Key Management Service (KMS) provides default data encryption capabilities for other Alibaba Cloud services. To encrypt data in an Alibaba Cloud service, you can use the service key that is created by the Alibaba Cloud service or a key that is created in KMS. This topic describes the integration of Alibaba Cloud services with KMS, including the integration benefits and the encryption mechanism.
Benefits of integrating Alibaba Cloud services with KMS
Increase data security and privacy protection
KMS provides data encryption capabilities for most Alibaba Cloud services. You can configure an encryption solution when or after you purchase an Alibaba Cloud service. KMS performs end-to-end encryption on cloud data, such as data generated by database engines, when Alibaba Cloud services are being used. This provides a secure encryption solution for your cloud data and increases the overall security and privacy of your data.
Eliminate the fees for developing your own data encryption systems
When you develop your own data encryption systems, you may encounter various challenges. You can integrate your services with KMS to address the challenges. The following list describes the challenges:
Design a proper key hierarchy and data distribution mode to balance encryption performance and security.
Design the key rotation and data re-encryption mechanisms.
Master cryptography technologies and use appropriate encryption algorithms to ensure that encryption systems are robust, secure, and tamper-proof.
Types of keys that support data encryption in Alibaba Cloud services
KMS provides default keys, software-protected keys, and hardware-protected keys. You can use these keys to encrypt data in Alibaba Cloud services. The following table describes the keys. For more information, see Overview of key management.
Key creator | Key type | Key material origin | Billing | Description |
Alibaba Cloud service | Default key (service key) | KMS | Free of charge | Within an Alibaba Cloud account, each Alibaba Cloud service can create only one service key in a region. |
User | Customer master key (CMK) which is used as the default key | Supported key material origins:
| Free of charge | After you create a key, you must authorize your Alibaba Cloud service to use the key. For more information, see Custom policies. |
Software-protected key | KMS | Paid | ||
Hardware-protected key | Supported key material origins:
| Paid |
Use a key for server-side encryption in Alibaba Cloud services
In this example, a key is configured for server-side encryption in an Alibaba Cloud service when you purchase the Alibaba Cloud service. You can also configure a key after you purchase an Alibaba Cloud service. For more information, see the documentation on the official website of each Alibaba Cloud service.
Service key
You can view the service keys that are created in the KMS console.
When you purchase an Alibaba Cloud service, select Default Service CMK. This way, you can use the service key created by your Alibaba Cloud service to encrypt server-side data. In this example, an Elastic Compute Service (ECS) instance is purchased.
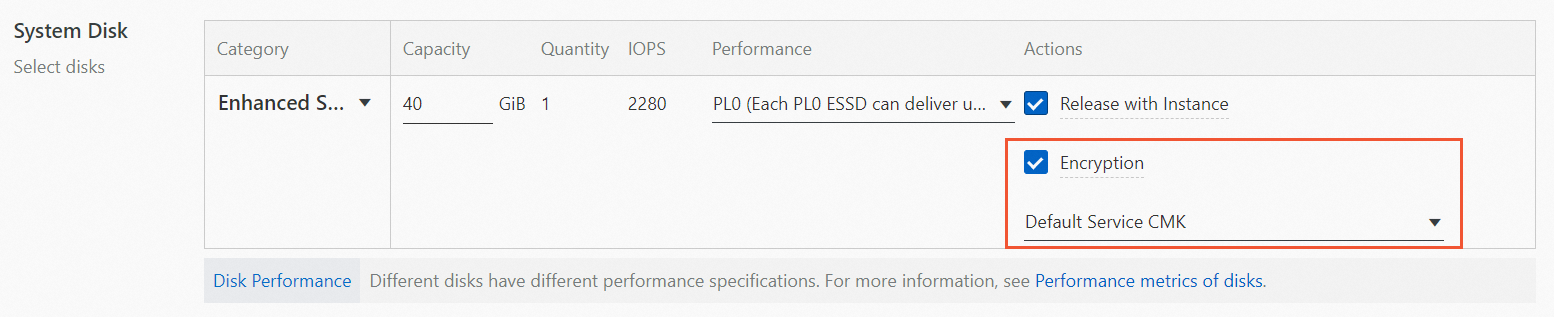 Note
NoteFor easy identification, a service key is automatically associated with an alias in the
alias/acs/<cloud product code>format. For example, the service key created by ECS is associated with thealias/acs/ecsalias.In the KMS console, view the service key that is created.
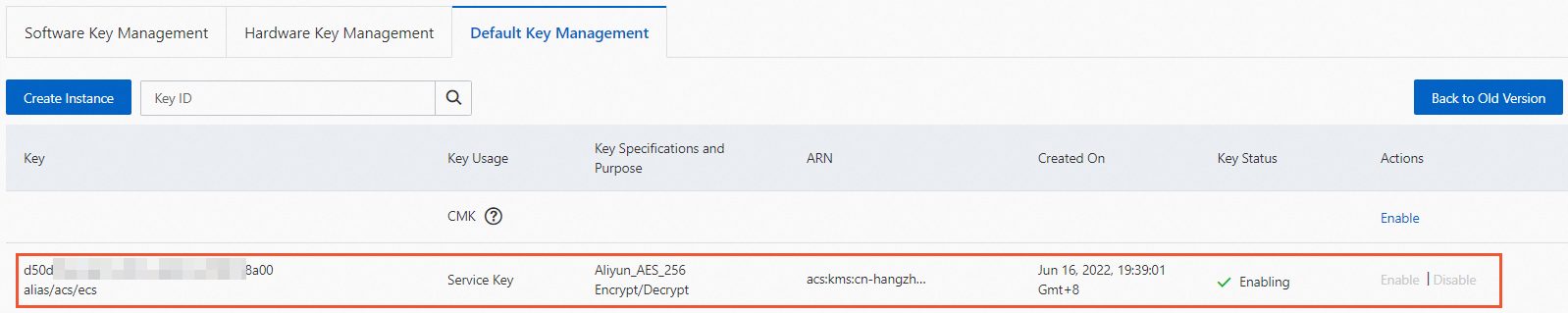 Note
NoteFor a service key, the value of Key Usage is Service Key.
A service key is managed by an Alibaba Cloud service. You cannot manage a service key in the KMS console. For example, you cannot enable or disable a service key. You can view the operation and usage records of a service key in the ActionTrail console.
User-created key
CMK as a default key
Enable a CMK in the KMS console. For more information, see Getting started with keys.
In this example, the alias of the CMK is
alias/byok.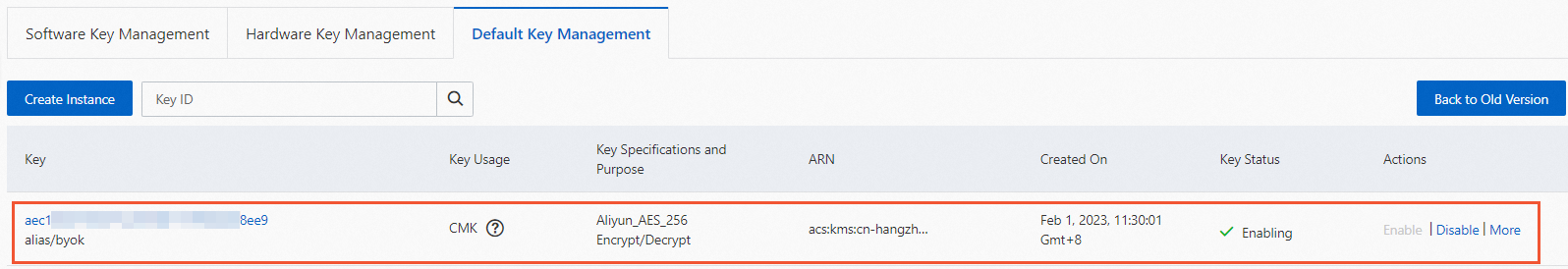
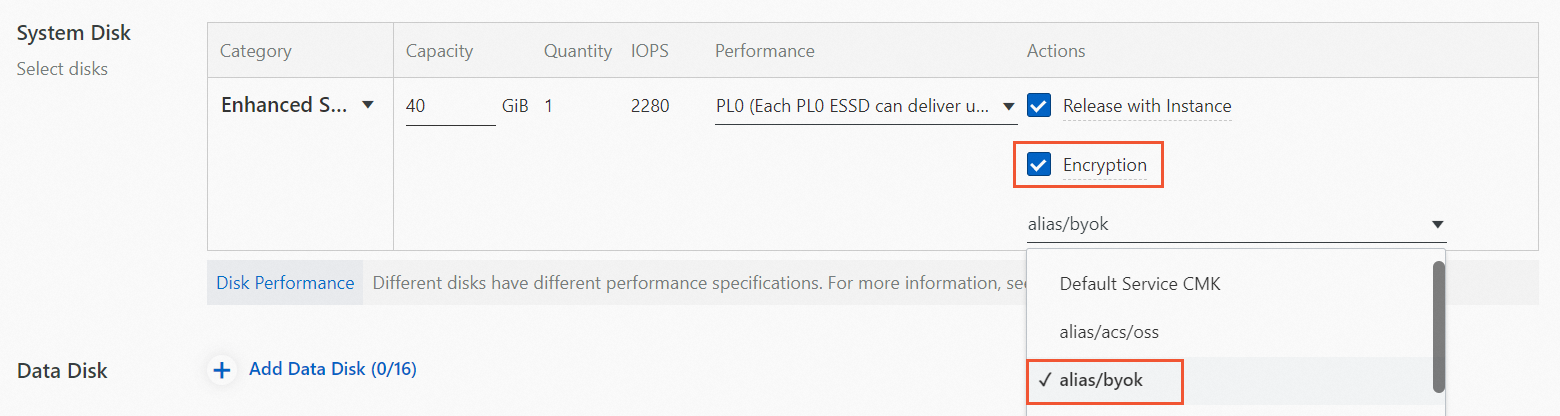
When you purchase an Alibaba Cloud service, select the CMK that is used as a default key to encrypt server-side data.
In this example, an ECS instance is purchased.
Software-protected key
Purchase a KMS instance of the software key management type. For more information, see Purchase and enable a KMS instance.
In the KMS console, create a software-protected key. For more information, see Getting started with keys.
When you purchase an Alibaba Cloud service, select the software-protected key to encrypt server-side data.
Hardware-protected key
Purchase a KMS instance of the hardware key management type. For more information, see Purchase and enable a KMS instance.
In the KMS console, create a hardware-protected key. For more information, see Getting started with keys.
When you purchase an Alibaba Cloud service, select the hardware-protected key to encrypt server-side data.
Encryption process
The encryption process in each Alibaba Cloud service varies based on the business form and customer requirements. In most cases, envelope encryption is used to implement server-side encryption in Alibaba Cloud services. Data keys are encrypted by using KMS keys and then are used to encrypt server-side data, as shown in the following figure.
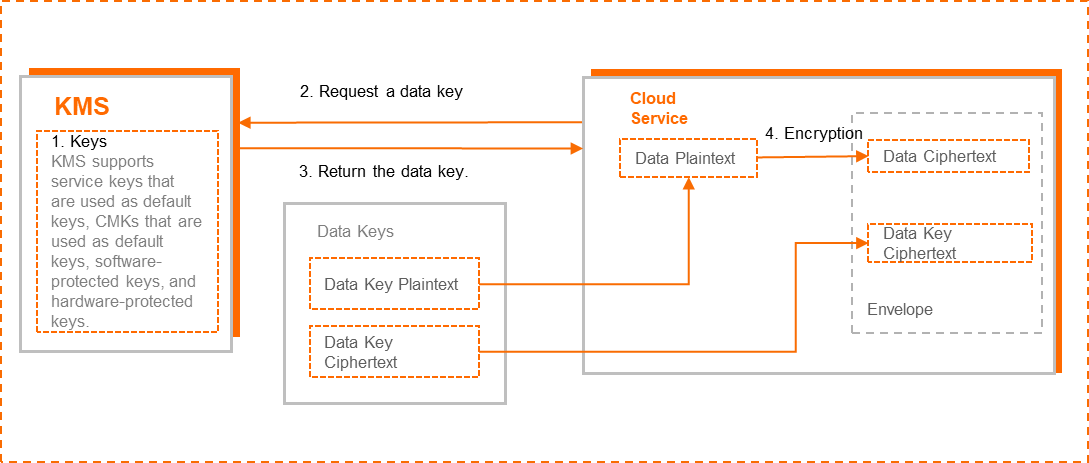
Create a key in KMS.
Call the GenerateDataKey operation of KMS to request a data key.
KMS returns a data key, which contains the data key plaintext and the data key ciphertext. The data key ciphertext is generated by encrypting the data key plaintext by using the specified key.
An Alibaba Cloud service uses the data key plaintext to encrypt data plaintext to generate data ciphertext, and writes the data key ciphertext and the data ciphertext in persistent storage.
The data key ciphertext and the data ciphertext are packaged together in an envelope.
KMS transfers the data key to your Alibaba Cloud service over a secure transmission channel. The data key plaintext is used only in the memory of your Alibaba Cloud service and is not stored in persistent storage.
Access control
KMS checks whether an Alibaba Cloud service has permissions to use a specific key based on Resource Access Management (RAM). You can configure permission policies for an Alibaba Cloud service in the RAM console or follow the on-screen instructions in the console of the Alibaba Cloud service to allow or deny the Alibaba Cloud service to use a specific key. For more information, see Custom policies.
Auditing
You can audit the use of keys for Alibaba Cloud services in ActionTrail. For more information, see Use ActionTrail to query KMS events.