edge-tunnel is the cloud-to-edge tunneling component in ACK edge clusters. After you create an edge cluster, edge-tunnel-server and edge-tunnel-agent are automatically deployed to establish encrypted tunnels between the cloud and edge nodes.
How it works
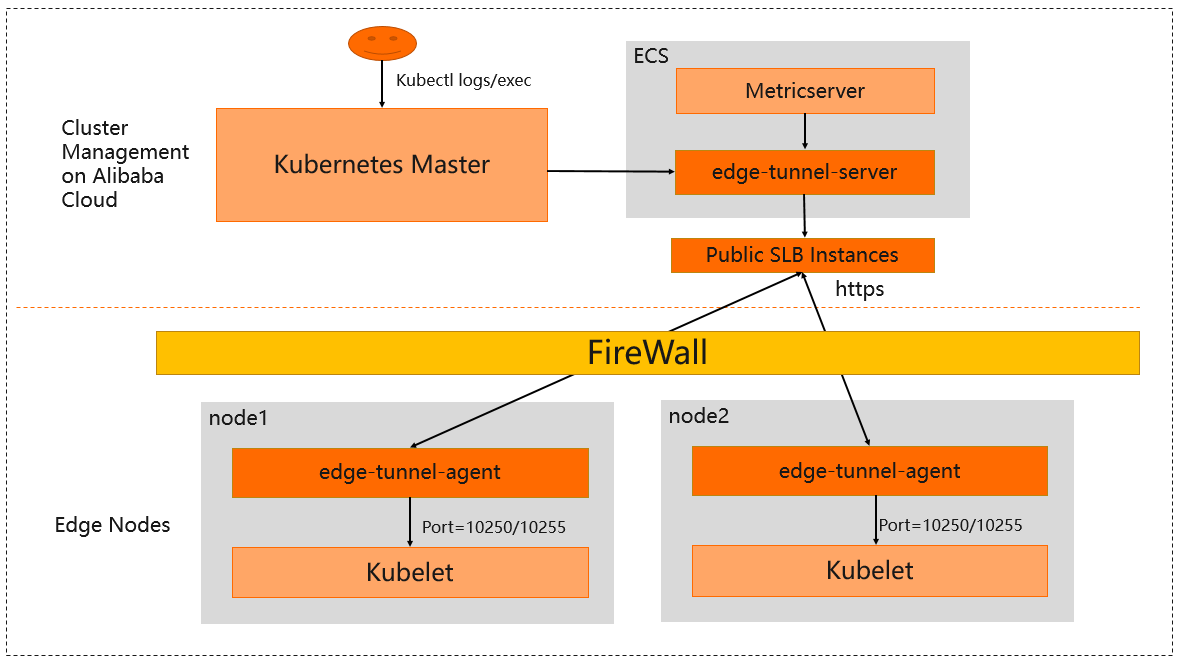
edge-tunnel uses a reverse tunnel in a client-server architecture:
edge-tunnel-server runs on the cloud as the server.
edge-tunnel-agent runs on each edge node as the client.
Tunnel establishment
A Server Load Balancer (SLB) instance is created for the Service exposed by edge-tunnel-server. Each edge-tunnel-agent establishes an encrypted tunnel to edge-tunnel-server through this SLB instance.
Automatic request forwarding
When cloud components such as kube-apiserver and metrics-server send requests to ports 10250 and 10255 on edge nodes, edge-tunnel intercepts and forwards those requests through the tunnel automatically. No changes to cloud components are required.
Network modes
Edge node pools can connect to the cloud in three modes. edge-tunnel behavior differs by mode.
| Mode | How the node pool connects | How cloud requests reach edge nodes | Label automatically applied |
|---|---|---|---|
| Internet | Over the Internet | Forwarded through the cloud-edge tunnel (forward proxy) | alibabacloud.com/interconnection-mode = normal |
| Express Connect | Over an Express Connect circuit | Sent directly to node ports (for example, 10250 and 10255) | alibabacloud.com/interconnection-mode = private |
| CCN | Via a Cloud Connect Network (CCN) instance | Sent directly to node ports (for example, 10250 and 10255) | alibabacloud.com/interconnection-mode = improved |
edge-tunnel-agent is deployed only on nodes in edge node pools that use Internet mode. For Express Connect and CCN modes, cloud components communicate directly with edge nodes without going through the tunnel.
Usage notes
For configuration details, see Cloud-edge tunneling.
Release notes
June 2023
| Version | Image address | Description | Release date | Impact |
|---|---|---|---|---|
| v0.22.1 | edge-tunnel-server: registry-cn-hangzhou-vpc.ack.aliyuncs.com/acs/edge-tunnel-server:v0.22.1 edge-tunnel-agent: registry-cn-hangzhou.ack.aliyuncs.com/acs/edge-tunnel-agent:v0.22.1 | - Communication between edge-tunnel and the API server is optimized to resolve restart failures caused by unstable networks. - Request forwarding from cloud to edge nodes is optimized to reduce URL leak risk from unstable Internet connections. - The iptables module is disabled. CoreDNS now handles domain name resolution during cloud-edge request forwarding. | 2023-06-28 | No impact on workloads |
December 2022
| Version | Image address | Description | Release date | Impact |
|---|---|---|---|---|
| v0.10.3 | edge-tunnel-server: registry.cn-hangzhou.aliyuncs.com/acs/edge-tunnel-server:v0.10.3 edge-tunnel-agent: registry.cn-hangzhou.aliyuncs.com/acs/edge-tunnel-agent:v0.10.3 | - Multiple network modes are now supported for cloud-edge communication. See Network modes for details on each mode and the labels applied. - DNS records are dynamically updated based on whether tunnel-agent is deployed on edge nodes. - Cloud component requests (from kube-apiserver and Prometheus) now go to port 10263 of x-tunnel-server-internal-svc instead of x-tunnel-server-svc. | 2022-12-14 | No impact on workloads |
January 2022
| Version | Image address | Description | Release date | Impact |
|---|---|---|---|---|
| v0.10.0 | edge-tunnel-server: registry.cn-hangzhou.aliyuncs.com/acs/edge-tunnel-server:v0.10.0 edge-tunnel-agent: registry.cn-hangzhou.aliyuncs.com/acs/edge-tunnel-agent:v0.10.0 | First edge-tunnel version for ACK edge clusters running 1.20.11-aliyunedge.1. Request forwarding improvements: requests to {nodeName:Port} and localhost endpoints can now be forwarded from the cloud to edge nodes. To forward requests to localhost endpoints, configure the localhost-proxy-ports field in the edge-tunnel-server-cfg ConfigMap. For ports other than 10250 and 10255: configure http-proxy-ports for HTTP endpoints or https-proxy-ports for HTTPS endpoints in edge-tunnel-server-cfg. The dnat-ports-pair field is retained but not recommended. Certificate management is improved: the TLS server certificate for edge-tunnel-server is automatically updated when the IP address of edge-tunnel-server-svc changes (for example, when associated with a new SLB instance). | 2022-01-27 | No impact on workloads |