Join your ApsaraDB RDS for SQL Server instance to your company's Active Directory (AD) domain to enable centralized identity authentication and permission management. This guide uses an Alibaba Cloud Elastic Compute Service (ECS) instance as the domain controller example, but the domain controller can also run on another cloud platform or in an on-premises data center.
After you configure the AD domain feature, you can create accounts in your self-managed AD domain and grant those accounts access to RDS SQL Server. However, if you create superuser (System Admin) or host accounts through the AD domain feature, RDS cannot control those accounts' permissions, and Alibaba Cloud cannot guarantee the SLA for the instance.
Prerequisites
Before you begin, make sure the following requirements are met.
RDS instance requirements:
| Requirement | Details |
|---|---|
| Instance type | General-purpose or Dedicated. Shared instances are not supported. |
| Billing method | Subscription or pay-as-you-go. Serverless ApsaraDB RDS for SQL Server instances are not supported. |
| Account | You must use an Alibaba Cloud account to perform the configuration. |
Check the instance type and billing method on the Basic Information page of the instance.
Domain controller requirements:
| Requirement | Details |
|---|---|
| Operating system | Windows Server 2012 R2 or later. Windows Server 2016 or later is recommended. |
| DNS configuration | The domain controller must also act as the DNS server. The domain controller's IP address must match the DNS server address. |
| Domain account permissions | The account used to join the RDS instance to the domain must be a member of the Domain Admins group. |
Network connectivity:
The RDS instance and the domain controller must have bidirectional network connectivity.
If you deploy the domain controller on an ECS instance (as shown in this guide):
Place the RDS instance and the ECS instance in the same Virtual Private Cloud (VPC) to simplify network configuration.
Configure the ECS security group to allow inbound traffic from the private IP address of your RDS instance. For instructions, see Add a security group rule.
If the ECS system firewall is enabled, also add a rule to allow traffic from the RDS instance's private IP address.
Limits
Joining or leaving an AD domain requires a restart of the Windows operating system on the RDS instance. Perform these operations during off-peak hours to minimize business impact.
AD domain-joined instances do not support:
Step 1: Configure the domain controller on the ECS instance
Log on to the ECS console.
In the left-side navigation pane, choose Instances & Images > Instances.
In the top navigation bar, select the region and resource group of the resource that you want to manage.

On the Instance page, click the ID of the target instance.
Remotely log on to the Windows Server 2016 operating system of the ECS instance.
Search for and open Server Manager.
Click Add roles and features and configure the settings as follows.
Page Settings Installation Type Keep the default settings. Server Selection Keep the default settings. Server Roles Select Active Directory Domain Services and click Add Features in the dialog box that appears. Then select DNS Server and click Add Features. If a message indicates that your computer does not have a static IP address, assign one to prevent the DNS server from becoming unavailable due to IP address changes. 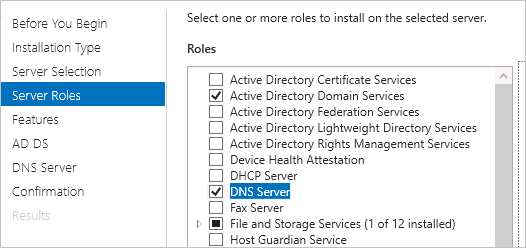
Features Keep the default settings. AD DS Keep the default settings. DNS Server Keep the default settings. Confirmation Click Install. After the installation is complete, click Close.
In the left navigation pane, click AD DS. In the upper-right corner, click More.
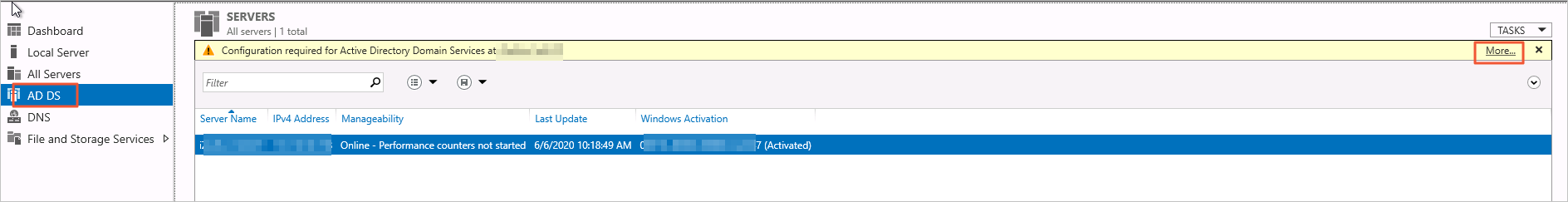
Click Promote this server to a domain... and configure the settings as follows.
Page Settings Deployment Configuration Select Add a new forest and set the domain name. 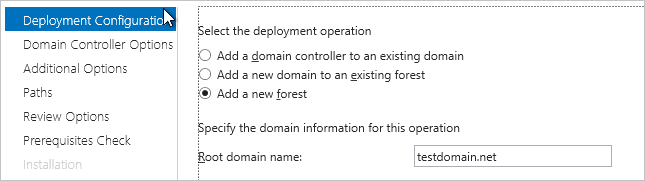
Domain Controller Options Set the recovery model password. 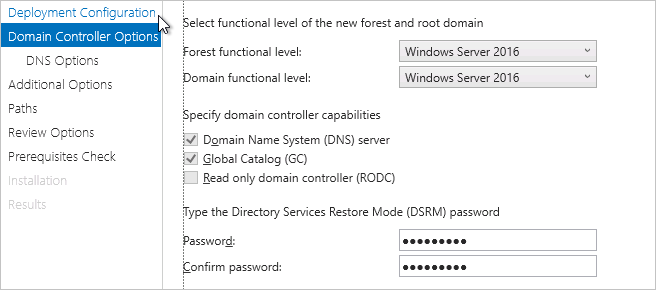
DNS Options Clear the Create DNS delegation checkbox. 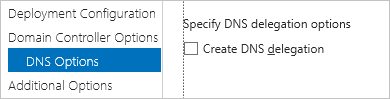
Additional Options Keep the default settings. Paths Keep the default settings. Review Options Keep the default settings. Prerequisites Check Click Install. The system restarts automatically after installation. 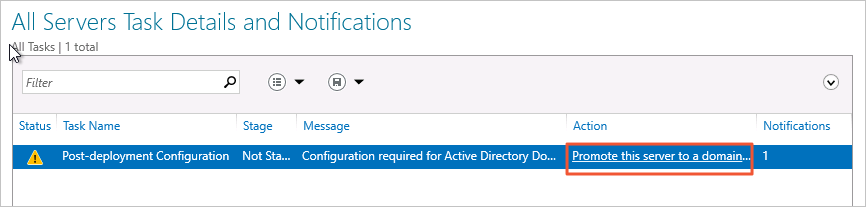
After the system restarts, open Server Manager again.
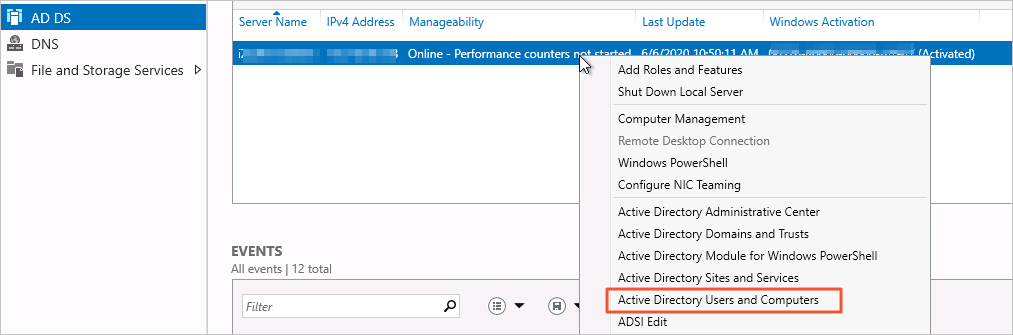
In the left navigation pane, click AD DS. Right-click the target domain controller and select Active Directory Users and Computers.
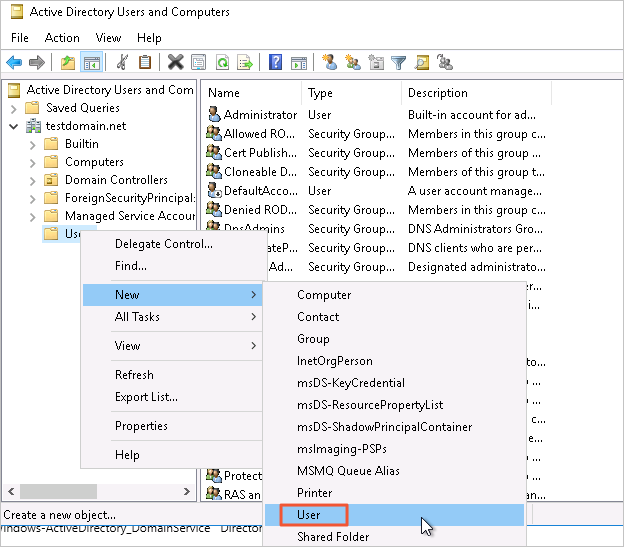
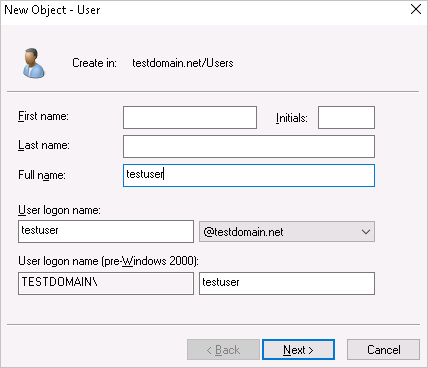
Right-click Users > testdomain.net and choose New > User.
Set the user logon name and click Next.
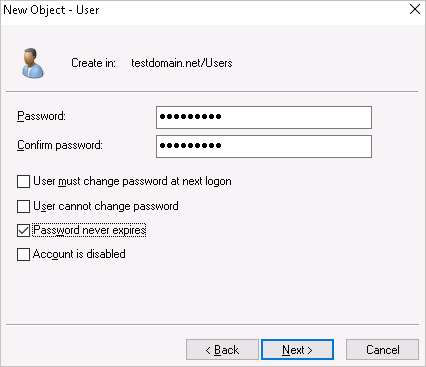
Set the logon password, select Password never expires, and click Next and then Finish.
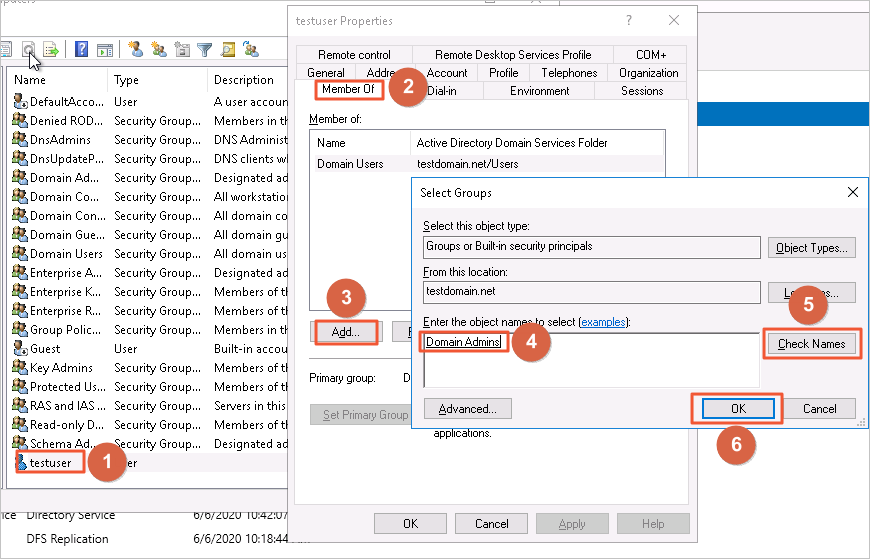
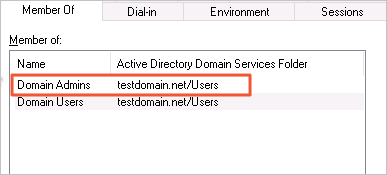
Double-click the newly created user and add the user to the Domain Admins group.
Step 2: Configure the ECS security group
Add inbound rules to allow the RDS instance to communicate with the domain controller.
Log on to the ECS console.
In the left-side navigation pane, choose Instances & Images > Instances.
In the top navigation bar, select the region and resource group of the resource that you want to manage.

On the Instance page, click the ID of the target instance.
On the top navigation bar, select Security Groups. In the Operation column of the security group, click Manage Rules.
On the Inbound tab, click Add Rule to open the required ports.
Protocol type Port range Description TCP 88 Kerberos authentication TCP 135 Remote Procedure Call (RPC) TCP/UDP 389 Lightweight Directory Access Protocol (LDAP) TCP 445 Common Internet File System (CIFS) TCP 3268 Global Catalog TCP/UDP 53 DNS TCP 49152–65535 Default dynamic port range. Enter the range as 49152/65535.
Step 3: Configure AD domain services for the RDS instance
Go to the Instances page. In the top navigation bar, select the region where your RDS instance resides. Click the ID of the instance.
In the left-side navigation pane, click Accounts.
Click the AD Domain Services tab, then click Configure AD Domain Services.
In the Configure AD Domain Services dialog box, set the following parameters.
Select I have read and understand the impact of AD Domain Services on the RDS Service Level Agreement, then click OK. Wait for the AD domain configuration to complete.
FAQ
What permissions does RDS use to join a domain? Can I limit those permissions?
By default, the account used to join the RDS instance to the domain must be a member of the Domain Admins group.
If you prefer to follow the least privilege principle, you can delegate the minimum required permissions to a non-admin account. However, if you use a least-privilege account to leave the domain, you must manually delete the corresponding computer object from the domain controller afterward — otherwise, you cannot rejoin the same RDS instance to the domain.
To delegate the minimum permissions:
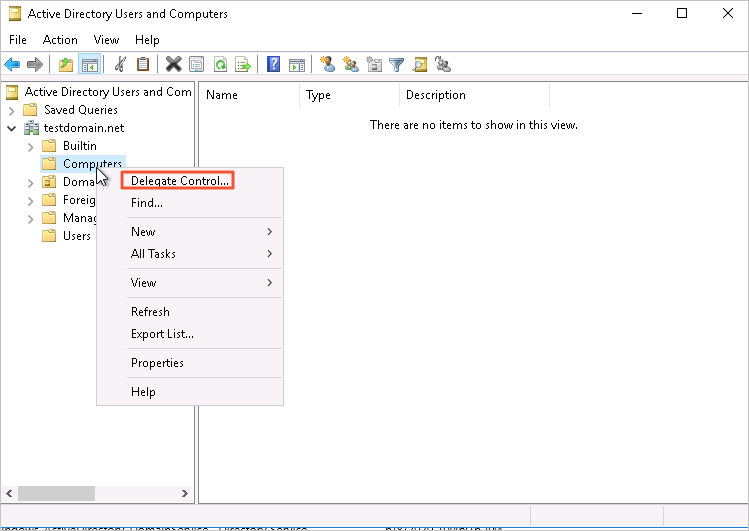
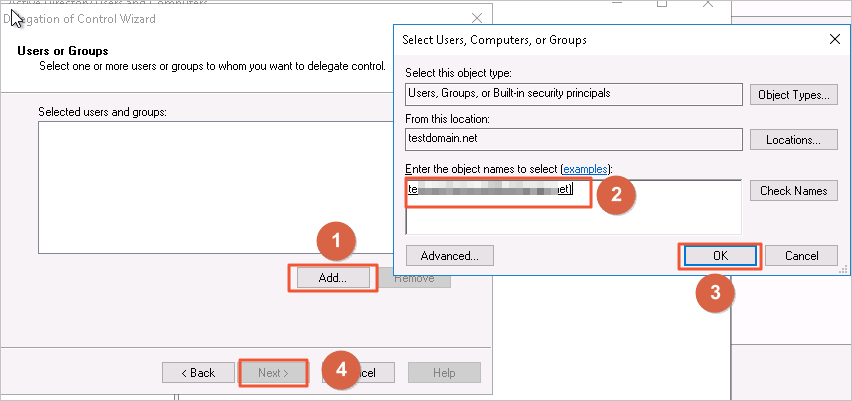
Create a new user and confirm the user is a member of the Domain Users group. Right-click Computers, select Delegate Control..., and add the newly created user.
Select Create a custom task to delegate and click Next.
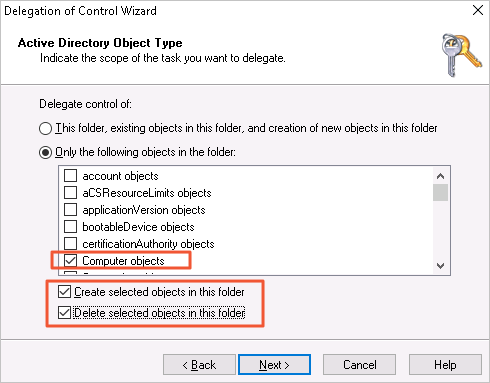
Select Only the following objects in the folder, select the options shown in the figure, and click Next.
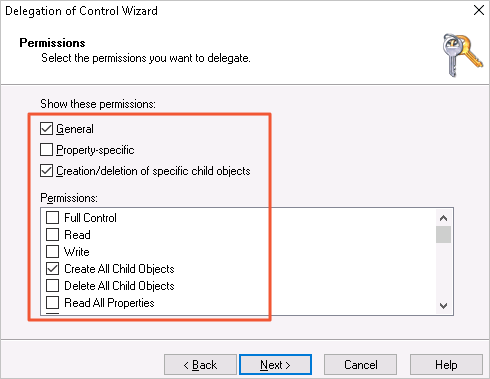
Select the options shown in the figure and click Next until the wizard is complete.
What's next
Use the following APIs to view, modify, or remove the AD domain configuration: