Alibaba Cloud Service Mesh (ASM) is a fully managed service mesh platform compatible with open source Istio. With ASM, you can route and split inter-service traffic, authenticate inter-service communication, and observe service behavior across clusters — simplifying service governance and reducing both development and O&M overhead. This topic describes the network architecture and network requirements for Alibaba Cloud Distributed Cloud Container Platform (ACK One) clusters that have ASM enabled.
For more information about ASM, see What is ASM?
Network architecture
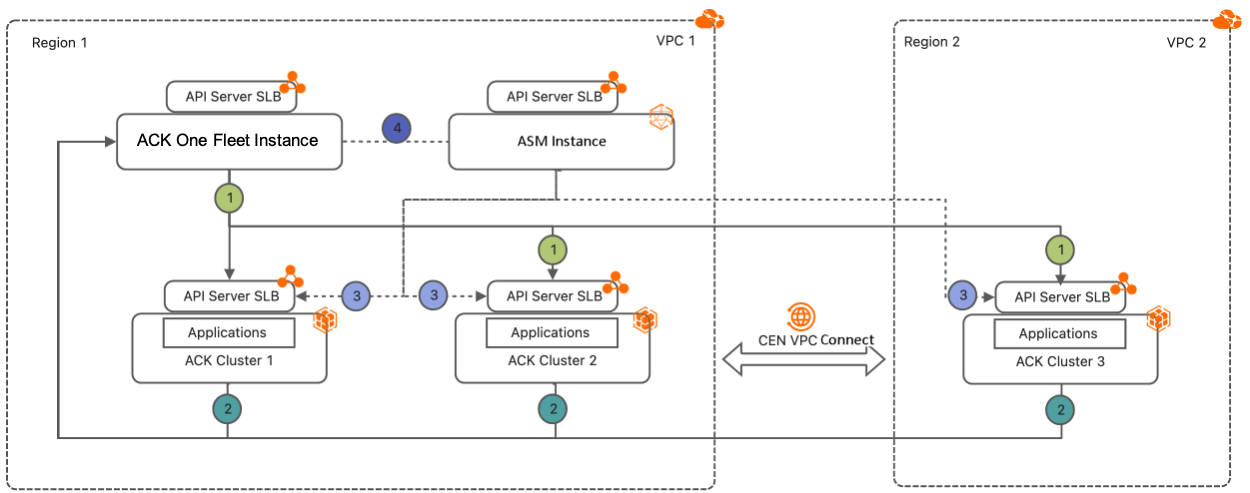
An ACK One deployment with ASM enabled consists of the following architecture: In this example, ACK Cluster 1 and ACK Cluster 2 are deployed in VPC 1 in Region 1, and ACK Cluster 3 is deployed in VPC 2 in Region 2.
Administrators connect to the Fleet instance's API server endpoint to manage all associated clusters and control network traffic — using a single kubeconfig file instead of switching between separate kubeconfig files for the Fleet instance and ASM instance.
The numbered connections in the architecture diagram correspond to the following communication paths:
-
① Fleet instance → associated clusters: The Fleet instance's VPC can reach the API server endpoints of all associated clusters.
-
② Associated clusters → Fleet instance: The VPCs of associated clusters can reach the Fleet instance's API server endpoint.
-
③ Service Mesh instance → associated clusters: The Service Mesh instance's VPC can reach the API server endpoints of all associated clusters.
-
④ Kubeconfig access to ASM: Modify the Fleet instance's kubeconfig to connect to the ASM instance and control traffic from ASM.
Network requirements
API server accessibility
All cluster API servers must be mutually reachable before ASM can manage traffic across them. If the Fleet instance and associated clusters are in different regions or different virtual private clouds (VPCs), create a Cloud Enterprise Network (CEN) instance to connect the VPCs. Alternatively, enable public endpoints on the Fleet instance and associated clusters to allow communication over the Internet. For more information, see CEN.
CIDR block requirements
To use ASM to manage applications and network traffic across associated clusters, the following CIDR block constraints must be satisfied. Overlapping address ranges can cause unpredictable traffic routing and prevent services from connecting to the correct endpoints.
Same-VPC deployments
When associated clusters are deployed in the same VPC:
| Resource | Constraint |
|---|---|
| Pod CIDR | Must not overlap with other clusters' pod CIDRs or with the VPC CIDR block |
| vSwitch CIDR | Must not overlap with each other, with the pod CIDR blocks, or with the Service CIDR blocks |
| Service CIDR | Must not overlap with other clusters' Service CIDRs or with the VPC CIDR block |
Cross-VPC deployments
When associated clusters are deployed in different VPCs, apply all same-VPC constraints above and also ensure:
| Resource | Constraint |
|---|---|
| VPC CIDR | Must not overlap with other clusters' VPC CIDR blocks |
| Pod CIDR | Must not overlap with other clusters' pod CIDRs |