When multiple team members need access to Performance Testing Service (PTS), use Resource Access Management (RAM) to control who can manage or view performance tests. Attach a PTS system policy to a RAM user or RAM role to grant the appropriate level of access.
PTS system policies
PTS provides two system policies. Choose a policy based on the access level you want to grant.
| Policy | Access level |
|---|---|
AliyunPTSFullAccess | Full access (management permissions) |
AliyunPTSReadOnlyAccess | Read-only |
Prerequisites
Before you begin, make sure that you have:
An activated PTS instance. For more information, see Billing overview
An Alibaba Cloud account or a RAM user with administrative rights
Attach a PTS policy to a RAM user
Step 1: Create a RAM user
If you already have a RAM user, skip to Step 2.
Create a RAM user in the RAM console. For detailed instructions, see Create a RAM user.
Step 2: Attach the policy
Log on to the RAM console.
In the left-side navigation pane, choose Identities > Users.
On the Users page, find the target RAM user and click Add Permissions in the Actions column.
In the Grant Permission panel, search for and select the policy to attach:
For full access, select
AliyunPTSFullAccess.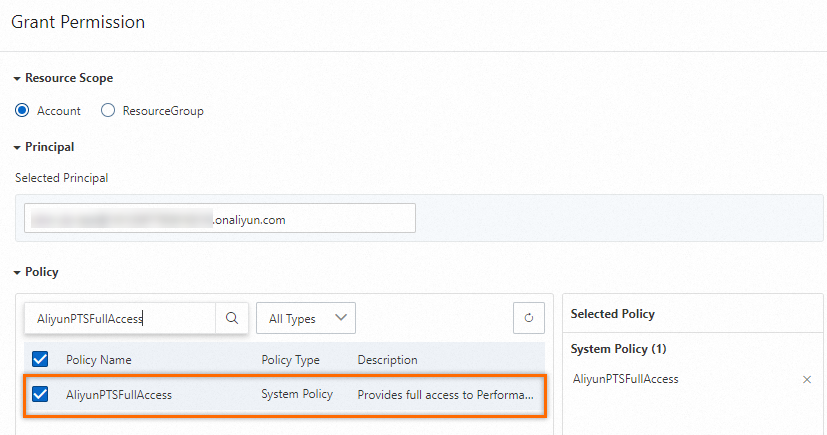
For read-only access, select
AliyunPTSReadOnlyAccess.
Click Grant permissions and then close the window.
Attach a PTS policy to a RAM role
RAM roles let you grant PTS access without using a permanent RAM user identity.
Step 1: Create a RAM role
If you already have a RAM role, skip to Step 2.
Create a RAM role for a trusted Alibaba Cloud account. For detailed instructions, see Create a RAM role for a trusted Alibaba Cloud account.
Step 2: Attach the policy
Log on to the RAM console.
In the left-side navigation pane, choose Identities > Roles.
On the Roles page, find the target RAM role and click Grant Permission in the Actions column.
In the Grant Permission panel, search for and select the policy to attach:
For full access, select
AliyunPTSFullAccess.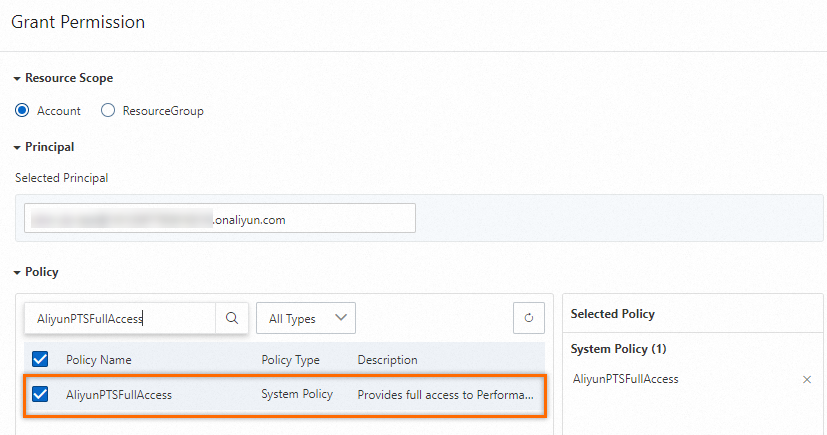
For read-only access, select
AliyunPTSReadOnlyAccess.
Click Grant permissions and then close the window.
Verify permissions
After attaching a policy, verify that the RAM identity has the expected access:
Log on to the PTS console as the RAM user, or assume the RAM role.
Confirm that the RAM identity can perform the expected operations. For example, a user with
AliyunPTSReadOnlyAccesscan view tests but cannot create or modify them.