If applications in your Container Service for Kubernetes (ACK) cluster need to access external resources over the Internet, such as pulling container images or downloading dependency packages, configure SNAT rules on a NAT gateway in the cluster's virtual private cloud (VPC).
This topic covers outbound Internet access from your cluster. To allow inbound access to the API server over the Internet (for example, connecting with kubectl from outside the cluster), see Control public access to the API server of a cluster.
Prerequisites
Before you begin, make sure that you have the following:
An ACK cluster with node pools
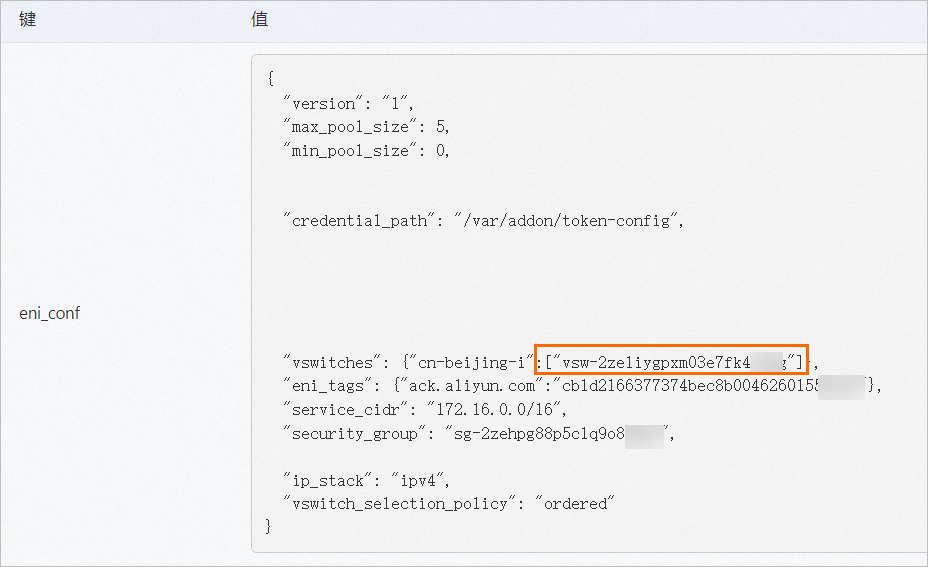
Knowledge of which network plugin your cluster uses (Terway or Flannel), because this determines which vSwitches require SNAT entries
The required permissions to create and manage NAT gateways and elastic IP addresses (EIPs)
Billing
Configuring SNAT rules involves the following billable services:
Service | Description | Billing details |
Provides fully managed NAT gateways that enable instances to access the Internet without exposing their private addresses. | ||
Provides independent public IP addresses that you can associate with cloud resources for Internet access. |
Terway vs. Flannel: vSwitch requirements
The vSwitches that require SNAT entries depend on your cluster's network plugin.
Network plugin | Required vSwitches for SNAT | Reason |
Terway | Node vSwitches and pod vSwitches | Terway assigns vSwitch-based IP addresses to pods, so both node and pod subnets need outbound routes. |
Flannel | Node vSwitches only | Flannel uses overlay networking, so pod traffic exits through the node's network interface. |
Enable SNAT for an existing cluster
To enable Internet access for an existing ACK cluster, create a NAT gateway, associate an EIP, and configure SNAT entries for the cluster's vSwitches.
You cannot use API operations to enable SNAT for existing clusters.
The following figure shows the overall workflow.
Step 1: Create a NAT gateway
Create an Internet NAT gateway in the same region as your cluster.
Log on to the NAT Gateway console.
In the left navigation pane, choose NAT Gateway > Internet NAT Gateway.
On the Internet NAT Gateway page, click Create Internet NAT Gateway.
Configure the parameters and click Buy Now. For more information about the parameters, see Create and manage an Internet NAT gateway.
When you create the first Internet NAT gateway in a VPC, the system automatically adds a route with destination CIDR block 0.0.0.0/0 and the Internet NAT gateway as the next hop to the VPC's system route table. This route directs traffic to the NAT gateway. If your VPC uses a custom route table or contains multiple Internet NAT gateways, you must add routes manually. For more information, see Create and manage a route table.
Step 2: Create an EIP (optional)
Skip this step if you already have an EIP that you want to use.
In the left-side navigation pane, choose Access to Internet > Elastic IP Addresses.
On the Elastic IP Addresses page, click Create EIP.
Select the same region as your NAT gateway, configure the remaining parameters, and then click Buy Now.
Step 3: Associate the EIP with the NAT gateway
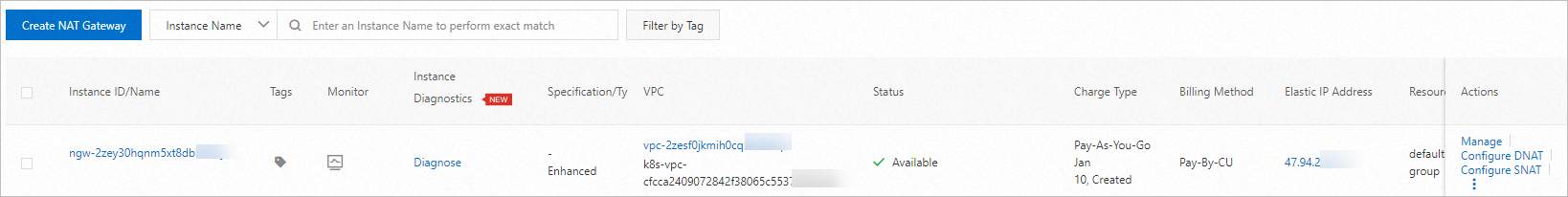
In the left-side navigation pane, choose NAT Gateway > Internet NAT Gateway.
On the Internet NAT Gateway page, find the NAT gateway that you created, and then choose
 > Associate EIP in the Actions column.
> Associate EIP in the Actions column.In the Associate EIP dialog box, select a resource group from the Resource Group drop-down list, select the EIP from the Select Existing EIP drop-down list, and then click OK.
Step 4: Create SNAT entries
On the Internet NAT Gateway page, find the NAT gateway that you created, and then click Manage in the Actions column.
On the gateway details page, click the SNAT Management tab, and then click Create SNAT Entry.
On the Create SNAT Entry page, configure the following parameters and click OK. For more information, see Create an SNAT entry.
Parameter
Description
SNAT Entry
Select Specify vSwitch and select the vSwitches used by your cluster. For Terway clusters, select both node vSwitches and pod vSwitches. For Flannel clusters, select only node vSwitches.
Select EIP
Select one or more EIPs for outbound Internet access.
After the SNAT entry is created, your cluster can access the Internet through the NAT gateway.
The following figure shows a NAT gateway configured for an ACK cluster that uses the Terway plugin, with SNAT rules enabling Internet access.
Enable SNAT during cluster creation
If you are creating a new ACK cluster, you can enable SNAT during the cluster creation process:
Log on to the ACK console.
When you create an ACK cluster, select Configure SNAT for VPC in the Network Settings section. For more information, see Create an ACK managed cluster.
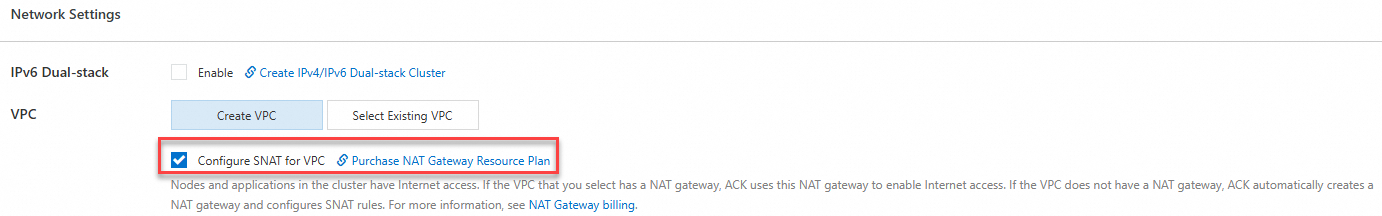
When you create the first Internet NAT gateway in a VPC, the system automatically adds a route with destination CIDR block 0.0.0.0/0 and the Internet NAT gateway as the next hop to the VPC's system route table. This route directs traffic to the NAT gateway. If your VPC uses a custom route table or contains multiple Internet NAT gateways, you must add routes manually. For more information, see Create and manage a route table.
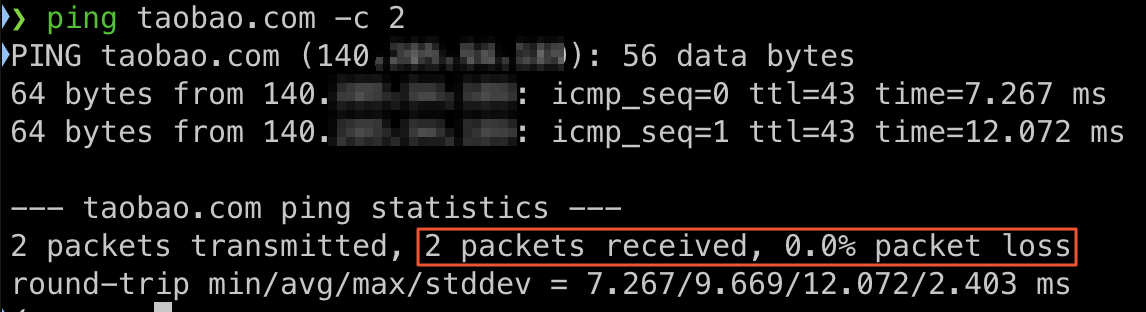
Verify Internet access
After you configure SNAT, verify that your cluster nodes can access the Internet.
Run a connectivity test to confirm Internet access:
ping -c 4 www.alibabacloud.comVerify that the outbound IP address matches the EIP you configured. The output should display the EIP associated with the NAT gateway:
curl ifconfig.me
FAQ
How do I find the public IP address used by my ACK cluster?
Log on to the NAT Gateway console.
In the left-side navigation pane, choose NAT Gateway > Internet NAT Gateway.
On the Internet NAT Gateway page, find the NAT gateway associated with your cluster and click Manage in the Actions column.
Click the SNAT Management tab. In the SNAT Entry List section, view the EIPs used by the cluster.

References
For notes on configuring pods to access external networks, including domain name resolution, network policies, and security groups, see Notes for configuring a pod to access an external network.
For recommended security group rules, see Configure security groups for clusters.
Do not configure SNAT entries and IPv4 gateways for an ACK cluster at the same time. For more information about using an IPv4 gateway, see Use IPv4 gateway to centralize control over Internet access.