Resource Access Management (RAM) supports OpenID Connect (OIDC) as a federation method. This allows applications to exchange an OIDC token from a trusted identity provider (IdP) for temporary Alibaba Cloud credentials, enabling secure, role-based access to your cloud resources.
Use cases
Role-based SSO with OIDC is a secure alternative to using long-term AccessKey pairs for applications that need to access Alibaba Cloud resources. Common use cases include:
Enterprise applications: You can register internal applications with your corporate IdP (such as Okta, Google Workspace, or your own OIDC-compliant system). The application can then obtain an OIDC token and exchange it for temporary Alibaba Cloud credentials to perform its tasks.
Third-party and mobile applications: You can develop applications that allow users to log on with their identities from external systems. If these providers support OIDC, your application can use the issued OIDC tokens to assume a RAM role and interact with Alibaba Cloud services on the user's behalf.
How role-based OIDC SSO works
The OIDC federation process involves establishing trust between your IdP and Alibaba Cloud, then exchanging tokens for temporary credentials.
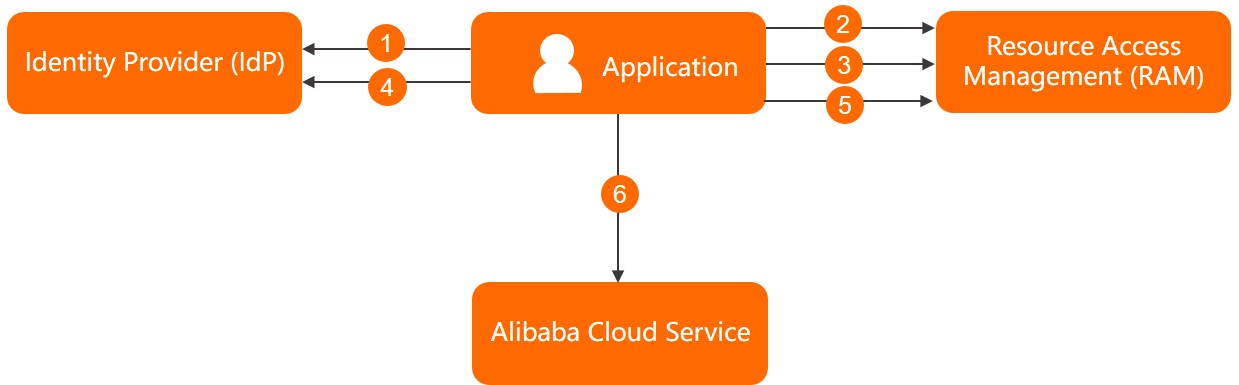
Configure trust: You first establish a trust relationship by creating an OIDC IdP in the RAM console and a corresponding RAM role that trusts this IdP.
Request OIDC token: Your application authenticates a user against the external IdP and requests an OIDC token.
Exchange for STS token: Your application calls the AssumeRoleWithOIDC API operation of Alibaba Cloud Security Token Service (STS), providing the OIDC token and the ARN of the RAM role it wants to assume.
Validate and issue STS token: STS validates the OIDC token's signature, issuer, and audience (client ID). If the validation succeeds, STS returns a temporary security credential (an STS token).
Access resources: Your application uses the STS token to make authenticated API calls to Alibaba Cloud resources, with the permissions granted by the assumed RAM role.
Key concepts
Concept | Description |
OIDC | OIDC is an identity layer built on top of the OAuth 2.0 protocol. It allows clients to verify a user's identity based on the authentication performed by an authorization server and to obtain basic profile information about the user. |
OIDC token (ID token) | A JSON Web Token (JWT) that contains claims about the authentication event, such as the user's ID, the issuer of the token, and the client for whom it was intended. |
Client ID | A unique identifier for an application that is registered with an OIDC IdP. It is included as the audience ( |
Issuer URL | The URL that identifies the OIDC IdP. It is included as the issuer ( |
Thumbprint (Fingerprint) | A unique identifier for the root CA certificate of an OIDC IdP's server. It is used to verify the authenticity of the IdP's public keys. For more information, see Obtain the thumbprint for an OIDC IdP. Note Before rotating your IdP's certificate, add the thumbprint of the new certificate to the OIDC provider configuration in RAM. After confirming that federation with the new certificate works, you can remove the old thumbprint. |
STS token | A temporary security credential provided by Alibaba Cloud Security Token Service (STS). In federated SSO, the user exchanges the SAML assertion or OIDC token for an STS token to make authenticated API calls to Alibaba Cloud services. |
Configuration tutorial
For a step-by-step guide, see Configure federation with Okta.
Service quotas
Resource | Maximum |
OIDC IdPs per Alibaba Cloud account | 100 |
Client IDs per OIDC IdP | 50 |
Thumbprints per OIDC IdP | 5 |