Many enterprises manage their own LDAP directories for identity management and want to extend those systems into Alibaba Cloud without re-provisioning accounts. This topic walks you through connecting an OpenLDAP directory to ACK by routing authentication through Identity as a Service (IDaaS), which maps external LDAP users to Alibaba Cloud Resource Access Management (RAM) users.
How it works
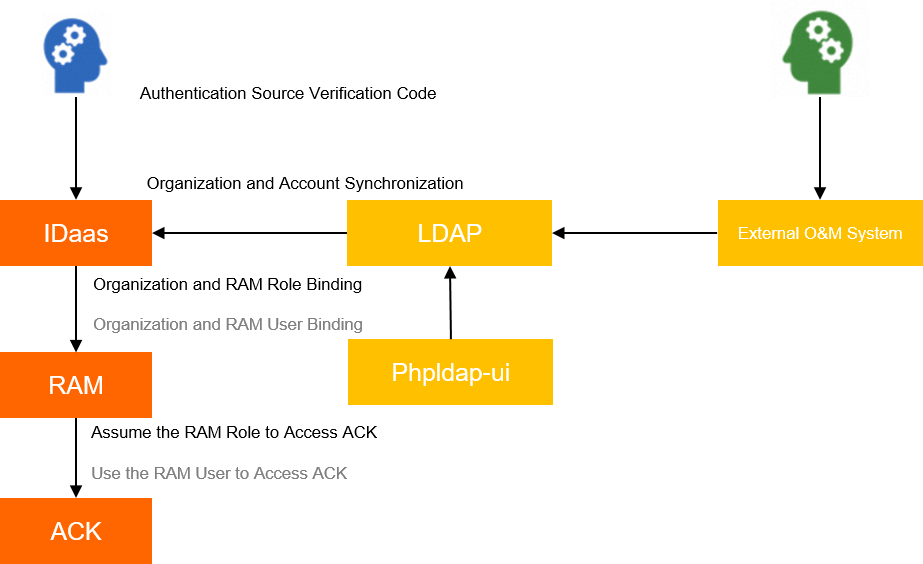
Authentication flows through four services:
OpenLDAP stores the user directory.
IDaaS bridges the external directory to RAM.
RAM controls Alibaba Cloud permissions.
ACK enforces role-based access control (RBAC) at the cluster level.
The end-to-end setup covers five stages:
Sync LDAP accounts to IDaaS. Add an LDAP authentication source in the IDaaS console. Account data (but not passwords) is pulled from LDAP into IDaaS. To let LDAP users log in with their LDAP credentials, set a password for each account in IDaaS — or configure single sign-on (SSO) to skip per-account password management.
Create an IDaaS application and link permissions. The application must be associated with a RAM user that holds the
AliyunRAMFullAccesspermission so it can manage RAM on your behalf — provide the AccessKey ID and AccessKey secret of that RAM user in the application configuration. It also needs to be linked to a separate RAM user or RAM role that grants LDAP accounts the ACK permissions they need. Import the synced LDAP accounts into the application and authorize them.Configure SSO for the IDaaS application. Set up an LDAP authentication source for IDaaS SSO so users can authenticate with their existing LDAP credentials.
Users log in via SSO. When an LDAP user logs in to the Alibaba Cloud Management Console through SSO, they inherit permissions from the RAM user or RAM role linked to the IDaaS application.
Complete RBAC authorization in ACK. Use an Alibaba Cloud account to assign Kubernetes RBAC roles to the LDAP-mapped users in the ACK console.
Prerequisites
Before you begin, ensure that you have:
An ACK cluster with an Nginx Ingress controller deployed
kubectlconfigured to connect to the clusterAn Alibaba Cloud account with permissions to create RAM users and IDaaS instances
A RAM user with the
AliyunRAMFullAccesspolicy attached (needed for the IDaaS application configuration)A RAM user or RAM role that you want LDAP users to inherit ACK permissions from
Step 1: Deploy OpenLDAP to your cluster
This step provisions an OpenLDAP data store and phpLDAPadmin (a web UI for managing LDAP entries) inside the public-service namespace.
Install OpenLDAP and phpLDAPadmin
Clone the demo repository, which contains the Kubernetes manifests for OpenLDAP and phpLDAPadmin:
git clone https://github.com/lilongthinker/demo-base-code.gitExpected output:
Cloning to 'demo-base-code'... remote: Enumerating objects: 12, done. remote: Counting objects: 100% (12/12), done. remote: Compressing objects: 100% (10/10), done. remote: Total 12 (delta 0), reused 9 (delta 0), pack-reused 0 Unpacking objects: 100% (12/12), done.Switch to the LDAP directory and review the included manifests:
cd demo-base-code/01_ldap tree ././ ├── ingress-phpadmin.yaml ├── ldap-deploy.yaml ├── ldap-secret.yaml ├── ldap-service.yaml ├── phpldapadmin-deploy.yaml └── phpldapadmin-svc.yaml 0 directories, 6 files ################################################ apiVersion: networking.k8s.io/v1 kind: Ingress metadata: labels: ingress-controller: nginx name: ldap-ui namespace: public-service spec: ingressClassName: nginx rules: - host: phpldap.example.com # Replace with the domain name you want to use. http: paths: - backend: service: name: phpldapadmin port: number: 8080 path: / pathType: ImplementationSpecific ################################################Before deploying, open
ingress-phpadmin.yamland replacephpldap.example.comwith the domain name you want to use for the phpLDAPadmin UI.Create the namespace:
kubectl create ns public-serviceExpected output:
namespace/public-service createdDeploy all manifests:
kubectl apply -f ./Expected output:
ingress.extensions/ldap-ui created deployment.extensions/ldap created secret/ldap-secret created service/ldap-service created deployment.extensions/phpldapadmin created service/phpldapadmin created
Initialize LDAP accounts
Get the external IP address assigned to the Ingress:
kubectl get ingNAME HOSTS ADDRESS PORTS AGE ldap-ui phpldap.example.com 121.xx.xxx.xxx 80 45sOpen the phpLDAPadmin console in your browser using the Ingress domain name. Log in with the default credentials:
Field Default value Distinguished name (DN) cn=admin,dc=example,dc=orgPassword adminIf the browser reports that you are unauthorized to access
/var/lib/php/sessions, run thechmodcommand to fix the session directory permissions.Create an organizational unit: In the left-side navigation pane, click Create new entry here. On the Create Object page, click Generic: Organisational Unit, then click Create Object. Enter a name for the organizational unit (for example,
dev) and click Create Object.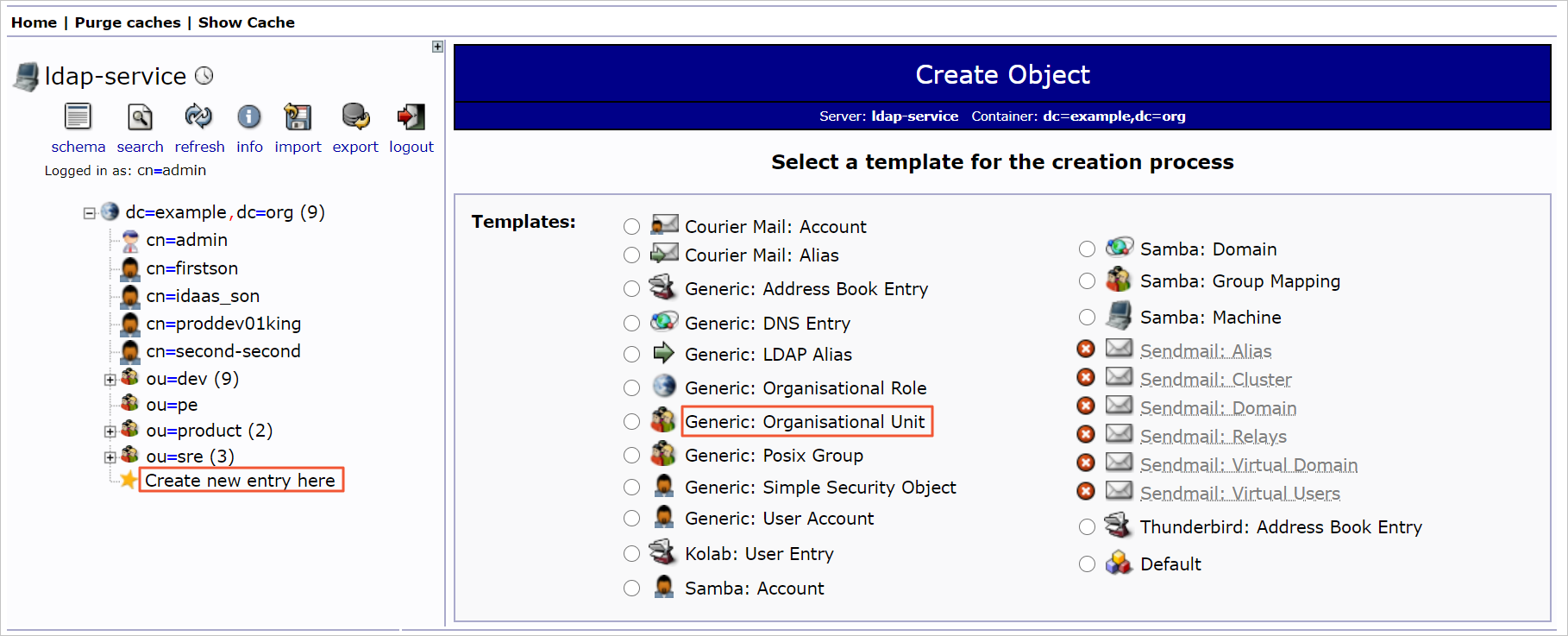
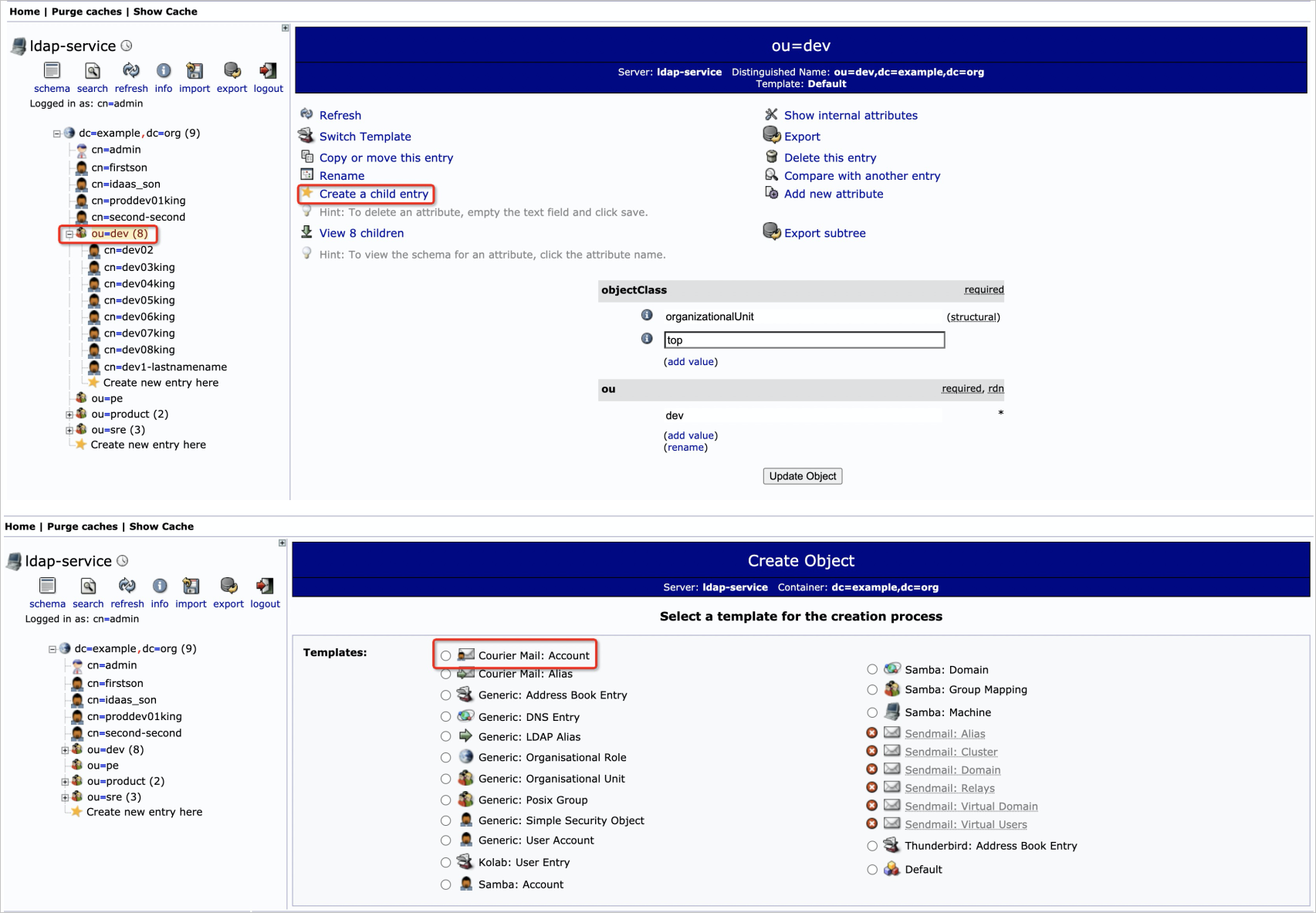
Create user accounts under the organizational unit: In the left-side navigation pane, click Create a child entry. Click Courier Mail:Account, fill in the user information, and click Create Object.
ImportantThe default account name may include trailing space characters. Delete them before saving.
Step 2: Configure IDaaS
Create an IDaaS instance and bind OpenLDAP
Log in to the IDaaS console and click Create Instance.
In the Create Instance dialog box, enter a description, accept the service agreement, and click Create.
In the instance list, click the instance you created to open the Quick Start page, then click Bind OpenLDAP.
On the Connect to LDAP step, fill in the LDAP connection details and click Next. For the full list of parameters, see Bind IDaaS to OpenLDAP - inbound.
Section Parameter Value Basic information Display name Enter a name for this LDAP source Server configuration Server address External IP address of the ldap-serviceService. To find it: log in to the ACK console, click Clusters, click the cluster name, choose Network > Services in the left-side navigation pane, and record the external IP address ofldap-service.LDAP domain configuration Administrator account cn=admin,dc=example,dc=orgLDAP domain configuration Administrator password adminOn the Select scenario step, configure the scenario settings and click Next. For guidance, see Bind IDaaS to OpenLDAP - inbound.
On the Field mapping step, map the following fields and click Save and Push:
IDaaS field Notes Username Map to the CN field in OpenLDAP. If the mapping rule is Select field, choose the IDaaS field that matches your directory schema. Email address Map to the corresponding field in OpenLDAP. When you designate a field as a unique mapping identifier, IDaaS automatically binds matching accounts between IDaaS and OpenLDAP and keeps them in sync. If no match is found, IDaaS creates a new account and binds it.
Verify account synchronization and configure sign-in
After saving, navigate to Accounts > Accounts and Orgs in the left-side navigation pane. Confirm that the organization and account data from OpenLDAP appears in IDaaS.
In the left-side navigation pane, click Sign-in. On the General tab, set the sign-in method to
ack-ldapfor both computers and mobile platforms.
Step 3: Verify the IDaaS configuration
In the left-side navigation pane, navigate to IdPs > Delegated Authentication. Find the delegated authentication link and open it in your browser. If the IDaaS logon page appears and you can log in successfully, the configuration is working.
Troubleshooting
If the logon page does not appear or authentication fails, check the following:
| Symptom | Likely cause | Action |
|---|---|---|
| Cannot reach the IDaaS delegated authentication URL | Network or firewall issue | Confirm the IDaaS instance is active and the URL is correct |
| "Invalid credentials" on the IDaaS logon page | Wrong DN or password | Re-check the Administrator account and Administrator password values in the LDAP source configuration |
| Accounts not visible in Accounts and Orgs | Field mapping misconfigured or base DN incorrect | Review the Field mapping step |
| Users cannot log in with LDAP credentials | Password not set in IDaaS (SSO not configured) | Set a password for each IDaaS account, or complete SSO configuration |
What's next
To allow LDAP users to log in to the Alibaba Cloud Management Console through SSO and to assign them ACK permissions via RBAC, complete the following:
Create an Application — create an IDaaS application, link it to the required RAM user and RAM role, and import the synced LDAP accounts
Login and SSO — configure SSO so users authenticate with their LDAP credentials