Learn how to configure security rules for branches.
Branches
You can configure security rules for these branches:
Default branch: Serves as the base for cloning, branch creation, merge requests. Default branch settings are configurable to administrators.
Protected branch: Unauthorized operations, like deletion and force push, are not allowed, so as to ensure branch security and commit traceability.
Where to configure
Log on as repository administrator, go to the code repository details page, and navigate to .
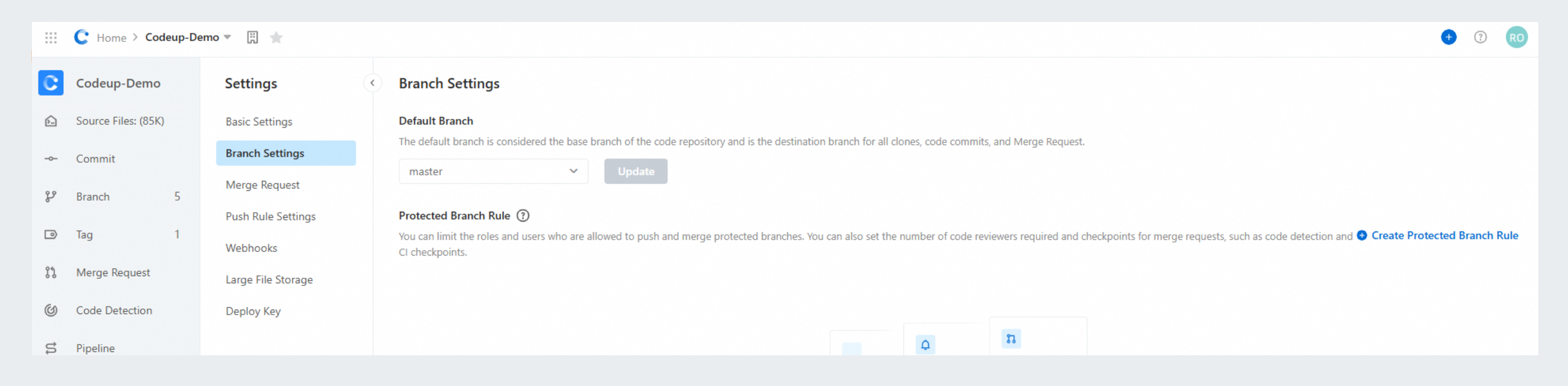
Configure security rules for protected branches
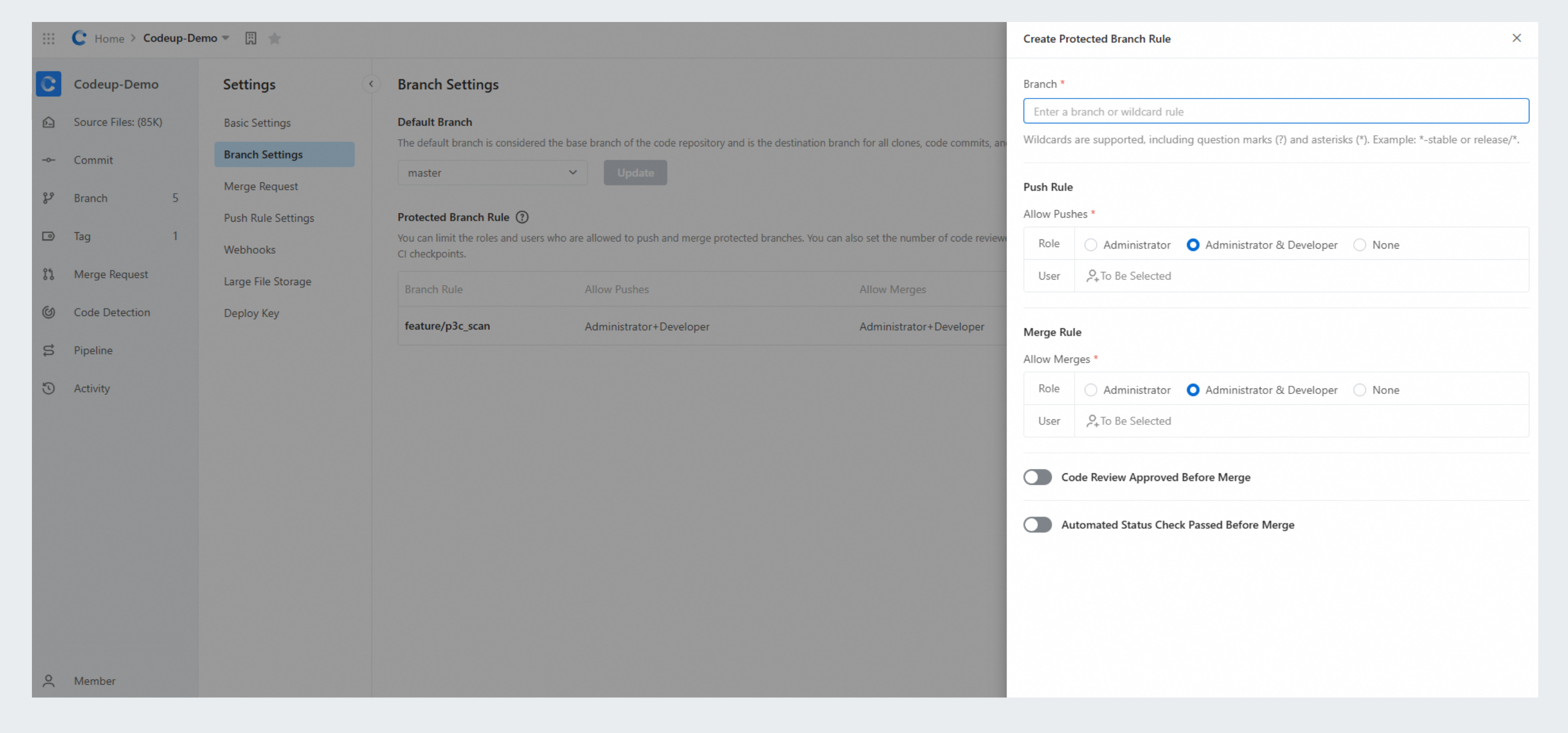
Step 1: Select a branch
Use either of the following methods to select a branch:
Specify the branch name.
Use wildcard patterns to match branches. Only question marks (?) and asterisks (*) are supported. All matched branches will be displayed.
Question: Which rule is the effective one if multiple rules are matched?
Answer: The rule containing a specific branch name has the highest priority. If a branch matches multiple wildcard rules, the earliest created rule takes priority. To explain this further, assume a code repository contains the master, master-1, and master-prod-1 branches, and you specify the rmaster-*, master-1, and master-prod-* rules in order. The following table lists the matching between the branches and rules.
Branch name | Rule that can be matched | Effective rule |
master-1 | master-* and master-1 | master-1 |
master-2 | master-* | master-* |
master-prod-1 | master-* and master-prod-* | master-* |
Step 2: Configure push rules
Specify the roles or members that are allowed for protected branch push.
For role:
By default, managers and developers are allowed.
If you deselect a role, it is not allowed for push.
If you select None, no users are allowed for push.
For member:
Select members from the code repository. Note that the settings take effect only if the selected members have write permissions on the code repository.
Step 3: Configure a merge rule
Specify roles or members allowed to perform a merge operation on a merge request.
For role:
By default, managers and developers are allowed.
If you deselect a role, it is not allowed to perform a merge operation.
For member:
Select members from the code repository. Note that the settings take effect only if the selected members have write permissions on the code repository.
The roles and members specified by the preceding rules take effect simultaneously. For example, if rule A says that only administrators can push and rule B says that user C can push, then both of them are allowed to push, even though user C is not an administrator.
Step 4: Configure approval rules for code review
Configure manual approval rules
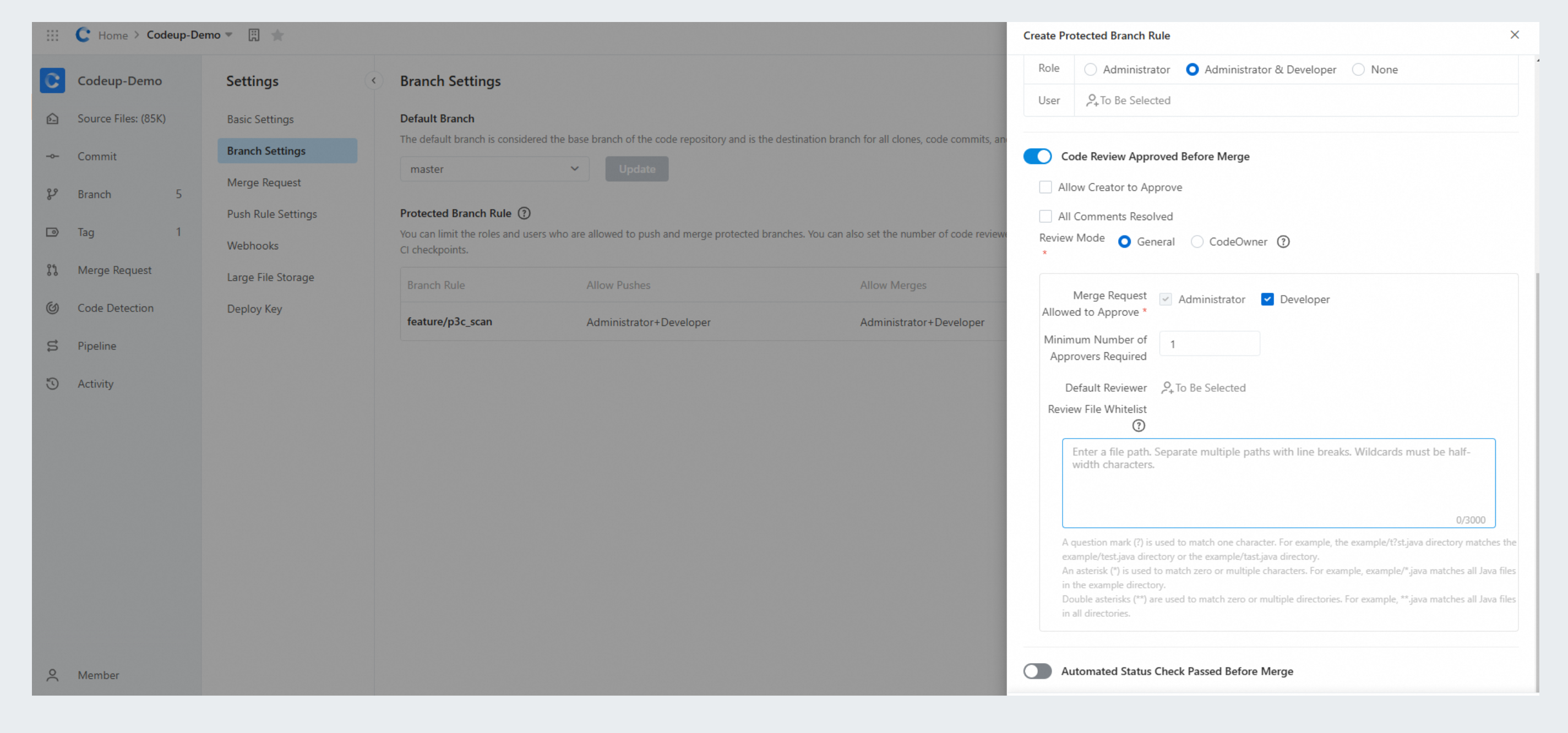
The following approval rules for code review are supported:
Allow Creator to Approve: Yes/No.
All Comments Resolved: Yes/No.
The following code review modes are supported:
General
Minimum Number of Approvers Required: 1.
Merge Request Allowed to Approve: Administrator or Developer.
Default Reviewer: If not specified, it is not displayed. Up to 20 reviewers are allowed.
CodeOwner
For more information, see CodeOwner mechanism.
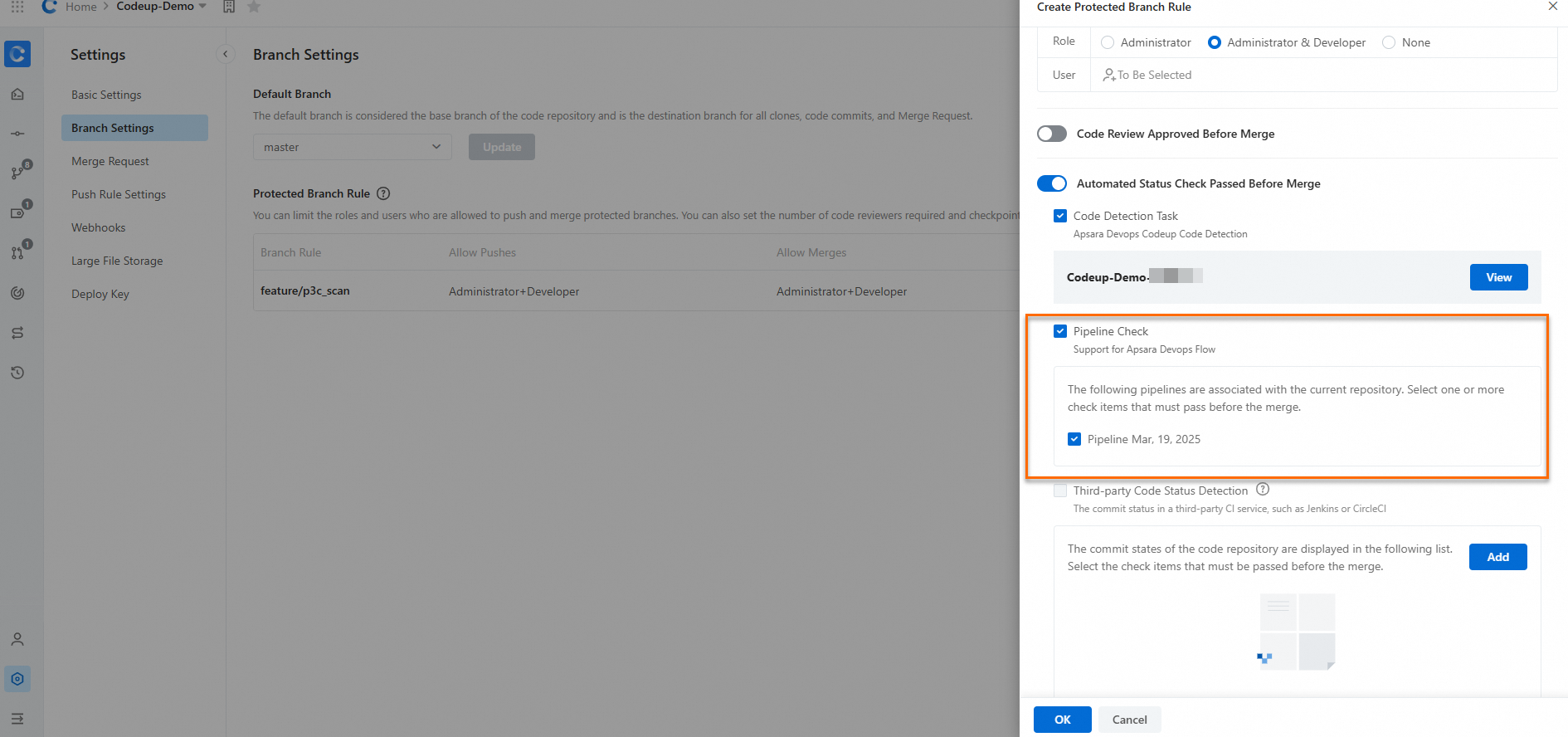
Configure approval rules of automation check
Code scanning
If Automated Status Check Passed Before Merge is not enabled , the code detection service cannot be launched.
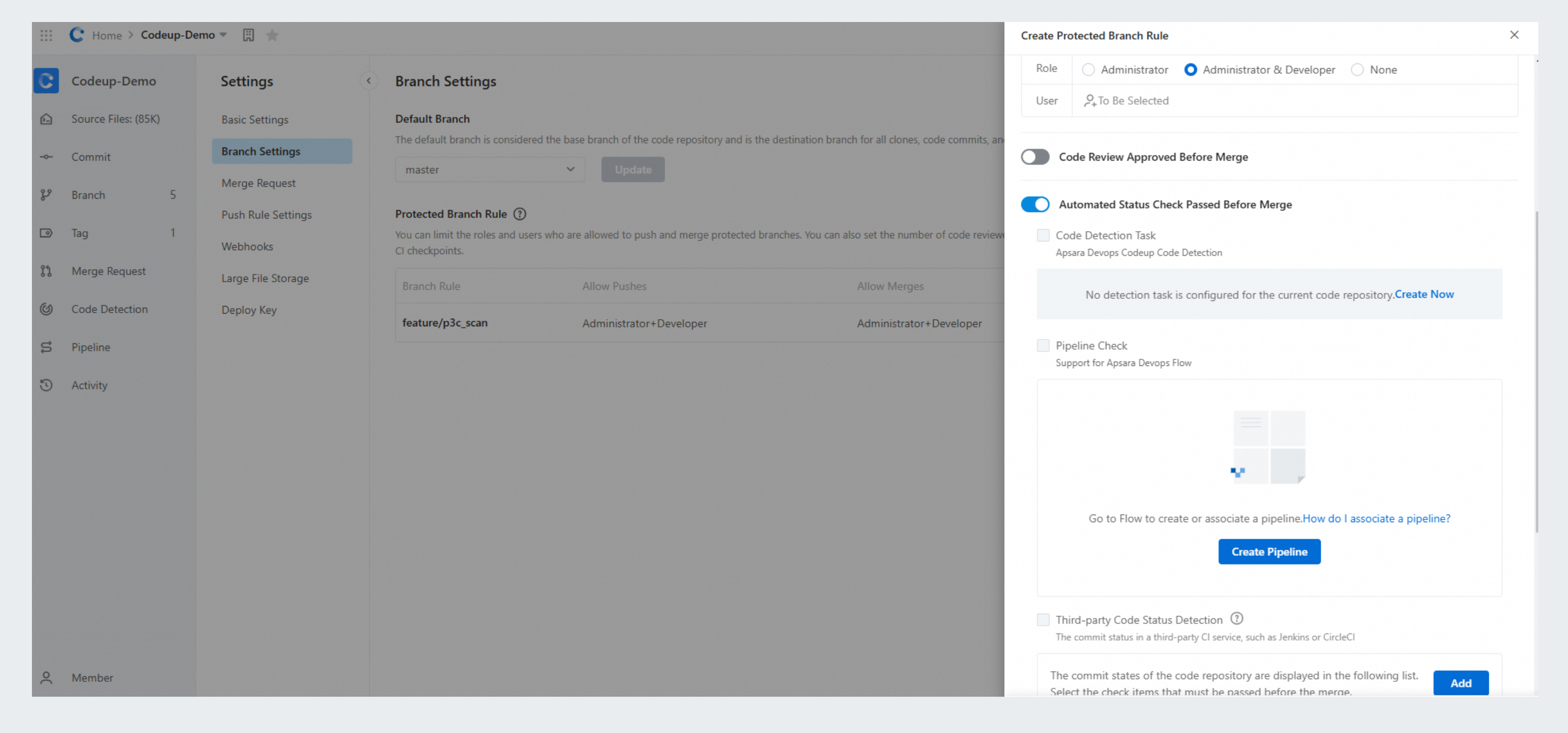
When a code scan service is enabled, it will check code accordingly.
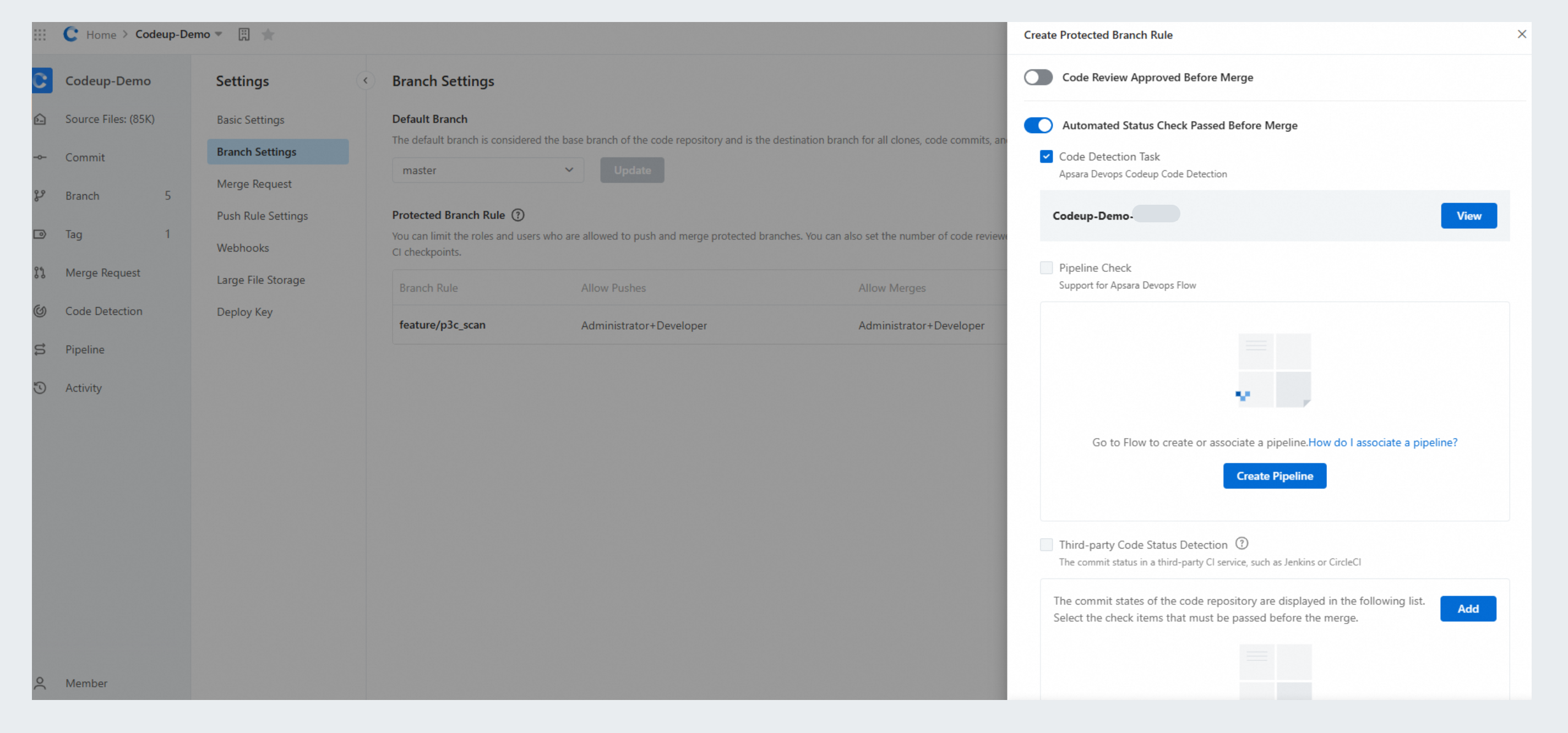
Pipeline check
A protected branch is allowed to be associated with pipelines.
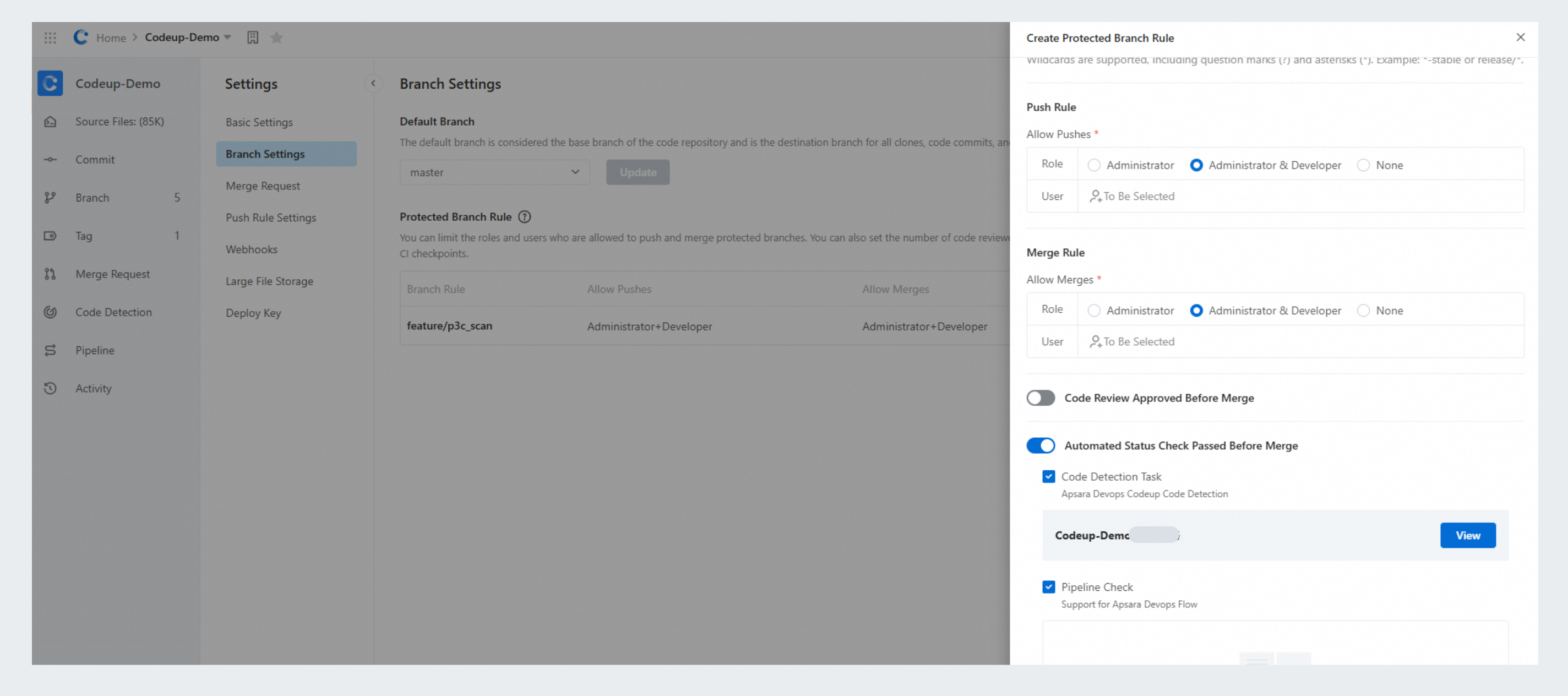
If the code repository has never been associated with a pipeline before, associate one or create one in Alibaba Cloud DevOps Flow.
To trigger a pipeline check when code is committed, select Submit Code during pipeline selection. Otherwise, you have to manually trigger the check every time.
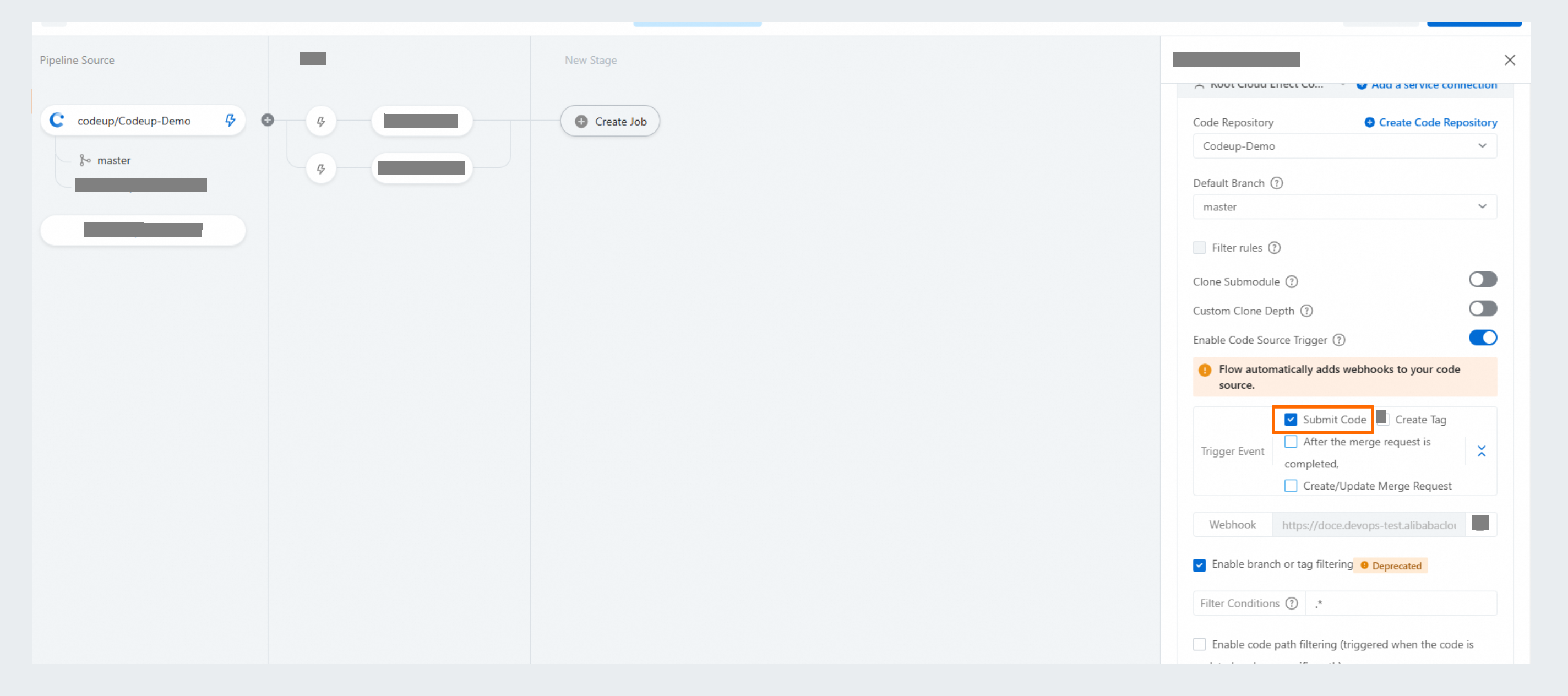
Associated pipelines will be listed as shown in the following figure. Select a pipeline to apply its checks to all the merge requests to the protected branch. Merge requests will be approved only when all the checks have passed. If the selected pipeline is not running, the relevant merge requests will not be approved.