Microservices Engine (MSE) is an O&M-free and highly available engine service for building and operating microservices. MSE provides three core modules -- Microservices Registry, Microservices Governance, and Cloud-native Gateway -- along with Alibaba Cloud SchedulerX for task scheduling. MSE can be used in the big data and microservices fields to help you accelerate business integration and reduce modification costs.
Service registration and discovery
As the number of microservice applications grows, tracking healthy service instances across environments becomes difficult. Hardcoded IP addresses and manual load balancer configurations create bottlenecks and single points of failure.
Microservices Registry provides an O&M-free, highly available, and stable service registry, configuration management, and distributed data management layer for applications built on Spring Cloud or Dubbo. Services register on startup and discover each other automatically, removing the need for static configuration.
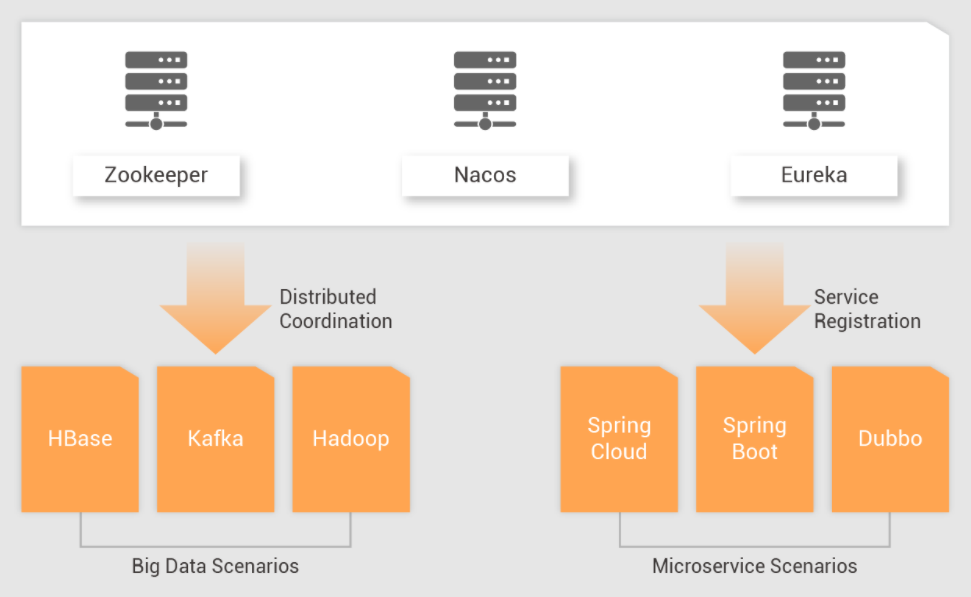
Microservices Registry supports three engine types:
Nacos -- Service discovery and dynamic configuration management
ZooKeeper -- Distributed coordination for applications and big data components
Eureka -- Service registry for microservice applications
Distributed coordination for big data and non-microservices workloads
ZooKeeper instances in MSE provide distributed coordination solutions -- distributed locks and distributed queues -- for building highly available distributed systems.
If you run big data components such as Hadoop, HBase, Kafka, or Flink, MSE ZooKeeper serves as the high availability (HA) backend by default.
Safe application releases
Releasing updates to a microservice carries risk. A faulty deployment can cascade across dependent services, causing outages that are hard to diagnose and slow to recover from.
Microservices Governance addresses these risks without requiring changes to your code or configuration:
Graceful start and shutdown -- Ensure smooth service transitions during deployment. See Implement graceful start and shutdown of microservice applications by using MSE.
End-to-end canary release -- Validate the new version with a subset of traffic before rolling out to all users.
Configuration management -- Push configuration changes dynamically without redeploying.
Traffic protection and fault tolerance
When traffic surges or a downstream service fails, unprotected services become overloaded, cascading failures across the entire system.
Microservices Governance provides built-in resilience capabilities:
| Capability | Description |
|---|---|
| Throttling | Limits the request rate to prevent overload |
| Circuit breaking | Stops calling a failing service to let it recover |
| Fault isolation | Contains failures within a single service to prevent cascading |
| Degradation | Falls back to a simplified response when a service is unavailable |
| Load balancing | Distributes traffic evenly across healthy instances |
These capabilities activate automatically based on the policies you define -- without requiring you to modify code and configurations.
Development environment isolation
In a shared development environment, multiple teams deploying to the same cluster often interfere with each other. Traffic meant for one team's version of a service may route to another team's version, causing confusing test failures.
Microservices Governance supports logical isolation of multiple development environments. Each team gets an isolated routing context without requiring separate physical clusters, resolving environment preemption and conflict issues while keeping infrastructure costs flat and enabling parallel development.
Unified gateway for traffic management and security
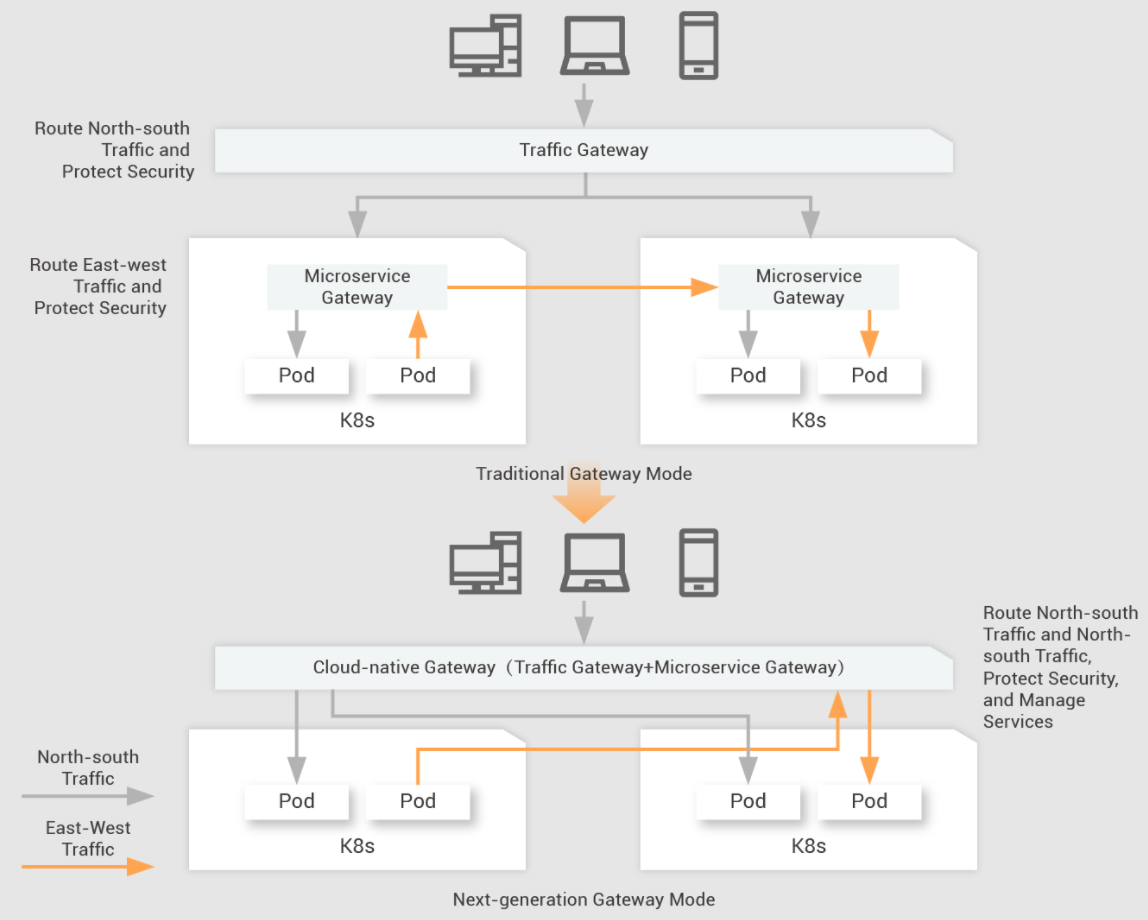
Traditional architectures require two separate gateways:
A traffic gateway (such as NGINX) for north-south traffic -- providing global policies irrelevant to backend business applications, such as HTTPS certificate offloading, Web Application Firewall (WAF) rules, and global traffic monitoring
A microservices gateway (such as Spring Cloud Gateway) for east-west traffic -- providing policies tightly coupled with your business, such as microservices governance and identity authentication
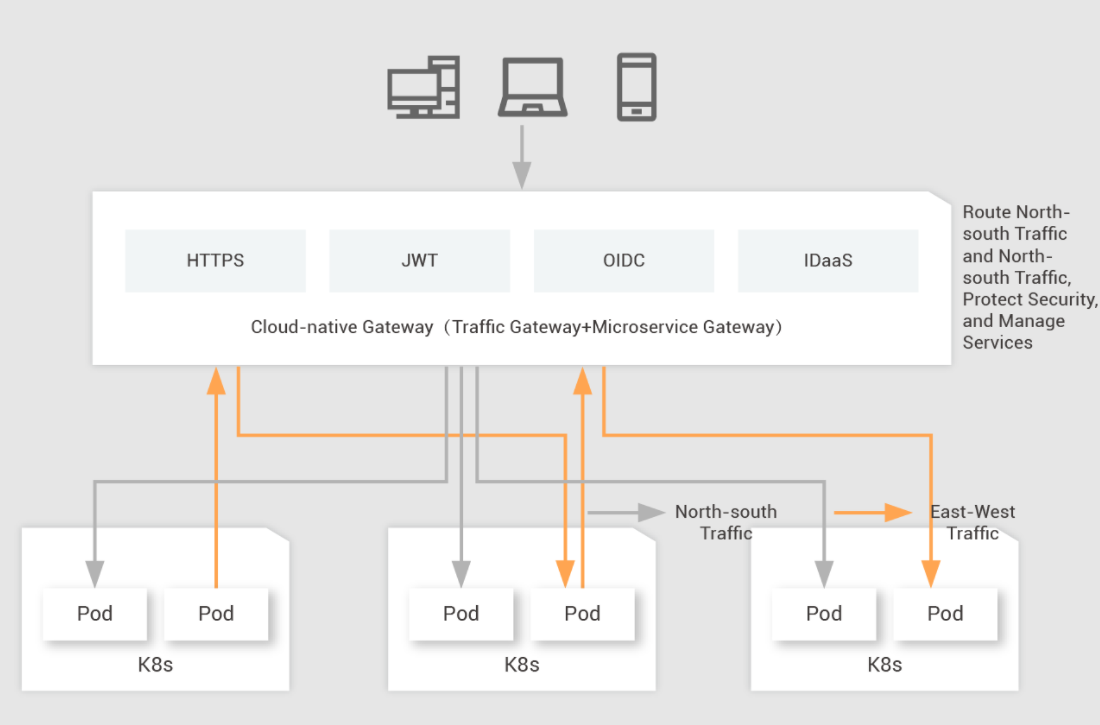
Cloud-native Gateway merges both roles into a single layer. This cuts gateway resource consumption by half and simplifies operations by giving you one place to manage routing, security, and governance.
Authentication
Cloud-native Gateway provides built-in authentication to secure API access:
JSON Web Token (JWT) authentication -- Validate JWTs at the gateway level
OpenID Connect (OIDC) authentication -- Integrate with OAuth 2.0-based identity providers
Identity as a Service (IDaaS) authentication -- Enable third-party sign-up through Alibaba Cloud IDaaS, supporting providers such as Alipay, Taobao, and Tmall
Extend authentication capabilities further through plug-ins, helping you reduce secure access costs.
Task scheduling
Alibaba Cloud SchedulerX provides reliable, distributed task scheduling for both time-based triggers and workflow orchestration.
Supported job types
SchedulerX supports jobs in multiple languages and frameworks:
| Job type | Use case |
|---|---|
| Java job | General-purpose scheduled tasks in Java applications |
| Spring job | Spring-native scheduling with dependency injection |
| Go job | Scheduled tasks in Go applications |
| Script job | Shell, Python, or other script-based jobs |
| HTTP job | Trigger an HTTP endpoint on a schedule |
| Kubernetes job | Run scheduled workloads in Kubernetes clusters |
| DataWorks job | Integrate with DataWorks data processing pipelines |
For more information, see Job types.
Workflow orchestration
SchedulerX provides a visual editor for building job workflows. Configure jobs on GUIs and transfer data between steps.
For details, see Use workflows to orchestrate jobs.
Recommended service integrations
| MSE module | Commonly used with |
|---|---|
| Microservices Governance | Elastic Compute Service (ECS), ApsaraDB RDS, Object Storage Service (OSS), Container Service for Kubernetes (ACK) |
| Cloud-native Gateway | ApsaraDB RDS, OSS, ACK |