateway is not yet associated with the cluster, MSE Ingress Controller automatically associates it and configures Ingress listening based on
spec.ingress.local.ingressClass. If the gateway is already associated, the existing Ingress listening options are unchanged.`true`: The gateway's Ingress listening options, TLS hardware acceleration, global IP access control, and observability settings are overwritten with values from the MseIngressConfig. If the parameters are not specified in the MseIngressConfig, the original parameter settings of the gateway are overwritten and your traffic may be negatively affected. Verify all relevant parameters are set before applying.
Delete an MSE cloud-native gateway
Each MseIngressConfig maps to one cloud-native gateway. In non-reuse scenarios, deleting an MseIngressConfig deletes the associated gateway.
kubectl delete mseingressconfig your-config-nameDeletion behavior depends on billing method and how the gateway was created:
| Billing method | Auto-created gateway | Reused gateway |
|---|---|---|
| Pay-as-you-go | Deleted with the MseIngressConfig | Retained |
| Subscription | N/A | Retained |
Configure IP access control
The global.ipAccessControl field applies IP filtering at the gateway level, affecting all traffic passing through the gateway. You can configure a whitelist, a blacklist, or both.
Configure an IP address whitelist
Only source IP addresses or CIDR blocks in the whitelist can access the gateway. All other traffic is denied.
apiVersion: mse.alibabacloud.com/v1alpha1
kind: MseIngressConfig
metadata:
name: test
spec:
global:
ipAccessControl:
whitelist:
- 1.1.XX.XX
- 2.0.XX.XX/8Configure an IP address blacklist
Source IP addresses or CIDR blocks in the blacklist are denied access. All other traffic is allowed.
apiVersion: mse.alibabacloud.com/v1alpha1
kind: MseIngressConfig
metadata:
name: test
spec:
global:
ipAccessControl:
blacklist:
- 1.1.XX.XX
- 2.0.XX.XX/8Activate Simple Log Service
Simple Log Service (SLS) delivers gateway access logs to a specified SLS project.
Prerequisites
Grant SLS permissions to MSE Ingress Controller before activating this feature:
ACK managed or dedicated cluster: See the "Grant permissions to MSE Ingress Controller in an ACK dedicated cluster" section in Grant permissions to MSE Ingress Controller.
ACK Serverless cluster: See the "Grant permissions to MSE Ingress Controller in an ACK Serverless cluster" section in Grant permissions to MSE Ingress Controller.
ACS cluster: See the "Grant permissions to MSE Ingress Controller in an ACS cluster" section in Grant permissions to MSE Ingress Controller.
Configure log delivery
Set monitor.logging.sls.reuseProject to the target SLS project name. Leave it blank to use the default project.
apiVersion: mse.alibabacloud.com/v1alpha1
kind: MseIngressConfig
metadata:
name: test
spec:
monitor:
logging:
sls:
# Leave blank to deliver logs to the default project.
reuseProject: "demo"Activate Managed Service for OpenTelemetry
Managed Service for OpenTelemetry enables end-to-end tracing for requests passing through the gateway, helping you diagnose and locate production issues.
Managed Service for OpenTelemetry and open source OpenTelemetry cannot be activated at the same time.
Set monitor.tracing.openTelemetry.sampleRate to the desired sampling percentage. The following example activates tracing with 100% sampling.
apiVersion: mse.alibabacloud.com/v1alpha1
kind: MseIngressConfig
metadata:
name: test
spec:
monitor:
tracing:
openTelemetry:
sampleRate: "100"