Log Analysis in Security Center centralizes host logs (logon, process, and network connectivity) and security logs (alerts, vulnerabilities, and baseline checks) in one place. Use it to investigate security events, trace threats, run audits, and meet compliance requirements — without hunting across scattered log sources.
View log reports
After you enable Log Analysis, Security Center automatically creates dashboards that visualize host and security log data across six report types.
Supported report types
| Log type | Report | What it shows |
|---|---|---|
| Host log | Logon Center | Logon activity across servers — spot unusual logons by source, user, and method |
| Host log | Process Center | Process startup events — detect suspicious programs running on your servers |
| Host log | Network Connectivity Center | Network connection changes — identify suspicious inbound or outbound traffic |
| Security log | Baseline Center | Configuration risk distribution and remediation trends across your assets |
| Security log | Vulnerability Center | Vulnerability distribution, types, and remediation status across your assets |
| Security log | Alert Center | Alert levels, types, and handling status for all security events |
Reports only show data after you turn on the Enable switch on the Log Analysis page. If you just enabled the feature, wait 5 to 10 minutes for data delivery and processing before data appears.
For a full list of charts in each report, see Appendix: Log report details.
View a report
Go to the Security Center console > Risk Governance > Log AnalysisSecurity Center console > Risk Governance > Log Analysis page. In the upper-left corner, select your asset region: Chinese Mainland or Outside Chinese Mainland.
On the Log Analysis page, turn on the Enable switch.

Click a report tab to open its dashboard.

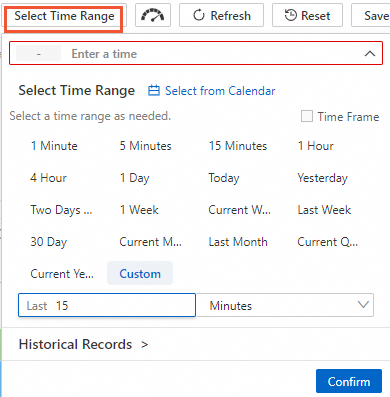
To filter by time, click the time range selector in the upper-right corner and specify a range.
NoteThis setting is temporary. The next time you open the report page, the dashboard reverts to its default time range.
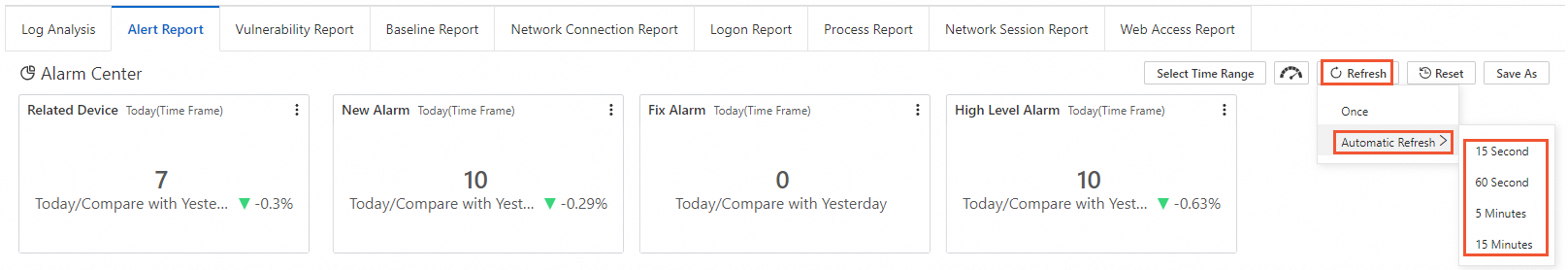
(Optional) To set a refresh rate, click Refresh in the upper-right corner and select an option:
Once: Refreshes the dashboard immediately.
Automatic Refresh: Refreshes at a set interval — 15 seconds, 60 seconds, 5 minutes, or 15 minutes.
Export logs
Limits
Before you start an export, note the following limits:
You can export a maximum of 20 million log entries per task.
If your query is too complex, the export may time out. Narrow the time range or simplify the query statement, then retry.
Export log data
Log on to the Security Center console.Log in to the Security Center console.
In the left-side navigation pane, choose Risk Governance > Log Analysis. In the upper-left corner, select your asset region: Chinese Mainland or Outside Chinese Mainland.
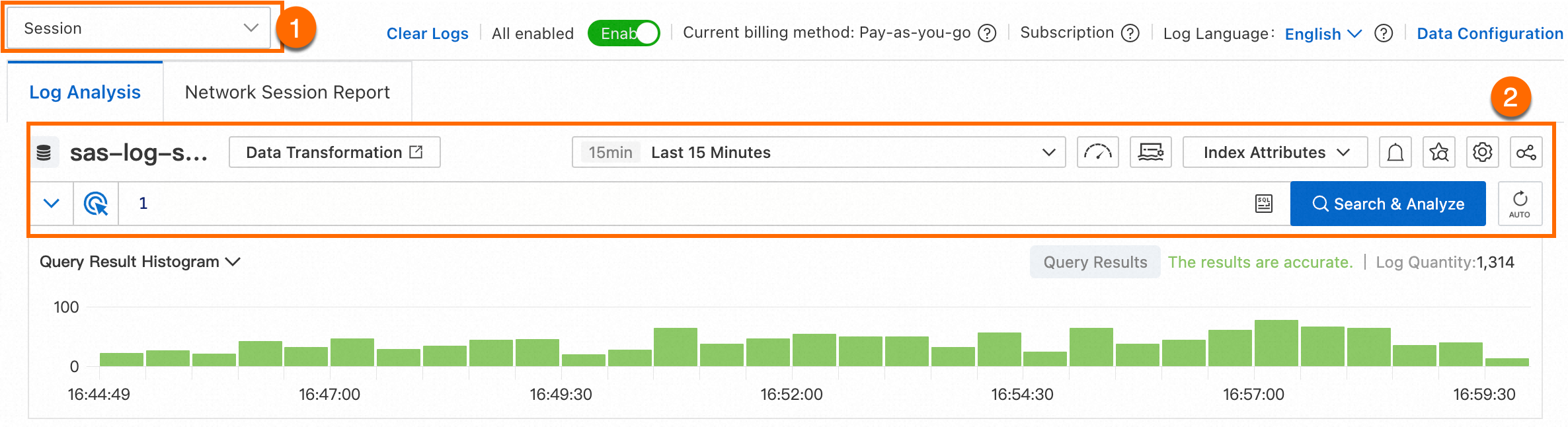
In the upper-left corner, select a log type from the drop-down list and run a query. For details, see Customize log queries and analysis.
On the Raw Logs tab, click the
 icon above the log list, then select Download Log.
icon above the log list, then select Download Log.In the Log Download dialog box, configure the export parameters and click OK.
Parameter Description Time Range (Read-only) The time range for the export, as set in your query. Search Statement (Read-only) The query statement used for the export. Task Name A custom name to identify this export task. Number of Logs Export all logs (up to 20 million) or a custom number. Data Format CSVfor tabular data, orjsonfor structured data.Quote Character CSV only. The character used to enclose fields: "or'.Allow Inaccurate Results Yes: faster export, results may be approximate. No: accurate results, but the export may take longer or fail. Compression Method Compression format for the exported file: None, gzip, orzstd.Sort Order Time-based sort order: ascending (asc) or descending (desc). Download the exported file:
Click the
 icon above the log list on the Raw Logs tab, then select Download Tasks.
icon above the log list on the Raw Logs tab, then select Download Tasks.In the Advanced Download dialog box, wait for the task status to show Success, then click Download.
For other download methods — such as Cloud Shell or the command line — go to the Simple Log Service (SLS) console. For instructions, see Download logs.
Advanced management of Simple Log Service
Log Analysis integrates with Simple Log Service (SLS), giving you access to advanced capabilities: alert rules, notification methods, real-time data consumption, and data shipping.
Go to the Security Center console > Risk Governance > Log AnalysisSecurity Center console > Risk Governance > Log Analysis page. In the upper-left corner, select the region where your assets are located: Chinese Mainland or Outside Chinese Mainland.
In the upper-right corner of the Log Analysis page, click Advanced Management of Simple Log Service.
In the SLS console that opens, use the relevant SLS features:
You can also use SLS APIs to write and query log data and manage projects and Logstores. For details, see Simple Log Service API.
FAQ
Why did my log export task fail?
The most common cause is exceeding the 20-million-entry limit. If your query returns more than 20 million logs, narrow the time range or add filters to reduce the result set, then retry. If the query is too complex, it can also time out — try simplifying the query statement.
Why is there no data in my report?
Check these three things in order: confirm the Enable switch is on for Log Analysis, confirm the selected time range covers the period you expect to see, and if you just enabled the feature, wait 5 to 10 minutes for data delivery and processing to complete.
Appendix: Log report details
Host logs
Logon center
| Chart name | Type | Default time range | Description | |
|---|---|---|---|---|
| Logon count | Single value comparison | 1 hour (relative) / Day-over-day | Total logon count and percentage change from the same period the previous day. | |
| Number of logged-on devices | Single value comparison | Today (to the hour) / Day-over-day | Count of unique host devices with logon events, and percentage change from the previous full day. | |
| Number of unique logon source IPs | Single value comparison | Today (to the hour) / Day-over-day | Count of unique source IPs for device logons, and percentage change from the previous full day. | |
| Number of unique logon usernames | Single value comparison | Today (to the hour) / Day-over-day | Count of unique usernames for device logons, and percentage change from the previous full day. | |
| Endpoint logon monitoring trend | Line and column chart | Today (to the hour) | Hourly trend for the number of devices with logon events and total logon count. | |
| Logon method trend | Stacked area chart | Today (to the hour) | Hourly trend of logon counts by method (RDP, SSH, and others). Unit: count/hour. | |
| Logon method distribution | Pie chart | 4 hours (relative) | Distribution of logon methods, such as RDP and SSH. | |
| Device distribution | Map (global) | 4 hours (relative) | Geographic distribution of public devices with logon events. | |
| Logon source distribution | Map (global) | 4 hours (relative) | Geographic distribution of logon sources by logon count for public devices. | |
| Unique logon source distribution | Map (global) | 4 hours (relative) | Geographic distribution of unique logon sources for public devices. | |
| Top 10 users by logon count | Pie chart | 4 hours (relative) | Top 10 usernames ranked by logon count. | |
Active user list | table | 4 hours (relative) | Lists the 30 user accounts with the earliest activation times. | None |
| Top 10 ports by logon count | Pie chart | 4 hours (relative) | Top 10 destination ports ranked by logon count. | |
| Active user list | Table | 4 hours (relative) | 30 user accounts with the earliest activation times. | |
| Top 30 users and sources by machine logon count | Table | 4 hours (relative) | Top 30 users and sources by machine logon count, including source network, logon IP, username, logon method, unique devices logged on to, and logon count. |
Process center
| Chart name | Type | Default time range | Description |
|---|---|---|---|
| Process startup count | Single value comparison | 1 hour (relative) / Day-over-day | Total process startup event count and percentage change from the same period the previous day. |
| Number of related devices | Single value comparison | Today (to the hour) / Day-over-day | Count of devices with process startup events and percentage change from the previous full day. |
| Number of unique started process names | Single value comparison | Today (to the hour) / Day-over-day | Count of unique started process names and percentage change from the previous full day. |
| Number of endpoint devices | Line and column chart | Today (to the hour) | Hourly trend for the number of devices with process startups and count of unique started process names. Unit: count/hour. |
| Process startup trend | Line chart | Today (to the hour) | Hourly trend of the average number of processes started per device. Unit: count/hour. |
| Public device distribution | Map (global) | Today (to the hour) | Geographic distribution of public devices with process startup events. |
| Distribution of process startup counts on public-IP devices | Map (global) | Today (to the hour) | Geographic distribution of process startup event counts on devices with public IP addresses. |
| Top 20 processes by startup count | Table | Today (to the hour) | Top 20 processes ranked by startup count, including process name, process path, and startup count. |
| Top 20 processes by Bash trigger count | Table | Today (to the hour) | Top 20 processes that triggered Bash the most, including parent process name and total trigger count. |
| Top 30 Java files by process startup count | Table | Today (to the hour) | Top 30 Java files ranked by process startup count, including Jar file name, Jar file path, and total startup count. |
| Top 30 clients by process startup count | Table | Today (to the hour) | Top 30 clients ranked by process startup count, including client, total startup count, most common command line, process name, count, and percentage. |
Network Connectivity Center
| Chart name | Chart type | Default time range | Description |
|---|---|---|---|
| Connection event count | Single value comparison | 1 hour (relative) / Day-over-day | Total network connection change events on devices, and percentage change from the same time the previous day. |
| Number of related devices | Single value comparison | Today (hourly) / Day-over-day | Count of unique host devices with connection change events, and change compared to the previous full day. |
| Number of unique processes | Single value comparison | Today (hourly) / Day-over-day | Count of unique process names with network connection change events, and change compared to the previous full day. |
| Number of unique source IPs | Single value comparison | Today (hourly) / Day-over-day | Count of unique connection source IPs with network connection change events, and change compared to the previous full day. |
| Number of unique destination IPs | Single value comparison | Today (hourly) / Day-over-day | Count of unique connection destination IPs with network connection change events, and change compared to the previous full day. |
| Network connection trend | Dual line chart | 1 hour (relative) | Hourly trend of devices and events with network connections. Unit: items per hour. |
| Connection type trend | Dual line chart | 1 hour (relative) | Hourly trend of connection type distribution (outbound, inbound). Unit: items per hour. |
| Connection type distribution | Pie chart | 1 hour (relative) | Distribution of connection types (outbound, inbound) for network connection change events. |
| Protocol type distribution | Pie chart | 1 hour (relative) | Distribution of connection protocols (TCP, UDP, and others) for network connection change events. |
| Public device distribution | Map (global) | 1 hour (relative) | Geographic distribution of devices with network connection change events. |
| Public device event distribution | Map (global) | 1 hour (relative) | Geographic distribution of network connection change events on devices with public IP addresses. |
| Outbound connection destination distribution | Map (global) | 1 hour (relative) | Geographic distribution of outbound connection destinations. |
| Inbound connection source distribution | Map (global) | 1 hour (relative) | Geographic distribution of inbound connection sources. |
| Top 30 devices with the most outbound connections | Table | 1 hour (relative) | Top 30 devices with outbound connections, including device, number of outbound connection events, unique connection destinations, and examples. |
| Top 30 devices with the most inbound connections | Table | 1 hour (relative) | Top 30 devices with inbound connections, including device, listening IP, number of inbound connection events, listening ports, and examples. |
| Top 30 devices with the most outbound connection destinations | Table | 1 hour (relative) | Top 30 devices with the most unique outbound connection destinations, including device, outbound connection events, unique destinations, and examples. |
| Top 30 listening ports with the most inbound connections | Table | 1 hour (relative) | Top 30 listening ports with inbound connections, including listening port, inbound connection events, and examples. |
| Top 30 processes with the most outbound connections | Table | 1 hour (relative) | Top 30 processes with outbound connections, including process name, outbound connection events, related devices, and example paths. |
| Top 30 processes with the most inbound connections | Table | 1 hour (relative) | Top 30 processes with inbound connections, including process name, inbound connection events, related devices, and example paths. |
Security logs
Baseline center
| Chart name | Chart type | Default time range | Description |
|---|---|---|---|
| Number of affected clients | Single value comparison | Today (to the hour) / Day-over-day | Count of unique host devices with baseline issues, and increase or decrease compared to the previous day. |
| Number of new baselines | Single value comparison | Today (to the hour) / Day-over-day | Count of new baseline events, and increase or decrease compared to the previous day. |
| Number of verified baselines | Single value comparison | Today (to the hour) / Day-over-day | Count of verified baseline events, and increase or decrease compared to the previous day. |
| Number of high-priority baselines | Single value comparison | Today (to the hour) / Day-over-day | Count of high-priority baseline events, and increase or decrease compared to the previous day. |
| Baseline operation trend | Flow chart | Today (to the hour) | Hourly trend of baseline operations (new, verified, and others). Unit: count. |
| Baseline subtype trend | Flow chart | Today (to the hour) | Hourly trend of baseline subtypes (system account security, registry, and others). Unit: count. |
| Baseline status trend | Flow chart | Today (to the hour) | Hourly trend of baseline statuses (unfixed, fixed, and others). Unit: count. |
| Baseline operation distribution | Doughnut chart | Today (to the hour) | Distribution of baseline operations (new, verified, and others). |
| Baseline subtype distribution | Doughnut chart | Today (to the hour) | Distribution of baseline subtypes (system account security, registry, and others). |
| Baseline status distribution | Doughnut chart | Today (to the hour) | Distribution of the latest baseline statuses (unfixed, fixed, and others). Important If a baseline changes status multiple times, this chart uses the latest status. |
| Top 10 new baselines | Doughnut chart | Today (to the hour) | 10 baselines with the most new occurrences across all devices. |
| Top 10 verified baselines | Doughnut chart | Today (to the hour) | 10 baselines with the most verifications across all devices. |
| Top 20 clients by baseline event count | Table | Today (to the hour) | Top 20 clients with the most baseline events, including client, total baseline event count, new baselines, fixed baselines, and count of high- or medium-priority baselines. |
Vulnerability center
| Chart name | Chart type | Default time range | Description |
|---|---|---|---|
| Number of affected clients | Single value comparison | Today (to the hour) / Day-over-day | Count of servers with vulnerabilities, and increase or decrease compared to the previous day. |
| Number of new vulnerabilities | Single value comparison | Today (to the hour) / Day-over-day | Count of new security vulnerability events, and increase or decrease compared to the previous day. |
| Number of verified vulnerabilities | Single value comparison | Today (to the hour) / Day-over-day | Count of verified security vulnerability events, and day-over-day change. |
| Number of fixed vulnerabilities | Single value comparison | Today (to the hour) / Day-over-day | Count of fixed security vulnerabilities, and change compared to the previous day. |
| Vulnerability operation trend | Flow chart | Today (to the hour) | Hourly trend of vulnerability operations (new, verified, and others). Unit: count. |
| Vulnerability type trend | Flow chart | Today (to the hour) | Hourly trend of vulnerability types (Windows vulnerability, Linux vulnerability, Web-CMS vulnerability, and others). Unit: count. |
| Vulnerability status trend | Flow chart | Today (to the hour) | Hourly trend of vulnerability statuses (unfixed, fixed, and others). Unit: count. |
| Vulnerability operation distribution | Doughnut chart | Today (to the hour) | Distribution of vulnerability operations (new, verified, and others). |
| Vulnerability type distribution | Doughnut chart | Today (to the hour) | Distribution of vulnerability types (Windows vulnerability, Linux vulnerability, Web-CMS vulnerability, and others). |
| Vulnerability status distribution | Doughnut chart | Today (to the hour) | Distribution of the latest vulnerability statuses (unfixed, fixed, and others). Important If a vulnerability changes status multiple times, this chart uses the latest status. |
| Top 10 new vulnerabilities | Doughnut chart | Today (to the hour) | 10 vulnerabilities with the most new occurrences across all devices. |
| Top 10 verified vulnerabilities | Doughnut chart | Today (to the hour) | 10 vulnerabilities with the most verifications across all devices. |
| Top 10 fixed vulnerabilities | Doughnut chart | Today (to the hour) | 10 vulnerabilities with the most fixes across all devices. |
| Top 20 clients by vulnerability event count | Table | Today (to the hour) | Top 20 clients with the most vulnerability events, including client, total vulnerability event count, new vulnerabilities, verified vulnerabilities, fixed vulnerabilities, and breakdown by type. |
Alert center
| Chart name | Chart type | Default time range | Description |
|---|---|---|---|
| Number of affected clients | Single value comparison | Today (to the hour) / Day-over-day | Count of hosts with security alerts, and increase or decrease compared to the previous day. |
| Number of new alerts | Single value comparison | Today (to the hour) / Day-over-day | Count of new security alert events, and increase or decrease compared to the previous day. |
| Number of fixed alerts | Single value comparison | Today (to the hour) / Day-over-day | Count of handled security alert events, and change compared to the previous day. |
| Number of high-priority alerts | Single value comparison | Today (to the hour) / Day-over-day | Count of critical security alerts, and increase or decrease compared to the previous day. |
| Alert operation trend | Flow chart | Today (to the hour) | Hourly trend of alert operations (new, fixed, and others). Unit: count. |
| Alert level trend | Flow chart | Today (to the hour) | Hourly trend of alert levels (critical, suspicious, informational, and others). Unit: count. |
| Alert status trend | Flow chart | Today (to the hour) | Hourly trend of alert statuses (unfixed, fixed, and others). Unit: count. |
| Alert operation distribution | Doughnut chart | Today (to the hour) | Distribution of alert operations (new, fixed, and others). |
| Alert level distribution | Doughnut chart | Today (to the hour) | Distribution of alert levels (critical, suspicious, informational, and others). |
| Alert status distribution | Doughnut chart | Today (to the hour) | Distribution of the latest alert statuses (unfixed, fixed, and others). Important If an alert changes status multiple times, this chart uses the latest status. |
| Top 10 new alerts | Doughnut chart | Today (to the hour) | 10 alerts with the most new occurrences across all devices. |
| Top 10 fixed alerts | Doughnut chart | Today (to the hour) | 10 alerts with the most fixes across all devices. |
| Top 20 clients by alert event count | Table | Today (to the hour) | Top 20 clients with the most alert events, including client, total alert event count, new or fixed events, critical or suspicious events, and breakdown by alert type. |