The Security Center agent supports four advanced features that let you harden agent integrity, improve threat detection coverage, and control resource consumption: Agent Protection, Local File Detection Engine, In-depth Detection Engine, and Client Resource Management.
Agent Protection
Agent Protection is a built-in self-protection mechanism that blocks unauthorized attempts to remove or terminate the Security Center agent. When an attacker compromises a server and tries to disable the agent, Agent Protection intercepts the attempt and keeps the agent running.
Agent Protection secures the agent process itself. It does not directly provide server security scanning or threat detection.
What Agent Protection covers
When Agent Protection is active, the following actions are blocked from unauthorized processes on a protected server:
Uninstalling the agent
Terminating core agent processes
Interrupting security protection continuity caused by agent failure
Agent Protection depends on the operating system and kernel version of the server. If the server's kernel is not supported, the protection status displays Protection failed: Incompatible kernel version and the feature does not take effect. See Supported operating systems and kernel versions for the full compatibility list.
Enable Agent Protection
Before you begin, ensure that you have:
A Security Center account (free or paid editions are both supported)
The Security Center agent installed on the target servers
Log on to the Security Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center console.
In the left navigation pane, choose System Settings > Feature Settings. In the upper-left corner, select the region where your assets are located: Chinese Mainland or Outside Chinese Mainland.
Click the Settings > Agent Settings tab. In the Agent Protection section, turn on the Defense Mode switch.
To the right of Protection Scope, click Manage.
In the Agent Protection panel, select the servers to protect, then click OK.
Agent Protection is automatically applied to all servers in the protection scope that have the agent installed. Protection takes effect immediately.
If you disable Agent Protection, the protection mechanism stops after 5 minutes.
Verify Agent Protection status
Log on to the Security Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center console.
In the left navigation pane, choose Assets > Host. Select the region in the upper-left corner.
In the host list, find the target server. Click the server name or click View in the Actions column.
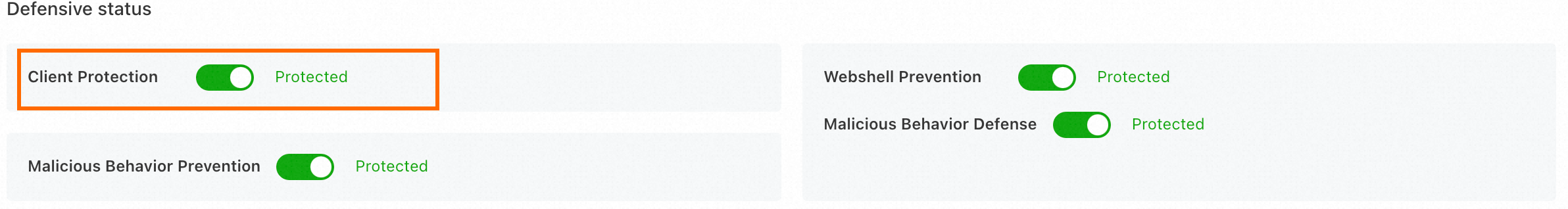
On the server details page, click the Basic Information > Details tab. In the Defense Status section, check the Agent Protection status.
Uninstall the agent when Agent Protection is enabled
Agent Protection restricts uninstallation to authorized methods only. Choose the approach that fits your workflow:
| Method | When to use |
|---|---|
| Uninstall from the console | Centralized management; no direct server access required |
| Disable protection first, then uninstall locally | Direct server access available; disable Agent Protection for the server in the console first, then run the uninstall command locally |
Local File Detection Engine
The Local File Detection Engine scans files directly on the server using a proprietary Alibaba Cloud threat detection engine. This engine reduces performance overhead from data uploads and cloud-based scanning, which improves detection efficiency. After you enable this feature, files are scanned using a dual-engine mode that combines local and cloud-based scanning. The system first uses the local engine to scan files. If no threats are found, the files are then uploaded to the cloud for a secondary scan to ensure comprehensive detection.
Enable local file detection
Before you begin, ensure that you have:
Edition: Enterprise or Ultimate. If your current edition is different, upgrade Security Center.
Protection edition assigned: The server must have the purchased edition assigned. See Attach a protection edition to a server.
Pay-as-you-go billing: Required for Host and Container Security. See Purchase Security Center.
Protection level assigned: The server protection level must be set to Host Protection or Host and Container Protection. See Attach a protection level to a server.
Log on to the Security Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center console.
In the left navigation pane, choose System Settings > Feature Settings. Select the region in the upper-left corner.
Click the Settings > Agent Settings tab. In the Local File Detection Engine section, turn on the File Test switch.
To the right of Installation Scope, click Manage.
In the Local File Detection Engine panel, select the servers to enable, then click OK.
In-depth Detection Engine
The In-depth Detection Engine helps you discover advanced security risks, such as rootkits, tunneling, and backdoors.
Enable deep detection
Before you begin, ensure that you have:
Edition: Enterprise or Ultimate. If your current edition is different, upgrade Security Center.
Protection edition assigned: The server must have the purchased edition assigned. See Attach a protection edition to a server.
Pay-as-you-go billing: Required for Host and Container Security. See Purchase Security Center.
Protection level assigned: The server protection level must be set to Host Protection or Host and Container Protection. See Attach a protection level to a server.
Log on to the Security Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center console.
In the left navigation pane, choose System Settings > Feature Settings. Select the region in the upper-left corner.
Click the Settings > Agent Settings tab. In the In-depth Detection Engine section, turn on the Depth Test switch.
To the right of Installation Scope, click Manage.
In the In-depth Detection Engine panel, select the servers to enable, then click OK.
Client Resource Management
The Security Center agent consumes a small amount of server resources during normal operation. Client Resource Management lets you choose a resource mode that balances protection coverage against server performance.
If the agent exceeds the memory or CPU limit configured for its mode, the agent pauses automatically. It restarts once resource usage drops to an acceptable level.
Choose a resource mode
| Mode | Memory limit | CPU limit | Supported editions | Default | Best for |
|---|---|---|---|---|---|
| Low Consumption Mode | Up to 200 MB | Up to 10% | All editions | Yes (for newly added assets) | Servers with low security requirements. Some resource-intensive detection features are downgraded, which may delay threat detection. We recommend that you enable Smooth Mode. |
| Smooth Mode | Up to 300 MB | Up to 30% | Anti-virus, Advanced, Enterprise, Ultimate | No | Critical business servers. The agent collects more data to support timely risk detection. |
| Custom Mode | 200, 300, 400, or 500 MB | Single-core: 5%, 10%, 20%, or 30%; Overall: 5%, 10%, 20%, 30%, 40%, 50%, or 60% | Enterprise, Ultimate | No | Major events or situations where you need precise control over memory and CPU consumption. |
Custom Mode CPU threshold enforcement:
Linux: The limit applies to single-core CPU usage.
Windows: The limit applies to overall CPU usage.
Setting the CPU or memory threshold too low may cause some detection capabilities to fail. Configure this setting with caution.
In Custom Mode, more types of alerts are detected and the detection engine is more sensitive. This may increase the false positive rate. Monitor and handle alerts promptly.
Each server can be assigned only one mode. If you assign Custom Mode to a server already in Smooth Mode, the mode changes to Custom Mode.
Set a resource mode
Log on to the Security Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center consoleSecurity Center console.
In the left navigation pane, choose System Settings > Feature Settings. Select the region in the upper-left corner.
Click the Feature Settings > Agent Settings tab. In the Client Resource Management section, click Manage to the right of Smooth Mode or Custom Mode.
In the panel, select the servers to apply the mode to, then click OK.
(Optional) If you selected Custom Mode, adjust the memory and CPU usage thresholds. Higher thresholds allow more precise protection.
Appendix: Supported operating systems and kernel versions for agent self-protection
The following table lists the operating systems and kernel versions that support agent self-protection.
| Operating system | Supported versions | Supported kernel series |
|---|---|---|
| Windows (64-bit) | Windows Server 2008 R2, 2012 R2, 2016, 2019, 2022, 2025 | All versions |
| CentOS (64-bit) | CentOS 6.3–6.10, 7.0–7.9, 8.0–8.5 | 2.6.32, 3.10.0, 4.x.x, 5.x.x series |
| Ubuntu (64-bit) | Ubuntu 14.04, 16.04, 18.04, 20.04 | 3.x.x, 4.x.x, 5.x.x series |
| Alibaba Cloud Linux / Alinux (64-bit) | Alinux 2.1903 | 3.10.0, 4.x.x, 5.x.x series |
| Anolis (64-bit) | All versions | 3.10.0, 4.x.x series |
| RHEL | RHEL 6, 7, 8 | Selected 3.10.0 and 2.6.32 builds |
For the full list of verified kernel builds, expand the sections below.
CentOS (64-bit)
Ubuntu (64-bit)
Alibaba Cloud Linux / Alinux (64-bit) — Alinux 2.1903
Anolis (64-bit) — All versions
RHEL — RHEL 6, 7, and 8
3.10.0-1160.42.2.el7.x86_64
3.10.0-1160.76.1.el7.x86_64
2.6.32-754.el6.x86_64
Agent communication management
Configure the file collection limit for the agent to meet your business and security requirements. This setting helps you balance effective data collection with minimal resource consumption.
Important: If Client Resource Management is set to custom mode, setting the file collection limit too low may delay data collection. Configure this setting carefully.
Log on to the Security Center console.
In the left-side navigation pane, choose . In the upper-left corner of the console, select the region where your assets are located: Chinese Mainland or Outside Chinese Mainland.
Select the tab. In the Agent Communication Management section, configure the file collection limit.
Selecting Custom allows you to set the file collection frequency. The valid range is 100 to 10,000 collections per second.
Selecting Unlimited removes the limit on the agent's file collection frequency.