Key Management Service (KMS) provides default data encryption capabilities for other Alibaba Cloud services. To encrypt data in an Alibaba Cloud service, you can use the service key created by the Alibaba Cloud service or a key created in KMS. Cloud administrators, security engineers, and architects can use this page to understand how KMS integrates with other services, choose the right key type, and set up access control and auditing.
Why integrate with KMS
Building your own encryption system requires solving hard problems: designing a key hierarchy that balances performance and security, implementing key rotation and data re-encryption, and applying encryption algorithms correctly to keep the system tamper-proof. KMS handles all of this for you, eliminating the fees for developing your own data encryption systems.
When you enable KMS integration, KMS performs end-to-end encryption on cloud data — including data generated by database engines — without requiring changes to how your applications access that data.
Key types for server-side encryption
KMS supports four key types for server-side encryption. The following table compares them across the dimensions most relevant to choosing a key.
| Service key | CMK as default key | Software-protected key | Hardware-protected key | |
|---|---|---|---|---|
| Key creator | Alibaba Cloud service | You | You | You |
| Key material origin | KMS | KMS or Bring your own key (BYOK) | KMS | KMS or BYOK |
| Control | Managed by the Alibaba Cloud service; not configurable in KMS console (for example, you cannot enable or disable a service key) | Full control via KMS console | Full control via KMS console | Full control via KMS console |
| Billing | Free | Free | Paid | Paid |
| Limit | One per service per region per account | — | Requires a KMS instance (software key management type) | Requires a KMS instance (hardware key management type) |
For more information about key types, see Overview of key management.
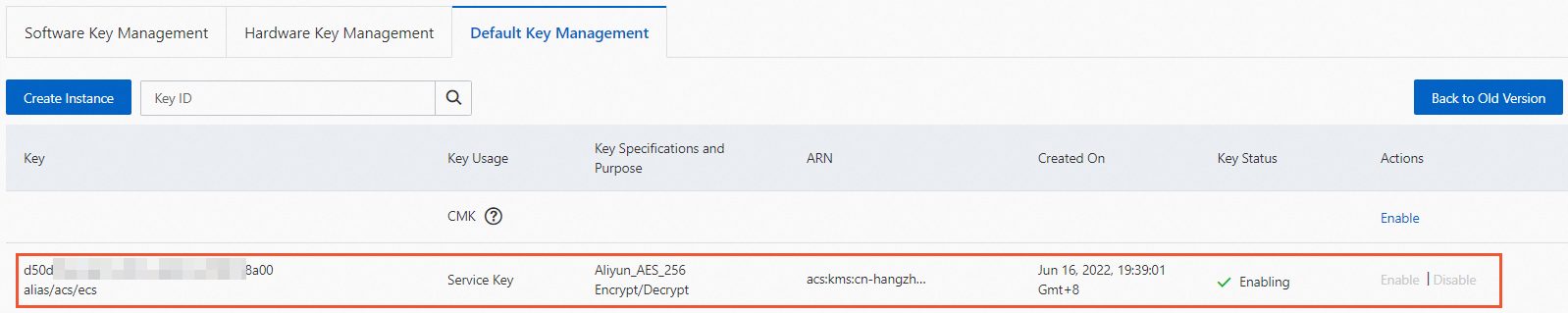
Service keys are automatically assigned an alias in the alias/acs/<cloud product code> format. For example, the service key created by Elastic Compute Service (ECS) uses the alias alias/acs/ecs. The Key Usage field in the KMS console shows Service Key for these keys. Operation and usage records for service keys are available in the ActionTrail console.
Configure server-side encryption
The following steps show how to configure each key type when purchasing an Alibaba Cloud service. ECS is used as the example, but the same steps apply to other integrated services. You can also configure encryption after purchase — see the documentation for each service.
Use a service key
When purchasing an Alibaba Cloud service, select Default Service CMK. The service automatically creates and manages a service key to encrypt server-side data.
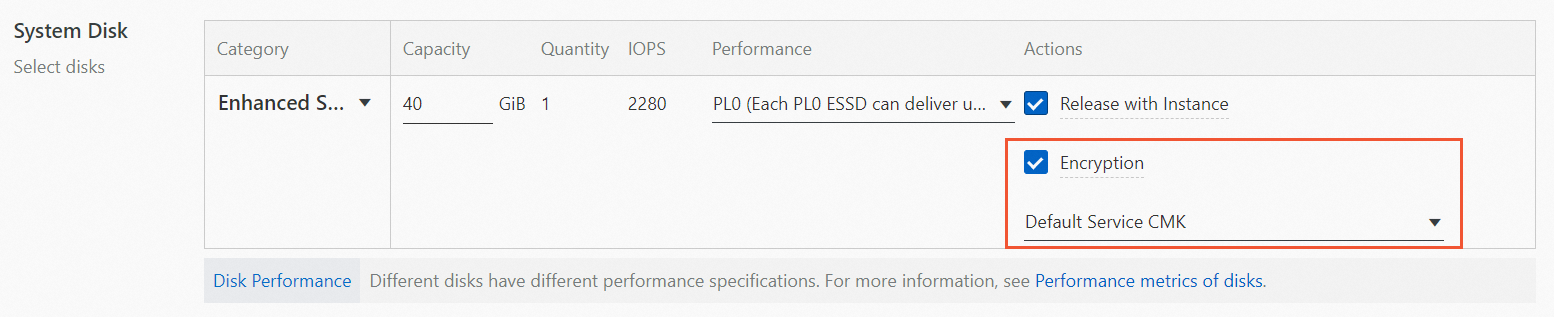
In the KMS console, view the service key that was created.
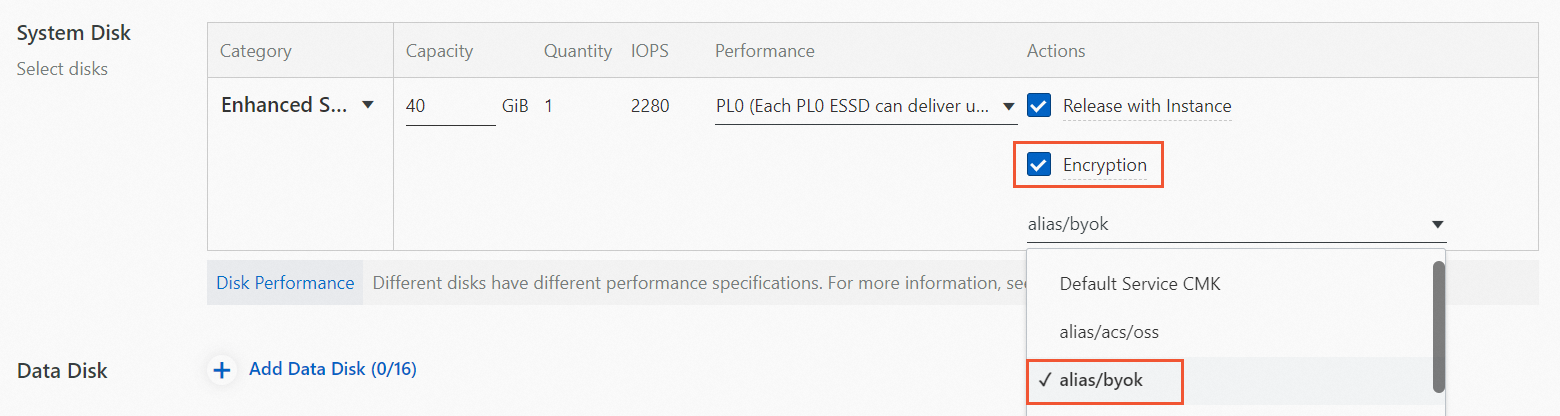
Use a CMK as a default key
Enable a customer master key (CMK) in the KMS console. For details, see Getting started with keys. In this example, the CMK alias is
alias/byok.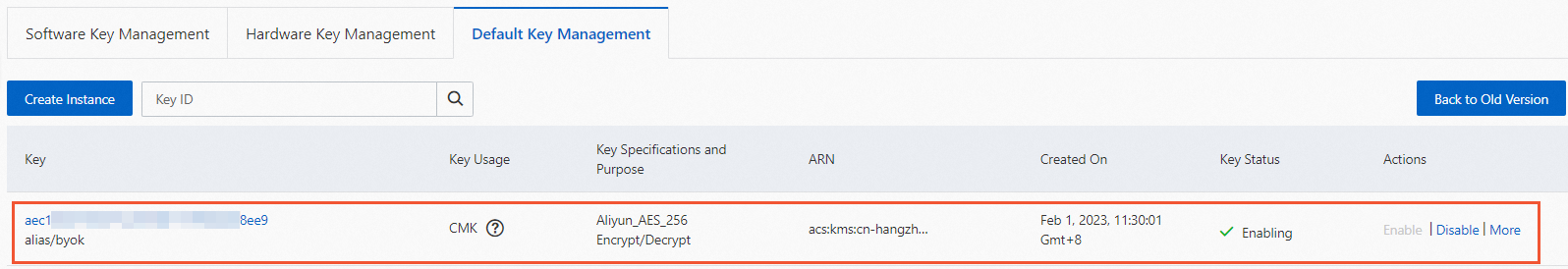
When purchasing an Alibaba Cloud service, select the CMK as the default key.
Use a software-protected key
Purchase a KMS instance of the software key management type. For details, see Purchase and enable a KMS instance.
Create a software-protected key in the KMS console. For details, see Getting started with keys.
When purchasing an Alibaba Cloud service, select the software-protected key.
Use a hardware-protected key
Purchase a KMS instance of the hardware key management type. For details, see Purchase and enable a KMS instance.
Create a hardware-protected key in the KMS console. For details, see Getting started with keys.
When purchasing an Alibaba Cloud service, select the hardware-protected key.
How it works
Encryption and decryption happen transparently in the Alibaba Cloud service — your applications access data the same way regardless of whether encryption is enabled.
Most Alibaba Cloud services implement server-side encryption using envelope encryption: a data key encrypts the actual data, and KMS encrypts the data key. The following diagram and steps describe this process.
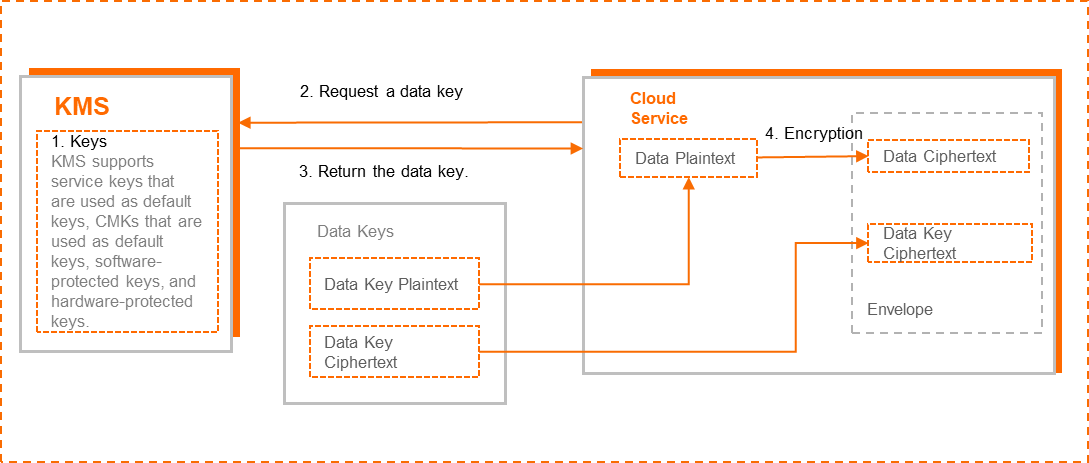
Create a key in KMS.
Call the
GenerateDataKeyoperation to request a data key.KMS returns the data key in two forms: plaintext and ciphertext. The ciphertext is the plaintext encrypted by the specified KMS key.
The Alibaba Cloud service uses the data key plaintext to encrypt the data, then writes the data key ciphertext and the data ciphertext to persistent storage as an envelope.
KMS transfers the data key over a secure channel. The data key plaintext is used only in memory and is never written to persistent storage.
Access control
KMS uses Resource Access Management (RAM) to check whether an Alibaba Cloud service has permission to use a specific key. Configure permission policies in the RAM console or follow the on-screen instructions in the Alibaba Cloud service console. For details, see Custom policies.
Auditing
You can audit the use of keys for Alibaba Cloud services in ActionTrail. Use the ActionTrail console to review which keys were used and when. For details, see Use ActionTrail to query KMS events.
What's next
KMS-compatible Alibaba Cloud services — see the full list of services that support KMS integration