The validate_password plugin for RDS for MySQL lets you enforce custom password complexity rules on database account passwords — including minimum length, character composition, and whether a password can match the username.
This feature is free of charge.
How it works
Password validation in RDS for MySQL operates at two independent layers:
RDS platform layer — Enforces a fixed baseline rule whenever you create or reset a password through the RDS console or API. This rule cannot be disabled or overridden by plugin settings.
Plugin layer — The
validate_passwordplugin enforces your custom rules. These apply at the MySQL level and are separate from the platform baseline.
Understanding this two-layer model helps you predict which rules apply and troubleshoot rejections.
Supported versions
MySQL 5.7
MySQL 8.0
Step 1: Install the validate_password plugin
Connect to the RDS for MySQL instance using a privileged account.
Run the following command to install the plugin.
INSTALL PLUGIN validate_password SONAME 'validate_password.so';Verify the installation.
SHOW GLOBAL VARIABLES LIKE 'validate_password%';If the plugin is installed correctly, the output lists the
validate_passwordvariables.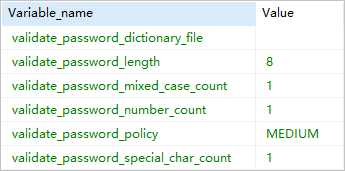
For instances with a primary/secondary architecture (High-availability Edition or Cluster Edition), install the plugin on the secondary node as well. The plugin is not automatically synchronized. To install on the secondary node, perform a manual primary/secondary failover to switch to the secondary node, then repeat steps 1–3. If you skip this step, the password policy becomes invalid after a failover.
NoteAfter the plugin is installed on both nodes, password policy parameters configured in the RDS console are automatically synced to the secondary node — no additional setup is needed.
Step 2: Configure password policy parameters
Go to the Instances page. In the top navigation bar, select the region where your instance resides. Click the instance ID.
In the left navigation pane, click Parameters.
Search for and modify the
loose_validate_passwordparameters. For instructions, see Set instance parameters.
The plugin must be installed before you modify these parameters. Changes have no effect if the plugin is not installed. For the full parameter reference, see the official MySQL documentation.
The following table describes the configurable parameters.
| Parameter | Supported versions | Description | Example |
|---|---|---|---|
loose_validate_password_check_user_name | 5.7 | Controls whether the password can match the username. ON (default): allowed. OFF: not allowed. | Set to OFF to prohibit passwords that match the username. |
loose_validate_password_policy | 8.0, 5.7 | The strength check level. 0: checks length only. 1 (default): checks length, digits, uppercase and lowercase letters, and special characters. 2: same as level 1 (dictionary file is not supported). | Set to 1 for standard enforcement. |
loose_validate_password_length | 8.0, 5.7 | The minimum password length. MySQL 5.7: 0–256, default 8. MySQL 8.0: 1–12, default 8. | Set to 10 to require at least 10 characters. |
loose_validate_password_number_count | 5.7 | The minimum number of digits. Range: 0–256, default 1. | Set to 2 to require at least 2 digits. |
loose_validate_password_mixed_case_count | 5.7 | The minimum number of uppercase and lowercase letters in the password. Range: 0–256, default 1. | Set to 2 to require at least one uppercase letter and one lowercase letter (a total of 2 mixed-case letters). |
loose_validate_password_special_char_count | 5.7 | The minimum number of special characters. Range: 0–256, default 1. | Set to 1 to require at least 1 special character. |
Parameter length formula
The loose_validate_password_length value must satisfy:
length >= number_count + (2 × mixed_case_count) + special_char_countIf the value you set does not meet this requirement, RDS automatically adjusts length to equal the formula result.
Example: If number_count = 2, mixed_case_count = 2, and special_char_count = 1, the minimum valid length is 2 + (2 × 2) + 1 = 7.
Constraints
RDS platform baseline rules
Regardless of the plugin settings, all passwords created or reset through the RDS console or the CreateAccount / ResetAccountPassword API operations must meet these requirements:
8 to 32 characters in length
At least three of the following character types: uppercase letters, lowercase letters, digits, and special characters (
!@#$%^&*()_+-=)
These rules apply even if you configure the plugin to allow shorter or simpler passwords.
Setting passwords shorter than 8 characters (not recommended)
Adjusting plugin parameters alone cannot bypass the 8-character minimum enforced by the RDS platform. Even if loose_validate_password_length is set to 5, the console and API still require at least 8 characters.
To set a password shorter than 8 characters, use the SET PASSWORD SQL command to bypass the platform check directly. Use this method only in test environments. Do not use it in production.
What's next
Create or reset account passwords through the console: Create an account or Reset the password of an account
Manage account permissions: Modify the permissions of an account, Grant an account access from specified IP addresses, and Grant an account access to specified tables, views, or fields