Starting with Kubernetes v1.33, new ACK managed clusters have the latest version of ack-ram-authenticator pre-installed as a system add-on by default, without consuming additional node resources.
Scope
This change only affects new ACK managed clusters running Kubernetes v1.33 or later, including ACK managed Pro clusters and ACK managed Basic clusters.
Change details
For details about ack-ram-authenticator and its usage instructions, see ack-ram-authenticator and Use ack-ram-authenticator for API server webhook authentication in an ACK managed cluster.
For all new ACK managed clusters created with Kubernetes v1.33 or later:
The latest version of
ack-ram-authenticatoris pre-installed as a non-removable system add-on.Node pool scaling operations (both manual and auto scaling) require the ack-ram-authenticator add-on. This dependency will generate a few OpenAPI access traces within the cluster virtual private cloud (VPC) network during scaling events, specifically recording worker Resource Access Management (RAM) roles verifying identity through the STS GetCallerIdentity API.
ack-ram-authenticator configuration
Custom parameter description
Configure the custom parameter
Method 1: Terraform
When creating clusters through Terraform, you can use the addons attribute in the alicloud_cs_managed_kubernetes resource to install the ack-ram-authenticator add-on with custom configuration. For more information, see Use Terraform to manage add-ons.
resource "alicloud_cs_managed_kubernetes" "default" {
# Other parameters
# ...
addons {
name = "ack-ram-authenticator"
config = jsonencode(
{
"EnableNonBootstrapMapping": false
}
)
}
}Method 2: OpenAPI
When creating clusters through API, you can use the addons parameter in the CreateCluster interface to specify the installation of ack-ram-authenticator and configure the custom parameter.
"addons": [
// Other add-on configurations
{
"name": "ack-ram-authenticator",
"config": "{\"EnableNonBootstrapMapping\": false}"
}
],Method 3: Console
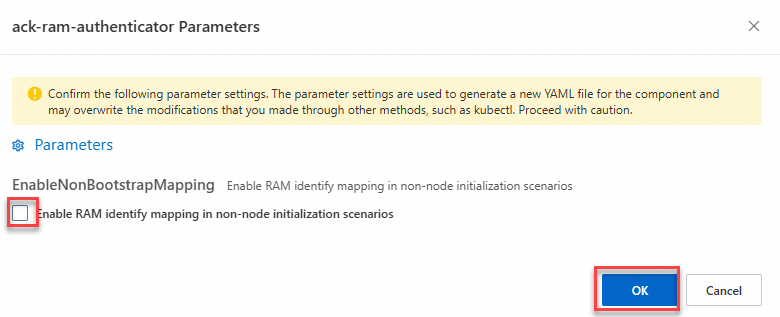
The ack-ram-authenticator add-on installed by default when you create clusters through the console disables RAM identity mapping for non-node initialization scenarios. To modify this configuration, follow these steps:
Contact us
If you encounter any issues or have suggestions for our product, submit a ticket to contact us.