The Log Service for WAF feature includes three built-in dashboards—Operation Center, Access Center, and Security Center—that display real-time log analysis results as charts. To view website traffic and security data, select a time range on a dashboard. No query statement is required.
Which dashboard to use
| Dashboard | Use it to |
|---|---|
| Operation Center | Check your website's overall health, including traffic protection data and attack summaries |
| Access Center | Analyze access patterns, including traffic trends, request distribution, and client behavior |
| Security Center | Investigate attacks, including attack targets, trends, and the geographic distribution of attack sources |
You can also manually create dashboards for your own query and analysis scenarios, then add custom charts based on your commonly used query statements. For more information, see Overview of visualization.
Prerequisites
Before you begin, ensure that you have:
Enabled the Log Service for WAF feature. For details, see Get started with the Simple Log Service for WAF feature
Enabled log collection for the domain names you want to monitor (step 3 below)
View a dashboard
Log on to the WAF console. In the top navigation bar, select the resource group and the region where your WAF instance is deployed. The region can be Chinese Mainland or Outside Chinese Mainland.
In the left-side navigation pane, choose Security Operations > Log Service.
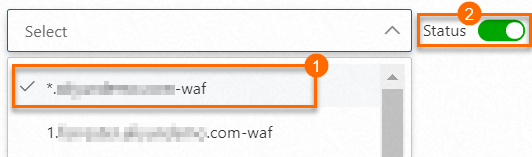
Select a domain name from the domain name drop-down list and turn on Status to enable log collection for the domain name.
Click the Log Analysis tab.
Click Operation Center, Access Center, or Security Center, then specify a time range to query data.
What's next
Specify a time range
Each dashboard and chart reads from raw log data within a time range. Two types of time selectors are available:
Dashboard time selector: Applies to all charts on the current dashboard. Click the dashboard tab, then click Time Range. In the Time panel, select a relative time, a time frame, or a custom range. The selected range applies only to the current dashboard—switch to another dashboard and you must specify a new time range.
Chart time selector: Applies to a single chart. Move the pointer over the
 icon in the upper-right corner of a chart, then select Select Time Range. In the Time panel, select a time range for that chart.
icon in the upper-right corner of a chart, then select Select Time Range. In the Time panel, select a time range for that chart.
By default, no time range is set when you open the Log Analysis tab. Specify a time range before reading dashboard data.
Subscribe to a dashboard
Subscribe to a dashboard to receive chart data automatically by email or DingTalk group message on a regular schedule. In the upper-right corner of a dashboard, click Subscribe and complete the Create Subscription wizard. For details, see Subscribe to a dashboard.
Drill down into chart data
Drill-down is pre-configured on specific charts, indicated by underlined numbers. Click an underlined number to see the underlying data. For example, clicking the underlined number in the Attacked Hosts chart of the Security Center dashboard shows which domain names were attacked and how many times.
To check whether drill-down is available for a chart, move the pointer over the ![]() icon in the upper-right corner. If the
icon in the upper-right corner. If the ![]() icon appears, drill-down is configured.
icon appears, drill-down is configured.
Switch to the Raw Logs tab to view unprocessed log entries. For details, see Configure an interaction occurrence for a dashboard to perform drill-down analysis.
Download chart data
Move the pointer over the ![]() icon in the upper-right corner of a chart, then select Download Chart or Download Chart Data to save the data as a CSV file.
icon in the upper-right corner of a chart, then select Download Chart or Download Chart Data to save the data as a CSV file.
Preview a chart's query statement
Move the pointer over the ![]() icon in the upper-right corner of a chart, then select the
icon in the upper-right corner of a chart, then select the ![]() icon to see the query statement behind the chart.
icon to see the query statement behind the chart.
Charts supported by the built-in dashboards
For an overview of chart types, see Chart overview.
Operation Center
Displays the overall status of a website, including traffic protection data and an attack overview.
| Chart name | Chart type | Default time range | Description | Example value |
|---|---|---|---|---|
| User Request | Single value chart | Compared with last day | Number of page views (PVs) and unique visitors (UVs) | 48,300 |
| Peak Traffic | Single value chart | Compared with last day | Peak inbound and outbound Internet traffic and peak attack traffic. Unit: Kbit/s | 4.6 |
| Valid Request Ratio | Single value chart | Compared with last hour | Percentage of valid requests routed over the Internet and forwarded by WAF | 98.41% |
| Valid Traffic | Single value chart | Compared with last hour | Volume of traffic forwarded by WAF to the origin server. Unit: MB | 10.7 |
| Request Trend | Line chart | 1 week (relative) | Trends in request count, valid request ratio, and inbound/outbound bandwidth. Unit: Kbit/s | None |
| Attack Statistics | Single-value chart, world map, and China map | Compared with last hour | Number of attacks, traffic volume in KB, and geographic attack distribution | None |
| Attacker List | Table | 1 hour (relative) | IP addresses from which attacks originate | None |
| Top 100 Attacked Websites | Table | 1 hour (relative) | Top 100 domain names that received the most attacks | None |
Access Center
Displays access information for a website, including access metrics, traffic trends, and request distribution.
| Chart name | Chart type | Default time range | Description | Example value |
|---|---|---|---|---|
| PV | Single value chart | 1 hour (relative) | Total number of PVs | 100,000 |
| UV | Single value chart | 1 hour (relative) | Total number of UVs | 100 |
| Traffic In | Single value chart | 1 hour (relative) | Total inbound traffic. Unit: MB | 300 MB |
| Peak Network In Traffic | Single value chart | Today (time frame) | Peak inbound traffic. Unit: Kbit/s | 0.5 KB/s |
| Peak Network Out Traffic | Single value chart | Today (time frame) | Peak outbound traffic. Unit: Kbit/s | 1.3 KB/s |
| Traffic Network Trend | Area chart | Today (time frame) | Inbound and outbound traffic trends. Unit: Kbit/s | None |
| PV/UV Trends | Line chart | Today (time frame) | PV and UV trends over time | None |
| Access Status Distribution | Flow chart | Today (time frame) | Request trends by HTTP status code (such as 400, 304, and 200). Unit: count/h | None |
| Access Source | World map | 1 hour (relative) | Distribution of requests by country | None |
| Traffic In Source (World) | World map | 1 hour (relative) | Distribution of inbound traffic by country | None |
| Traffic In Source (China) | China map | 1 hour (relative) | Distribution of inbound traffic by province in China | None |
| Access Heatmap | AMAP | 1 hour (relative) | Geographic heat map of request sources | None |
| Network Provider Source | Pie chart | 1 hour (relative) | Distribution of requests by Internet service provider (ISP), including China Telecom, China Unicom, China Mobile, and China Education and Research Network | None |
| Referer | Table | 1 hour (relative) | Top 100 most frequently detected Referers, including Referer URLs, Referer hosts, and detection count | None |
| Mobile Client Distribution | Pie chart | 1 hour (relative) | Distribution of mobile client requests by client type | None |
| PC Client Distribution | Pie chart | 1 hour (relative) | Distribution of PC client requests by client type | None |
| Request Content Type Distribution | Pie chart | 1 hour (relative) | Distribution of requested resources by content type, including HTML, form, JSON, and streaming data | None |
| Accessed Sites | Treemap chart | 1 hour (relative) | Top 30 most frequently accessed domain names | None |
| Top Clients | Table | 1 hour (relative) | Top 100 clients by visit frequency, including IP address, region and city, network information, request method, inbound traffic, access errors, and attack count | None |
| URL With Slowest Response | Table | 1 hour (relative) | Top 100 URLs with the longest response times, including domain name, URL, average response time, and request count | None |
Security Center
Displays attack information for a website, including attack targets, trends, and the geographic distribution of attack sources.
| Chart name | Chart type | Default time range | Description | Example value |
|---|---|---|---|---|
| Peak Attack Size | Single value chart | 1 hour (relative) | Peak attack traffic. Unit: bit/s | 100 Bps |
| Attacked Hosts | Single value chart | Today (time frame) | Number of attacked websites | 3 |
| Source Country Of Attack | Single value chart | Today (time frame) | Number of countries from which attacks originate | 2 |
| Attack Traffic | Single value chart | 1 hour (relative) | Total traffic generated by attacks. Unit: bytes | 1 B |
| Attacker UV | Single value chart | 1 hour (relative) | Number of unique attacking visitors (UVs) | 40 |
| Attack type distribution | Flow chart | Today (time frame) | Distribution of attacks by attack type | None |
| Intercepted Attack | Single value chart | 1 hour (relative) | Total number of attacks blocked by WAF | 100 |
| CC Attack Interception | Single value chart | 1 hour (relative) | Number of HTTP flood attacks blocked by WAF | 10 times |
| Web Attack Interception | Single value chart | 1 hour (relative) | Number of web application attacks blocked by WAF | 80 |
| Access Control Event | Single value chart | 1 hour (relative) | Number of requests blocked by custom protection policies (ACL policies) | 10 times |
| CC Attack (World) | World map | 1 hour (relative) | Distribution of HTTP flood attacks by country | None |
| CC Attack (China) | China map | 1 hour (relative) | Distribution of HTTP flood attacks by province in China | None |
| Web Attack (World) | World map | 1 hour (relative) | Distribution of web application attacks by country | None |
| Web Attack (China) | China map | 1 hour (relative) | Distribution of web application attacks by province in China | None |
| Access Control Attack (World) | World map | 1 hour (relative) | Distribution of requests blocked by ACL policies by country | None |
| Access Control Attack (China) | China map | 1 hour (relative) | Distribution of requests blocked by ACL policies by province in China | None |
| Attacked Hosts | Treemap chart | 1 hour (relative) | Most frequently attacked websites | None |
| CC Attack Strategy Distribution | Pie chart | 1 hour (relative) | Distribution of attacks that triggered HTTP flood protection policies | None |
| Web Attack Type Distribution | Pie chart | 1 hour (relative) | Distribution of web attacks by attack type | None |
| Top Attackers | Table | 1 hour (relative) | Top 100 attacking clients, including IP addresses, province, carrier, attacks per type, and traffic volume | None |
| Attacker Referer | Table | 1 hour (relative) | Referer information for attacks, including Referer URLs, Referer hosts, and detection count | None |