OSS encrypts communication between clients and buckets using transport layer security (TLS). By default, buckets accept TLS 1.0, 1.1, and 1.2. Enable TLS version management to restrict which versions and cipher suites clients can use — a common requirement for Payment Card Industry Data Security Standard (PCI DSS) and other security compliance frameworks.
Before changing TLS settings on a bucket with active traffic, check which TLS versions your clients currently use. Removing a version that clients rely on breaks their connections immediately. See Check the current TLS version.
Prerequisites
Before you begin, ensure that you have:
The
oss:PutTLSVersionandoss:GetTLSVersionpermissions granted to your RAM user. For details, see Attach a custom policy to a RAM user.
TLS versions
| Version | Key algorithms | Security status | Supported browsers |
|---|---|---|---|
| TLS 1.0 | RSA, DES, 3DES | Vulnerable to BEAST and POODLE attacks; does not meet PCI DSS requirements | IE6+, Chrome 1+, Firefox 2+ |
| TLS 1.1 | AES, RSA, SHA-256 | Addresses known TLS 1.0 vulnerabilities | IE11+, Chrome 22+, Firefox 24+, Safari 7+ |
| TLS 1.2 | AES-GCM, AES-CBC, ECDHE; adds Server Name Indication (SNI) | Current mainstream standard; suitable for most secure communication scenarios | IE11+, Chrome 30+, Firefox 27+, Safari 7+ |
| TLS 1.3 | Stronger key exchange; removes insecure algorithms; better forward secrecy | Highest security and performance; required for financial, government, and high-privacy scenarios | Chrome 70+, Firefox 63+ |
Usage notes
Include at least TLS 1.2 in the allowed versions. Setting only TLS 1.0 or TLS 1.1 introduces security and compliance risks.
Downgrading the TLS version or disabling TLS version management may break client connections and create compliance gaps. Before making changes, check which TLS versions your clients are currently using. See Check the current TLS version.
Before disabling a TLS version, verify that no clients rely exclusively on that version.
Changes take effect within 30 minutes.
Cipher suite options
A cipher suite defines the combination of algorithms used for key exchange, authentication, symmetric encryption, and message integrity. OSS offers three options:
| Option | Security | Compatibility | Use when |
|---|---|---|---|
| All Cipher Suites (default) | Low | High | Maximum client compatibility is required |
| Strong Cipher Suite | High | Reduced | PCI DSS or similar compliance frameworks require stronger encryption |
| Custom Cipher Suite | Configurable | Configurable | Specific algorithms must be allowed or excluded (TLS 1.2 and TLS 1.3 only) |
Custom cipher suite configuration is only available when TLS 1.2 or TLS 1.3 is enabled.
Configure TLS version management
Use the OSS API
For custom integrations, call the OSS RESTful APIs directly. Signature calculation must be included in your request. For details, see PutBucketHttpsConfig and GetBucketHttpsConfig.
Verify TLS configuration
Check the current TLS version
Run the following command to check which TLS version a client negotiates with the bucket when no version is explicitly specified:
openssl s_client -connect <Bucket>.<Endpoint>:443 -servername <Bucket>.<Endpoint>| Parameter | Description |
|---|---|
<Bucket> | The bucket name |
<Endpoint> | The public endpoint, internal endpoint, or custom domain name of the bucket |
The negotiated TLS version is shown in the command output.
Verify that the TLS version is configured correctly
The following examples assume the allowed TLS version is set to TLS 1.2 only.
Verify that TLS 1.2 access succeeds:
openssl s_client -connect <Bucket>.<Endpoint>:443 -servername <Bucket>.<Endpoint> -tls1_2| Parameter | Description |
|---|---|
<Bucket> | The OSS bucket name |
<Endpoint> | The public endpoint, internal endpoint, or custom domain name of the bucket |
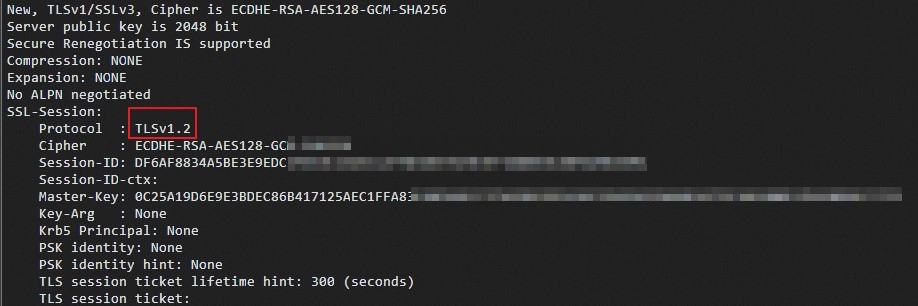
Expected output (successful connection):
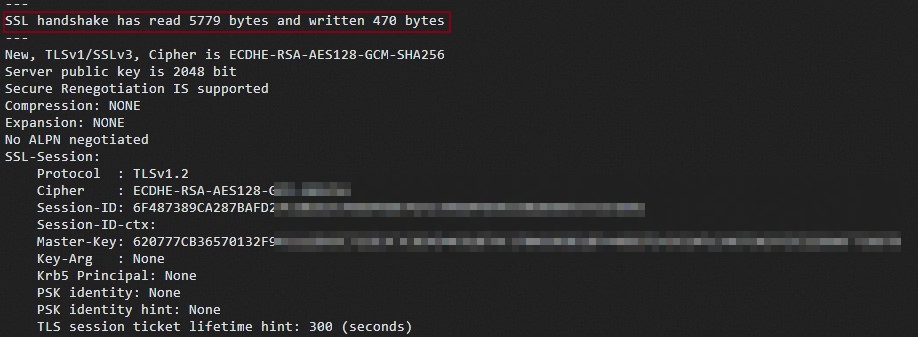
The same result applies when the client does not specify a TLS version but natively supports TLS 1.2.
Verify that non-allowed versions are blocked:
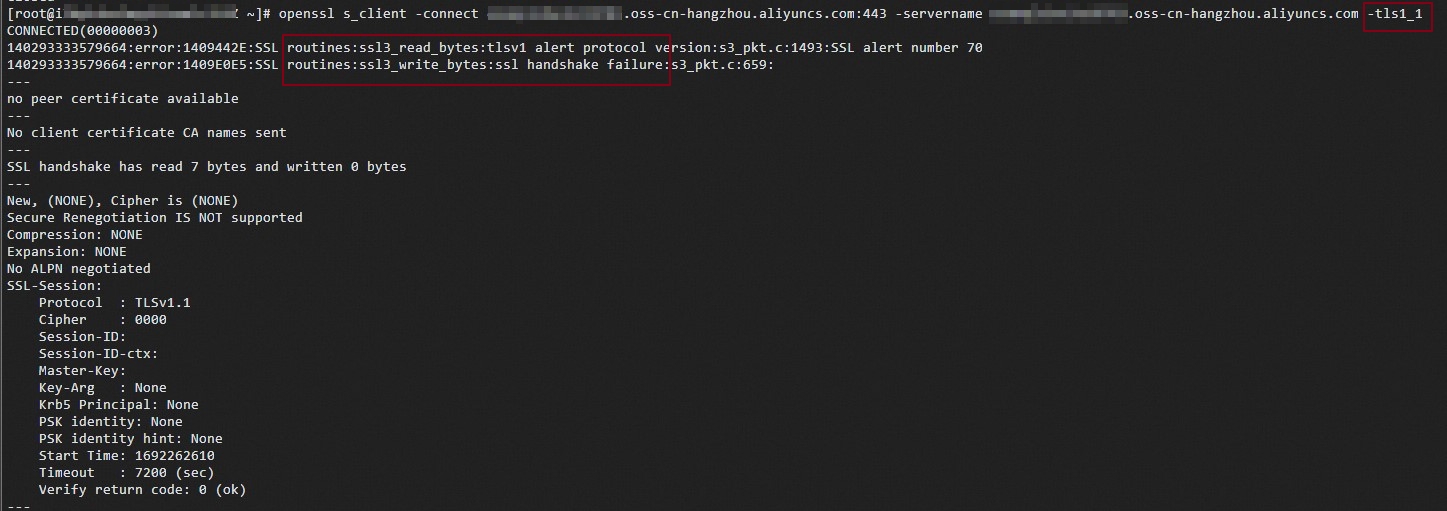
openssl s_client -connect <Bucket>.<Endpoint>:443 -servername <Bucket>.<Endpoint> -tls1_1Expected output (connection rejected — TLS 1.1 is not in the allowed list):