ACK lets you customize containerd parameters at the node pool level, so you can tailor runtime behavior without modifying each node individually. For example, you can configure registry mirrors for a specific image repository, or skip TLS certificate verification for repositories that use self-signed certificates.
Prerequisites
Before you begin, make sure that:
-
The node pool uses containerd as its container runtime
-
The containerd version is 1.6.20 or later. If it isn't, upgrade the node pool
Usage notes
-
Custom containerd configurations apply to nodes in batches. Changes take effect immediately on existing nodes in the node pool, and new nodes automatically use the updated configuration.
-
Don't modify supported containerd parameters directly from the command line. ACK blocks such changes and they won't take effect. If you've already made changes this way, restore those parameters to their original values.
-
When a configuration takes effect, the system automatically normalizes the format and corrects any invalid syntax.
Supported containerd parameters
Container runtime configuration
| Parameter | Type | Default | Valid range | Description |
|---|---|---|---|---|
max_concurrent_downloads |
Int | containerd 2.x and later: 3; containerd 1.x and earlier: determined by internal runtime logic |
[1, 20] | Maximum number of concurrent image layer downloads. Increasing this value speeds up pulling multi-layer images but increases network and I/O load. |
ignore_image_defined_volumes |
Bool | true |
— | Whether to ignore anonymous volumes defined in the image using the VOLUME instruction. Set to true to prevent containers from automatically creating anonymous volumes. |
limitCore |
Int | infinity |
Non-negative integer | Maximum size (in bytes) of core dump files generated when processes in a container crash. 0 disables core dump generation; infinity sets no size limit. |
limitNoFile |
Int | 1048576 |
≥ 1024 | Maximum number of file descriptors that processes in a container can open. |
limitMemLock |
Int | 65536 (matches host OS). For Lingjun nodes, or nodes where RDMA or EDMA devices are detected during initialization, the default is automatically set to infinity. Attaching devices after the node becomes ready does not trigger this behavior. |
≥ 65536 | Maximum amount of memory (in bytes) that processes in a container can lock. |
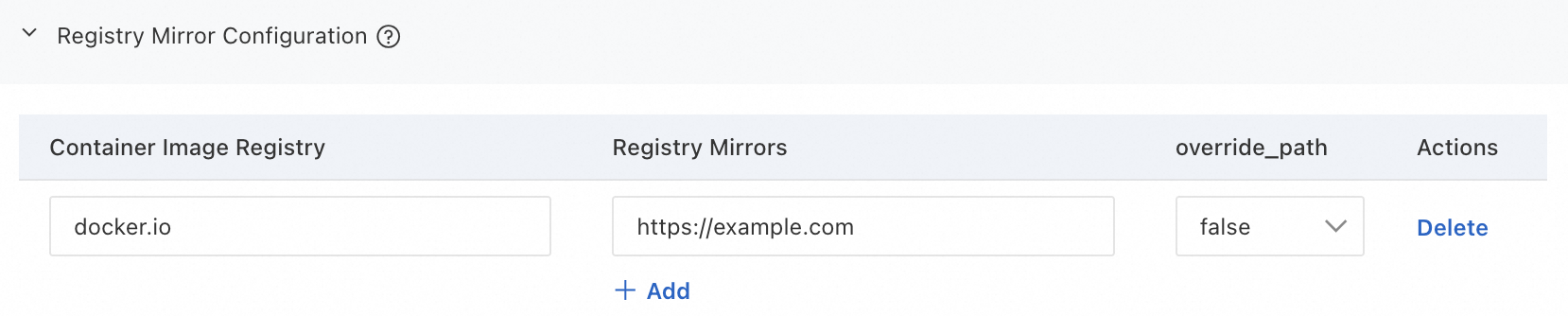
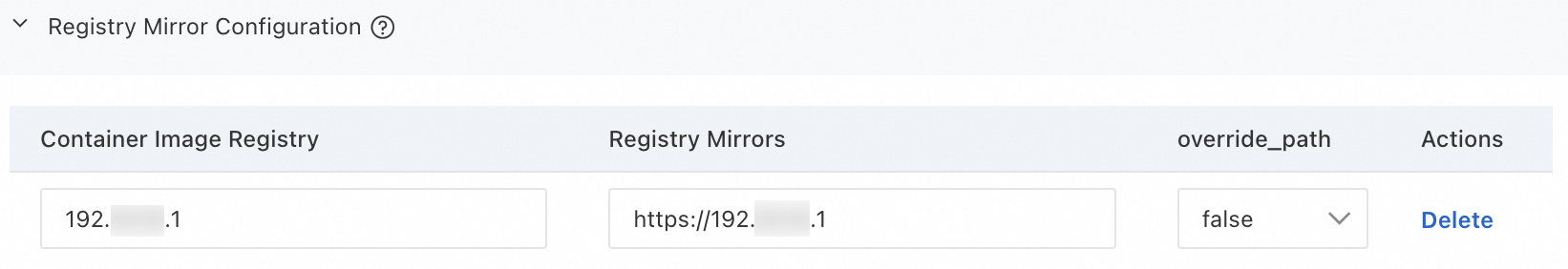
Registry mirror configuration
Configure registry mirrors to let the container runtime use alternative image repositories when pulling images, which speeds up image pulls and improves availability.
Each mirror supports custom path mapping using the override_path parameter.
This change does not restart containers.
Recommendations:
-
Add a local image repository to speed up image pulls.
-
Configure multiple image repositories to improve fault tolerance and availability.
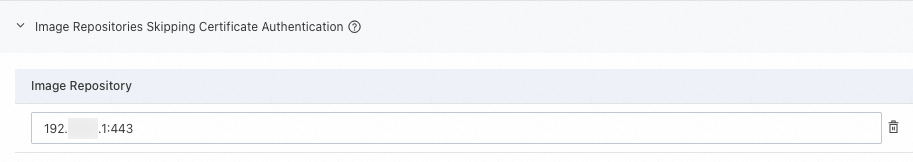
Insecure registries
Skip TLS certificate verification for specified image repositories when pulling images. Use this in staging environments where repositories have self-signed certificates.
This change does not restart containers.
Skipping certificate verification poses security risks. Use this only in development or staging environments. Use this only for private image repositories that use self-signed certificates or cannot provide valid certificates.
Configure containerd parameters using the console
This change does not affect existing containers. To keep your cluster stable, perform this operation during off-peak hours.
-
Log on to the ACK console. In the left navigation pane, click Clusters.
-
On the Clusters page, click the name of your cluster. In the left navigation pane, click Nodes > Node Pools.
-
On the node pool list page, click
 > Containerd Configuration in the Actions column of the target node pool.
> Containerd Configuration in the Actions column of the target node pool. -
Read the important notes on the current page. Add the parameters you need, select the target nodes, and set the batch configuration policy. Then click Submit. > See the configuration examples below.
-
Removing a container runtime configuration parameter reverts it to its default value automatically.
-
After you click Submit, the configuration applies to nodes in batches. You can track progress and control execution in the Events section — pause, resume, or cancel as needed. If a node task fails, troubleshoot the node and click Continue to retry. When you pause, nodes currently being configured finish applying the changes before pausing. Nodes not yet started wait until you resume. Complete the task as soon as possible — tasks paused for more than 7 days are canceled automatically, and the related events and logs are cleaned up.
-
Configuration examples
|
Configure a replacement image repository for docker.io |
Skip certificate verification for a private repository |
Configure an HTTP private image repository |
|
|
|
|
FAQ
Does customizing containerd parameters affect running workloads?
No. The change doesn't affect running pods — it applies only to new pods created after the change. To apply the new configuration to existing pods, recreate them manually.
I get an error like must be between XXX or not match XXX when customizing parameters. How do I fix it?
-
must be between XXX: The parameter value or format is invalid. Check that the value is within the allowed range and uses the correct format. -
`not match XXX`: You modified the configuration file directly from the command line. ACK blocks such changes — restore the parameter to its original value.
What's next
-
For automated O&M capabilities supported by node pools, see Automated O&M capabilities.
-
If your nodes, pods, containerd, or kubelet report errors or behave unexpectedly, see Troubleshoot node issues, Troubleshoot pod issues, and Node and node pool FAQ.