KMS integrates with Cloud Monitor to track security-relevant lifecycle events and instance resource usage. When an event is triggered, it appears automatically in both the KMS console and the Cloud Monitor console — no configuration required to start receiving events.
This topic covers:
KMS system events — what events exist and what triggers them
Cloud Monitor metrics — metrics available for custom alerting
View system events — how to query past events (up to 90 days)
Set up alert notifications — how to get notified when events occur
Event notification JSON reference — field-level reference for alert payloads
KMS system events
The following events are generated automatically when trigger conditions are met.
| Event | Level | Trigger condition |
|---|---|---|
| QPS has reached 90% | CRITICAL | Real-time queries per second (QPS) of a KMS instance reaches 90% of its quota. |
| QPS has reached 70% | INFO | Real-time QPS reaches 70% of its quota. If the limit is exceeded, KMS may become inaccessible and affect business continuity. |
| Key scheduled for deletion | WARN | A key enters the scheduled deletion waiting period. |
| Key deleted | WARN | A key is permanently deleted. |
| Secret scheduled for deletion | WARN | A secret enters the scheduled deletion waiting period. |
| Secret deleted | WARN | A secret is permanently deleted. |
| Managed secret rotation failed | CRITICAL | An automatic secret rotation fails. |
| Managed secret rotation succeeded | INFO | An automatic secret rotation completes successfully. |
| Key sync failed | CRITICAL | A key fails to sync across regions. See Cross-region synchronization. |
| Key sync succeeded | INFO | A key successfully syncs across regions. See Cross-region synchronization. |
| ClientKey expiration reminder | CRITICAL | Triggered 180, 90, 30, and 7 days before a ClientKey expires. See Application access points overview. |
| Access management usage has reached 70% | INFO | Access management usage reaches 70% of its quota. If the limit is exceeded, you cannot create new access management policies. |
| Access management usage has reached 90% | WARN | Access management usage reaches 90% of its quota. If the limit is exceeded, you cannot create new access management policies. |
| Key usage has reached 70% | INFO | Key usage reaches 70% of its quota. If the limit is exceeded, you cannot create new keys. |
| Key usage has reached 90% | WARN | Key usage reaches 90% of its quota. If the limit is exceeded, you cannot create new keys. |
| Log analysis log volume has reached 70% | INFO | Log analysis log volume reaches 70% of its quota. If the limit is exceeded, new logs cannot be written. |
| Log analysis log volume has reached 90% | WARN | Log analysis log volume reaches 90% of its quota. If the limit is exceeded, new logs cannot be written. |
| Secret usage has reached 70% | INFO | Secret usage reaches 70% of its quota. If the limit is exceeded, you cannot create new secrets. |
| Secret usage has reached 90% | WARN | Secret usage reaches 90% of its quota. If the limit is exceeded, you cannot create new secrets. |
To receive notifications (email, SMS, or webhook) for these events, configure alert rules in the Cloud Monitor console. See Set up alert notifications.
Cloud Monitor metrics
The following KMS metrics are available in Cloud Monitor. All metrics support alerting, and the statistics type for all metrics is Value.
| Metric | Description | Dimensions | Recommended use |
|---|---|---|---|
| Requests per minute for an instance | Total requests per minute across all operation types | userId, regionId, instanceId | Identify overall traffic trends; alert on sustained spikes that may exhaust your QPS quota |
| Symmetric encryption/decryption requests per minute | Symmetric operation requests per minute | userId, regionId, instanceId | Monitor symmetric operation load |
| Asymmetric encryption requests per minute | Asymmetric encryption requests per minute | userId, regionId, instanceId | Monitor asymmetric encryption load |
| Asymmetric decryption requests per minute | Asymmetric decryption requests per minute | userId, regionId, instanceId | Monitor asymmetric decryption load |
| Asymmetric signing requests per minute | Asymmetric signing requests per minute | userId, regionId, instanceId | Monitor signing operation load |
| Asymmetric signature verification requests per minute | Asymmetric signature verification requests per minute | userId, regionId, instanceId | Monitor signature verification load |
| Secret operation requests per minute | Secret-related requests per minute | userId, regionId, instanceId | Monitor Secrets Manager usage |
| Other requests per minute | Requests not classified under the above operation types | userId, regionId, instanceId | Catch unexpected request patterns |
| 5xx error requests | Requests that returned 5xx error codes per minute | userId, regionId, instanceId | Detect service-side failures; alert on sustained error spikes to catch systemic issues early |
| 4xx error requests | Requests that returned 4xx error codes per minute | userId, regionId, instanceId | Detect misconfigured clients or permission issues |
| Request latency | Average request latency per minute across all operations | userId, regionId, instanceId | Alert when latency exceeds your application's tolerance threshold |
| KMS instance CPU utilization | CPU utilization of the KMS instance | user_id, instance_id | Alert when CPU is consistently high, indicating the need for capacity review |
| KMS instance symmetric QPS utilization | Symmetric QPS utilization as a percentage of quota | user_id, instance_id | Alert before quota exhaustion causes service degradation |
| KMS instance asymmetric QPS utilization | Asymmetric QPS utilization as a percentage of quota | user_id, instance_id | Alert before quota exhaustion causes service degradation |
For instructions on configuring Cloud Monitor alerts and viewing metric statistics, see KMS overview.
View system events
KMS retains system events for the last 90 days. Use either of the following methods to query them.
Method 1: KMS console
Log on to the KMS console. In the top navigation bar, select a region. In the left navigation pane, choose Security Operations > Alert Events.KMS console
On the CloudMonitor Alerts tab, select the event type and time range you want to query.
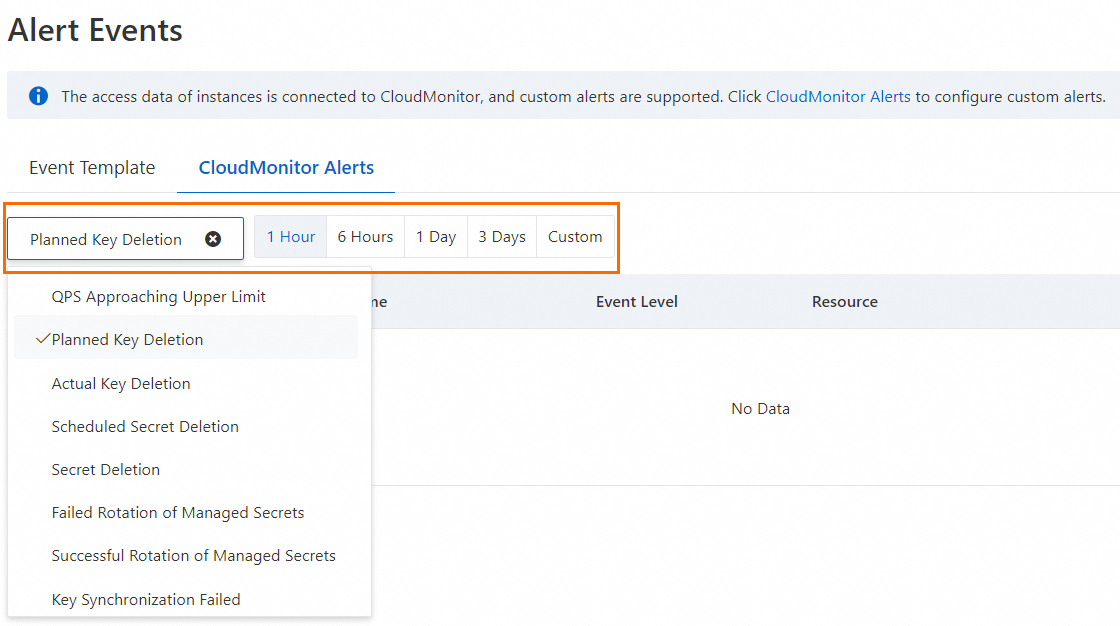
In the Actions column, click Details to view the full event payload.
Method 2: Cloud Monitor console
Log on to the Cloud Monitor console.
In the left navigation pane, choose Event Center > System Event.
On the Event Monitoring tab, set Product to Key Management Service, select an event level, event name, and time period, then click Search.
Click Details in the Actions column for the target event.
Set up alert notifications
Alert rules route event notifications to contacts via email, SMS, or webhook. Rules can only be configured in the Cloud Monitor console.
Log on to the Cloud Monitor console.
In the left navigation pane, choose Event Center > System Event.
On the Event Monitoring tab, click Save as Alert Rule.
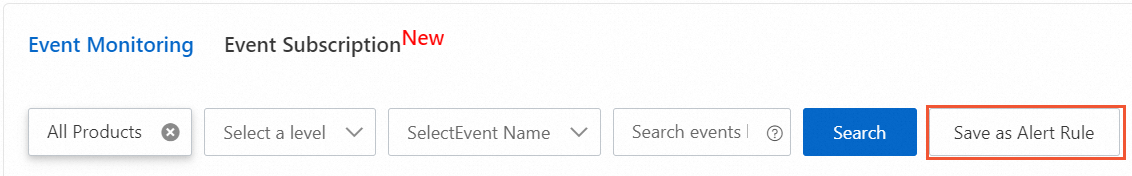
In the Create/Modify Event-triggered Alert Rule panel, configure the alert settings. For details on each configuration field, see Create an alert rule for a system event.
To apply custom processing to alert notifications — such as deduplication or noise reduction — configure notification policies on the Event Subscription page instead. For more information, see Manage event subscriptions (recommended).
Event notification JSON reference
Each system event notification includes a JSON payload with two parts:
Top-level fields — metadata for routing and filtering (product, resource, level, event name, status)
`content` fields — the event-specific data payload
All event notification examples below follow this structure.
QPS has reached 90%
This event fires when real-time QPS on a KMS instance reaches 90% of its configured quota. At this threshold, KMS is at risk of becoming inaccessible if traffic continues to grow. Use the qps and qpsQuota fields to calculate how close you are to the limit and plan capacity accordingly.
{
"product": "kms",
"resourceId": "acs:kms:cn-shanghai:119285********60:instance/<resource-id>",
"level": "CRITICAL",
"instanceName": "instanceName",
"regionId": "cn-hangzhou",
"name": "Instance:QPS:Reminder",
"content": {
"eventId": "119285********60:0d603b4a-********71:175*****07",
"qps": "***",
"kmsInstanceId": "kst***pn8",
"time": "2025-08-26 05:43:00",
"qpsQuota": "***"
},
"status": "normal"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119285******60:0d603b4a-****71:175***07 |
qps | Current QPS | 10000 |
kmsInstanceId | KMS instance ID | kst***pn8 |
qpsQuota | QPS quota limit | 10000 |
QPS has reached 70%
This event fires when real-time QPS reaches 70% of quota. Use it as an early warning to investigate traffic growth before the 90% threshold is reached.
{
"product": "kms",
"resourceId": "acs:kms:cn-hangzhou:1192******18460:instance/<resource-id>",
"level": "INFO",
"instanceName": "instanceName",
"regionId": "cn-hangzhou",
"name": "Instance:QPS:Reminder:70%",
"content": {
"eventId": "130***756",
"qps": "***",
"kmsInstanceId": "kst***e4x",
"time": "2025-12-12 07:49:00",
"qpsQuota": "10***"
},
"status": "normal"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119285******60:0d603b4a-****71:175***07 |
qps | Current QPS | 10000 |
kmsInstanceId | KMS instance ID | kst***pn8 |
qpsQuota | QPS quota limit | 10000 |
Key scheduled for deletion
This event fires when a key enters the scheduled deletion waiting period. The key is not yet deleted — use this window to cancel the deletion if it was unintentional. Check plannedDeleteTime to determine how much time remains before the deletion becomes permanent.
{
"id": "83d05dd6-1066-4b3f-99be-********19",
"status": "normal",
"instanceName": "0d603b4a-********71be",
"resourceId": "acs:kms:cn-hangzhou:119285********60:key/0d603b4a-********71be",
"content": {
"eventId": "119285********60:0d603b4a-********71:175*****07",
"keyId": "0d603b4a-********71be",
"deleteEntityArn": "acs:kms:cn-hangzhou:119285********60:key/0d603b4a-********71be",
"plannedDeleteTime": "2025-09-01T07:15:07Z"
},
"product": "kms",
"time": 1756106122000,
"level": "WARN",
"regionId": "cn-hangzhou",
"groupId": "0",
"name": "Key:DeleteKey:ScheduleDeletion"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119285******60:0d603b4a-****71:175***07 |
keyId | Key ID | 0d603b4a-********71be |
deleteEntityArn | Alibaba Cloud Resource Name (ARN) of the key pending deletion | acs:kms:cn-hangzhou:119285******60:key/0d603b4a-******71be |
plannedDeleteTime | Scheduled deletion time | 2025-09-01T07:15:07Z |
Key deleted
This event fires when a key is permanently deleted after the scheduled waiting period ends. After this event is generated, the key cannot be recovered.
{
"id": "40d14dbc-5b49-481f-********ce",
"status": "normal",
"instanceName": "key-hzz68916ed********q4",
"resourceId": "acs:kms:cn-hangzhou:119285********60:key/key-hzz6********pq4",
"content": {
"eventId": "119285********60:key-hzz6********pq4:1755855590",
"keyId": "0d603b4a-********71be",
"deleteEntityArn": "acs:kms:cn-hangzhou:119285********60:key/0d603b4a-********71be",
"deleteTime": "2025-08-22T09:39:50Z"
},
"product": "kms",
"time": 1755855632000,
"level": "WARN",
"regionId": "cn-hangzhou",
"groupId": "0",
"name": "Key:DeleteKey:ActualDeletion"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119285******60:0d603b4a-****71:175***07 |
keyId | Key ID | 0d603b4a-********71be |
deleteEntityArn | ARN of the deleted key | acs:kms:cn-hangzhou:119285******60:key/0d603b4a-******71be |
deleteTime | Time the key was permanently deleted | 2025-08-22T09:39:50Z |
Secret scheduled for deletion
This event fires when a secret enters the scheduled deletion waiting period. The secret is not yet deleted — cancel the deletion if it was unintentional. Check plannedDeleteTime to see how much time remains before the deletion becomes permanent.
{
"id": "a065edc8-*******f9ba432",
"status": "normal",
"instanceName": "XrGp****",
"resourceId": "acs:kms:cn-shanghai:119285********60:secret/XrGp****",
"content": {
"eventId": "119285********60:XrGp****:175*****45",
"secretName": "XrGp****",
"deleteEntityArn": "acs:kms:cn-shanghai:119285********60:secret/XrGp****",
"plannedDeleteTime": "2025-09-01T06:10:45Z"
},
"product": "kms",
"time": 1756102268000,
"level": "WARN",
"regionId": "cn-shanghai",
"groupId": "0",
"name": "Secret:DeleteSecret:ScheduleDeletion"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119285******60:0d603b4a-****71:175***07 |
secretName | Secret name | XrGp**** |
deleteEntityArn | ARN of the secret pending deletion | acs:kms:cn-shanghai:119285******60:secret/XrGp** |
plannedDeleteTime | Scheduled deletion time | 2025-09-01T06:10:45Z |
Secret deleted
This event fires when a secret is permanently deleted after the scheduled waiting period ends. After this event is generated, the secret cannot be recovered.
{
"id": "a065edc8-********ba432",
"status": "normal",
"instanceName": "XrGp****",
"resourceId": "acs:kms:cn-shanghai:119285********60:secret/XrGp****",
"content": {
"eventId": "119285********60:XrGp****:1756102245",
"secretName": "XrGp****",
"deleteEntityArn": "acs:kms:cn-shanghai:119285********60:secret/XrGp****",
"deleteTime": "2025-09-01T06:10:45Z"
},
"product": "kms",
"time": 1756102268000,
"level": "WARN",
"regionId": "cn-shanghai",
"groupId": "0",
"name": "Secret:DeleteSecret:ScheduleDeletion"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119285******60:0d603b4a-****71:175***07 |
secretName | Secret name | XrGp**** |
deleteEntityArn | ARN of the deleted secret | acs:kms:cn-shanghai:119285******60:secret/XrGp** |
deleteTime | Time the secret was permanently deleted | 2025-08-22T09:39:50Z |
Managed secret rotation failed
This event fires when Secrets Manager fails to automatically rotate a secret. Check the failureInfo field for the specific error code and message to diagnose the root cause.
{
"id": "ac54ac2b-********01aba",
"status": "Failed",
"instanceName": "acs/ecs/secret_rotator",
"resourceId": "acs:kms:cn-chengdu:119285********60:secret/acs/ecs/secret_rotator",
"content": {
"eventId": "119285********60:acs/ecs/secret_rotator:1755853996",
"secretName": "acs/ecs/secret_rotator",
"secretType": "ECS",
"rotationEntityArn": "acs:kms:cn-chengdu:119285********60:secret/acs/ecs/secret_rotator",
"rotationStatus": "Enabled",
"secretSubType": "ECSLoginPassword",
"failureInfo": {
"errorCode": "RotateError",
"errorMessage": "output , err stdout:[Module:DescribeECSInstances failed] "
},
"failureTime": "2025-08-22T09:13:16Z"
},
"product": "kms",
"time": 1755854045000,
"level": "CRITICAL",
"regionId": "cn-chengdu",
"groupId": "0",
"name": "Secret:RotateSecret:Failure"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119285******60:0d603b4a-****71:175***07 |
secretName | Secret name | acs/ecs/secret_rotator |
secretType | Secret type: Rds, Redis, RAMCredentials, ECS, or PolarDB | ECS |
secretSubType | Secret subtype, determined by secretType: <br>- Rds → RdsSingleUser, RdsDoubleUsers <br>- Redis → RedisDoubleUsers <br>- RAMCredentials → RamUserAccessKey <br>- ECS → ECSLoginPassword, ECSLoginSSHKey <br>- PolarDB → PolarDBDoubleUsers | ECSLoginPassword |
rotationEntityArn | ARN of the resource for which rotation was attempted | acs:kms:cn-hangzhou:119285******60:key/0d603b4a-******71be |
rotationStatus | Rotation configuration status: Enabled, Disabled, or Invalid | Enabled |
failureInfo | Rotation failure details: errorCode and errorMessage | {"errorCode": "RotateError", "errorMessage": "..."} |
failureTime | Time the rotation failed | 2025-08-22T09:13:16Z |
Managed secret rotation succeeded
This event fires when Secrets Manager successfully completes an automatic secret rotation.
{
"id": "21c9b9e0-********f3e678",
"status": "normal",
"instanceName": "acs/ram/user/secrettest",
"resourceId": "acs:kms:cn-shanghai:119285********60:secret/acs/ram/user/secrettest",
"content": {
"eventId": "119285********60:acs/ram/user/secrettest:17******59",
"secretName": "acs/ram/user/secrettest",
"secretType": "RAMCredentials",
"rotationEntityArn": "acs:kms:cn-shanghai:119285********60:secret/acs/ram/user/secrettest",
"rotationStatus": "Enabled",
"secretSubType": "RamUserAccessKey",
"successTime": "2025-08-20T09:37:19Z",
"message": ""
},
"product": "kms",
"time": 1755855610000,
"level": "INFO",
"regionId": "cn-shanghai",
"groupId": "0",
"name": "Secret:RotateSecret:Success"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119285******60:acs/ram/user/secrettest:17****59 |
secretName | Secret name | acs/ram/user/secrettest |
secretType | Secret type: Rds, Redis, RAMCredentials, ECS, or PolarDB | RAMCredentials |
secretSubType | Secret subtype, determined by secretType (see values in Managed secret rotation failed) | RamUserAccessKey |
rotationEntityArn | ARN of the rotated resource | acs:kms:cn-shanghai:119285********60:secret/acs/ram/user/secrettest |
rotationStatus | Rotation configuration status: Enabled, Disabled, or Invalid | Enabled |
successTime | Time the rotation completed successfully | 2025-08-20T09:37:19Z |
Key sync failed
This event fires when a key fails to sync from the primary instance to the replica instance during cross-region synchronization. Check errorCode for the failure reason and verify network connectivity and permissions between instances.
{
"product": "kms",
"resourceId": "acs:kms:cn-hangzhou:119285********60:key/<resource-id>",
"level": "CRITICAL",
"instanceName": "instanceName",
"regionId": "cn-hangzhou",
"name": "Instance:KeySync:Failure",
"content": {
"eventId": "119285********60:8071aa27-********87",
"syncTaskId": "8071aa27-********0fc87",
"masterInstanceId": "kst-ph********z6",
"shadowInstanceId": "kst-ps********qq",
"syncStatus": "SyncFailure",
"errorCode": "",
"resourceId": "key-ph********4d",
"resourceType": "KEY",
"eventTime": "2024-03-22T07:41:17Z"
},
"status": "Normal"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119285******60:8071aa27-******87 |
syncTaskId | Sync task ID | 8071aa27-********0fc87 |
masterInstanceId | Primary instance ID (sync source) | kst-ph********z6 |
shadowInstanceId | Replica instance ID (sync destination) | kst-ps********qq |
syncStatus | Sync result: SyncFailure | SyncFailure |
errorCode | Error code, if available | "" |
resourceId | Resource ID of the key that failed to sync | key-ph********04d |
resourceType | Resource type. Only KEY is supported. | KEY |
eventTime | Time the sync was attempted | 2024-03-22T07:41:17Z |
Key sync succeeded
This event fires when a key successfully syncs from the primary instance to the replica instance.
{
"product": "kms",
"resourceId": "acs:kms:cn-hangzhou:119285********60:key/<resource-id>",
"level": "INFO",
"instanceName": "instanceName",
"regionId": "cn-hangzhou",
"name": "Instance:KeySync:Success",
"content": {
"eventId": "119285********60:8071aa27-********0fc87",
"syncTaskId": "8071aa27-********420fc87",
"masterInstanceId": "kst-ph********z6",
"shadowInstanceId": "kst-ps********qq",
"syncStatus": "SyncSuccess",
"errorCode": "",
"resourceId": "key-ph********04d",
"resourceType": "KEY",
"eventTime": "2024-03-22T07:41:17Z"
},
"status": "Normal"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119285******60:8071aa27-******0fc87 |
syncTaskId | Sync task ID | 8071aa27-********420fc87 |
masterInstanceId | Primary instance ID (sync source) | kst-ph********z6 |
shadowInstanceId | Replica instance ID (sync destination) | kst-ps********qq |
syncStatus | Sync result: SyncSuccess | SyncSuccess |
errorCode | Error code, if any | "" |
resourceId | Resource ID of the synced key | key-ph********04d |
resourceType | Resource type. Only KEY is supported. | KEY |
eventTime | Time the sync completed | 2024-03-22T07:41:17Z |
ClientKey expiration reminder
This event fires 180, 90, 30, and 7 days before a ClientKey expires. Use daysToExpire to track how much time remains and renew the ClientKey before expiration to avoid application access failures.
{
"product": "kms",
"resourceId": "<aap_arn>",
"level": "CRITICAL",
"instanceName": "instanceName",
"regionId": "cn-hangzhou",
"name": "Instance:ClientKey:ExpireReminder",
"content": {
"clientKeyName": "clientKeyName",
"eventId": "eventId",
"dateOfExpiration": "2024-09-30T18:23:46Z",
"daysToExpire": "180",
"affectedKmsInstanceId": "kst-exxxx"
},
"status": "Normal"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119285******60:0d603b4a-****71:175***07 |
clientKeyName | Application access point (AAP) name | kms-client |
dateOfExpiration | ClientKey expiration time | 2024-09-30T18:23:46Z |
daysToExpire | Days remaining until expiration | 180 |
affectedKmsInstanceId | KMS instance ID associated with this ClientKey | kst-hzz********bxt |
Access management usage has reached 70%
This event fires when access management usage on a KMS instance reaches 70% of its quota. If the quota is fully consumed, you cannot create new access management policies.
{
"product": "kms",
"resourceId": "acs:kms:cn-shanghai:1192******18460:instance/<resource-id>",
"level": "INFO",
"instanceName": "instanceName",
"regionId": "cn-hangzhou",
"name": "Instance:Quota:AccessManagement:70%",
"content": {
"eventId": "119***d:2",
"quota": "***",
"kmsInstanceId": "kst***em7",
"used": "***"
},
"status": "normal"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119***d:2 |
kmsInstanceId | KMS instance ID | kst***pn8 |
quota | Total access management policy quota | 1000 |
used | Current number of access management policies in use | 700 |
Access management usage has reached 90%
This event fires when access management usage on a KMS instance reaches 90% of its quota. At this threshold, you are close to being unable to create new access management policies.
{
"product": "kms",
"resourceId": "acs:kms:ap-southeast-6:1192******18460:instance/<resource-id>",
"level": "WARN",
"instanceName": "instanceName",
"regionId": "cn-hangzhou",
"name": "Instance:Quota:AccessManagement:90%",
"content": {
"eventId": "119***d:1",
"quota": "***",
"kmsInstanceId": "kst***rz5",
"used": "***"
},
"status": "normal"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119***d:2 |
kmsInstanceId | KMS instance ID | kst***pn8 |
quota | Total access management policy quota | 1000 |
used | Current number of access management policies in use | 900 |
Key usage has reached 70%
This event fires when key usage on a KMS instance reaches 70% of its quota. If the quota is fully consumed, you cannot create new keys.
{
"product": "kms",
"resourceId": "acs:kms:cn-shanghai:1192******18460:instance/<resource-id>",
"level": "INFO",
"instanceName": "instanceName",
"regionId": "cn-hangzhou",
"name": "Instance:Quota:Key:70%",
"content": {
"eventId": "119***774",
"quota": "10***",
"kmsInstanceId": "kst***urs",
"used": "***"
},
"status": "normal"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119***d:2 |
kmsInstanceId | KMS instance ID | kst***pn8 |
quota | Total key quota | 1000 |
used | Current number of keys in use | 700 |
Key usage has reached 90%
This event fires when key usage on a KMS instance reaches 90% of its quota. At this threshold, you are close to being unable to create new keys.
{
"product": "kms",
"resourceId": "acs:kms:cn-shanghai:1192******18460:instance/<resource-id>",
"level": "INFO",
"instanceName": "instanceName",
"regionId": "cn-hangzhou",
"name": "Instance:Quota:Key:90%",
"content": {
"eventId": "119***774",
"quota": "10***",
"kmsInstanceId": "kst***urs",
"used": "***"
},
"status": "normal"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119***d:2 |
kmsInstanceId | KMS instance ID | kst***pn8 |
quota | Total key quota | 1000 |
used | Current number of keys in use | 900 |
Log analysis log volume has reached 70%
This event fires when log analysis log volume on a KMS instance reaches 70% of its quota. If the quota is fully consumed, new logs cannot be written.
{
"product": "kms",
"resourceId": "key-phzz******jro04d",
"level": "INFO",
"instanceName": "instanceName",
"regionId": "cn-hangzhou",
"name": "Instance:Quota:Log:70%",
"content": {
"eventId": "eventId",
"quota": "1000",
"kmsInstanceId": "key-phzz******jro04d",
"used": "700"
},
"status": "Normal"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119***d |
kmsInstanceId | KMS instance ID | kst***pn8 |
quota | Total log analysis capacity (GB) | 1000 |
used | Used log analysis capacity (GB) | 700 |
Log analysis log volume has reached 90%
This event fires when log analysis log volume on a KMS instance reaches 90% of its quota. At this threshold, you are close to being unable to write new logs.
{
"product": "kms",
"resourceId": "key-phzz******jro04d",
"level": "INFO",
"instanceName": "instanceName",
"regionId": "cn-hangzhou",
"name": "Instance:Quota:Log:90%",
"content": {
"eventId": "eventId",
"quota": "1000",
"kmsInstanceId": "key-phzz******jro04d",
"used": "900"
},
"status": "Normal"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119***d |
kmsInstanceId | KMS instance ID | kst***pn8 |
quota | Total log analysis capacity (GB) | 1000 |
used | Used log analysis capacity (GB) | 900 |
Secret usage has reached 70%
This event fires when secret usage on a KMS instance reaches 70% of its quota. If the quota is fully consumed, you cannot create new secrets.
{
"product": "kms",
"resourceId": "key-phzz******jro04d",
"level": "INFO",
"instanceName": "instanceName",
"regionId": "cn-hangzhou",
"name": "Instance:Quota:Secret:70%",
"content": {
"eventId": "eventId",
"quota": "1000",
"kmsInstanceId": "key-phzz******jro04d",
"used": "700"
},
"status": "Normal"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119***d |
kmsInstanceId | KMS instance ID | kst***pn8 |
quota | Total secret quota | 1000 |
used | Current number of secrets in use | 700 |
Secret usage has reached 90%
This event fires when secret usage on a KMS instance reaches 90% of its quota. At this threshold, you are close to being unable to create new secrets.
{
"product": "kms",
"resourceId": "key-phzz******jro04d",
"level": "INFO",
"instanceName": "instanceName",
"regionId": "cn-hangzhou",
"name": "Instance:Quota:Secret:70%",
"content": {
"eventId": "eventId",
"quota": "1000",
"kmsInstanceId": "key-phzz******jro04d",
"used": "900"
},
"status": "Normal"
}content field descriptions:
| Field | Description | Example |
|---|---|---|
eventId | Event ID | 119***d |
kmsInstanceId | KMS instance ID | kst***pn8 |
quota | Total secret quota | 1000 |
used | Current number of secrets in use | 900 |