Static ECS logon credentials — passwords and SSH keys set once and changed only when someone remembers to update them — stay valid even after a breach goes undetected. Dynamic ECS secrets address this by having Secrets Manager periodically rotate ECS logon credentials to strong passwords and SSH keys automatically, so a leaked credential expires at the next rotation cycle without any manual effort.
How it works
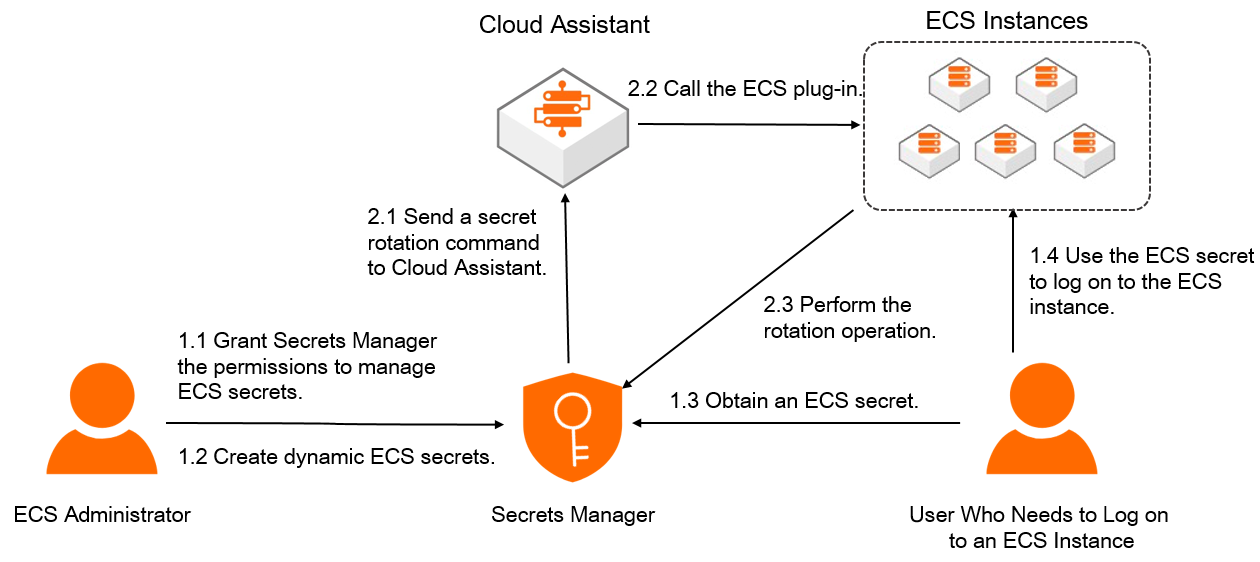
When a rotation is triggered — either on a schedule or on demand — Secrets Manager sends a rotation command to Cloud Assistant. Cloud Assistant then calls the plug-in installed on the ECS instance to apply the new credential. After rotation completes, use the new secret to log on to the instance.
Security mechanisms
Secrets Manager provides centralized, secure management of ECS secrets through four mechanisms:
Encryption protection: Dedicated hardware encrypts ECS secrets to protect them at rest.
Permission management: Fine-grained permission management based on Resource Access Management (RAM) reduces the risk of secret leaks.
Manual rotation: When a secret is leaked, immediately rotate it to block intrusions.
Periodic rotation: ECS logon credentials rotate on a schedule to strong passwords and SSH keys — even if a leak goes undetected, the exposed credential expires at the next rotation.
Get started
To use dynamic ECS secrets, grant Secrets Manager the permissions to manage passwords and SSH keys for your ECS instances. Once permissions are in place, Secrets Manager manages the logon credentials on your behalf.
Log on to the ECS instance using the current secret from Secrets Manager.
Limitations
| Instance type | Supported credential types |
|---|---|
| Linux | Passwords and SSH keys |
| Windows | Passwords only |