You can create a Resource Access Management (RAM) role to delegate permissions to users and roles in another trusted Alibaba Cloud account. This allows you to grant cross-account access to your resources without sharing long-term credentials.
Procedure
Log on to the RAM console as a RAM administrator.
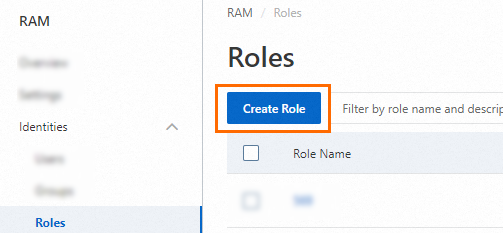
In the left-side navigation pane, choose .
On the Roles page, click Create Role.
On the Create Role page, set Principal Type to Cloud Account. Configure the trusted account and click OK.
 For Principal Name, choose one of the following:
For Principal Name, choose one of the following:Current Account: Allows all RAM users and roles within the current account to assume this role.
Other Account: Allows RAM users and roles from a different Alibaba Cloud account to assume this role. Enter the ID of the trusted account. You can find an account ID on the Security Settings page. For more information about cross-account access, see Access resources across Alibaba Cloud accounts.
(Optional) To refine the trust policy and allow only specific principals to assume the role, click Switch to Policy Editor.
The following JSON example modifies the trust policy to allow only the RAM user
Alicefrom account100******0719to assume the role.Visual Editor
In the Principal section, specify the RAM user.


JASON Editor
In the
RAMfield of thePrincipalelement, specify the RAM user.{ "Version": "1", "Statement": [ { "Effect": "Allow", "Principal": { "RAM": "acs:ram::100******0719:user/Alice" }, "Action": "sts:AssumeRole" } ] }
In the Create Role dialog box, enter a Role Name and click OK.
What to do next
Grant permissions to the RAM role.
A newly created role has no permissions. You must attach permission policies to the role before it can be used.
Use the RAM role.
A principal (a RAM user or role) in the trusted account can now assume this role. They can do this either through the console or by calling the
AssumeRoleAPI operation to obtain temporary credentials from the Security Token Service (STS). These credentials can then be used to access the authorized resources. For more information, see Assume a RAM role.