To enable distributed transactions between specific Elastic Compute Service (ECS) instances and an ApsaraDB RDS for SQL Server instance, configure a distributed transaction whitelist on the RDS side and open the required ports on the ECS security group.
Steps overview:
Add the ECS instance's IP address to the RDS IP whitelist.
Add the ECS instance's computer name and IP address to the distributed transaction whitelist.
Add inbound security group rules on the ECS instance to allow traffic on ports 135 and 1024–65535.
Prerequisites
Before you begin, make sure that:
The RDS instance runs one of the following SQL Server versions: SQL Server 2022 EE (Always On), SQL Server 2019 EE (Always On), SQL Server 2017 EE (Always On), SQL Server 2016 EE, SQL Server 2012 EE, SQL Server 2022 SE, SQL Server 2019 SE, SQL Server 2017 SE, SQL Server 2016 SE, SQL Server 2012 SE, or SQL Server 2008 R2 with cloud disks.
The RDS instance uses the general-purpose or dedicated instance family.
The RDS instance uses the subscription or pay-as-you-go billing method.
To verify the instance version, family, and billing method, go to the Basic Information page of the RDS instance.
Limitations
The following configurations are not supported:
Shared instance family
Serverless instances
Usage notes
After a major engine version upgrade, minor engine version update, or instance migration across zones, the host name and IP address of the underlying ECS instance may change. After any of these operations, update the ECS security group rules to match the current whitelist settings.
To view the current host name and IP address, go to Data Security > Distributed Transaction Whitelist in the RDS console.
Configure the RDS instance
Step 1: Add the ECS IP address to the RDS whitelist
Distributed transactions require the RDS instance to accept connections from the ECS instance. Add the ECS instance's IP address to the default IP address whitelist.
Log on to the ApsaraDB RDS console and go to the Instances page. In the top navigation bar, select the region where the RDS instance resides, then click the instance ID.
In the left-side navigation pane, click Whitelist and SecGroup. On the Whitelist Settings tab, click Modify to the right of the
defaultwhitelist and add the ECS instance's IP address.The following figure shows where to find the IP addresses of an ECS instance.
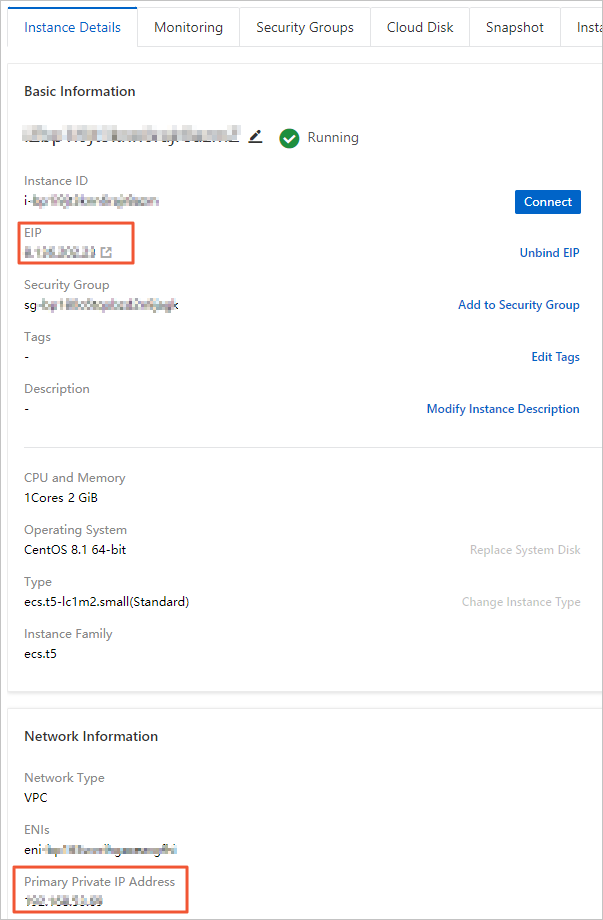
If the ECS instance and the RDS instance are in the same virtual private cloud (VPC), enter the ECS instance's private IP address.
If they are in different VPCs, enter the ECS instance's public IP address. You also need to apply for a public endpoint for the RDS instance. For details, see Apply for or release a public endpoint.
To find the ECS instance's IP addresses, go to the Instance Details page of the ECS instance in the ECS console. For more information, see View IP addresses.
Click OK.
Step 2: Configure the distributed transaction whitelist
In the left-side navigation pane, click Data Security, then click the Distributed Transaction Whitelist tab.
Click Create Whitelist. In the dialog box, configure the following parameters, then click OK.
Parameter Description Whitelist Name Enter a name 2–32 characters long. Allowed characters: digits, lowercase letters, and underscores ( _). Must start with a lowercase letter and end with a lowercase letter or digit.IP Addresses Enter entries in the format IP address,Hostname, where the hostname is the Windows computer name of the ECS instance. Example:192.168.1.100,k3ecstest. For multiple entries, put each entry on a separate line. To find the computer name, open Control Panel and go to System and Security > System
Configure the ECS instance
Add inbound security group rules to open the ports that MSDTC uses for distributed transaction coordination.
Log on to the ECS console.
In the left-side navigation pane, choose Instances & Images > Instances.
In the top navigation bar, select the region where the ECS instance resides.
Find the ECS instance and click the instance ID.
Click Security Groups in the top navigation bar.
Find the security group and click Manage Rules in the Actions column.
On the Inbound tab, click Add Rule and configure the following parameters, then click Save.
Port 135 is the fixed port for the Remote Procedure Call (RPC) service.
Parameter Value Action Allow Priority 1 (default) Protocol type Custom TCP Port range 135 Source The two IP addresses shown in Data Security > Distributed Transaction Whitelist in the RDS console. 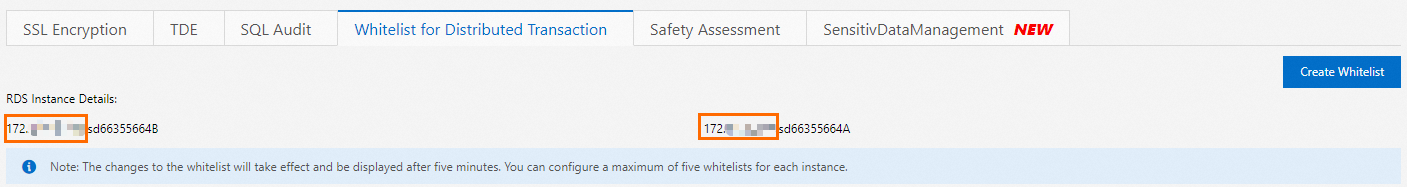 You can also call the DescribeDBInstanceIpHostname API operation to query these IP addresses.
You can also call the DescribeDBInstanceIpHostname API operation to query these IP addresses.Description Enter a description 2–256 characters long. Cannot start with http://orhttps://.Add a second inbound rule with the same settings, except set Port range to 1024/65535.
Troubleshooting
"Communication with the underlying transaction manager has failed"
This error has two common causes:
The host name or IP address of the underlying ECS instance changed. This typically happens after a major engine version upgrade, minor engine version update, or instance migration across zones. Go to Data Security > Distributed Transaction Whitelist in the RDS console, check the current host name and IP address, then update the ECS security group rules to match.
The distributed transaction manager is not running properly. Check for incorrect settings, permission issues, or insufficient server resources. Also verify that the connection to the transaction manager is stable.