By default, Security Center supports sending notifications through DingTalk chatbots. If you need to receive Security Center alerts in Lark or WeCom, use the event subscription feature of Cloud Monitor to forward alerts to your Lark or WeCom groups.
Overview
Security Center can push security alerts to Cloud Monitor, which then forwards the alerts to Lark or WeCom using an event subscription. The overall configuration workflow is as follows:
Enable Cloud Monitor Push: In the Security Center notification settings, enable Cloud Monitor Push and select the alert types to forward.
Create a messaging bot: In Lark or WeCom, create a custom chatbot and obtain its webhook URL.
Create a Cloud Monitor alert contact group:
In Cloud Monitor, create an alert contact and bind the webhook URL to the contact.
Add the webhook-bound alert contact to an alert contact group in Cloud Monitor.
Create a Cloud Monitor notification policy: In Cloud Monitor, create a notification policy and associate it with the alert contact group to specify notification recipients.
Configure a Cloud Monitor event subscription: Create an event subscription policy to subscribe to system events from Security Center and associate it with the notification policy.
Step 1: Enable Cloud Monitor push
Enable the Cloud Monitor Push feature in Security Center to allow Cloud Monitor to receive alert events.
You must enable Cloud Monitor Push in Security Center before Cloud Monitor can receive alert data.
Go to the Security Center console > System Settings > Notification Settings page. At the top of the left-side navigation pane, select the region where your assets are located: Chinese Mainland or Outside Chinese Mainland.
On the Cloud Monitor Push tab, select the notification items as needed. The following table describes the items.
Notification item
Push frequency
Description
Security Incident
Push Result Details: No limit
Detected security attacks, such as DDoS attacks and brute-force attacks.
Alert
Push Result Details: No limit
Threat alerts detected on hosts or in containers, such as anomalous logins and malicious processes.
Baseline Check
Push Result Overview: Sent every Thursday.
Summary of baseline check results.
CSPM
Push Result Overview: Sent once every Thursday.
Summary of check results for cloud platform configuration risks.
Agentless Detection
Push Result Details: You can customize the selection.
Security detection results that do not require an agent to be installed.
Malicious file
Push Result Details: Customizable.
Malicious files detected by the malicious file detection SDK.
Vulnerability
Push Result Overview: Sent once every Thursday.
Push Result Details: Customizable.
Detection results and summaries of system vulnerabilities and application vulnerabilities.
Application Protection
Push Result Details: You can customize the selection.
Alerts for Runtime Application Self-Protection (RASP).
Step 2: Create a messaging bot
Create a custom bot in Lark or WeCom and obtain its webhook URL. This URL is required for configuring the alert contact in Step 3.
Lark bot
This section describes how to create a custom Lark bot by using the Lark desktop client.
Open and log in to Lark. In a Lark group, click the
 icon in the upper-right corner and then click Group Robot.
icon in the upper-right corner and then click Group Robot.On the Group Robot panel, click Add Robot, and then select Custom Robot.
On the robot configuration page, set the Robot Name (for example, Cloud Monitor Alert Notification) and click Add.
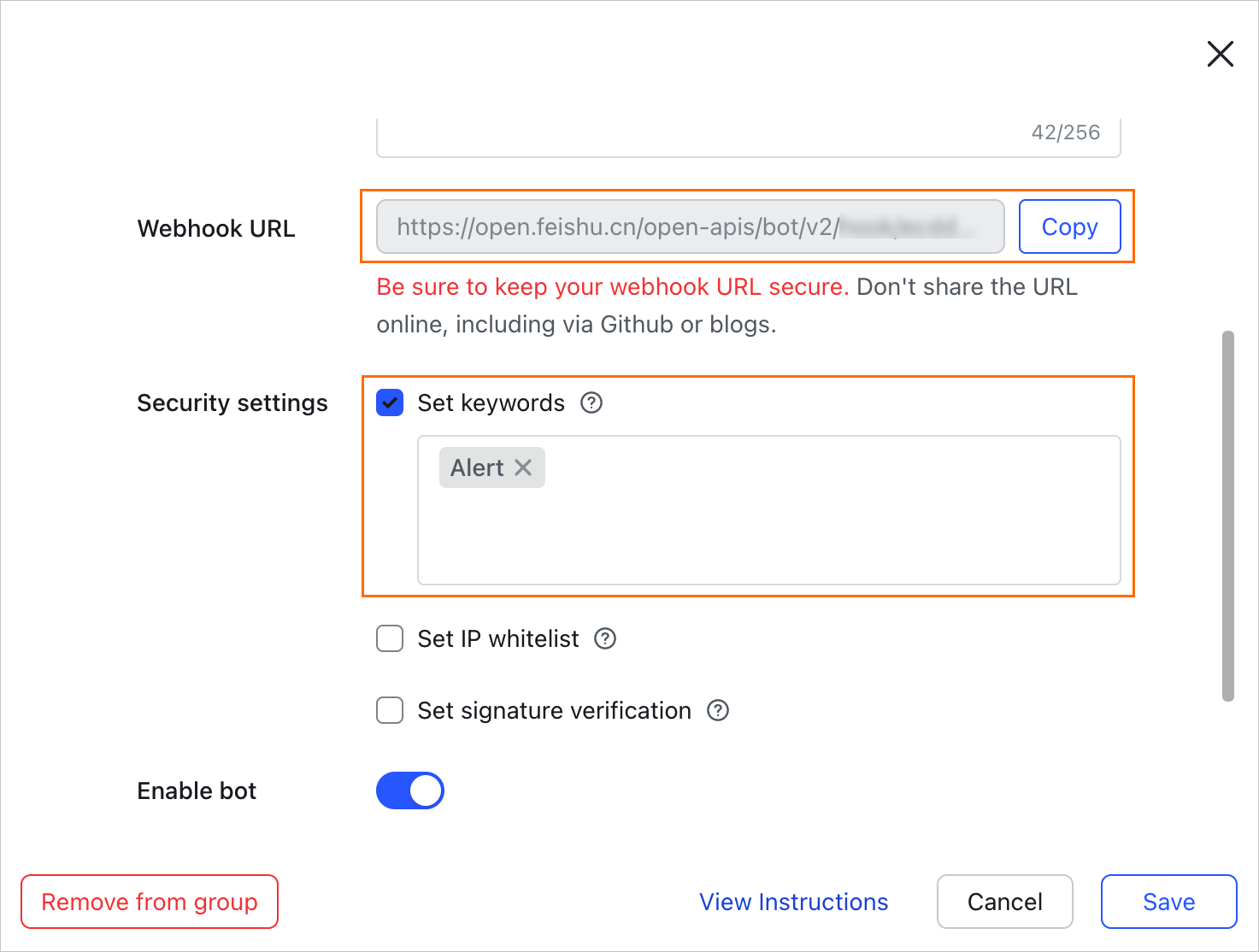
Copy the webhook URL. Then, select Custom Keywords and enter keywords such as
alert,Cloud Monitor, andSecurity Center.ImportantLark requires that messages contain at least one of the custom keywords. Otherwise, Lark blocks the message. Add multiple keywords to ensure you receive alert messages.
Securely store the webhook URL. This URL is required to configure the alert contact in Cloud Monitor.
WeCom bot
This section describes how to create a custom WeCom bot by using the WeCom mobile client.
Open and log in to WeCom.
In a WeCom group, tap the
 icon in the upper-right corner and then tap Group Robot.
icon in the upper-right corner and then tap Group Robot.On the Group Robot page, tap Add Robot.
On the Add Robot page, set a Custom Robot Name (for example, Cloud Monitor Alert Notification) and tap Add.
On the confirmation page, tap Copy to save the WeCom bot's webhook URL.
ImportantSecurely store the webhook URL. This URL is required to configure the alert contact in Cloud Monitor.
Step 3: Configure alert notifications
Create an alert contact in Cloud Monitor, bind the webhook URL from Step 2 to the contact, and then add the contact to an alert contact group. This allows Cloud Monitor to send alert notifications to Lark or WeCom through the webhook URL.
Create an alert contact
Log in to the Cloud Monitor console. In the left-side navigation pane, choose .
On the Alert Contacts tab, click Create Alert Contact.
In the Set Alert Contact panel, configure the parameters as described below.
Name: Enter a name, such as Lark Bot or WeCom Bot.
DingTalk|LarkWeComSlack Webhook(http|https): Paste the webhook URL from Step 2. This field accepts webhook URLs for both Lark and WeCom.
(Optional) Test webhook connectivity: Click the Test button to the right of the webhook field. A 200 status code indicates a successful connection.
After you verify the information, click Confirm.
Create an alert contact group
Switch to the Alert Contact Group tab and click Create Alert Contact Group.
In the Create Alert Contact Group panel, configure the parameters as described below and click Confirm.
Group Name: Enter a name for the group, such as Lark Bot Group or WeCom Bot Group.
Select contacts: Select the alert contact that you created in the previous step.
Create a notification policy
In the left-side navigation pane, choose .
Click Create policy, configure the parameters as described below, and click OK.
Name: Enter a name for the notification policy. For example, Security Center Alert Notifications.
Notification Settings: Select Set Notification Group Directly.
Contact Group: Select the alert contact group that you created.
Step 4: Configure an event subscription
Create an event subscription policy to subscribe to system events from Security Center. Associate this policy with the notification policy you created in Step 3.
Log in to the Cloud Monitor console. In the left-side navigation pane, choose .
On the Subscription Policy tab, click Create Subscription Policy and configure the parameters as described below.
Name: Use a descriptive name, such as
Security-Center-Alerts-to-Lark.Subscription Type: Select System Events.
Subscription Scope:
Products: Select Cloud Security Center.
Event Type: Select the event type that corresponds to the Notification Item and Push Content for the Cloud Monitor push notifications that you enabled in Security Center in Step 1. The mapping is as follows:
Security Center
Cloud Monitor
Security Incident
Incident
Alert
Suspicious
Baseline Check
System-Baseline-cnt
CSPM
Cspm-cnt
Agentless Detection
Agentless
Malicious file
mfd SDK
Vulnerability
Push Result Overview: Vulnerability-cnt
Push Result Details: Vulnerability
Application Protection
Rasp
Event name and Event Level: Select the events for which you want to receive notifications.
If you leave these unconfigured, you will receive notifications for all events.
If you select Set as blacklist, it functions as a deny list, meaning you will receive notifications for all events except those with the specified Event name and Event Level.
Application grouping, Event Content, and Event Resources: Keep the default settings.
Combined Noise Reduction: Use the default settings.
Notification Configuration: Select the notification policy that you created in Step 3.
Custom Notification Method and Push and Integration: Keep the default settings.
After you finish configuring the parameters, click Submit.
FAQ
Why am I not receiving alerts after completing the configuration?
Check the following items in order:
Security Center push switch: In Step 1, verify that the Cloud Monitor Push switch is enabled for the alert types you want to receive.
Event subscription policy: In Step 4, check the event subscription policy to confirm that its filter conditions, such as event type and event level, match the alerts you expect to receive.
Lark keywords (most common reason): If you use Lark, ensure that your bot's Custom Keywords match the content of the actual alert message. Use generic terms like
alertandevent.Webhook URL: In Cloud Monitor's Alert Contacts, use the Test function to check if the webhook URL is reachable. Confirm the URL is correct and not blocked by a firewall or other network policies.
Cloud Monitor Event History: Go to Event Center > Event History to check whether events were successfully received and pushed. If an event exists but the push failed, a failure reason is usually provided.
How can I reduce alert noise?
Enable deduplication: In the event subscription policy from Step 4, configure deduplication. For example, set it to "Merge and notify for the same event within 1 minute".
Use precise filters: In the same event subscription policy, filter out less important alerts by setting the event level (for example, subscribe to High-risk only) or specifying an event name.
What should I do if the webhook test returns a non-200 status code?
A non-200 status code means Cloud Monitor failed to send the message to your bot. Common reasons include:
Incorrect URL: The copied webhook URL is incomplete or contains errors.
IP allowlist restrictions: Some messaging tools, like Lark, may have security settings that require you to add the Cloud Monitor server IP addresses to an IP allowlist.
Keyword mismatch (Lark): The message content does not contain any of the configured keywords, causing the Lark bot to block it.
Rate limiting: Sending too many messages in a short period triggered the messaging tool's rate limit. For example, WeCom bots have a limit of 15 messages per minute.