This topic describes how to establish a seamless connection between Tablestore and MaxCompute across Alibaba Cloud accounts.
Prerequisites
Prepare two Alibaba Cloud accounts, Account A for Tablestore and Account B for MaxCompute. Use Account A to grant permissions to Account B to enable Account B to access all table data of Account A in Tablestore. The following table describes the basic information about the accounts.
The information in the table is for demonstration only. Replace the information with actual information during operations.
Item | Tablestore | MaxCompute |
Alibaba Cloud account name | Account A | Account B |
UID | 1234567890**** | 5678901234**** |
Before you use MaxCompute to access Tablestore, make sure that the following preparations are made:
Activate MaxCompute for Account B on the MaxCompute product details page and create a workspace. For more information, see Create a workspace.
Obtain the AccessKey pairs of Account A and Account B. For more information, see Obtain an AccessKey pair.
Use Account A to create a Resource Access Management (RAM) role for Account B and edit the trust policy of the RAM role. For more information, see Create a RAM role for a trusted Alibaba Cloud account and Edit the trust policy of a RAM role.
NoteIn the policy, 5678901234**** is the UID of Account B.
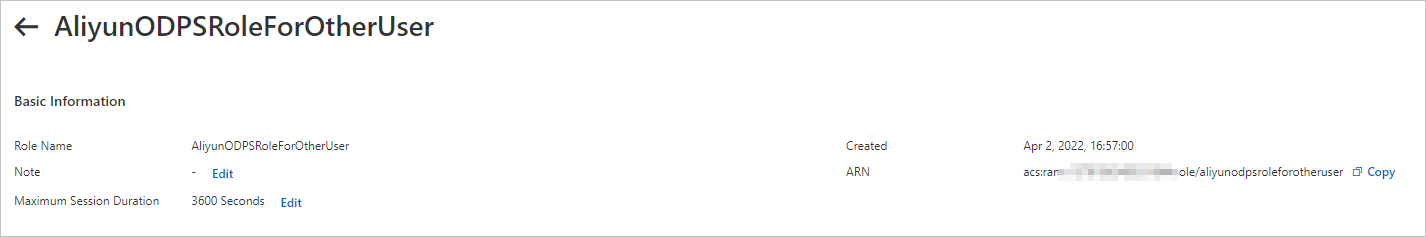
The following example shows a trust policy by assuming that the name of the created RAM role is AliyunODPSRoleForOtherUser. The example indicates that the RAM role can be assumed by MaxCompute under Account B.
{ "Statement": [ { "Action": "sts:AssumeRole", "Effect": "Allow", "Principal": { "Service": [ "5678901234****@odps.aliyuncs.com" ] } } ], "Version": "1" }Record the ARN of the AliyunODPSRoleForOtherUser role of Account A. Example: acs:ram::1234567890****:role/aliyunodpsroleforotheruser. The ARN is used to create an external table.
Create a policy and attach the policy to AliyunODPSRoleForOtherUser, which is the RAM role of Account A. For more information, see Create custom policies and Grant permissions to a RAM role.
The following example shows a custom policy where the RAM role has the permissions to read and write the following resources of Account A in the China (Hangzhou) region: an instance named cap1 and all tables that belong to cap1.
{ "Version": "1", "Statement": [ { "Effect": "Allow", "Action": "ots:*", "Resource": [ "acs:ots:cn-hangzhou:1234567890****:instance/cap1", "acs:ots:cn-hangzhou:1234567890****:instance/cap1/table/*" ], "Condition": {} } ] }For more information, see Create a custom policy.
In the Tablestore console, create an instance and a data table. For more information, see the Create a Tablestore instance and Create a data table.
In the preceding example, the following Tablestore instance and data table are created:
Instance name: cap1
Data table name: vehicle_track
Primary key information: vid (integer) and gt (integer)
Endpoint:
https://cap1.cn-hangzhou.ots-internal.aliyuncs.comNoteWhen you use MaxCompute to access Tablestore, we recommend that you use the private endpoint of Tablestore.
Set Access Type to Custom and select VPC, Classic Network, and Internet for Allowed Network Type and Trusted Gateway (Console) for Allowed Source Type for the instance.
Use MaxCompute to access Tablestore
The procedure to access Tablestore across accounts is the same as the procedure to access Tablestore within one account, except that you must use the ARN of the role to create an external table under a different account.
Account B creates external tables in MaxCompute and specifies the role ARN created in Preparations to access Tablestore.
CREATE EXTERNAL TABLE ads_log_ots_pt_external
(
vid bigint,
gt bigint,
longitude double,
latitude double,
distance double,
speed double,
oil_consumption double
)
STORED BY 'com.aliyun.odps.TableStoreStorageHandler'
WITH SERDEPROPERTIES (
'tablestore.columns.mapping'=':vid, :gt, longitude, latitude, distance, speed, oil_consumption',
'tablestore.table.name'='vehicle_track',
'odps.properties.rolearn'='acs:ram::1234567890****:role/aliyunodpsroleforotheruser'
)
LOCATION 'tablestore://cap1.cn-hangzhou.ots-internal.aliyuncs.com'
USING 'odps-udf-example.jar'