The OSS malicious file detection feature scans objects in your buckets for security threats such as webshells, ransomware, and trojans. When a threat is detected, you can review the event description and follow the recommendations to promptly handle the risk file.
Supported threat types
Supported virus types
Virus type ( | Virus name |
Backdoor | reverse shell backdoor |
DDoS | DDoS Trojan |
Downloader | Downloader Trojan |
Engtest | engine test program |
Hacktool | hacking tool |
Trojan | high-risk program |
Malbaseware | compromised base software |
MalScript | malicious script |
Malware | malicious program |
Miner | mining program |
Proxytool | proxy tool |
RansomWare | ransomware |
RiskWare | riskware |
Rootkit | Rootkit |
Stealer | information-stealing tool |
Scanner | scanner |
Suspicious | suspicious program |
Virus | infectious virus |
WebShell | web shell |
Worm | worm |
AdWare | adware |
Patcher | cracking program |
Gametool | private server tool |
Prerequisites
A RAM user must have the oss:ActivateProduct permission. For more information, see Common examples of RAM policies.
Billing
Malicious file detection is billed based on the number of files scanned. The rate is USD 1.42 per 10,000 files.
In addition to detection fees, OSS charges standard request fees for API calls made during scanning: ListBuckets (GetService), GetBucketStat, ListObjectsV2 (GetBucketV2), GetObjectMeta, and GetObject. For more information, see Request fees.
Only the pay-as-you-go billing method is supported. This feature is billed on an hourly basis. Bills are typically generated after the current billing cycle ends. The system determines the exact billing time.
Limits
Supported regions
Malicious file detection is available in the following regions: China (Qingdao), China (Beijing), China (Zhangjiakou), China (Hohhot), China (Ulanqab), China (Hangzhou), China (Shanghai), China (Shenzhen), China (Heyuan), China (Guangzhou), China (Chengdu), China (Hong Kong), Singapore, Indonesia (Jakarta), Thailand (Bangkok), Philippines (Manila), Malaysia (Kuala Lumpur), South Korea (Seoul), Japan (Tokyo), US (Silicon Valley), UK (London), US (Virginia), and Germany (Frankfurt).
Detection task completion time
By default, there is no limit on the number of files that can be scanned in a bucket. Detection tasks are processed asynchronously in a queue. When the queue is not busy, a scan of hundreds of thousands of files can be completed within an hour, and a scan of millions of files can be completed within 24 hours.
Bucket storage classes
Only buckets of the Standard and Infrequent Access (IA) storage classes support malicious file detection rules. Buckets of the Archive, Cold Archive, and Deep Cold Archive storage classes are not supported.
Object storage classes
Only objects of the Standard and Infrequent Access (IA) storage classes can be scanned. The feature does not scan objects of the Archive, Cold Archive, and Deep Cold Archive storage classes.
Single file size limit
The maximum size for a scannable file is 500 MB.
Archive limits
Supported archive formats include
.7z,.zip,.tar,.gz,.rar,.ar,.bz2,.xz, and.lzma.An archive can be decompressed up to 5 levels deep. The total number of files extracted from an archive cannot exceed 1,000, and their total size cannot exceed 1 GB. The scan skips files that exceed these limits.
Use the OSS console
When you first use malicious file detection for a bucket, you must authorize the AliyunServiceRoleForOssMfd service role.
Log on to the OSS console.
In the left-side navigation pane, click Buckets. On the Buckets page, find and click the desired bucket.
In the left-side navigation pane, choose .
On the Malicious file detection page, click Activate Now. Follow the on-screen instructions to claim your free trial quota. Usage beyond the free trial quota is billed on a pay-as-you-go basis.
On the Malicious file detection page, click Confirm Authorization.
After you grant the authorization, the system automatically creates the AliyunServiceRolePolicyForOssMfd access policy for this role. This policy grants permissions to read bucket and object lists, access KMS, and decrypt objects.
Configure a malicious file detection rule.
Run immediately
Full detection
Full detection provides a comprehensive security scan of all data in a bucket to identify risks and ensure that file content meets compliance requirements.
In the upper-right corner of the Malicious Object Detection page, click Detect.
In the Detect dialog box, select a File detection type and a Scan path.
File detection type
You can choose to scan all file types in the bucket or specify particular file types.
Scan path
To scan all files in the bucket, select Configure for the entire bucket. To scan only files that match a specific prefix, select Match by prefix and specify the prefix.
Click OK.
Incremental detection
After a full detection scan on a bucket or path is complete, you can use incremental detection to scan only new or modified files. This helps save computing resources and time.
In the upper-right corner of the Malicious Object Detection page, click Incremental Detection.
In the Detect dialog box, select a File detection type and a Scan path.
File detection type
You can choose to scan all file types in the bucket or specify particular file types.
Scan path
To scan all files in the bucket, select Configure for the entire bucket. To scan only files that match a specific prefix, select Match by prefix and specify the prefix.
Click OK.
Custom schedule
In the Basic Information section of the bucket, click the
 icon next to Policy configuration status.
icon next to Policy configuration status.In the Create Policy dialog box, configure the following parameters.
Parameter
Description
Policy name
Enter a custom name for the policy.
Policy status
Enable the policy.
Scan path
Match by prefix
Select this option to scan only files in the bucket that match a specific prefix. Then, specify the prefix, such as dir.
Configure for the entire bucket
Select this option to scan all files in the bucket.
Detection cycle
Specify a custom detection cycle. You can select multiple days. For example, you can schedule the scan to run every Monday and Tuesday.
File detection time
Specify the start and end time for the scan, accurate to the second.
File detection type
Select whether to scan all file types or only specific file types. If you select specific file types, you must select the file extensions from the drop-down list, such as .7z.
Click OK.
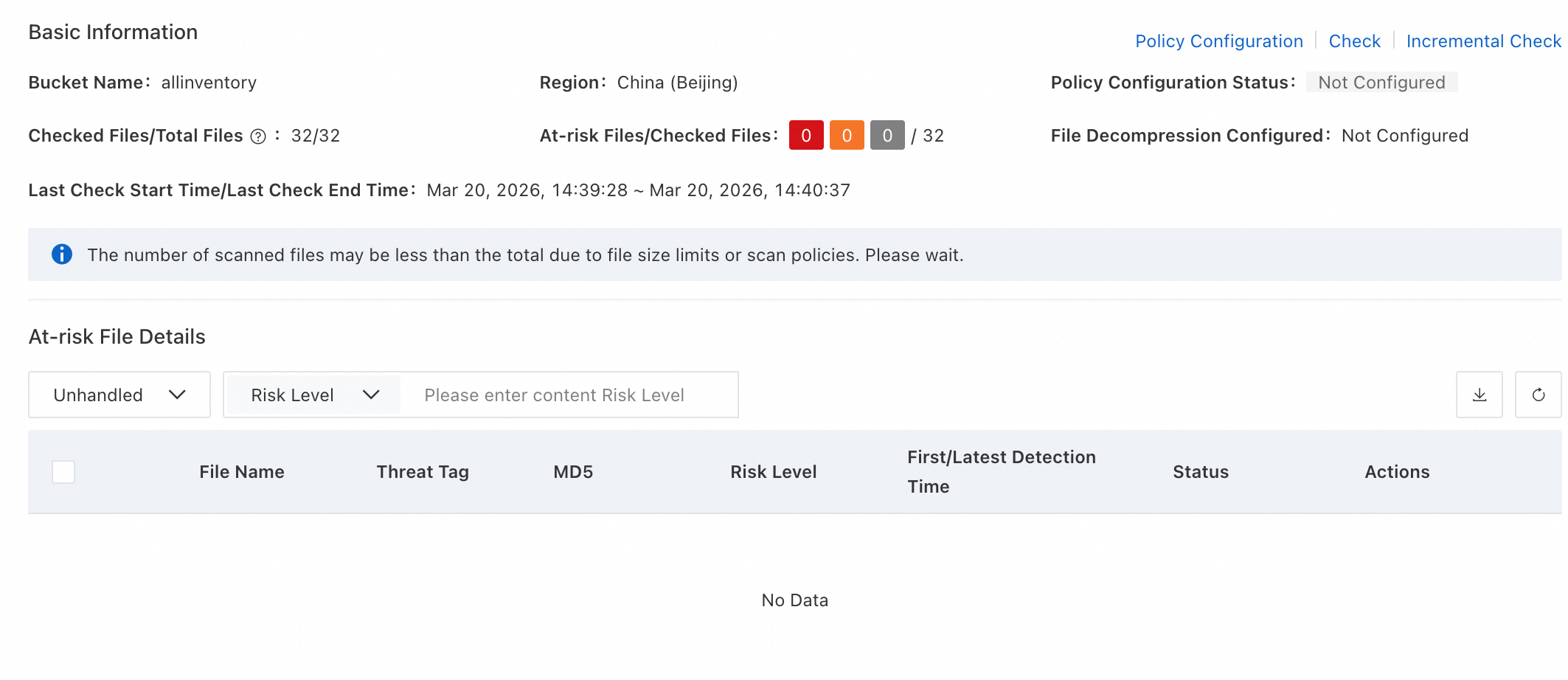
View detection results.
If no risk files are detected, the risk file details area does not display any results.
If risk files are detected, the risk file details area lists each flagged file with its name, threat label, file MD5, risk level, first discovery time, and latest scan time.
Handle risk files.
In the Actions column for a risk file, click Details to view the event description. Follow the recommendations in the event description to address the risk promptly.