This page answers common questions about alerts, intrusion detection, and response actions in Security Center.
Mining programs
How do I know if a mining program is running on my server?
Two signs point to an active mining program: CPU utilization consistently at 80% or higher, and an unknown process continuously sending packets. Security Center detects mining programs using process monitoring and network traffic analysis, then sends an alert notification by text message or email.
Handle the alert on the CWPP tab of the Alert page. If the mining alert is associated with related alerts — such as communication with mining pools or access to malicious domains — handle those as well. For details, see View and handle security alerts.

How do I handle a mining attack?
Only the Anti-virus, Advanced, Enterprise, and Ultimate editions support handling mining alerts.
Choose the appropriate path based on your situation:
If antivirus is not enabled:
Log on to the Security Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center console. In the top navigation bar, select the region of the asset. You can select China or Outside China.
In the left-side navigation pane, choose Detection and Response > Alert.
If you have activated the Agentic SOC feature, navigate to Agentic SOC > Alert instead.
On the Alert page, under the CWPP tab, find the alert and click Handle in the Actions column.
In the dialog box, select Virus Detection and Removal and click Process Now.
In the left-side navigation pane, choose System Settings > Feature Settings.
Click the Settings tab, then the Host Protection Settings tab. In the Proactive Defense section, turn on Malicious Host Behavior Prevention.
If you want to verify that automatic virus blocking is active:
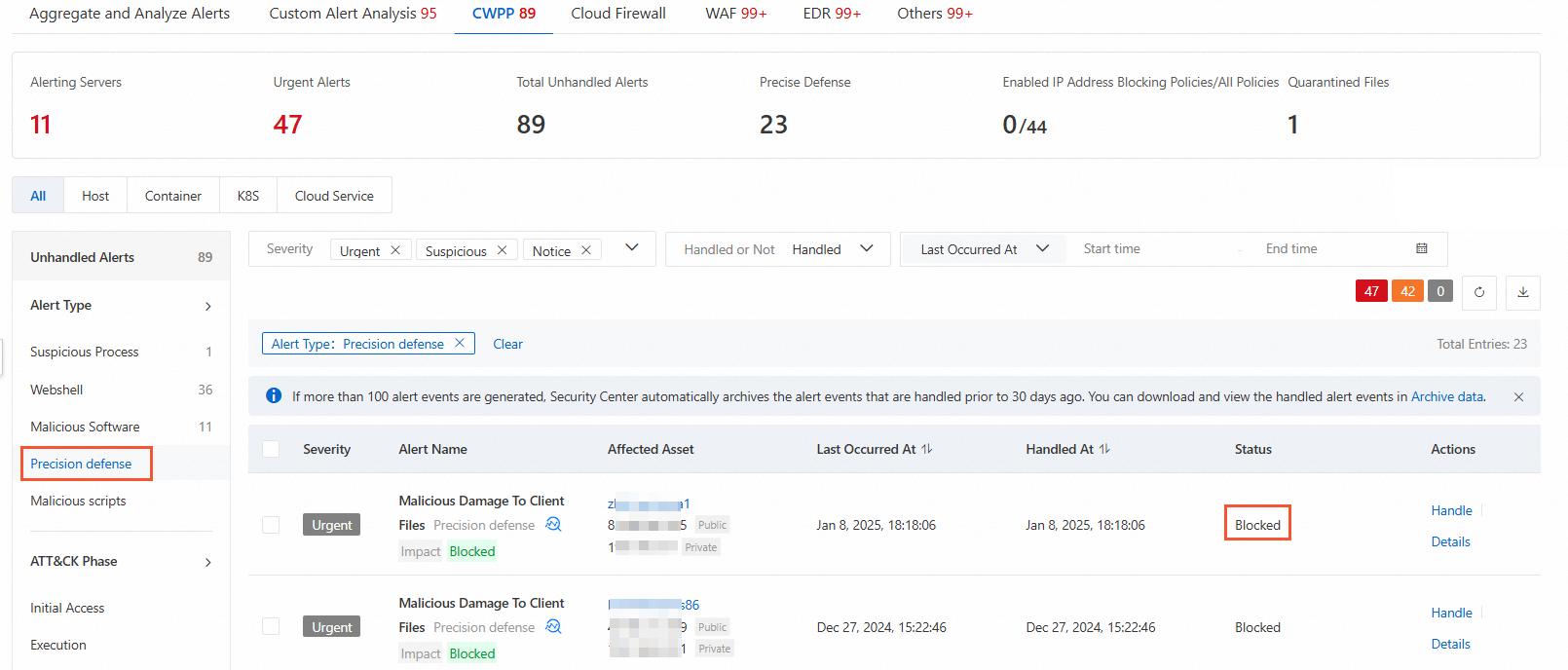
Go to System Configuration > Feature Settings and confirm that Malicious Host Behavior Prevention is turned on. Then go to Detection and Response > Alert. On the Alert page, under the CWPP tab, set Alert Type to Precision defense. If the filtered alerts show a status of Blocked, automatic virus blocking is active.
If the alert is a known false positive from a legitimate process:
Whitelist the alert on the Alert page under the CWPP tab. Only whitelist alerts you have confirmed as false positives — pre-emptive whitelisting reduces your security coverage.
I accidentally whitelisted a mining alert. How do I remove it?
Log on to the Security Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center console. In the top navigation bar, select the region of the asset.
In the left-side navigation pane, choose Detection and Response > Alert.
On the Alert page, under the CWPP tab, set the status filter to Handled to find all handled alerts.
Find the alert and click Remove from Whitelist in the Actions column.
Intrusion detection
How does Security Center detect intrusions?
Security Center combines two data sources to detect intrusions: automated scans of your assets, and analysis of user traffic data performed by Alibaba Cloud security engineers. Common intrusions detected include web shells, brute-force attacks, and mining attacks. For the full alert catalog, see Overview of CWPP security alerts.
Web shell detection
How does Security Center detect web shells?
Security Center scans PHP, ASP, and JSP script files using three methods:
Disk-based detection: After a file is uploaded to or downloaded from your server, Security Center scans it and generates an alert if malicious content is found.
Real-time monitoring of web directories.
Scheduled scanning of web directories.
Alerts for common files
This is not a false positive. If a commonly used file on your server is modified or its content contains obvious backdoor statements, Security Center will also generate an alert. After investigation, you can handle the alert accordingly.
Can Security Center automatically quarantine web shell files?
No. Web shell files may contain business-related content, so Security Center requires manual review before quarantine. After you quarantine a file, it appears in the File Quarantine panel and can be restored within 30 days. See Evaluate and handle security alerts.
Alert whitelist
What types of alerts can I add to the whitelist?
Only whitelist alerts you have confirmed as false positives. Pre-emptive whitelisting reduces your security coverage.
You can whitelist alerts generated for malware. When you whitelist an alert for a malicious process, only the source file of that process is added — not every file associated with it.
| Alert type | What gets added to the whitelist |
|---|---|
| Malware | MD5 hash value |
| Unusual logon | IP addresses used for the unusual logons |
| Access to malicious IP addresses or communication with mining pools | Related IP addresses |
| Access to malicious domains | Related domain names |
| Access or connection to malicious download sources | Source URLs |
| Web shell | Web directories, based on directory configuration |
| Malicious script | MD5 hash value and path |
| Cloud threat detection | Whitelist rules configured in the Security Center console |
| Suspicious process | Command lines |
| Persistent web shells | MD5 hash values and characteristic values |
| Tampering of sensitive files | File path |
| Intrusion into applications | Command lines |
| Threat to web applications | Related domain names or URLs |
| Suspicious network connection | Command lines, destination IP addresses, and destination ports (only the fields that exist are added if some are missing) |
Is the phpinfo alert a false positive?
No. The phpinfo file exposes sensitive information — including the absolute path of your website — that attackers use to plan follow-on attacks. Most attackers upload a phpinfo file as a first step in penetration.
If your business genuinely requires phpinfo, whitelist the alert on the Alert page under the CWPP tab.
Alert states
Why are some alerts in the Expired state?
Security Center moves alerts older than 30 days to the Expired state. If the same activity is detected again after expiry, Security Center creates a fresh alert with an updated timestamp and sets the status back to Unhandled.
Why does the alert timestamp for accessing a suspicious domain differ from when the access actually occurred?
Domain Name System (DNS) data reaches Security Center with a delay. After receiving the data, Security Center runs analysis before generating the alert, so the alert timestamp is later than the actual access time. A difference of up to 5 hours is normal.
Unusual logon detection
How does Security Center detect and alert on unusual logons?
After you install the Security Center agent, it regularly collects server logon logs and uploads them to the cloud for analysis. Security Center detects logons based on four independent factors: logon location, IP address, time range, and account. An alert is generated when any one of these factors falls outside the approved set.
Here is how Security Center builds its list of approved locations:
First use: No alerts are generated because no approved locations have been defined yet.
First successful logon from a public IP: The location of that IP is automatically marked as approved. All locations of public IPs that log on within the next 24 hours are also marked approved. After 24 hours, logons from any other location trigger an alert.
Recurring logons from an unapproved location: An alert and text message notification are sent for the first logon only. If 6 or more logons from that IP succeed, Security Center automatically marks the IP's location as approved.
Security Center determines approved logon locations based on public IP addresses only.
For unapproved IP addresses specifically:
A text message notification is sent for the first logon only. Subsequent logons from the same IP generate alerts in the console but no additional text messages.
If you use the Advanced, Enterprise, or Ultimate edition, you can explicitly define approved logon locations, IP addresses, time ranges, and accounts. These custom settings take priority over the default mechanism.
What types of unusual logons trigger alerts?
Logon from a malicious IP address (targets include servers, FTP, MySQL, and SQL Server)
Server logon using a backdoor account
Server logon using a weak password
Suspicious external logon scanning
Logon from an unusual location
Logon using an unusual account
ECS instance logon after a successful brute-force attack via Remote Desktop Protocol (RDP) or SSH
ECS instance logon over SSH before a suspicious command sequence is executed
ECS instance logon from an unapproved time range, location, IP address, or account
For the full alert list, see Alerts.
How do I stop Security Center from alerting on my own logons?
In the console, go to Protection Configuration > Host Protection > Host-specific Rule Management and click Common Logon Management. Specify approved logon locations, IP addresses, time ranges, and accounts. You can add them manually or configure automatic updates. Security Center only generates alerts for logons that fall outside what you define here.
Does an unusual logon alert mean the logon was blocked?
No. The logon succeeds. Security Center flags the logon as suspicious and generates an alert, but it does not block the session.
A logon is identified as coming from an attacker. What do I do?
In the console, go to Detection and Response > Alert. Under the CWPP tab, find the alert and click Handle. Set Handling Method to Block for and Rule Validity Period to 12 Hours, then click Process Now. This blocks further logons from that IP.
After blocking, change your account password immediately and check your server for unknown accounts and public keys that could enable SSH password-free logons.
I received an alert about suspicious commands executed after an SSH logon. Were the commands actually run?
Yes. Change your server logon password immediately and check the ECS instance for signs of other abnormal activity, such as unfamiliar running processes.
Where can I find logon logs on my server after an unusual logon alert?
Check the /var/log/secure directory. For example, to look up activity from a specific IP:
grep 10.80.22.22 /var/log/secureI set approved logon IP addresses, time ranges, and accounts, but I still see unusual logon alerts. Why?
Logon IP address, location, account, and time range are evaluated independently, with no priority order. An alert fires if any one of these factors is outside the approved set. Check which specific factor triggered the alert.
What should I do if a false alert is triggered by the brute-force defense rule?
You may enter your password incorrectly several times before a successful logon, which Security Center can interpret as a brute-force attack. If you confirm the alert is a false positive, ignore it. See Evaluate and handle security alerts.
Brute-force attacks
How do I view brute-force attack details and blocking statistics?
Log on to the Security Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center console. In the left-side navigation pane, choose Detection and Response > Attack Analysis. The Attack Analysis page shows SSH brute-force attacks that Security Center has blocked.
How do I protect my servers from brute-force attacks?
Specify approved logon IP addresses, or switch to certificate-based logon. For configuration steps, see Configure alert settings.
The brute-force defense rule was triggered accidentally and now I can't log on. What do I do?
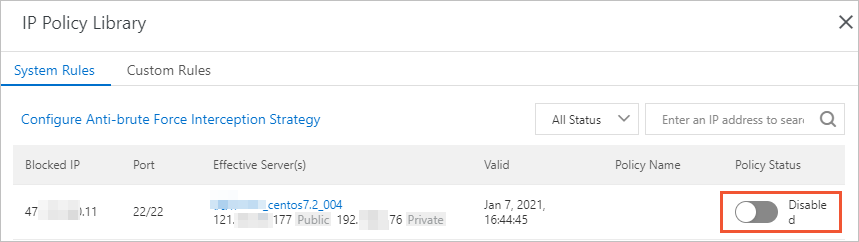
Log on to the Security Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center console. Go to Detection and Response > Alert. Under the CWPP tab, click the number below Enabled IP Address Blocking Policies/All Policies. In the IP Policy Library panel, find the rule and set Policy Status to Disabled.
Can Security Center protect web applications and websites from brute-force attacks?
No. Security Center's brute-force protection covers only servers that accept RDP or SSH logons. It does not protect web application login endpoints.
My server password was cracked. What do I do?
A cracked password means attackers may have already installed malicious programs on your server. Take these steps immediately:
Check for brute-force alerts. Go to Detection and Response > Alert and look under the CWPP tab for alerts indicating ECS instance logons via brute-force attacks. If such alerts exist, your password was cracked.
Block the attacker. On the Alert page, find the alert and click Process. Set Process Method to Block and click Process Now. Security Center creates security group rules to block the malicious IP addresses. See View and handle alert events.
Change your password. Replace the cracked password immediately with a complex one.
Run a baseline check. Use Security Center's baseline check feature to scan for residual risks and follow the remediation suggestions it provides.
The Advanced, Enterprise, and Ultimate editions support baseline checks.
I changed my weak password, but I'm still receiving brute-force attack alerts. Why?
The new password takes effect the next day. The baseline check model collects the updated password at approximately midnight on the day you change it, but the abnormal logon detection model continues using the previous password database until then. For example, if you change your password at 10:00 on January 15, 2023, the detection model updates at approximately 24:00 on January 15, 2023.
If you have confirmed the weak password is changed and no weak passwords appear in baseline checks, ignore the remaining alerts.
If the password was actually cracked, see My server password was cracked. What do I do?
RDP brute-force attack records appear even after I blocked port 3389. Why?
Windows records IPC (Inter-Process Communication), RDP, and Samba logon events in the same security log without distinguishing the logon method. If you see RDP brute-force records after blocking port 3389, check whether IPC or Samba is enabled.
Verify whether ports 135, 139, or 445 are open on your ECS instance and accessible from public IP addresses. Also check the Windows security logs for logon records within the attack period.
Does Security Center detect weak passwords only for RDP and SSH?
No. Security Center also detects weak passwords used by administrators to log on to content management systems (CMSs).
Attack Awareness page
What data is shown on the Attack Awareness page?
The page aggregates two data sources: attacks automatically identified and blocked by Security Center, and attack data from Alibaba Cloud Web Application Firewall (WAF). The statistics include data on the assets that are protected by Security Center and WAF, which you can view in the Assets module.