ALB Ingress static routing rules work well for fixed path matching and request header filtering. When you need complex conditional logic — such as combining domain, path, and header checks — or need to return custom responses, AScript lets you write programmable scripts directly on the ALB listener. Although ALB supports forwarding rules that route traffic based on domain names and URLs, ALB provides limited capabilities in deeper user behavior analytics. You can use AScript to meet requirements for deeper user behavior analytics. This topic shows how to use AScript to block requests that match specific conditions.
Billing
AScript includes a free quota of 25 lines of code in the scriptContent field of the ConfigMap. Lines beyond the free quota are billed. For pricing details, see ALB billing rules.
Prerequisites
Before you begin, ensure that you have:
An ALB Ingress controller installed in the cluster at version 2.15.0 or later. For more information, see Manage the ALB Ingress controller.
NoteTo use an ALB Ingress with an ACK dedicated cluster, grant the cluster permissions to access the ALB Ingress controller first. For more information, see Authorize an ACK dedicated cluster to access the ALB Ingress controller.
A kubectl client connected to the ACK cluster. For more information, see Obtain the kubeconfig file of a cluster and use kubectl to connect to the cluster.
An AlbConfig and an IngressClass created. For more information, see Create an ALB Ingress.
Configure AScript rules on an ALB Ingress
To configure AScript, store the script in a ConfigMap, then reference the ConfigMap from the AlbConfig.
Scenario
An application receives frequent malicious and unidentified requests that increase backend load and degrade response times. To block these requests, the ALB Ingress applies the following logic:
If all three conditions are true:
The request uses the
example.comdomain nameThe request URI starts with
/order/createThe
User-Agentheader does not contain the stringtrusted
The ALB Ingress returns HTTP status code 403 and the message The order data is abnormal. Requests that don't match all three conditions are forwarded to the backend service.
Step 1: Configure a script in a ConfigMap
Create a file named
ascript_configmap.yamlwith the following content. When multiple conditions must all be true simultaneously, wrap them inand(). Theeq()function checks for exact string equality,split()strips the query string from the URI, andmatch_re()tests a value against a regular expression. For the full function reference, see References. In this example, the script is 5 lines, which falls within the 25-line free quota.apiVersion: v1 kind: ConfigMap metadata: name: ascript-rule namespace: default data: scriptContent: | if and(eq($host,'example.com'),eq(get(split($request_uri, '?'),1),'/order/create')){ if not(match_re($http_user_agent,'.*trusted.*')){ exit(403,'{"code":10063,"msg":"The order data is abnormal","data":{}}') } }Apply the ConfigMap:
kubectl apply -f ascript_configmap.yaml
Step 2: Associate the script with an AlbConfig
Open the AlbConfig for editing:
kubectl edit albconfig <ALBCONFIG_NAME>Replace
<ALBCONFIG_NAME>with the name of your AlbConfig.Add the
aScriptConfigfield under the listener configuration. Save and exit to apply the changes.apiVersion: alibabacloud.com/v1 kind: AlbConfig metadata: name: default spec: config: name: alb-test-1 addressType: Intranet listeners: - port: 80 protocol: HTTP aScriptConfig: - aScriptName: ascript-rule # The name of the script. enabled: true # Set to false to disable without removing the config position: RequestFoot # The position at which you want to execute the script. A value of RequestFoot specifies that the script is executed after the routing rules of the Ingress are applied. configMapNamespace: default # Namespace of the ConfigMapFor more information about execution positions, see AScript.
Verify the result
Send a test request that matches all three blocking conditions:
curl -v -H "Host:example.com" -H "User-Agent:suspicious test" http://<Domain name>/order/createIf the script is active, the response contains HTTP status code
403and the body{"code":10063,"msg":"The order data is abnormal","data":{}}.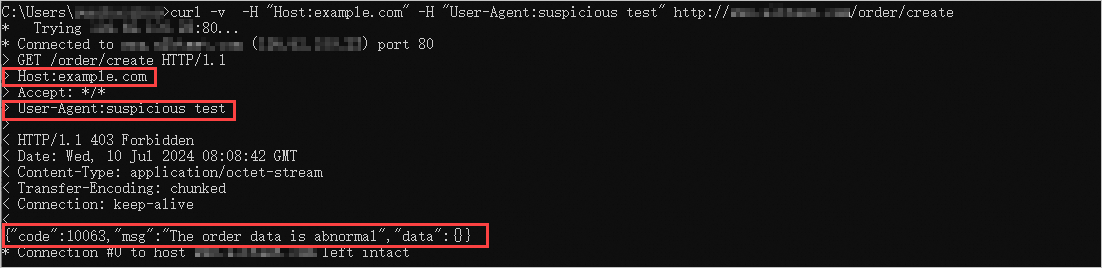
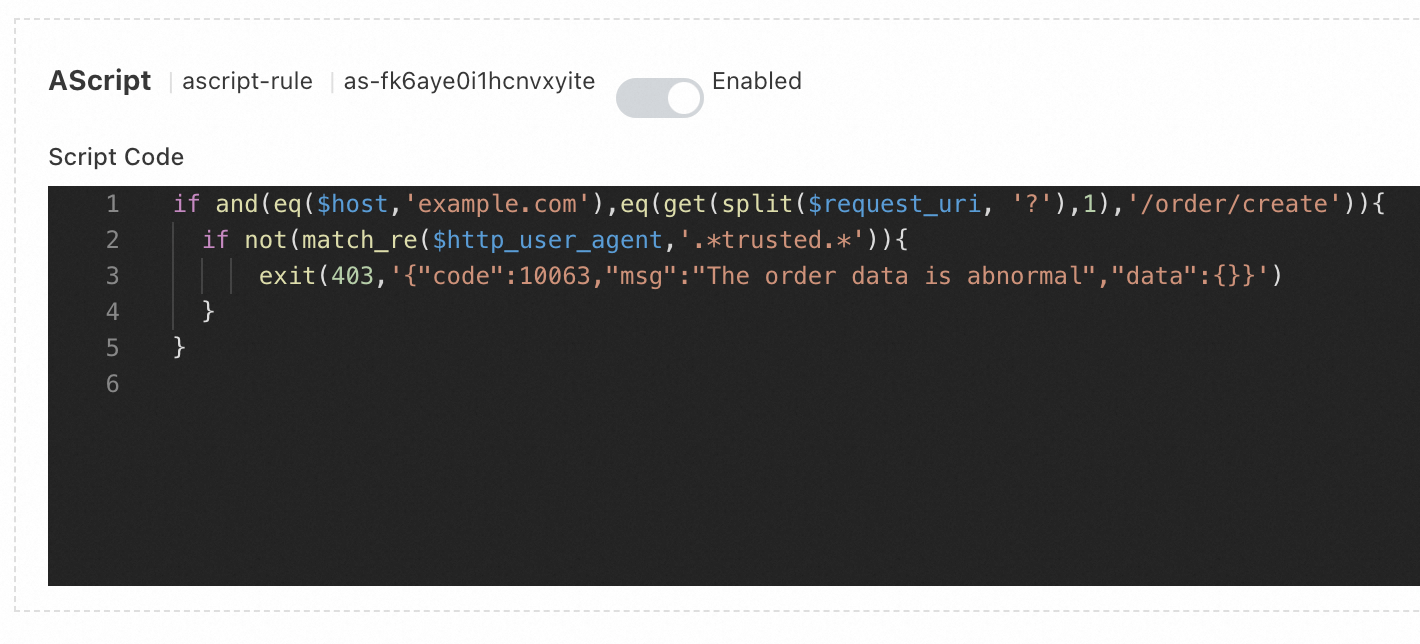
In the ALB console, navigate to the listener of your ALB instance to view the applied script.