This topic describes common issues with PCA certificates and provides solutions.
What type of certificate does Matter use?
Matter is a new smart home automation standard managed by the Connectivity Standards Alliance (CSA). Matter provides seamless and secure cross-vendor connectivity for smart home devices, such as light switches, door locks, and media devices. This means that all Matter-enabled apps and hardware models can connect and work together seamlessly. To ensure security and interoperability, smart home devices must pass Matter's device authentication checks before they can join a Matter smart home network, also known as a fabric, and communicate with other Matter devices.
Matter's device authentication is based on a public key infrastructure (PKI) and uses standard X.509 digital certificates to identify devices and secure communication between them. Matter uses two types of device certificates:
-
A Device Attestation Certificate (DAC) is provided by the device manufacturer to uniquely identify the device vendor and product type. You can trace the certificate chain of a device's DAC to confirm that your Matter device was produced by the manufacturer indicated on the packaging.
DACs are issued by a trusted certification authority (CA) or a Product Attestation Authority (PAA). To bring a Matter-certified device to market, developers must first obtain a Matter DAC for each device. Alibaba Cloud PCA helps you build a Matter-compliant PKI certificate system, which speeds up the launch of your Matter-certified products.
-
A Node Operational Certificate (NOC) is issued by a Matter administrator during commissioning to authenticate the identity of other devices and ensure the privacy and integrity of data communication.
How to install a PCA certificate trust chain in Google Chrome
The following steps use the import of an Alibaba Cloud PCA root certificate as an example.
-
Obtain the root certificate content from the console and save it to a local file named root.crt.
Log in to the Certificate Management Service console.
In the navigation pane on the left, choose . On the Private Certificate Management page, select the region where the PCA service is located.
-
On the Private CA tab, find the root certificate that you want to use. In the Actions column, choose .
-
In the Details pane, copy the root CA certificate content and save it locally as root.crt.
-
Install the root CA certificate in your browser. The installation steps vary by browser. The following procedure uses Google Chrome as an example.
-
Open Google Chrome. In the upper-right corner of the browser window, choose .
-
On the Notification page, click Privacy and Security and then select Security.
-
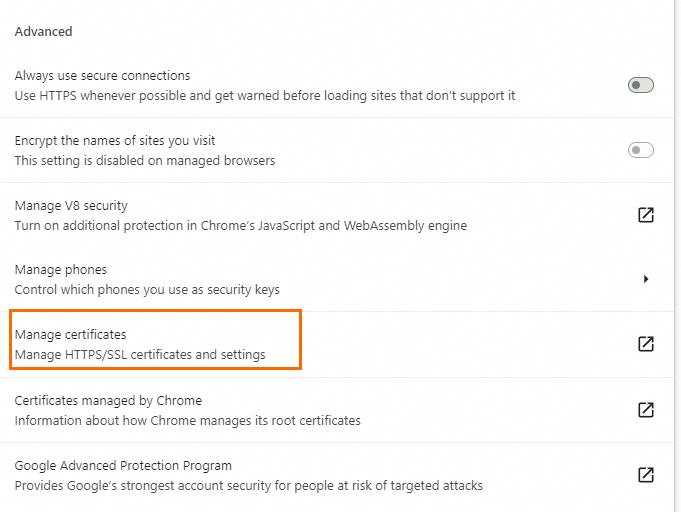
On the Secure page, in the Advanced section, click Use Certificate Application Repository to Manage Private Certificates.
-
On the Trusted Root Certification Authorities tab, click Upload and Parse File and follow the Certificate Import Wizard to import the root.crt file.
-
How do I understand the validity periods of private certificates and private CAs?
-
Private certificate validity period:
-
If your PCA service subscription is for less than one year, the validity period of a private certificate cannot exceed the subscription duration. For example, if you purchase a 1-month PCA service subscription, the maximum validity period for an issued certificate is 31 days. If you need a longer certificate validity period, you must renew your PCA service subscription to extend its duration. For more information about renewal, see PCA certificate billing.
-
If the subscription duration for the intermediate CA service is one year or longer, the validity period of an issued private certificate can be from 1 to 100 years.
-
-
Private CA validity period:
-
If the subscription duration for the private root CA is less than one year, the maximum validity period for the root CA is 20 years.
-
If the subscription duration for the private root CA is one year or longer, the maximum validity period for the root CA is 100 years.
-
If a private CA expires, it can no longer be used to issue private certificates. However, previously issued certificates that have not expired are unaffected and continue to function.