If your business is based on native iOS or Android apps (excluding H5 pages used in the apps), you can create a Bot-App protection template to customize protection rules and defend against app bots.
Create a template
If you enable the JavaScript Validation or Slider CAPTCHA protection action, Web Application Firewall (WAF) initiates a JavaScript check or slider verification for a client whose traffic hits a rule. After the client is authenticated, WAF inserts the acw_sc__v2 and acw_sc__v3 cookies into the HTTP message header, respectively, to confirm that the client has passed verification.
Log on to the Web Application Firewall 3.0 console, and in the top menu bar, select the resource group and region for your WAF instance. The region can be Chinese Mainland or Outside Chinese Mainland.
In the navigation pane on the left, select , and click Create Template. On the Configure Scenarios page, configure the parameters and click Create Template.
Enter a Template Name and Template Description.
Select the Traffic Characteristics. You can choose between Global and Customize Match Conditions.
Global: Applies to scenarios that involve only web or H5 environments.
Customize Match Conditions: Applies to scenarios that involve app or miniapp environments in addition to web or H5 environments, or scenarios where you need to protect specific business endpoints, such as logon or flash sale endpoints.
Global
If you select Global, you do not need to define specific match conditions.
Customize Match Conditions
WAF matches requests based on the conditions you define. Click Add Condition to add a condition. Each condition consists of a Match Field, a Logical Operator, and the Match Content. The following table provides configuration examples.
NoteIf a rule has multiple conditions, a request must meet all of them (a logical AND) to hit the rule. For more information about match fields and logical operators, see Match conditions.
Match Field
Logical Operator
Match Content
Description
URI Path
Contains
/login.phpMatches if the request path contains
/login.php.IP
Belongs to
192.1.XX.XXMatches if the client IP is
192.1.XX.XX.
Select whether to Exclude Static Files. Requests for static files usually do not involve business logic, and their content is not susceptible to injection attacks. Excluding static files can reduce the detection workload and allow WAF to focus on protecting dynamic APIs. We recommend selecting the default static file types. You can also add custom types.
On the Edit page, configure the following parameters and click Next.
Configuration item
Description
Risk Identification
In the Risk Identification section, you can click Create to create a fraud detection rule. This feature blocks access from suspicious phone numbers by checking them against WAF's built-in phone number reputation database. It is suitable for scenarios such as phone number-based logon and registration. For more information, see Fraud Detection.
Policy Configurations
Click the
 icon in the Status column of the target rule to enable or disable the rule.
icon in the Status column of the target rule to enable or disable the rule.Click Edit in the Status column of the destination rule to modify the rule.
Actions
Configuration
Description
JavaScript Validation
WAF returns a block of JavaScript validation code to the client. A standard browser automatically executes this code. If the client completes execution successfully, WAF allows all requests from that client for a period of time (30 minutes by default). Otherwise, the requests are blocked.
Block
Blocks requests that match the rule and returns a block page to the client.
NoteWAF uses a default block page. You can also create a custom block page using the Custom Response feature.
Monitor
Does not block requests that match the rule but logs them. When testing a rule, you can first use the Monitor mode to analyze WAF logs and confirm that no false positives occur before changing the action.
Slider CAPTCHA
WAF returns a slider CAPTCHA page to the client. If the client successfully completes the slider challenge, WAF allows all requests from that client for a period of time (30 minutes by default). Otherwise, the requests are blocked.
Strict Slider CAPTCHA Verification
WAF returns a slider CAPTCHA page to the client. If the client successfully completes the slider challenge, the current request is allowed. Otherwise, the request is blocked. In this mode, the client must complete a slider challenge for every request that matches the rule.
Add Tag
You can define a custom header name and content (including rule type, rule ID, and web UMID). WAF does not process the request directly but instead adds a header to forward the match information to the origin server. You can integrate this with your backend risk control system for business-side processing.
Canary Release
Configure the percentage of objects, based on different dimensions, to which the rule applies.
After you enable rule grayscale, you also need to set the grayscale Dimension and Canary Release Proportion. The grayscale Dimension include the following: IP, Custom Header, Custom Parameter, Custom Cookie, Session, and App UMID.
NoteA canary release takes effect based on the configured Dimension, not by randomly applying the rule to a percentage of requests. For example, if the Dimension is IP and the Canary Release Proportion is 10%, WAF selects approximately 10% of the IP addresses. WAF then applies the rule to all requests from these selected IP addresses, not to a random 10% of all requests.
Effective Mode
Permanently Effective (Default): The rule is always active when the protection template is enabled.
Fixed Schedule: The protection rule is active only during a specified time period.
Recurring Schedule: The protection rule is active only during a specified recurring schedule.
On the Configure Effective Scope page, select the protected objects or protected object groups, click the
 icon to add them to the Selected area, and then click OK.
icon to add them to the Selected area, and then click OK.Integrate the app SDK (Important)
ImportantBot protection capabilities rely on information collected by the SDK. Without SDK integration, you will not receive full protection.
WAF provides an SDK for native apps to enhance protection in this scenario. After integration, the SDK collects client risk features and generates a security signature to include in requests. WAF uses this signature to detect and block risky requests.
Follow these steps to integrate the app SDK:
Submit a ticket to obtain the SDK.
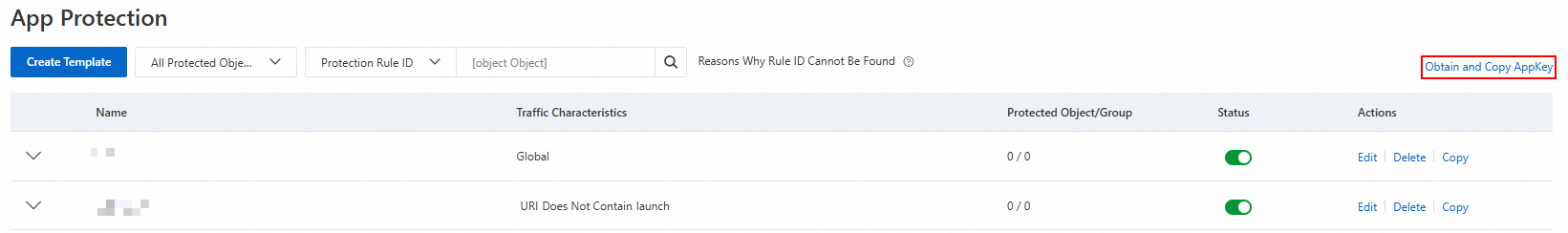
Click Obtain and Copy AppKey to initiate SDK initialization.
Integrate the app SDK. For more information, see the SDK Integration Guide.
Manage templates
Edit a template
Click Edit in the Actions column for the target template. Modify the template in the Edit panel.
Delete a template
Click Delete in the Actions column for the target template. In the Delete dialog box, confirm the information and click OK.
Copy a template
Click Copy in the Actions column for the target template. In the Copy dialog box, confirm the information and click OK.
Enable or disable a template
Click the switch in the Status column for the target template to enable or disable it.
View rules
Click the
 icon for the target template to view its rules. Click the switch in the Status column for a specific rule to enable or disable it.
icon for the target template to view its rules. Click the switch in the Status column for a specific rule to enable or disable it.