Security Center monitors server logons and generates an Unusual Logon alert when a logon falls outside your approved criteria. Define which locations, IP addresses, time ranges, and accounts are considered safe for your servers to reduce false positives and catch unauthorized access.
Prerequisites
Before you begin, ensure that you have:
Access to the Security Center consoleLog on to the Security Center console.
The required permissions to configure host protection rules
How approved logon policies work
Security Center evaluates logons against the dimensions you configure. A logon triggers an Unusual Logon alert only when it falls outside the approved criteria for a configured dimension.
Policies are scoped to specific servers. You specify which servers each policy applies to when creating or editing a policy.
Configure approved logon policies
Security Center supports four logon dimensions:
| Dimension | What it controls |
|---|---|
| Approved Logon Location | Geographic regions from which logons are permitted |
| Approved Logon IP Address | Source IP addresses or ranges from which logons are permitted |
| Approved Logon Time | Time ranges during which logons are permitted |
| Approved Logon Account | User accounts that are permitted to log on |
All four dimensions follow the same configuration steps. The example below uses Approved Logon Location.
Log on to the Security Center console. In the upper-left corner, select the region where your assets are located: China or Outside China.
In the left-side navigation pane, choose Protection Configuration > Host Protection > Host-specific Rule Management.
Click the Common Logon Management tab.
On the Approved Logon Location tab, click Create Policy.
In the Approved Logon Location panel, select one or more approved locations, select the servers the policy applies to, and click OK.
Repeat steps 4–5 on the Approved Logon IP Address, Approved Logon Time, and Approved Logon Account tabs to configure the remaining dimensions.
Edit or delete a policy
Edit: Find the entry and click Edit to change the servers covered by the policy.
Delete: Find the entry and click Delete in the Actions column to remove the policy.
Add notes to an approved IP address
On the Approved Logon IP Address tab, find the IP address and click the ![]() icon in the Note column to add remarks.
icon in the Note column to add remarks.
View unusual logon alerts
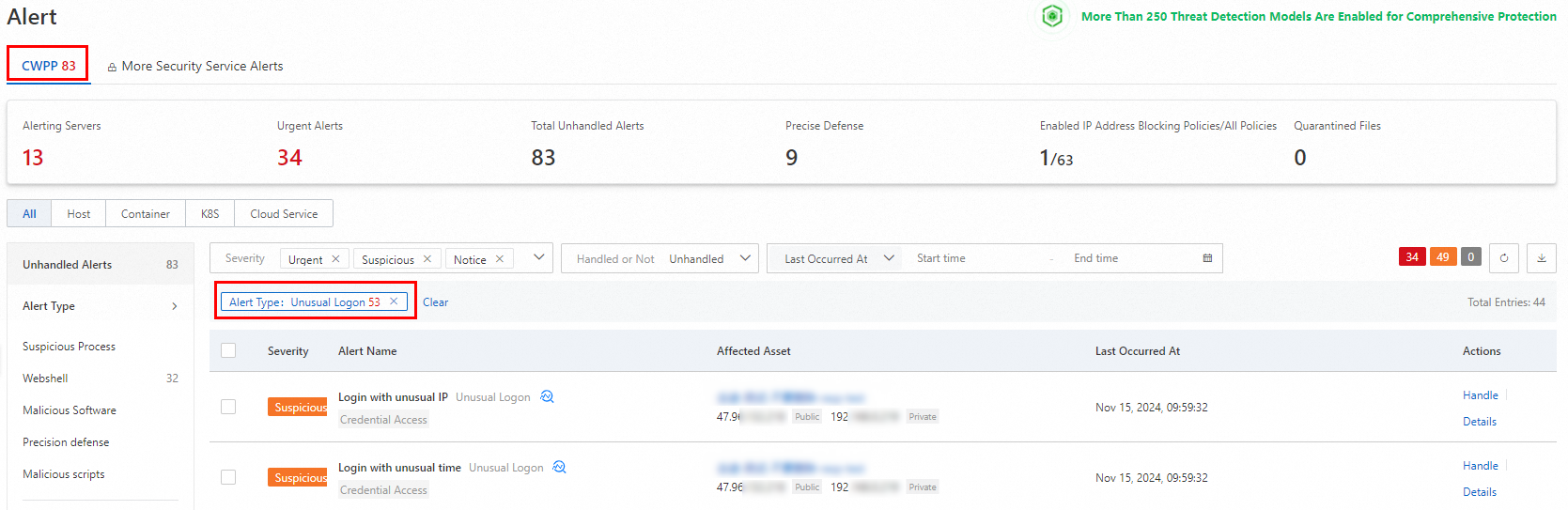
When a logon falls outside your approved criteria, Security Center generates an Unusual Logon alert on the Alerts page.
To review these alerts:
Go to the Alerts page.
Select the CWPP tab.
Set Alert Type to Unusual Logon.
Click Details in the Actions column to view threat information for a specific alert.
For instructions on handling alerts, see View and handle alerts.