MaxCompute lets you restrict project access by IP address. When you enable the IP address whitelist feature, only IP addresses on the whitelist can access the project — even requests with a valid AccessKey pair are denied if the source IP is not listed.
Only the project owner, the Super_Administrator role, and custom administrator roles with the required permissions can manage IP address whitelists.
How it works
MaxCompute supports two independent whitelists, one per network type:
| Network type | Parameter |
|---|---|
| Internet and cloud product interconnection network | odps.security.ip.whitelist |
| Virtual private cloud (VPC) | odps.security.vpc.whitelist |
Whitelist interaction rule: configuring a whitelist for one network type blocks all access from the other network type. For example, if you set only odps.security.ip.whitelist, all VPC access is denied, and vice versa. To allow unrestricted access from the other network type, use a wildcard:
To allow all VPC access while restricting Internet access: set
odps.security.vpc.whitelist=*To allow all Internet access while restricting VPC access: set
odps.security.ip.whitelist=0.0.0.0/0
After you update a whitelist, the change takes effect after 5 minutes.
Default behavior
When the whitelist feature is not enabled, access is unrestricted by IP:
Cloud product interconnection network: all IPs using the cloud product interconnection network endpoint within the same account and region can access the project.
VPC: all IPs using the VPC endpoint within the same VPC can access the project.
Public network: all IPs using the public network endpoint can access the project.
Supported IP address formats
MaxCompute supports project-level whitelists only. Accepted formats:
Individual IPv4 or IPv6 address — for example,
192.168.0.0or2001:db8::CIDR notation — for example,
172.12.0.0/16or2001:db8::/32IP address range — for example,
192.168.10.0-192.168.255.255or2001:db8:1:1:1:1:1:1-2001:db8:4:4:4:4:4:4
Prerequisites
Before you begin, identify the IP addresses to add to the whitelist:
For the cloud product interconnection network whitelist:
MaxCompute client: get the IP address of the device where the client is installed.
Application server: get the IP address of the server running the application.
Proxy server: get the IP address of the last-hop proxy server.
DataWorks: add the IP addresses of the DataWorks exclusive resource group.
For the VPC whitelist:
Get the ID of the VPC.
Configure a VPC endpoint. For more information, see Endpoints.
Identify the IP addresses of all services that need to access MaxCompute (for example, Data Integration of DataWorks, Data Map of DataWorks, and Realtime Compute for Apache Flink).
Configure an IP address whitelist
Configure whitelists using the MaxCompute client or the MaxCompute console.
Configure using the MaxCompute client
Use the setproject command to set odps.security.ip.whitelist (Internet and cloud product interconnection network) and odps.security.vpc.whitelist (VPC). For command syntax and parameters, see View the properties of a project.
Always include your current IP address in the whitelist before running the command. If your IP is not in the whitelist when the change takes effect, you will lose access to the project.
Internet and cloud product interconnection network only
Allows listed IPs over the Internet and cloud product interconnection network. Blocks all VPC access.
setproject odps.security.ip.whitelist=192.168.0.0 odps.security.vpc.whitelist=\N;To allow all VPC access while restricting Internet access:
setproject odps.security.ip.whitelist=192.168.0.0 odps.security.vpc.whitelist=*;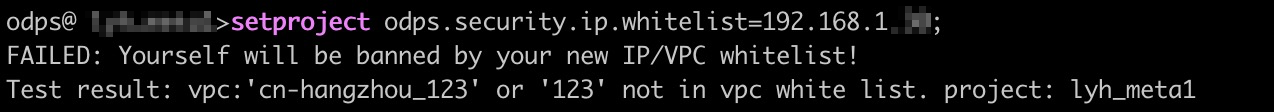
VPC only
Allows listed IPs over the VPC. Blocks all Internet and cloud product interconnection network access.
setproject odps.security.ip.whitelist=\N odps.security.vpc.whitelist=<VPC-ID>[192.168.0.10,192.168.0.20];To allow all Internet access while restricting VPC access:
setproject odps.security.ip.whitelist=0.0.0.0/0 odps.security.vpc.whitelist=<VPC-ID>[192.168.0.10,192.168.0.20];Both network types
Allows the listed IPs over the Internet, cloud product interconnection network, and VPC:
setproject odps.security.ip.whitelist=192.168.0.0 odps.security.vpc.whitelist=<VPC-ID>[192.168.0.10,192.168.0.20];To include multiple IPs and multiple VPCs:
setproject odps.security.ip.whitelist=192.168.0.0,192.168.0.10 odps.security.vpc.whitelist=<VPC-ID-1>[192.168.0.10,192.168.0.20],<VPC-ID-2>;Separate multiple Internet/cloud product interconnection network IPs with commas. For VPCs, use the format <VPC-ID>[IP1,IP2]. To allow all IPs from a VPC without filtering by IP, specify only the VPC ID.
Configure in the MaxCompute console
Log on to the MaxCompute console and select a region.
In the left-side navigation pane, click Projects.
Find the project and click Manage in the Actions column.
On the Parameter Configuration tab, click Edit in the IP Address Whitelist section.
Enter the IP addresses:
Internet and cloud product interconnection network IP addresses: separate multiple IPs with commas. To allow all VPC access while restricting Internet access, set VPC IP Addresses to
*.VPC IP addresses: use the format
<VPC-ID-1>[IP1,IP2],<VPC-ID-2>. To allow all Internet access while restricting VPC access, set Internet and Cloud Product Interconnection Network IP Address to0.0.0.0/0.

View IP address whitelists
Run setproject; to view the current whitelist configuration:
setproject;The output lists the current values of odps.security.ip.whitelist and odps.security.vpc.whitelist. An empty value means the corresponding whitelist is not configured.
Example output:
odps.security.ip.whitelist=192.168.0.0
odps.security.vpc.whitelist=<VPC-ID>[192.168.0.10,192.168.0.20]Legacy VPC ID format
If the whitelist was configured using a region ID and numeric VPC ID (for example, cn-beijing_125179), the output looks like:
odps.security.vpc.whitelist=cn-beijing_125179[192.168.0.10,192.168.0.20]The region prefix is used only as an identifier — cn-beijing_1234, cn_1234, cn-shanghai_1234, and 1234 all refer to the same VPC. Switch to using the VPC instance ID for consistency. If you have multiple format entries for the same VPC, the effective IP list is the union of all entries. To verify the mapping between numeric IDs and VPC instance IDs, submit a support ticket.
Modify an IP address whitelist
Run the setproject command to update the whitelist.
The setproject command replaces the entire whitelist, not just the IPs you specify. When adding IPs to an existing whitelist, include all existing IPs plus the new ones in a single command.
Update the Internet and cloud product interconnection network whitelist:
setproject odps.security.ip.whitelist=192.168.0.10;Update the VPC whitelist:
setproject odps.security.vpc.whitelist=<VPC-ID>[192.168.10.10,192.168.0.20]Disable the IP address whitelist feature
Leave both parameters blank to disable all IP restrictions:
setproject odps.security.ip.whitelist= odps.security.vpc.whitelist= ;After disabling, access over the Internet, cloud product interconnection network, and VPC is unrestricted.
Allow Alibaba Cloud services to access MaxCompute
To allow all Alibaba Cloud services to access MaxCompute over the internal network or VPC, run:
setproject odps.security.ip.whitelist=192.168.0.0/16,172.16.0.0/12,10.0.0.0/8,11.0.x.x/8,33.0.x.x/8,100.64.0.0/10 odps.security.vpc.whitelist=<regionname>_*,cn_*;Add IP addresses to odps.security.ip.whitelist as needed for your business requirements.
Region IDs
|
Region |
Region ID |
|
China (Hangzhou) |
cn-hangzhou |
|
China (Shanghai) |
cn-shanghai |
|
China (Beijing) |
cn-beijing |
|
China (Zhangjiakou) |
cn-zhangjiakou |
|
China (Ulanqab) |
cn-wulanchabu |
|
China (Shenzhen) |
cn-shenzhen |
|
China (Chengdu) |
cn-chengdu |
|
China (Hong Kong) |
cn-hongkong |
|
China East 2 Finance |
cn-shanghai-finance-1 |
|
China North 2 Ali Gov 1 |
cn-north-2-gov-1 |
|
China South 1 Finance |
cn-shenzhen-finance-1 |
|
Japan (Tokyo) |
ap-northeast-1 |
|
Singapore |
ap-southeast-1 |
|
Malaysia (Kuala Lumpur) |
ap-southeast-3 |
|
Indonesia (Jakarta) |
ap-southeast-5 |
|
Germany (Frankfurt) |
eu-central-1 |
|
UK (London) |
eu-west-1 |
|
US (Silicon Valley) |
us-west-1 |
|
US (Virginia) |
us-east-1 |
|
UAE (Dubai) |
me-east-1 |
Troubleshooting
Error: IP not in whitelist
FAILED: Access denied by project ip white list: sourceIP:'xxxxx' is not in white list. project:xxxThe source IP address is not in the Internet and cloud product interconnection network whitelist. Add the IP shown in sourceIP to odps.security.ip.whitelist for the project.
Error: VPC not in whitelist
FAILED: Access denied by project vpc white list: vpc:'vpc-xxx' not in vpc white list, ip: 'xxxx'.project:xxxThe VPC making the request is not in the VPC whitelist. Add the VPC instance ID to odps.security.vpc.whitelist.
Error: IP not allowed within a whitelisted VPC
FAILED: Access denied by project vpc white list: sourceIP:'xxxxx' from vpc 'vpc-xxx' is not in vpc white list. project: xxxThe VPC is in the whitelist, but the specific IP address is not in the allowed IP list for that VPC. Add the IP to the VPC's allowed IP list in odps.security.vpc.whitelist.