Deploy one or more SSL certificates to Alibaba Cloud services — individually, in bulk, or on a schedule. This topic covers deployment through the Certificate Management Service console to services such as ALB, NLB, CDN, DCDN, WAF, OSS, and ACK.
To deploy a certificate to an Elastic Compute Service (ECS) instance or Simple Application Server, see Update an existing certificate on an Alibaba Cloud ECS instance or a Simple Application Server instance.
Prerequisites
Before you begin, confirm all of the following:
Your certificate is purchased and applied for in Certificate Management Service, and its Status is Issued. See Purchase a commercial certificate and Apply for a certificate.
The alias of the issued SSL certificate contains no Chinese characters.
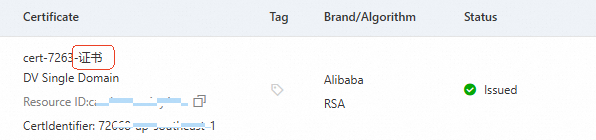
The certificate Status is Issued. If the status is About to Expire or Expired, renew the SSL certificate before proceeding.
The Bound Domains on the certificate match the domain names you want to protect. A mismatch causes a browser security warning when users access the domain over HTTPS. To add or change a domain name, see Add and replace domain names.
Domain matching rules
The Bound Domains of a certificate can include exact and wildcard domain names:
Exact domain name — takes effect only for the specified domain name.
example.comcovers onlyexample.com.www.example.comcovers onlywww.example.com.
Wildcard domain name — takes effect only for first-level subdomains.
*.example.comcoverswww.example.comanda.example.com.*.example.comdoes not cover the root domainexample.comor multi-level subdomains such asa.b.example.com.
To match a multi-level subdomain, Bound Domains must include that specific domain name (for example,a.b.example.com) or a corresponding wildcard domain name (for example,*.b.example.com).
Supported cloud services
The following table lists the cloud services that support certificate deployment through Certificate Management Service for international certificates.
If a cloud service is not listed, deploy the certificate directly from that service's console.
In the following table, Update existing certificate refers to scenarios where a cloud service already has a certificate deployed and you need to replace it.
| Cloud service | Supported deployment scenarios | Certificate configuration |
|---|---|---|
| Container Service for Kubernetes (ACK) | Update existing certificate | ACK managed and dedicated clusters: AlbConfig certificate configuration, Secret certificate. Important Do not manually modify the Secret in the ACK console. |
| Serverless App Engine — gateway routing | Update existing certificate | Gateway routing with HTTPS forwarding protocol (ALB and CLB) |
| Function Compute (FC) | Update existing certificate | HTTP-triggered function |
| Microservices Engine — cloud-native gateway | Update existing certificate | Cloud-native gateway routing |
| API Gateway | Update existing certificate | API access via HTTPS domain name |
| Global Accelerator (GA) | Update existing certificate | HTTPS domain name with secure acceleration |
| Application Load Balancer (ALB) | Update existing certificate | HTTPS listener (server certificate). To deploy a client certificate, see Configure end-to-end HTTPS to encrypt communication. |
| Network Load Balancer (NLB) | Update existing certificate | HTTPS listener (server certificate) |
| Content Delivery Network (CDN) | Initial deployment, update existing certificate | HTTPS secure acceleration |
| Dynamic Content Delivery Network (DCDN) | Initial deployment, update existing certificate | HTTPS secure acceleration |
| Edge Security Acceleration (ESA) | Update existing certificate | HTTPS secure acceleration |
| Object Storage Service (OSS) | Update existing certificate | Accessing OSS via HTTPS. Note If a CDN-accelerated domain name is bound to the bucket, replace the certificate in the CDN console instead. |
| Web Application Firewall (WAF) | Update existing certificate | Onboarding via proxy mode |
| Anti-DDoS Proxy | Update existing certificate | Anti-DDoS Proxy domain name access |
| Platform for AI (PAI) | Update existing certificate | Elastic Algorithm Service (EAS) for online model services: dedicated gateway with a custom domain name |
Step 1: Purchase a deployment quota
Only Uploaded Certificates consume deployment quota. For all other certificate types, skip to Step 2: Check authorizations.
| Rule | Details |
|---|---|
| Certificates other than Uploaded Certificates | Do not consume quota |
| Certificates shared between accounts belonging to the same verified individual or enterprise | Do not consume quota |
| Failed deployments | Quota is refunded |
If your quota is insufficient, purchase a deployment package.
Step 2: Check authorizations
This step applies only to ACK deployments. For all other cloud services, skip to Step 3: Deploy certificates.
Before deploying a certificate to ACK, log on to the ACK console with your Alibaba Cloud account and grant the AliyunCASDefaultRole role permissions to manage the destination cluster. Without this permission, Certificate Management Service cannot detect the cluster namespace.
Go to ACK Authorization Management. On the RAM Roles tab, enter
AliyunCASDefaultRoleand click Modify Permissions.On the Permission Management tab, grant the O&M Engineer permission to the destination cluster.

Step 3: Deploy certificates
Deploy a single certificate
If this is your first time using the deployment service, grant access as prompted. For details, see Grant permissions to access cloud resources.
Log in to the Certificate Management Service console.
In the left navigation pane, choose Certificate Management > SSL Certificate Management.
On the SSL Certificate Management page, click the appropriate certificate tab, find your certificate, and click Deploy in the Actions column.
Certificates issued by a Private CA are synchronized to the Uploaded Certificates tab.
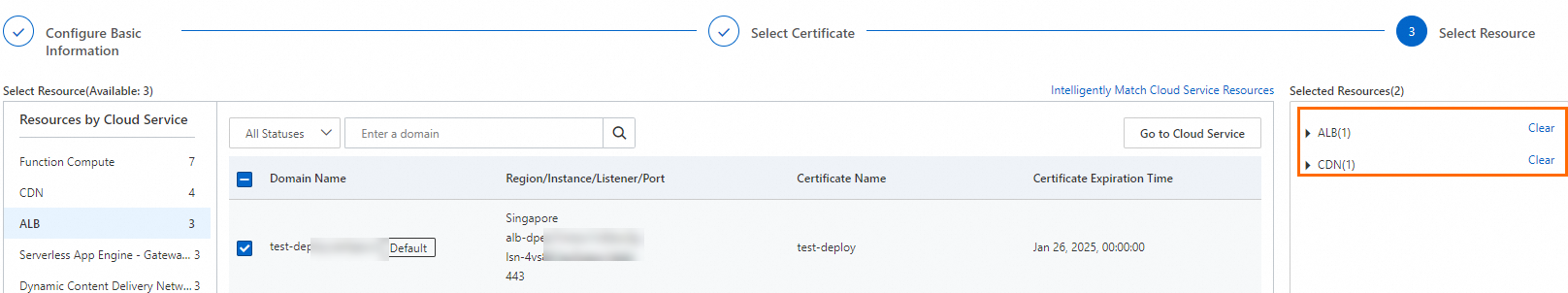
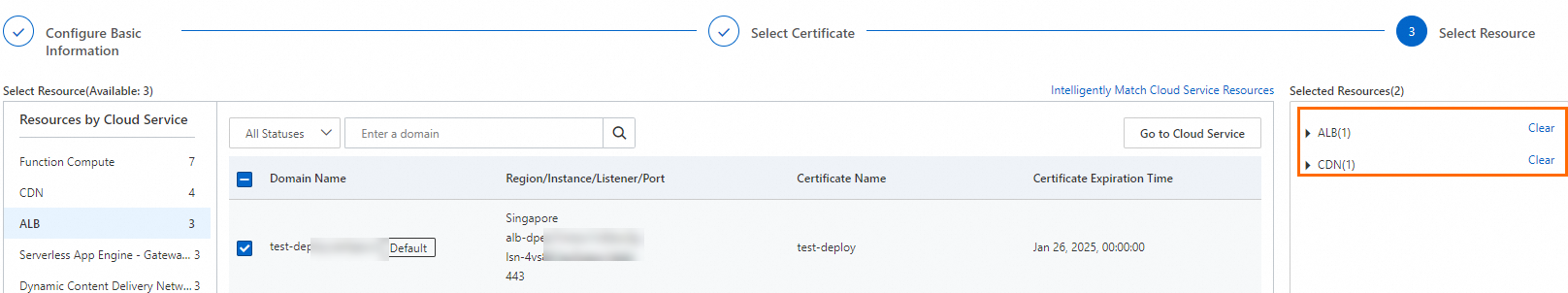
On the Select Resource step of the Create Task page, select or adjust the cloud services and resources, then click Preview and Submit.
The system automatically matches cloud service resources that already have an SSL certificate configured. In the automatic matching dialog box, click OK. The matched resources are added to the Selected Resources area, which you can adjust as needed.
If a resource does not appear, check the Total Resources section. Resources shown in a grayed-out state are still syncing — wait for the process to finish. Sync time depends on the number of resources in your cloud services.
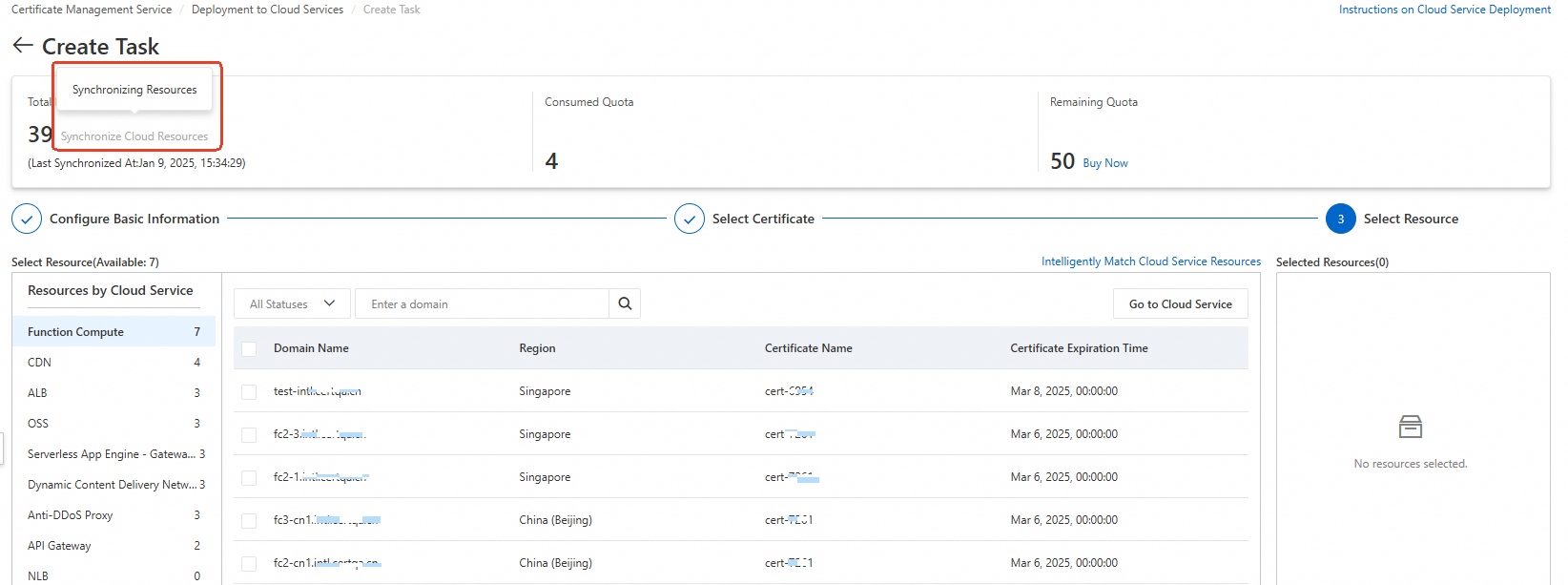
If the resource still does not appear after sync completes, confirm that you have met all deployment prerequisites.
In the Task Preview panel, confirm the certificate instances and cloud service resource details, then click Submit. The preview shows the number of matching certificates per cloud service and the deployment quota to be consumed. A match count of 0 means the selected certificate does not match the cloud service resource — the deployment will fail. Verify your selection before submitting.
Deploy multiple certificates
If this is your first time using the deployment service, grant access as prompted. For details, see Grant permissions to access cloud resources.
Log in to the Certificate Management Service console.
In the left navigation pane, choose Deployment and Resource Management > Deployment to Cloud Services.
On the Deployment to Cloud Services page, click Create Task and complete the following steps.
a. Configure basic information
Parameter Description Task Name A custom name for the deployment task Contact Contacts to receive deployment notifications. Up to 10 contacts. Deployment Time Deploy Now: deploys immediately. Custom Time: schedules the task for a specific time. Click Next.
b. Select certificates
Select the SSL certificates for your cloud resources, then click Next.
Certificates issued by a Private CA are on the Uploaded Certificates tab.
A single deployment task can include only one certificate type.
c. Select resources
Select or adjust the cloud services and resources, then click Preview and Submit.
Bulk deployment is not supported for SLB listeners with multiple server certificates.
The system automatically matches resources that already have an SSL certificate configured. Click OK in the matching dialog box to add them to the Selected Resources area.
If a resource does not appear, check the Total Resources section. A grayed-out state means sync is still in progress — wait for it to finish.
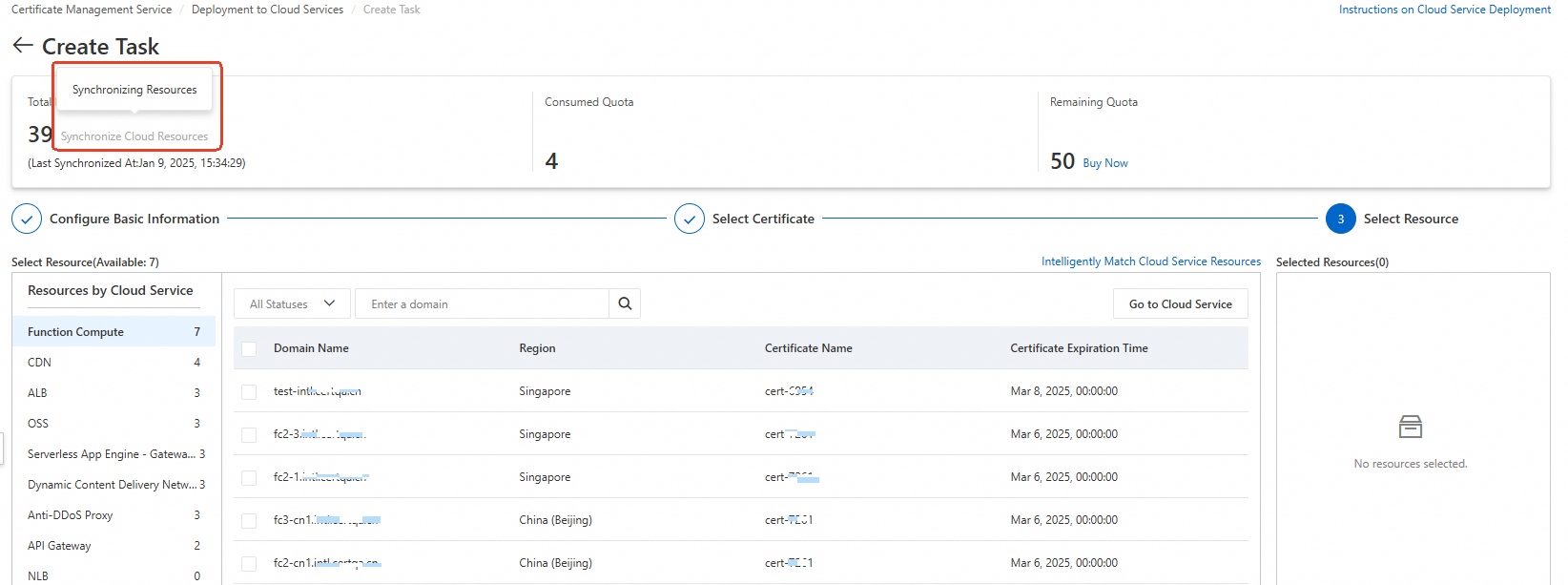
If the resource still does not appear after sync completes, confirm that your scenario supports initial deployment. See Prerequisites.
d. Review and submit
In the Task Preview panel, confirm the certificate instances and resource details. A match count of 0 means the certificates do not match the selected resources — the deployment will fail. Verify your selection, then click Submit.
More operations
View deployment task details
On the Deployment to Cloud Services page, find the task and click Details in the Actions column.
On the task details page, view the deployment status for each resource. For failed resources, the failure reason is shown in the Actions column.
If you cannot determine the failure reason, contact your account manager.
Roll back a deployment task
Deployment quota is not refunded after a successful rollback.
To revert a deployment — for example, if the wrong certificate was deployed — roll back to the state before deployment began:
On the Deployment to Cloud Services page, find the task and click Details in the Actions column.
On the task details page, click the cloud service, find the resource, and click Roll Back in the Actions column.
After a successful rollback, the task status changes to Rolled Back.
Delete a deployment task
Deleted tasks cannot be recovered.
On the Deployment to Cloud Services page, find the task and click Delete in the Actions column. To delete multiple tasks at once, select them and click Delete at the bottom of the list.
FAQ
Can I deploy SSL certificates across different Alibaba Cloud accounts?
SSL certificates cannot be deployed directly across accounts.
If the accounts belong to the same individual or enterprise that has completed identity verification, use the certificate sharing feature for free cross-account deployment. See Upload, sync, and share SSL certificates.
If the accounts belong to different entities, download the certificate from the original account, then manually upload and deploy it in the target account.
Does deploying a certificate automatically enable HTTPS on the cloud service?
No. A successful deployment means the certificate has been delivered to the cloud service. Go to that service's console to enable and configure HTTPS.
Why does the resource count show 0 during deployment?
The system automatically discovers resources when you create a deployment task. If a resource does not appear:
Check the Total Resources section. A grayed-out state means sync is still in progress — wait for it to finish.
If the resource still does not appear after sync completes, check whether your scenario supports initial deployment. If not, deploy the certificate from the corresponding cloud service's console first. See initial configuration.