By default, a Classic Load Balancer (CLB) instance routes all incoming traffic to the single backend server group associated with its listener. This can lead to uneven resource distribution, performance degradation, and complex maintenance. As your business grows, this default setup may not meet diverse needs. You can configure forwarding rules for a CLB listener to direct traffic to specific backend server groups. This enables fine-grained traffic management and service isolation, improving resource utilization, ensuring service stability, and optimizing the user experience.
Overview
Forwarding rules for a Classic Load Balancer (CLB) listener allow you to distribute incoming client requests to different backend servers based on domain names and URL paths, enabling efficient and intelligent traffic distribution.
Key features
Domain-based forwarding rules
Matching modes: CLB supports exact match and wildcard match (including single-level and multi-level wildcards). For example,
www.aliyun.comis an exact match, while*.aliyun.comand*.market.aliyun.comare wildcard matches.Matching priority: An exact match takes precedence over a wildcard match. If a request matches multiple wildcard domain names, CLB applies the more specific wildcard rule. This ensures the most precise rule is always executed.
The following table shows an example of matching priorities. A "✓" indicates a match, and an "×" indicates no match.
Mode
Test request URL
Configured domain
www.aliyun.com
*.aliyun.com
*.market.aliyun.com
Exact Match
www.aliyun.com
✓
×
×
Wildcard match
market.aliyun.com
×
✓
×
info.market.aliyun.com
×
×
✓
URL path-based forwarding
Matching logic: Path-based rules use the longest prefix match principle. For example, if you configure rules for both /abc and /abcd, a request for /abcde matches the /abcd rule.
Combining rules: You can configure multiple rules for a single listener, combining both domain and URL path criteria to handle complex traffic distribution scenarios, such as routing read and write requests to different server groups.
How it works
You can add multiple forwarding rules to a listener, with each rule directing traffic to a different vServer group. The matching logic is shown in the figure below. If no forwarding rules are configured, the load balancer routes all requests to the default server group configured for the listener. If forwarding rules exist, the load balancer first tries to match the request's domain or path against these rules. If a match is found, the load balancer forwards the request to the corresponding vServer group. If no rules match, it sends the request to the listener's default server group.
Use cases
Microservices architecture: In a microservices architecture, an application consists of multiple independent services, each deployed on different instances or containers. These services work together to deliver the application's full functionality. By using a path-based routing mechanism, you can ensure that client requests are precisely directed to the service instances that handle the corresponding business logic. For example, on an e-commerce platform, requests for user authentication, or*er processing, and payments can be routed to their respective authentication, or*er, and payment service instances based on the request's URL path.
Read/write splitting: For services with high concurrency and strict data consistency requirements, such as an order processing service, a read/write splitting strategy can optimize performance and data security. Different database instances or clusters handle read and write operations. Read operations are routed to a read database, while write operations are directed to a write database.
Multi-tenant applications: In multi-tenant applications, you need to provide isolated and customized environments for different tenants. For example, you can use tenant-specific subdomains to create separate entry points and combine them with URL paths to further differentiate services. This approach not only ensures data security and privacy but also provides a customized user experience and interface for each tenant.
Limitations
Forwarding rules are supported only for Layer 7 HTTP and HTTPS listeners.
The backend server group specified in a forwarding rule must be a vServer group.
You can add a maximum of 40 domain and URL forwarding rules to a single HTTP or HTTPS listener. For more information, see Limitations.
Example scenario
An education platform wants to offer diverse online learning services, such as video courses and an online exam library, through a single domain name. The video service requires high bandwidth and stream processing capabilities, while the exam library service must be compute-intensive and highly responsive. Initially, all services were deployed in a single server group, which led to uneven resource allocation. During peak hours for video streaming, the exam library became slow, resulting in a poor user experience. When user traffic surged, the high server load compromised service stability.
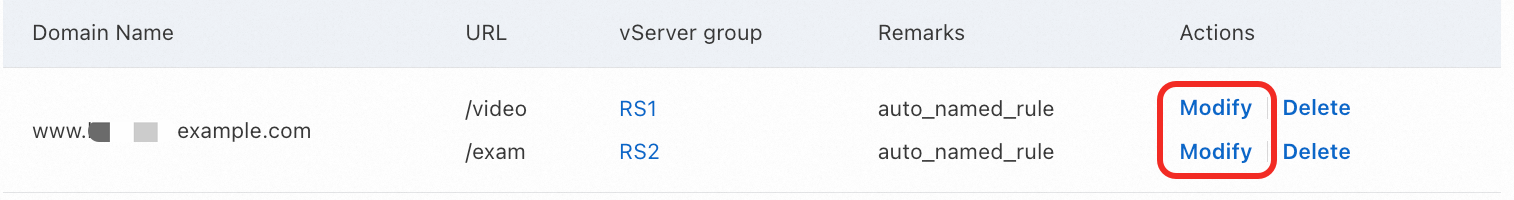
To address this, the platform uses Alibaba Cloud CLB to configure forwarding rules that route traffic based on different URL paths under the same domain name. As shown in the figure, requests for the /video/ path are forwarded to the video service's vServer group RS1, ensuring sufficient bandwidth and processing power. Requests for the /exam/ path are forwarded to the exam library's vServer group RS2, optimizing compute resources for fast query responses and submissions. This approach enables precise routing and ensures that each sub-service runs efficiently and independently.

Prerequisites
You have created a Virtual Private Cloud (VPC) named VPC1 in the China (Shanghai) region, and two vSwitches, VSW1 and VSW2, in availability zones E and G respectively.
You have created two ECS instances, ECS01 and ECS02, in VSW1 and VSW2 respectively. You have deployed application services on both instances. Note that you must configure the security groups of the ECS instances to allow traffic on the ports used by your applications.
The following is an example of how to deploy the test applications on ECS01 and ECS02:
You have created two vServer groups, RS1 and RS2, for the CLB instance, and added ECS01 to RS1 and ECS02 to RS2. For more information, see Create and manage a vServer group. The backend server port must match the application's service port. This example uses the default NGINX port, 80.
You have configured an HTTP listener or an HTTPS listener for your CLB instance.
You have registered a domain name with Alibaba Cloud and completed the ICP filing.
Procedure
Step 1: Configure a forwarding rule
Log on to the Classic Load Balancer (CLB) console.
In the top navigation bar, select the region where your CLB instance is deployed.
On the Instances page, click the ID of the target instance.
On the Listener tab, find the target listener and click Set Forwarding Rule in the Actions column.
In the Add Forwarding Policy panel, configure a forwarding rule based on the following information, and then click Add Forwarding Policy.

Domain Name: Your custom domain name that is registered and has an ICP filing.
URL: The request path.
URL paths in CLB forwarding rules are case-sensitive. For example, CLB considers
/videoand/viDeoas two separate paths that require distinct forwarding rules.
NoteIf a request URL contains special characters, you must use their URL-encoded equivalents. For example, if you configure a forwarding rule with the path
/#/, you must use the encoded version/%23/in the browser to access the service. This ensures that CLB matches and forwards the request correctly.
Step 2: Configure a health check
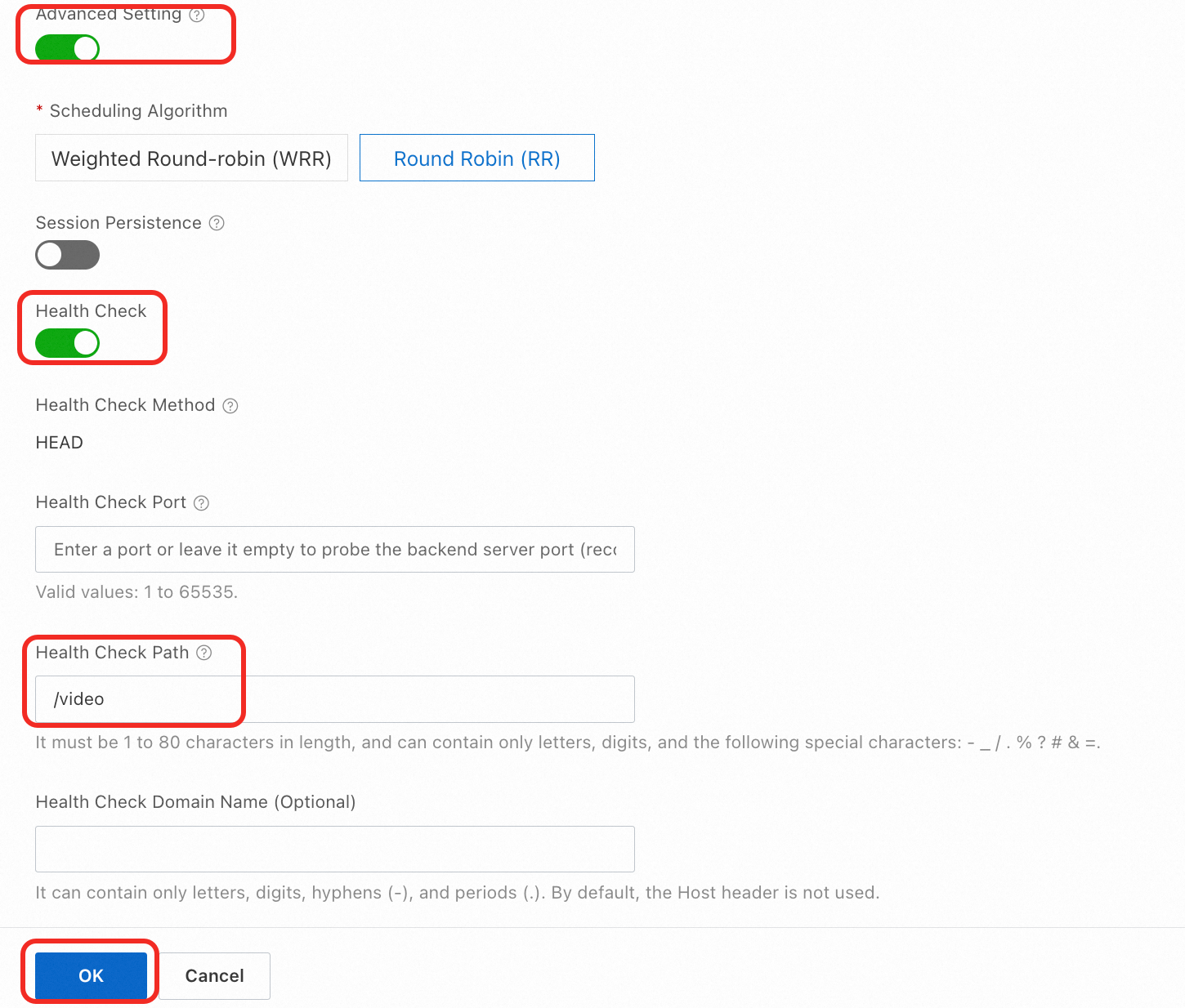
By default, an HTTP health check sends an HTTP request to the default homepage of the application configured on the server. If the page you want to use for health checks is not the application's default homepage, you must specify a different path.
On the Instances page, find the target CLB instance and click its ID.
On the Listener tab, click Set Forwarding Rule in the Actions column of the listener.
On the Add Forwarding Rules panel, in the Forwarding Rules, find the target rule and click Modify. Repeat this step if you need to configure multiple rules.
In the Modify Forwarding Rule panel, enable Advanced Setting, and configure the Health Check Path. You can set this to the path specified in the forwarding rule's URL field. For example, for a rule with the URL /video, configure the settings as shown below.
Step 3: Set up DNS resolution
If your domain is not registered with Alibaba Cloud, you must first add the domain to the Alibaba Cloud DNS console before you can set up DNS records.
If you are using an internal-facing CLB instance, you must first bind an Elastic IP address (EIP) to it. Then, configure an A record to resolve the domain name to the EIP to enable public access.
In the left-side navigation pane, choose .
On the Instances page, select the target instance and copy its IP Address.
Add an A record.
Log on to the Alibaba Cloud DNS console.
On the Public Zone page, find the target domain and click Settings in the Actions column.
On the Settings page, click Add Record.
In the Add Record panel, configure the following parameters. You can keep the default values for other parameters or modify them as needed. Then, click OK.
Parameter
Description
Record Type
Select A from the drop-down list.
Hostname
The prefix of your domain name.
NoteFor a root domain, set the host to @.
Record Value
The IP address for the domain name. Enter the endpoint you copied from the CLB instance.
Step 4: Test access
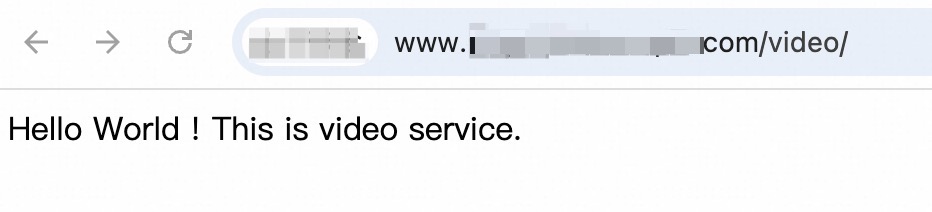
Open a browser and visit http://<Your-Domain>/<URL-Path>/ to verify that CLB routes requests to the correct server group.
Visit http://www.example.com/video/ to check if CLB routes the request to vServer group RS1 for the video service.
Visit
http://www.example.com/exam/to check if CLB routes the request to vServer group RS2 for the exam library service.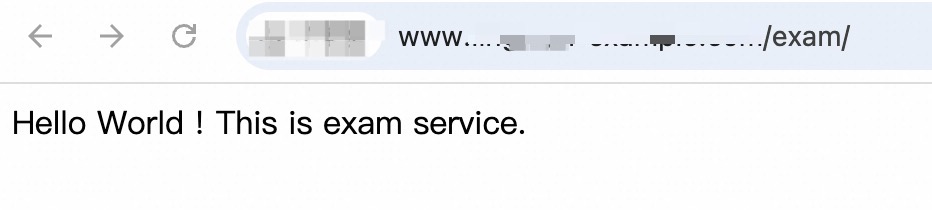
FAQ
Do CLB forwarding rules support path redirection?
No. CLB forwarding rules are for traffic forwarding only. If you need to configure path redirection, consider using an Application Load Balancer (ALB). For more information, see Configure listener forwarding rules.
Why is the health check status abnormal after I configure multi-path forwarding?
When performing a health check, the load balancer checks the health check path configured for the listener (the root path by default) and ignores the paths in forwarding rules. If your backend service responds differently based on the request path, a health check to the default path may fail. To resolve this, you can specify a custom health check path within each forwarding rule's advanced settings.
Are there any charges for configuring domain-based forwarding rules?
Configuring forwarding rules is free of charge. However, if you have an internal-facing CLB instance and bind an EIP to it for public access, you will incur internet data transfer fees. For more information about billing, see CLB billing overview.
References
If you need to configure multiple HTTPS domain names for a CLB instance, see Configure a CLB instance to serve multiple domain names over HTTPS.
If your application currently uses HTTP and you want to migrate to the secure HTTPS protocol, see Use CLB to redirect HTTP requests to HTTPS.
If you need to smoothly migrate from CLB to ALB, see Migrate Layer 7 listeners from CLB to ALB with one click and Manually migrate Layer 7 listeners from CLB to ALB.