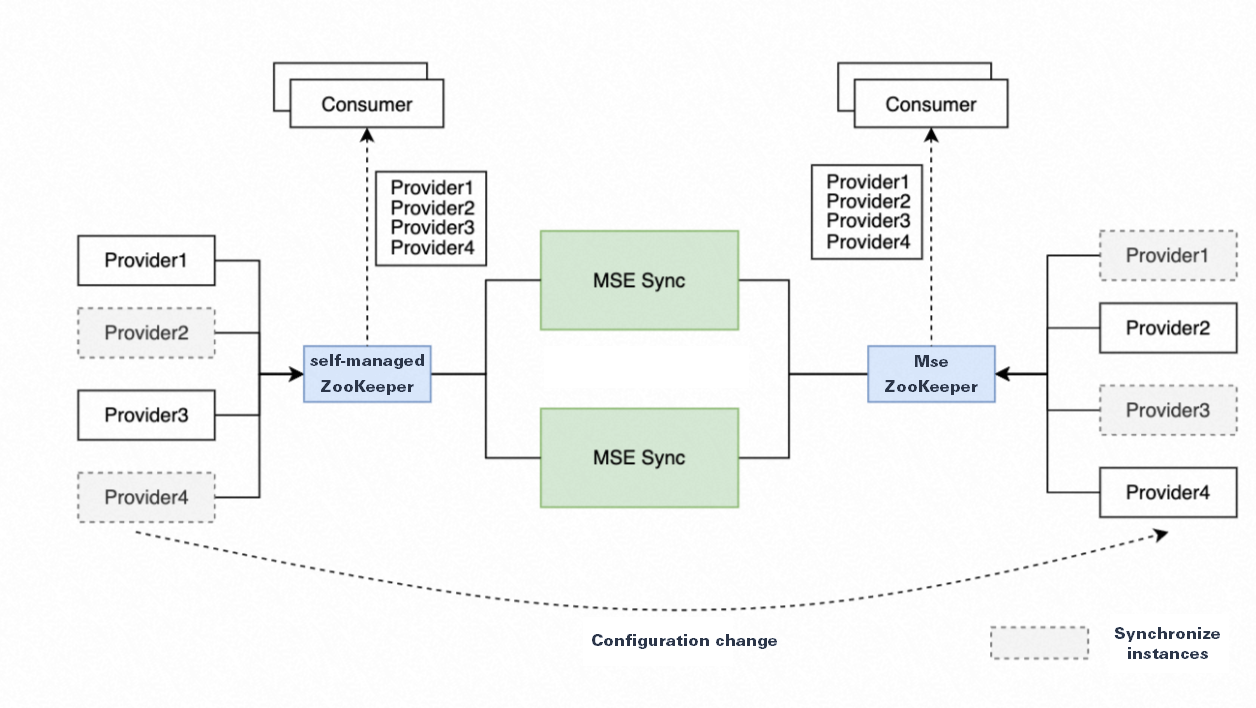
MSE Sync synchronizes service and configuration data between registries such as Nacos, ZooKeeper, Eureka, and Consul. Built on the open-source NacosSync project, MSE Sync supports bidirectional synchronization, automatic service discovery, and one-click full-service sync, enabling smooth migrations from self-managed registries to Microservices Engine (MSE) instances.
How it works
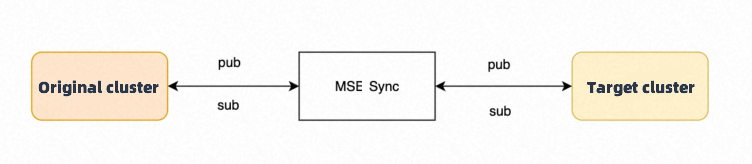
MSE Sync acts as a bridge between a source registry and a target MSE instance. During migration, it continuously synchronizes service registration data so that both registries serve identical information. Applications connected to either registry can discover services registered on the other, allowing you to migrate applications incrementally.
In the following diagram, pub represents a service publisher and sub represents a service subscriber.
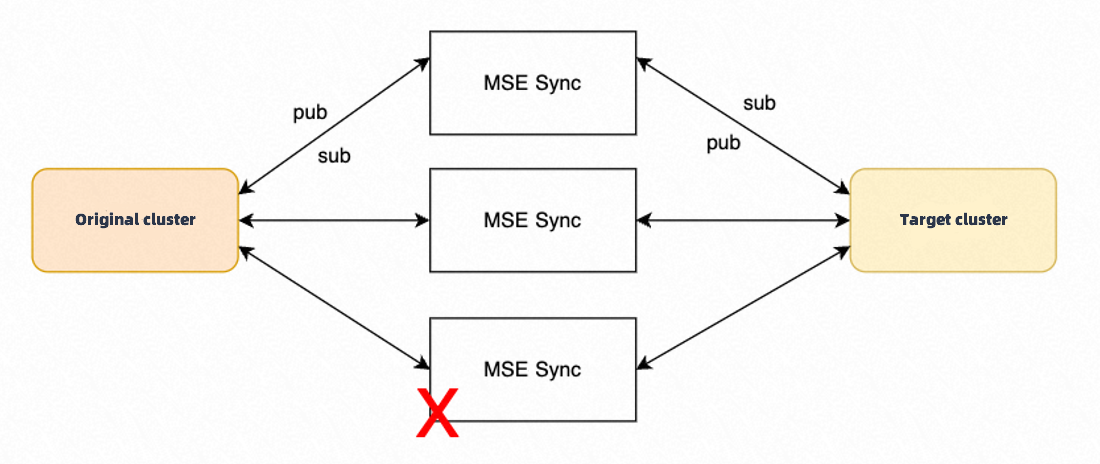
MSE Sync uses a multi-instance deployment architecture for high availability. If a node fails, healthy nodes run a scheduled recovery task to take over the failed node's synchronization work.
Key concepts
| Concept | Description |
|---|---|
| Cluster | A source or target registry instance defined in the MSE Sync configuration. Each cluster has a unique name, a type (Nacos, ZooKeeper, Eureka, or Consul), and one or more connection endpoints. |
| Task | A synchronization job that moves data from a source cluster to a destination cluster. Each task specifies the sync type, direction, and an optional service name filter. |
| Sync type | Determines what data is synchronized. Service syncs service registration data. Config syncs configuration data (Nacos and ZooKeeper only). All creates both service and configuration sync tasks based on the source cluster type. |
| Sync mode | Unidirectional copies natively registered service data from the source to the target. Bidirectional syncs natively registered service data in both directions. |
Supported migration paths
MSE Sync is compatible with the service registration logic of ZooKeeper, Nacos, Eureka, and Consul.
| Source registry | Target registry | What gets synchronized |
|---|---|---|
| Nacos | Nacos | Native Nacos service data |
| ZooKeeper | ZooKeeper | Services and persistent configurations |
| Eureka | Nacos | Native Eureka service data |
| Consul | Nacos | Native Consul service data (healthy instances only) |
ZooKeeper
Do not modify the same Znode in both the source and target clusters simultaneously. Concurrent writes can cause data loss during migration. Do not use configuration synchronization to sync services or ephemeral nodes.
When synchronizing persistent nodes, MSE Sync registers a watch on the source cluster for each Znode. If the source cluster contains many nodes, this creates a large number of watches and consumes significant memory. Make sure the source cluster's Znode count and resources can handle the additional watch listeners from MSE Sync.
Eureka to Nacos
Eureka registers service names in uppercase by default (for example, SERVICE-1). MSE Sync converts these names to lowercase when synchronizing to Nacos (for example, service-1).
This conversion can cause interoperability issues with mixed-case names. For example, if a service named Service-1 is registered directly in Nacos alongside the synchronized service-1, Nacos treats them as two separate services. Instances registered under one name cannot discover instances under the other.
To avoid this issue, standardize all service names to lowercase before starting the migration.
Consul to Nacos
MSE Sync synchronizes only healthy instance information from Consul. Metadata changes are not detected or synchronized automatically. Consul configuration data is not supported.
Step 1: Deploy MSE Sync
Before deploying, make sure that:
The MSE Sync deployment environment has network connectivity to both the source and target registries (for example, deploy MSE Sync in the same Virtual Private Cloud (VPC) or make sure it has public internet access to both clusters)
(If using MySQL) A MySQL service is available with a database and a user account that has read and write permissions
MSE Sync must connect to both the source and target registries. If it cannot reach both, the migration fails.
Choose a storage backend
MSE Sync supports two storage backends:
| Backend | Use when | Multi-instance support |
|---|---|---|
| MySQL (required for multi-instance deployment) | Running multiple MSE Sync instances for high availability | Yes -- multiple instances share one MySQL database |
| Embedded Derby | Testing or single-node deployments | No -- single machine only |
MSE Sync automatically selects the backend based on environment variables. If MYSQL_URL, MYSQL_USER_NAME, and MYSQL_PASSWORD are all set, MSE Sync connects to MySQL. Otherwise, it uses the embedded Derby database.
| Variable | Description | Example |
|---|---|---|
MYSQL_URL | MySQL connection string | jdbc:mysql://localhost:3306/sync |
MYSQL_USER_NAME | Username with read and write permissions | -- |
MYSQL_PASSWORD | Password for the account | -- |
Configure JVM parameters
Add JVM parameters in the conf/java.env file using the JAVA_OPT variable:
JAVA_OPT="$JAVA_OPT -Xms2048m -Xmx2048m"Deploy on Kubernetes
Save the following configuration as
mse-sync-deployment.yaml. Replace the MySQL connection details and adjustreplicasas needed.NoteTo access the MSE Sync web UI, create a Kubernetes Service that routes traffic to port 8000.
apiVersion: apps/v1 kind: Deployment metadata: labels: app.kubernetes.io/name: mse-sync name: mse-sync-svc spec: replicas: 3 selector: matchLabels: app.kubernetes.io/name: mse-sync template: metadata: labels: app.kubernetes.io/name: mse-sync spec: containers: - name: mse-sync image: msecrinstance-registry.cn-hangzhou.cr.aliyuncs.com/mse-demo/mse-sync:latest ports: - containerPort: 8000 env: - name: MYSQL_URL value: "jdbc:mysql://192.xx.xx.xx:3306/sync" - name: MYSQL_USER_NAME value: "mse-sync" - name: MYSQL_PASSWORD value: passwordDeploy MSE Sync:
kubectl apply -f mse-sync-deployment.yaml
Deploy on Elastic Compute Service (ECS)
Download the MSE Sync binary:
curl https://msesync.oss-cn-hangzhou.aliyuncs.com/MseSync.zip --output msesync.zipExtract the package:
unzip ./msesync.zip(Optional) If using MySQL, set the database environment variables:
export MYSQL_URL="" export MYSQL_USER_NAME="" export MYSQL_PASSWORD=""Start MSE Sync:
./MseSync/bin/startup.sh start
Step 2: Configure clusters and sync tasks
MSE Sync supports three configuration methods:
| Method | Best for | Details |
|---|---|---|
| Configuration file (recommended) | Automated or large-scale migrations | Define clusters and tasks in YAML; import via CLI or auto-load on startup |
| Web UI | Ad-hoc or small-scale migrations | Import configuration through the browser-based interface |
| MSE console | Generating initial configuration files | The Cloud Migration page auto-generates YAML configuration files |
Option A: Configure with a YAML file
A configuration file contains two sections: clusters (registry connection details) and tasks (synchronization jobs).
The following example synchronizes all services from the public and test namespaces in the source cluster to the destination cluster, using bidirectional sync:
clusters:
- clusterName: src
connectKeyList:
- mse-xxxxx-nacos-ans.mse.aliyuncs.com:8848
clusterType: NACOS
namespace: public,test
- clusterName: dst
connectKeyList:
- mse-xxxxxx-nacos-ans.mse.aliyuncs.com:8848
clusterType: NACOS
tasks:
- source: src
destination: dst
type: Service
mode: Bidirectional
serviceMatchPattern: ".*"
autoScanAndAddService: trueImport the configuration using the CLI:
./bin/msesyncCMD.sh apply -f {path_to_configuration_file}Alternatively, place the file at MseSync/conf/config.yaml. MSE Sync loads it automatically on startup.
When importing a configuration file, newly added services are automatically discovered and synchronized.
Option B: Configure through the web UI
Open the MSE Sync web interface.
In the left navigation pane, click Service Sync.
Click Import Configuration.
In the Import Configuration dialog box, paste the YAML configuration and click OK.
Configuration reference
Cluster fields
| Field | Description | Example |
|---|---|---|
clusterName | Unique name for the cluster. Once set, do not change this value. | sourceCluster |
clusterType | Registry type: NACOS, ZOOKEEPER, EUREKA, or CONSUL | NACOS |
namespace | Nacos namespace name. Separate multiple namespaces with commas. If left blank on a source cluster, data from all namespaces is synchronized. | public,test |
connectKeyList | List of connection endpoints for the cluster. | See example below |
userName | Nacos username (if authentication is enabled). | -- |
password | Nacos password (if authentication is enabled). | -- |
ak | AccessKey ID for authenticating with a cloud MSE Nacos instance. | LTAI5***dXai6 |
sk | AccessKey secret for authenticating with a cloud MSE Nacos instance. | Jdvdj***6vs7wBEKO |
connectKeyList example:
connectKeyList:
- localhost:8848
- localhost1:8848Task fields
| Field | Description | Default |
|---|---|---|
source | Name of the source cluster (must match a clusterName in the clusters section). | -- |
destination | Name of the target cluster. The target namespace is automatically kept consistent with the source. If the namespace does not exist in the target, MSE Sync creates it. | -- |
type | Sync type: Service (service data), Config (configuration data, Nacos and ZooKeeper only), or All (both). | -- |
mode | Sync direction: Unidirectional (source to target only) or Bidirectional (both directions). | -- |
serviceMatchPattern | Regular expression to filter which services to synchronize. | .* (all services) |
autoScanAndAddService | Automatically discover and synchronize new services added to the source cluster. | true |
Multi-instance deployment
For production environments, deploy multiple MSE Sync instances backed by a shared MySQL database. If one node fails, the remaining healthy nodes detect the failure through a scheduled task and take over the failed node's sync work.
Recovery scan interval
The recovery scan interval controls how frequently healthy nodes check for failed nodes. Configure it with the following Java Virtual Machine (JVM) parameter, set through the JAVA_OPT environment variable:
-Dmsesync.daemon.refresh.interval=60 // Unit: secondsExample:
JAVA_OPT="$JAVA_OPT -Dmsesync.daemon.refresh.interval=10"The default interval is 60 seconds. Do not set it too low -- a short interval increases load on both the server and MSE Sync nodes. The minimum recommended value is 10 seconds. Adjust based on cluster load and sync volume.
Do not use multi-instance deployment for configuration synchronization tasks.
During the interval between a node failure and the next scheduled recovery scan, the client's instance list may be temporarily empty.
Usage notes
Bidirectional sync and offline status: During bidirectional synchronization, if a service provider is taken offline from the target instance's console, the offline status is not propagated back to the source instance.
Cluster name immutability: Once a
clusterNameis set in the configuration, do not change it. Changing it can prevent sync tasks from resuming after a restart.
FAQ
A sync task was added through the UI or YAML file, but it does not appear in the task list.
Check that services exist in the source cluster's namespace. MSE Sync only creates sync tasks for services it can discover. Verify:
The cluster connection details are correct (endpoints, authentication credentials).
The namespace ID matches an existing namespace in the source cluster.
At least one service instance (service provider) is registered in the specified namespace.
During bidirectional sync, taking a service provider offline from the target console does not sync back to the source.
This is expected behavior. The offline status set through the target instance's console is not synchronized to the source instance.
Description of additional YAML configuration fields
Clusters field:
Field
Description
Example value
namespace
The Nacos namespace name.
Note: You can enter multiple namespaces, separated by commas. If this field is left empty and the instance is the synchronization source, data from all namespaces in the instance is synchronized.
public
test
test1
ak
The AccessKey for authenticating the cloud MSE Nacos instance.
LTAI5***********dXai6
sk
The AccessKey secret for authenticating the cloud MSE Nacos instance.
Jdvdj*************6vs7wBEKO