Key Management Service (KMS) integrates with ActionTrail and Simple Log Service (SLS) to record events generated during key and secret use. Use these records for troubleshooting and security monitoring.
Choose a query method
KMS events fall into two categories:
Management operations: create or delete keys, create or delete secrets, modify key aliases
Service-related operations: cryptographic operations, retrieve secret values
The right query method depends on the resource type, operation type, and where the resource is hosted.
Keys and secrets in KMS instances
| Resource | Operation | Query method |
|---|---|---|
| Key | Management operations | ActionTrail |
| Key | Cryptographic operations — server-side encryption in Alibaba Cloud services | ActionTrail |
| Key | Cryptographic operations — data encryption in self-managed applications | Simple Log Service |
| Secret | Management operations | ActionTrail |
| Secret | Retrieve secret values via KMS endpoint | ActionTrail or Simple Log Service |
| Secret | Retrieve secret values via KMS instance endpoint | Simple Log Service |
Keys and secrets outside KMS instances
Default keys are outside KMS instances. Secrets outside KMS instances are secrets created using the old version of KMS without a purchased KMS instance.
| Resource | Operation | Query method |
|---|---|---|
| Key | Management operations | ActionTrail |
| Key | Cryptographic operations | ActionTrail |
| Secret | Management operations | ActionTrail |
| Secret | Retrieve secret values | ActionTrail or Simple Log Service (via KMS endpoint only) |
Key state support
| Query method | Supported key states |
|---|---|
| ActionTrail | All states (enabled, disabled, Pending Deletion) |
| Simple Log Service | Enabled only |
Use ActionTrail
ActionTrail records KMS management and service operations as queryable events. For the full list of supported events, see Audit events of KMS.
ActionTrail provides two query modes:
| Mode | Retention | Cost | Notes |
|---|---|---|---|
| Event Query | 90 days | Free | Available by default |
| Advanced Event Query | Depends on SLS | Billed through SLS | Requires creating a trail and delivering events to SLS first |
For SLS pricing, see Simple Log Service billing.
Query events using Event Query
Log on to the ActionTrail console.
In the left-side navigation pane, choose Events > Event Query.
Select Resource Name, enter the ID of the key or secret, select a time range, and then click the
 icon.
icon. 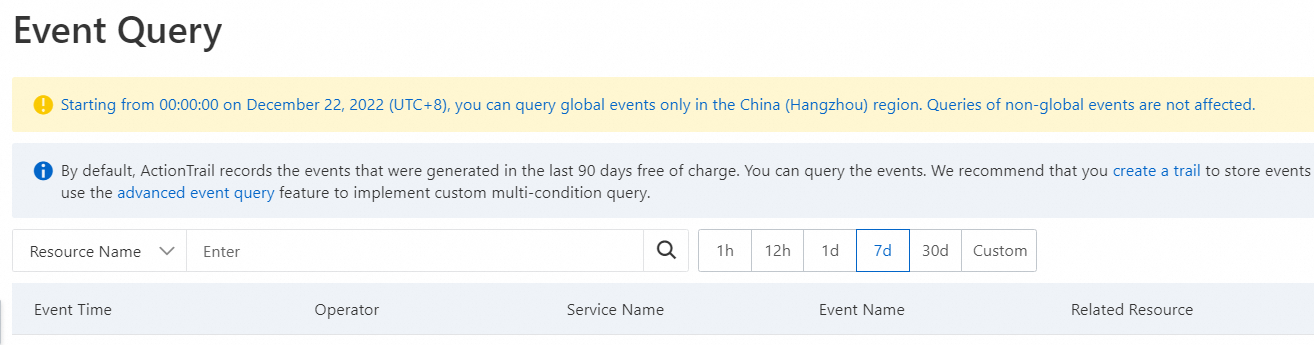
Find the event and click View Event Details in the Actions column.
Query events using Advanced Event Query
Before using Advanced Event Query, create a trail and configure event delivery to Simple Log Service. For setup instructions, see Single-account trail overview and Overview.
Note: Advanced Event Query covers only events generated after the trail is created. To query events from up to 90 days before the trail was created, create a data backfill task.
Log on to the ActionTrail console.
In the left-side navigation pane, choose Event > Advanced Event Query.
Select a trail name, turn off Simple Mode in the upper-right corner, and enter a query statement.
The following examples cover common audit scenarios. Replace the placeholder values with your actual resource IDs.
Query events for a specific key:
* AND (event.serviceName: "Kms") AND (event.eventRW: "Read") AND "key-szz63dc8c429ermur****"Replace
key-szz63dc8c429ermur****with the key ID.Query events for a disabled key:
* AND (event.serviceName: "Kms") AND (event.errorCode:"Rejected.Disabled")Query events for a key in the Pending Deletion state:
* AND (event.serviceName: "Kms") AND (event.errorCode:"Rejected.PendingDeletion")Query events for keys in an expired instance:
* AND (event.serviceName: "Kms") AND (event.errorCode:"Rejected.Unavailable")Query events for a specific secret:
* AND (event.serviceName: "Kms") AND (event.eventName: "GetSecretValue") AND "SecretName"Replace
SecretNamewith the secret name.
Note: For a complete list of error codes related to key states, see Common error codes.
Find the event and click View Event Details in the Actions column.
Use Simple Log Service
Simple Log Service for KMS provides a built-in log search interface directly in the KMS console.
Log on to the KMS console. In the top navigation bar, select the region. In the left-side navigation pane, choose Security Operations > Simple Log Service for KMS.
On the Simple Log Service for KMS page, select the instance ID from the Instance ID drop-down list and enter the key or secret ID in the Key/Secret ID field.
Specify a time range and click Search & Analyze.
Note:
Logs are retained for 180 days. Logs older than 180 days are deleted. Queries are limited to the previous 180 days.
Query results may include logs generated up to 1 minute before or after the specified time range.
No additional fees apply for query and analysis operations.