When multiple Alibaba Cloud accounts need to share cloud resources, the account that owns the resources (the resource owner) can delegate access to another account (the accessing account) through RAM role delegation. This avoids sharing permanent credentials between accounts while maintaining fine-grained access control.
The resource owner creates a RAM role, attaches permission policies such as Application Real-Time Monitoring Service (ARMS) policies, and establishes a trust relationship with the accessing account. A RAM user from the accessing account then assumes that role to work with the shared resources.
How cross-account access works
A RAM role is a virtual identity with no permanent credentials. It can only be used after a trusted entity assumes it. Cross-account access involves five steps:
The resource owner creates a RAM role and sets the accessing account as a trusted entity.
The resource owner attaches ARMS permission policies to the RAM role.
The accessing account creates a RAM user.
The accessing account attaches the
AliyunSTSAssumeRoleAccesspolicy to the RAM user.The RAM user assumes the role to access the resource owner's resources through the console or API.
ARMS permission policies
ARMS provides two system policies:
| Policy | Permissions |
|---|---|
AliyunARMSFullAccess | Full permissions on ARMS. RAM users can view, edit, and delete instances across all sub-services. |
AliyunARMSReadOnlyAccess | Read-only permissions on ARMS. RAM users can view instance information of each sub-service but cannot modify or delete anything. |
If you attachAliyunARMSFullAccess, you do not need to also attachAliyunARMSReadOnlyAccess.
To grant read-only access to all ARMS features within a specific resource group, attach both the AliyunARMSReadOnlyAccess policy and the ReadTraceApp permission to that resource group. Without both, ARMS cannot display the application list for the authorized resource group.
Prerequisites
Before you begin, make sure that you have:
Administrator access to the RAM console for both the resource owner account and the accessing account
The Alibaba Cloud account ID of the accessing account (viewable on the Security Settings page)
Step 1: Create a RAM role (resource owner)
Create a RAM role under the resource owner account and designate the accessing account as a trusted entity.
Log on to the RAM console with a RAM user that has administrative rights.
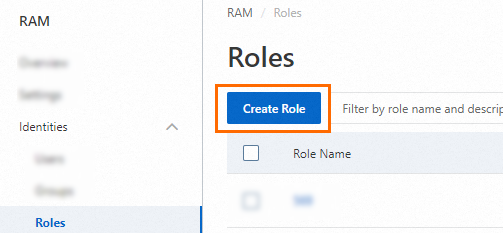
In the left-side navigation pane, choose Identities > Roles.
On the Roles page, click Create Role.
On the Create Role page, set the Principal Type to Cloud Account, then configure the trusted account:
Current Account: Select this if a RAM user or RAM role within your own account will assume the role.
Other Account: Select this if a RAM user or RAM role from a different Alibaba Cloud account will assume the role. Enter the ID of the accessing account.
For cross-account access, select Other Account and enter the accessing account's ID.

For more information, see Use a RAM role to grant permissions across Alibaba Cloud accounts. To find your account ID, go to the Security Settings page.
(Optional) To restrict which RAM user or RAM role from the trusted account can assume this role, click Switch to Policy Editor and modify the trust policy.
The editor supports both Visual editor and JSON modes. The following example allows only the RAM user
Alicefrom account100******0719to assume the role:Visual editor
Set a RAM user for the Principal element.


JSON
Specify a RAM user in the
RAMfield of thePrincipalparameter:{ "Version": "1", "Statement": [ { "Effect": "Allow", "Principal": { "RAM": "acs:ram::100******0719:user/Alice" }, "Action": "sts:AssumeRole" } ] }
In the Create Role dialog box, set the Role Name and click OK.
Step 2: Grant permissions to the RAM role (resource owner)
The newly created RAM role has no permissions by default. Attach permission policies to grant the access level you need.
Log on to the RAM console as a RAM administrator.
In the left-side navigation pane, choose Identities > Roles.
On the Roles page, find the target role and click Grant Permission in the Actions column.
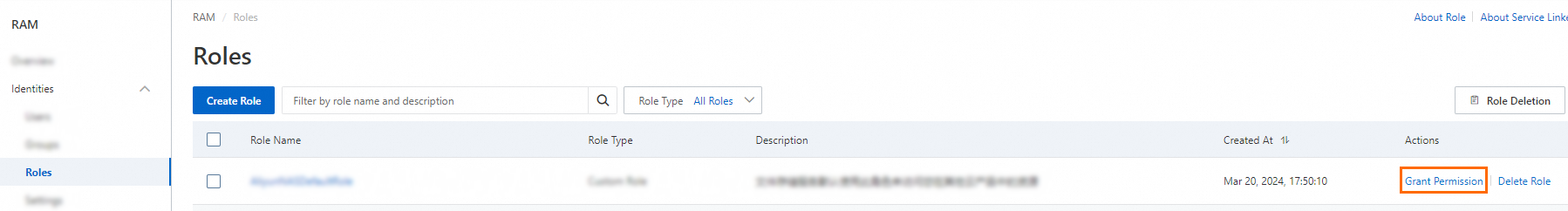
Tip: Select multiple RAM roles and click Grant Permission at the bottom of the list to grant permissions in bulk.
In the Grant Permission panel, configure the following settings:
Resource Scope: Choose the authorization scope.
Account: The authorization applies to the entire Alibaba Cloud account.
Resource Group: The authorization applies to a specific resource group.
Note: If you select Resource Group, make sure that the target cloud service supports resource groups. For more information, see Services that work with Resource Group.
Principal: The current RAM role is automatically selected.
Policy: Select one or more policies to attach. You can select multiple policies at a time.
System policies: Predefined by Alibaba Cloud and not editable. For more information, see Services that work with RAM.
Note: The system flags high-risk policies such as
AdministratorAccessandAliyunRAMFullAccess. Avoid attaching these unless necessary.Custom policies: Created and managed by you. For more information, see Create a custom policy.
Click Grant permissions.
Click Close.
Step 3: Create a RAM user (accessing account)
Create a RAM user under the accessing account. This user will assume the RAM role created in Step 1.
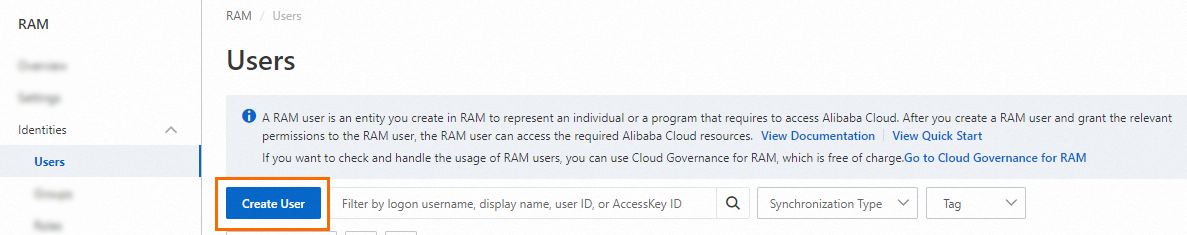
Log on to the RAM console with the accessing account's Alibaba Cloud account or a RAM user with administrative rights.
In the left-side navigation pane, choose Identities > Users.
On the Users page, click Create User.
In the User Account Information section, configure the following parameters:
Logon Name: Up to 64 characters. Supports letters, digits, periods (.), hyphens (-), and underscores (_).
Display Name: Up to 128 characters.
Tag: Click the
 icon and enter a tag key-value pair. Tags help you organize and manage RAM users.
icon and enter a tag key-value pair. Tags help you organize and manage RAM users.
Tip: Click Add User to create multiple RAM users at a time.
In the Access Mode section, select an access mode.
To keep credentials separate, select only one access mode per RAM user.
Console Access (for human users)
Allows the RAM user to log on with a username and password. Configure the following options:
Set Console Password: Choose Automatically Regenerate Default Password or Reset Custom Password. For custom passwords, the password must meet complexity requirements. For more information, see Configure a password policy for RAM users.
Password Reset: Whether the user must reset the password on next logon.
Enable MFA: Whether to enable multi-factor authentication (MFA). If enabled, bind an MFA device to the user. For more information, see Bind an MFA device to a RAM user.
Using permanent AccessKey to access (for programmatic access)
The system generates an AccessKey ID and AccessKey secret for API access. For more information, see Obtain an AccessKey pair.
ImportantThe AccessKey secret is displayed only at creation time. Save it immediately. For production workloads, use Security Token Service (STS) tokens instead of permanent AccessKey pairs to reduce credential leak risks. For more information, see Best practices for using an access credential to call API operations.
Click OK.
Complete security verification as prompted.
Step 4: Grant the AssumeRole permission to the RAM user (accessing account)
Attach the AliyunSTSAssumeRoleAccess policy to the RAM user so it can assume the resource owner's RAM role.
Log on to the RAM console as a RAM administrator.
In the left-side navigation pane, choose Identities > Users.
On the Users page, find the target RAM user and click Add Permissions in the Actions column.

Tip: Select multiple RAM users and click Add Permissions at the bottom of the page to grant permissions in bulk.
In the Grant Permission panel, configure the following settings:
Resource Scope: Choose the authorization scope.
Account: The authorization applies to the entire Alibaba Cloud account.
ResourceGroup: The authorization applies to a specific resource group.
ImportantImportant: If you select ResourceGroup, make sure that the target cloud service supports resource groups. For more information, see Services that work with Resource Group. For more information about how to grant permissions on a resource group, see Use a resource group to grant a RAM user the permissions to manage a specific ECS instance.
Principal: The current RAM user is automatically selected.
Policy: Search for and select the
AliyunSTSAssumeRoleAccesssystem policy.System policies: Predefined by Alibaba Cloud and not editable. For more information, see Services that work with RAM.
Note: The system flags high-risk policies such as
AdministratorAccessandAliyunRAMFullAccess. Avoid attaching these unless necessary.Custom policies: Created and managed by you. For more information, see Create a custom policy.
Click Grant permissions.
Click Close.
Verify cross-account access
After completing the setup, the RAM user from the accessing account can access the resource owner's cloud resources through the console or API.
Log on to the console
Open the Alibaba Cloud Management Console and log on as the RAM user.
On the RAM User Logon page, enter the username in one of the following formats and click Next:
Format Example <UserName>@<AccountAlias>.onaliyun.com(default domain)alice@company-alias.onaliyun.com<UserName>@<AccountAlias>(account alias)alice@company-alias<UserName>@<DomainAlias>(domain alias, if configured)alice@example.com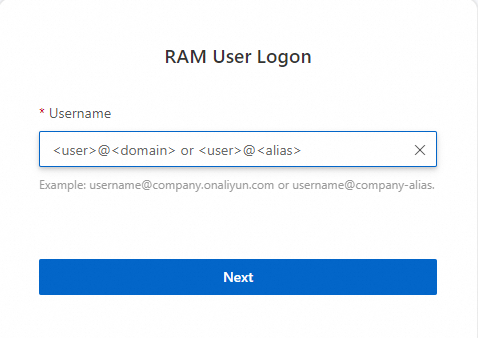
For more information about domain names and aliases, see Terms, View and modify the default domain name, and Create and verify a domain alias.
Enter the logon password and click Log On.
(Optional) If MFA is enabled, complete multi-factor authentication.
For more information, see Multi-factor authentication (MFA) and Bind an MFA device to a RAM user.
Call API operations
To access the resource owner's cloud resources through API calls, the RAM user must first call the STS AssumeRole operation to get a temporary security token. Use the returned AccessKeyId, AccessKeySecret, and SecurityToken in your API requests.
What's next
Create a custom policy to define fine-grained permissions for the RAM role
Use a RAM role to grant permissions across Alibaba Cloud accounts for detailed RAM role delegation guidance
Best practices for using an access credential to call API operations to secure your credential usage