This topic describes how to configure and enable third-party authentication for an RDS Supabase instance using GitHub as an example.
Background information
RDS Supabase supports integration with major third-party identity providers (IdPs), such as GitHub, Google, WeChat, and Alipay, to enable OAuth authentication. This feature allows users to log on to RDS Supabase applications with their existing third-party accounts. This simplifies the registration process and improves the user experience.
For more information about all supported providers and their parameter settings, see Alibaba Cloud RDS Supabase Authentication.
The following sections use GitHub as an example to describe how to configure and enable third-party authentication for an RDS Supabase instance.
Prerequisites
You have created an active Alibaba Cloud RDS Supabase instance.
You have a GitHub account.
Procedure
The configuration process consists of three main parts: creating a GitHub OAuth application, configuring the RDS Supabase instance, and verifying the feature.
Step 1: Create and configure a GitHub OAuth application
First, create an OAuth application on GitHub to obtain the Client ID and Client Secret for API authentication.
Log on to GitHub and go to the developer settings page.
In the navigation pane on the left, choose OAuth Apps and then click New OAuth App.
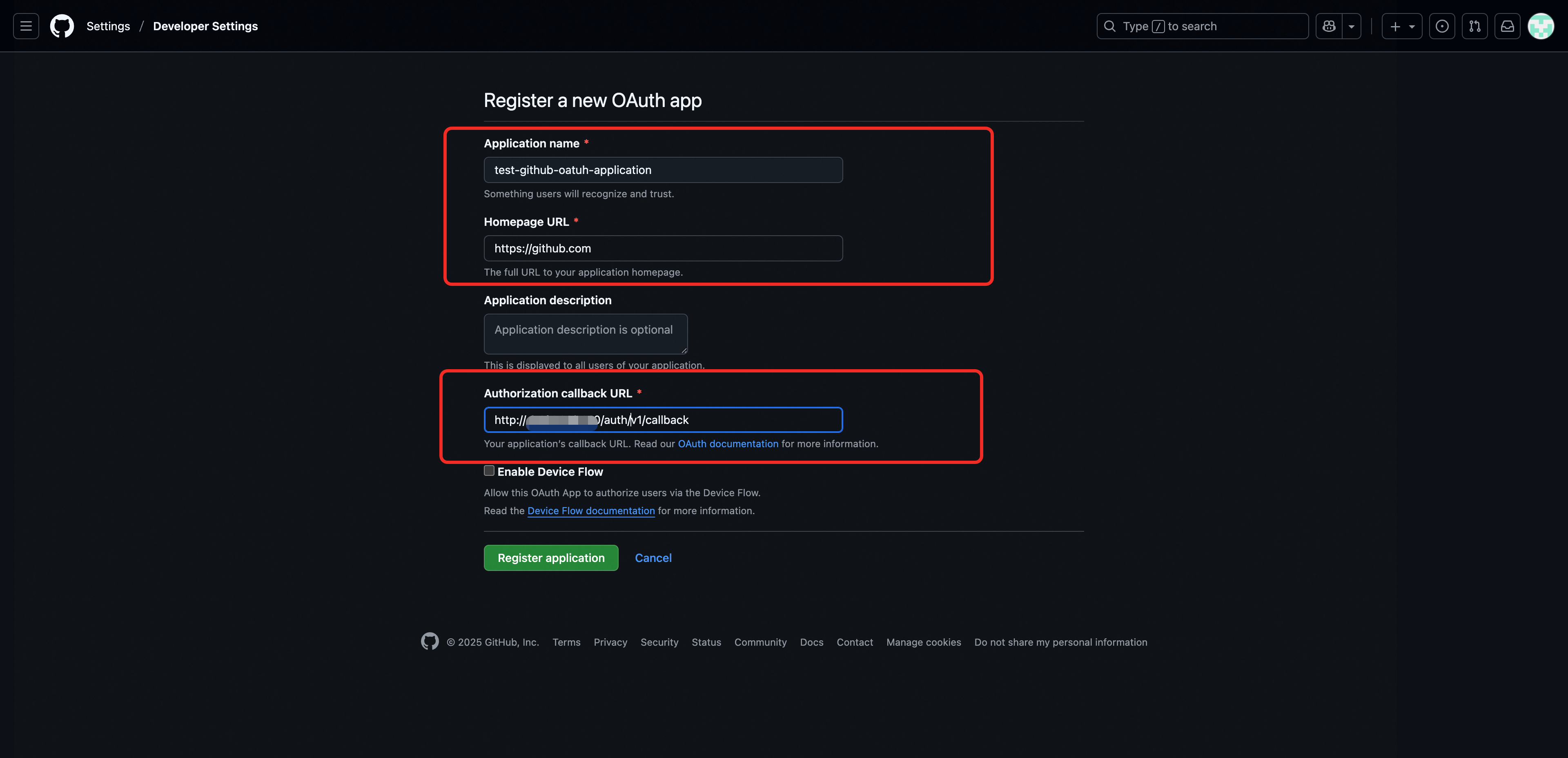
On the registration page, enter the application information:
Application name: Enter a name for your application.
Homepage URL: Enter the homepage URL of your application.
Authorization callback URL: Enter the public endpoint of your RDS Supabase instance and append the path
/auth/v1/callback. The format ishttps://<Supabase public endpoint>/auth/v1/callback.NoteDo not include the port number in the Supabase public endpoint.
Click Register application.
After registration, the page automatically redirects to the application details page. Record the Client ID displayed on the page.
Click Generate a new client secret to generate a client secret.
ImportantThe GitHub Client Secret is displayed in full only once when it is generated. Securely save it for later configuration.
Step 2: Configure RDS Supabase authentication parameters
After you obtain the credentials for the GitHub OAuth app, configure the required parameters in your RDS Supabase instance to enable this authentication method.
Go to the RDS console home page. In the navigation pane on the left, click AI Application Development. Select a region at the top and then click the Project ID to go to the RDS Supabase instance details page.
In the navigation pane on the left, click Auth Configuration.
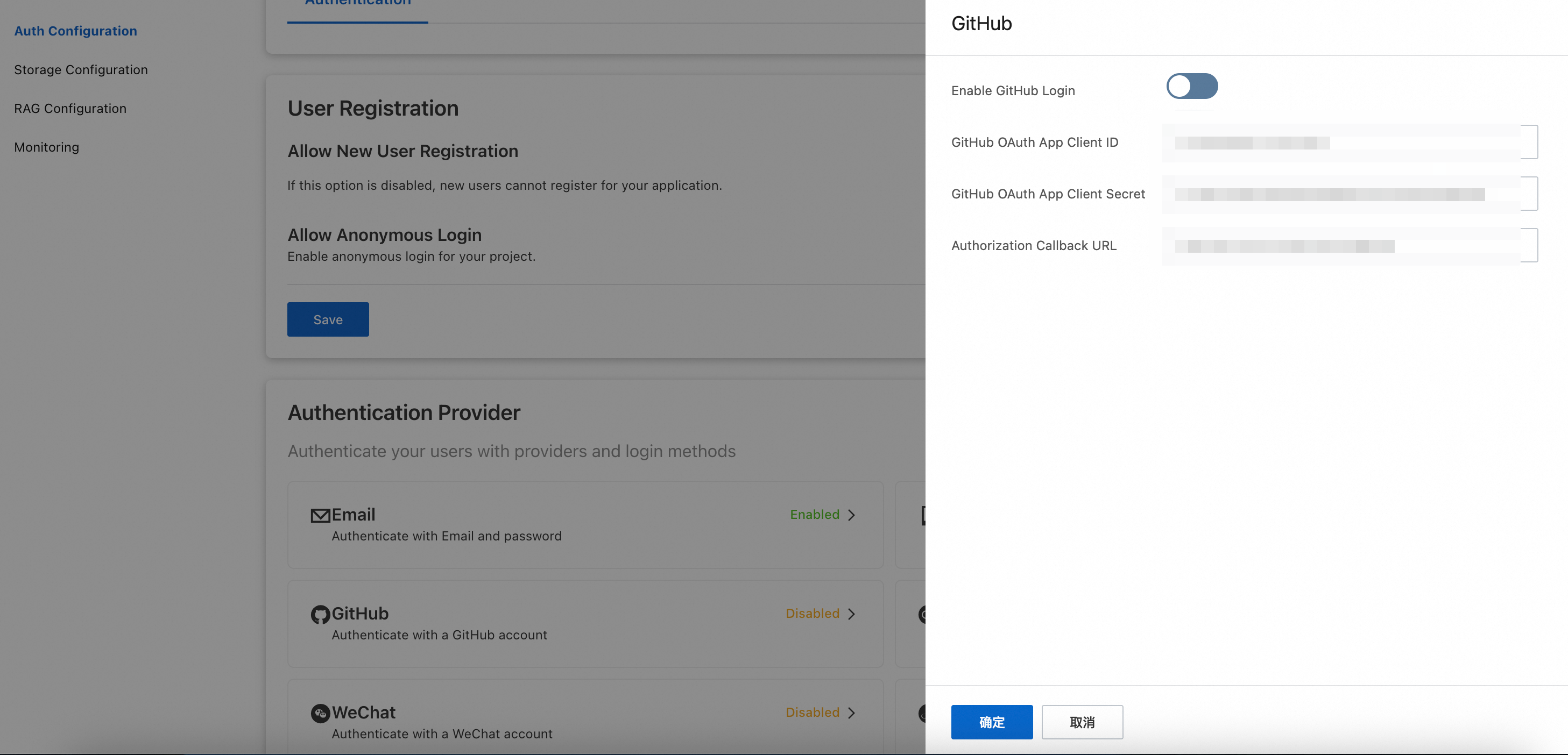
Click Identity Providers > GitHub and configure the following parameters:
Enable GitHub Logon: Turn on this switch to enable GitHub logon.
Client ID of the GitHub OAuth App: Enter the Client ID of the GitHub OAuth app that you obtained in Step 1.
Client Secret of the GitHub OAuth App: Enter the Client Secret of the GitHub OAuth app that you obtained in Step 1.
Authorization callback URL: Enter the same Authorization callback URL that you configured in Step 1.
After you complete the configuration, click Confirm. The instance automatically restarts for the settings to take effect. Wait for the restart to be completed.
Step 3: Configure the RDS Supabase whitelist
To ensure that your application can access the RDS Supabase instance, add its public IP address to the RDS Supabase access whitelist.
Go to the RDS console home page. In the navigation pane on the left, click AI Application Development.
Select a region at the top. In the RDS Supabase list, click the Project ID of the target instance to go to its details page.
On the Basic Information page, in the Whitelist Information section, click Add Whitelist Group to add the IP address of the target client to the whitelist.
Step 4: Allow the instance to access the public network
To ensure that the RDS Supabase instance can send API requests to the GitHub server over the public network to complete the OAuth authentication flow, enable Allow Instance to Access Public Network.
Go to the Basic Information page of the instance.
Turn on the Allow Instance to Access Public Network switch in the Network Information section.
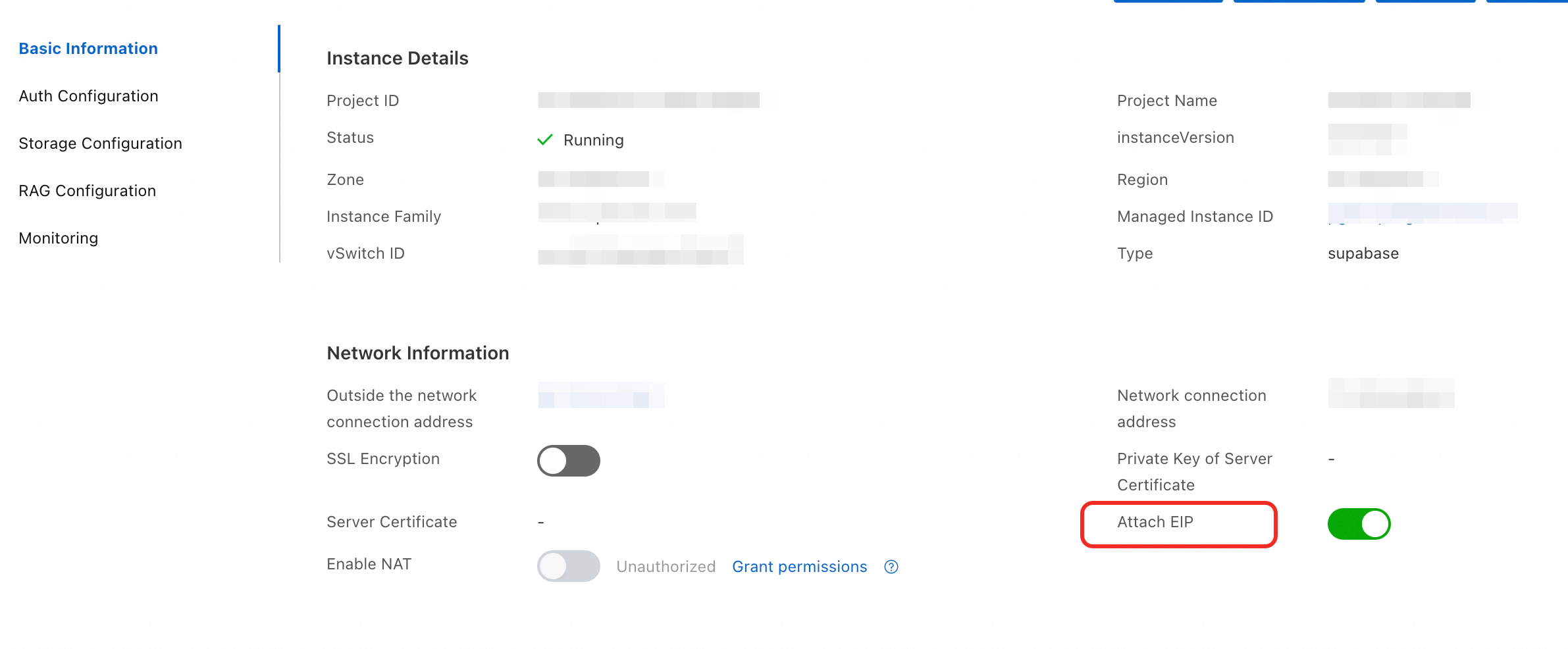
If the third-party application is in a region outside China, purchase an RDS Supabase instance in a region outside China to ensure the stability and performance of the third-party authentication feature.
Step 5: Verify the GitHub authentication feature
After you complete the preceding configurations, you can build a simple frontend project to verify that the GitHub logon flow works as expected.
Initialize the project structure
Create a project folder that contains the following files:
index.html: The frontend page structure.main.js: The core authentication logic.supabase-config.js: The RDS Supabase connection configuration.package.json: The project dependencies and script configuration.
Write the code
Create the following files in the project and add the corresponding content.
Obtain and configure Supabase connection information
Before you run the project, see RDS Supabase SDK User Guide to obtain the SUPABASE_URL and Anon Key for Supabase. Replace the values of url and anonKey in the
supabase-config.jsfile.Run and test the project
Open a terminal in the project's root directory. Run the following commands to install dependencies and start the server:
npm install npm run devAfter the commands are successfully executed, open a browser and visit
http://localhost:5173.On the page, click Log on with GitHub. The page redirects to the GitHub authorization page.
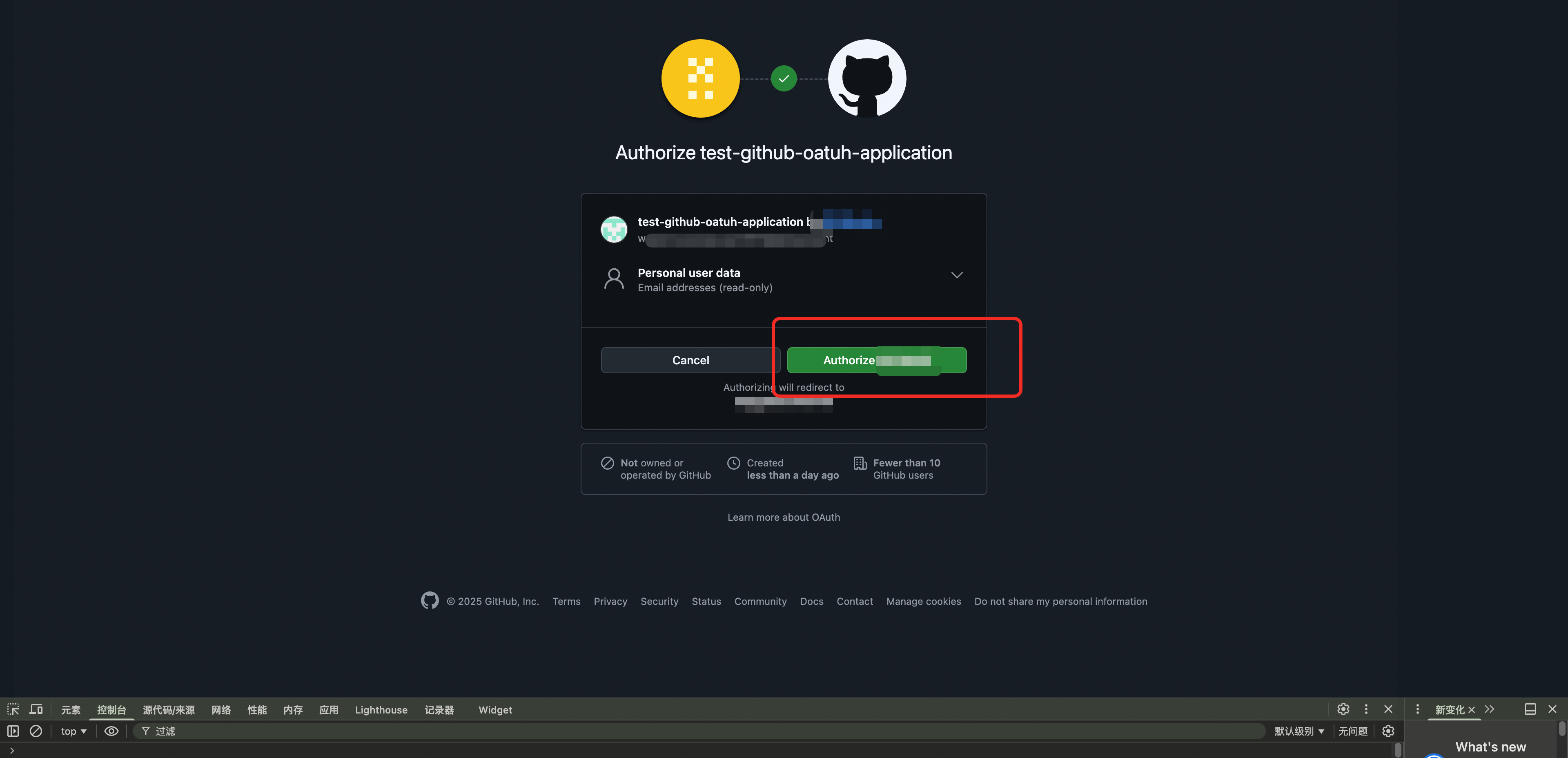
After successful authorization, the page automatically redirects back and displays the user information, such as user ID, username, and email, obtained from GitHub. This indicates that the authentication is successful.
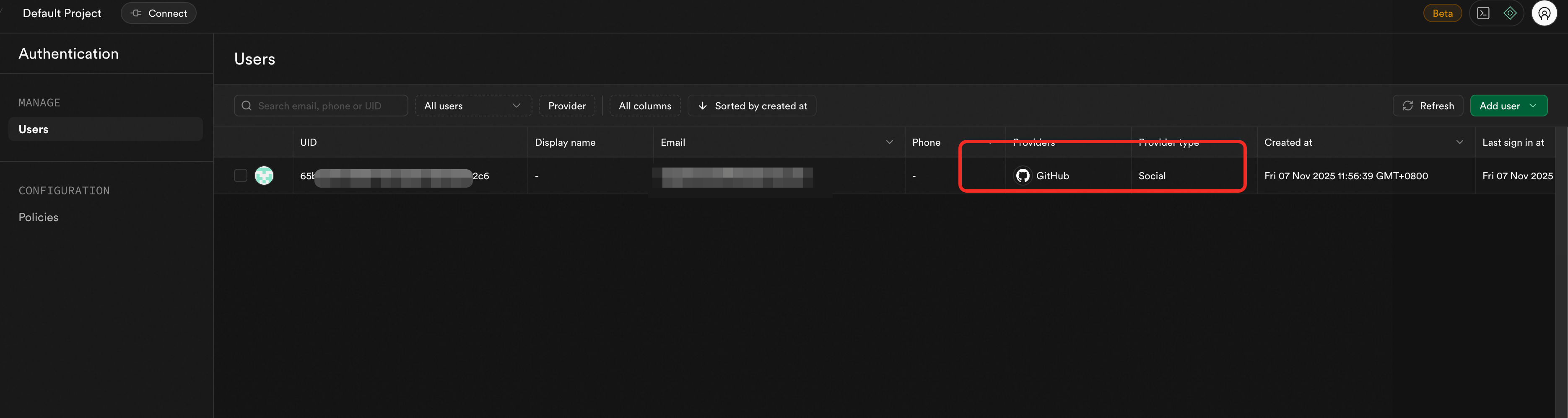
Verify the backend data
Go to the RDS console home page. In the navigation pane on the left, click AI Application Development.
Select a region at the top. In the RDS Supabase list, click the Project ID of the target instance to go to its details page.
Click Network Information > Public Endpoint to go to the Supabase logon page.
NoteIf you use an ECS instance in the same VPC as the RDS Supabase project to log on, use the Internal Endpoint.
In the navigation pane on the left, click Authentication > Users. View the new user information for the user who just logged on with GitHub to confirm that the user data has been synchronized to RDS Supabase.