Resource Access Management (RAM) controls who can call KMS API operations and which resources they can access. To grant a RAM user access to KMS, create a custom RAM policy that specifies the exact operations and resources allowed, then attach that policy to the user.
RAM provides two editing modes: visual editing and document editing. For KMS, use the document editing mode. Visual editing only allows you to select all KMS resources and all operations, which does not support least-privilege configuration.
Prerequisites
Before you begin, ensure that you have:
An Alibaba Cloud account with administrator access to the RAM console
A RAM user to grant permissions to
Policy structure
A KMS RAM policy statement contains up to four elements:
| Element | Required | Description |
|---|---|---|
| Effect | Yes | Allow or Deny |
| Action | Yes | One or more KMS API operations in kms:<api-name> format |
| Resource | Yes | The Alibaba Cloud Resource Name (ARN) of the target resource |
| Condition | No | Additional constraints such as time-based restrictions |
The Appendix below lists all supported actions, resource ARN formats, and condition keys.
Grant a RAM user access to KMS
Step 1: Create a custom policy
Log on to the RAM console using your Alibaba Cloud account.
In the left-side navigation pane, choose Permissions > Policies.
On the Policies page, click Create Policy.
On the Create Policy page, click the JSON tab.
Replace the default policy content with your custom policy document. The following example grants a RAM user permission to encrypt and decrypt using a specific key, without the ability to manage or delete it:
{ "Version": "1", "Statement": [ { "Effect": "Allow", "Action": [ "kms:Encrypt", // encrypt data using the key "kms:Decrypt", // decrypt data using the key "kms:GenerateDataKey" // generate a data key for envelope encryption ], "Resource": "acs:kms:${region}:${account}:key/${key-id}" } ] }Replace
${region},${account}, and${key-id}with your actual values. To target all keys in an account, useacs:kms:*:${account}:key/*.Click Optimize to validate and format the policy document (optional).
Click OK.
Enter a policy name and description, then click OK.
Step 2: Attach the policy to a RAM user
In the left-side navigation pane, choose Identities > Users.
On the Users page, find the target RAM user and click Add Permissions in the Actions column.
In the Grant Permission panel, configure the following parameters and click Grant Permissions.
Parameter Description Resource Scope Select Account. KMS does not support the resource group feature. Principal The RAM user to grant permissions to. Defaults to the user you selected; change as needed. Policy Select the custom policy you created in step 1.
Appendix: Supported resources, actions, and conditions
Resource
KMS defines six resource types. Configure the Resource element in a RAM policy using the ARN of the target resource.
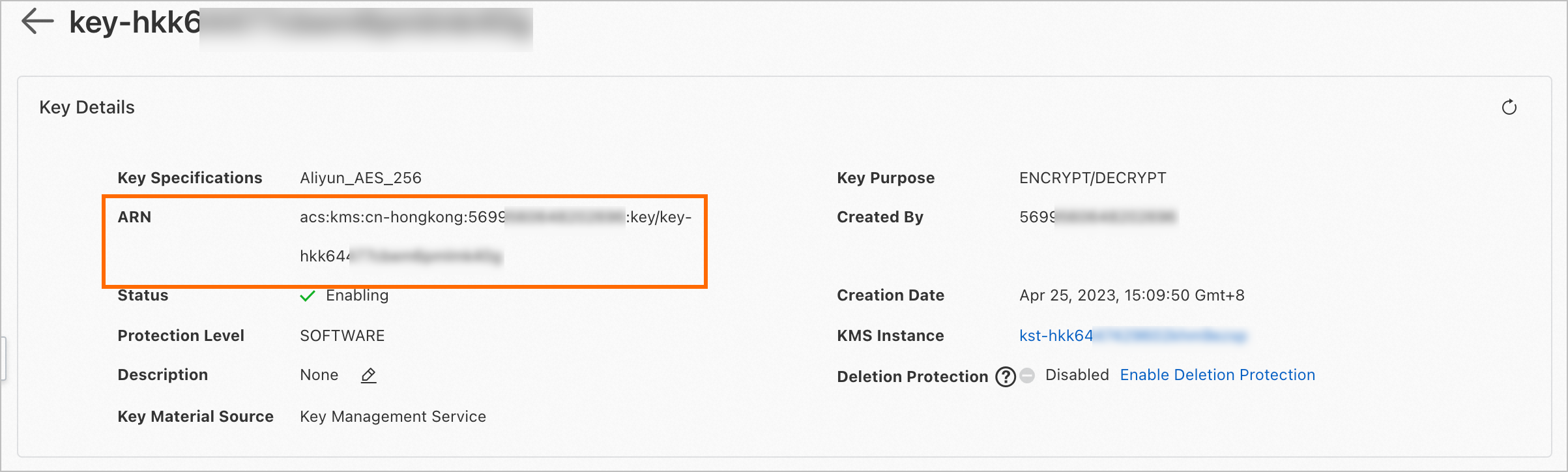
To find a key's ARN:
Log on to the KMS console. In the top navigation bar, select a region. In the left-side navigation pane, choose Resource > Keys.
On the Keys tab, find the key and click Details in the Actions column. The ARN appears on the details page.
Replace${region}and${account}with your actual region and Alibaba Cloud account ID.${region}supports the asterisk (*) wildcard to target all supported regions.
| Resource type | ARN |
|---|---|
| Key container | acs:kms:${region}:${account}:key |
| Secret container | acs:kms:${region}:${account}:secret |
| Alias container | acs:kms:${region}:${account}:alias |
| Key | acs:kms:${region}:${account}:key/${key-id} |
| Secret | acs:kms:${region}:${account}:secret/${secret-name} |
| Alias | acs:kms:${region}:${account}:alias/${alias-name} |
Wildcard examples
For keys:
acs:kms:${region}:${account}:key/*— all keys in a specific region within an accountacs:kms:*:${account}:key/*— all keys in all regions within an account
For secrets:
acs:kms:${region}:${account}:secret/*— all secrets in a specific region within an accountacs:kms:${region}:${account}:secret/prefix*— all secrets whose names start withprefix
Action
KMS defines an action for each API operation that requires access control. Actions follow the kms:<api-name> format.
The DescribeRegions operation does not require access control. It can be called by any Alibaba Cloud account, RAM user, or RAM role after passing RAM authentication.Key-related API operations
| Operation | Action | Resource type | ARN format |
|---|---|---|---|
| ListKeys | kms:ListKeys | Key container | acs:kms:${region}:${account}:key |
| CreateKey | kms:CreateKey | Key container | acs:kms:${region}:${account}:key |
| DescribeKey | kms:DescribeKey | Key | acs:kms:${region}:${account}:key/${key-id} |
| UpdateKeyDescription | kms:UpdateKeyDescription | Key | acs:kms:${region}:${account}:key/${key-id} |
| EnableKey | kms:EnableKey | Key | acs:kms:${region}:${account}:key/${key-id} |
| DisableKey | kms:DisableKey | Key | acs:kms:${region}:${account}:key/${key-id} |
| ScheduleKeyDeletion | kms:ScheduleKeyDeletion | Key | acs:kms:${region}:${account}:key/${key-id} |
| CancelKeyDeletion | kms:CancelKeyDeletion | Key | acs:kms:${region}:${account}:key/${key-id} |
| GetParametersForImport | kms:GetParametersForImport | Key | acs:kms:${region}:${account}:key/${key-id} |
| ImportKeyMaterial | kms:ImportKeyMaterial | Key | acs:kms:${region}:${account}:key/${key-id} |
| DeleteKeyMaterial | kms:DeleteKeyMaterial | Key | acs:kms:${region}:${account}:key/${key-id} |
| ListAliasesByKeyId | kms:ListAliasesByKeyId | Key | acs:kms:${region}:${account}:key/${key-id} |
| CreateKeyVersion | kms:CreateKeyVersion | Key | acs:kms:${region}:${account}:key/${key-id} |
| DescribeKeyVersion | kms:DescribeKeyVersion | Key | acs:kms:${region}:${account}:key/${key-id} |
| ListKeyVersions | kms:ListKeyVersions | Key | acs:kms:${region}:${account}:key/${key-id} |
| UpdateRotationPolicy | kms:UpdateRotationPolicy | Key | acs:kms:${region}:${account}:key/${key-id} |
| Encrypt | kms:Encrypt | Key | acs:kms:${region}:${account}:key/${key-id} |
| Decrypt | kms:Decrypt | Key | acs:kms:${region}:${account}:key/${key-id} |
| ReEncrypt | kms:ReEncryptFrom (source key) and kms:ReEncryptTo (destination key) | Key | acs:kms:${region}:${account}:key/${key-id} |
| GenerateDataKey | kms:GenerateDataKey | Key | acs:kms:${region}:${account}:key/${key-id} |
| GenerateDataKeyWithoutPlaintext | kms:GenerateDataKeyWithoutPlaintext | Key | acs:kms:${region}:${account}:key/${key-id} |
| ExportDataKey | kms:ExportDataKey | Key | acs:kms:${region}:${account}:key/${key-id} |
| GenerateAndExportDataKey | kms:GenerateAndExportDataKey | Key | acs:kms:${region}:${account}:key/${key-id} |
| AsymmetricSign | kms:AsymmetricSign | Key | acs:kms:${region}:${account}:key/${key-id} |
| AsymmetricVerify | kms:AsymmetricVerify | Key | acs:kms:${region}:${account}:key/${key-id} |
| AsymmetricEncrypt | kms:AsymmetricEncrypt | Key | acs:kms:${region}:${account}:key/${key-id} |
| AsymmetricDecrypt | kms:AsymmetricDecrypt | Key | acs:kms:${region}:${account}:key/${key-id} |
| GetPublicKey | kms:GetPublicKey | Key | acs:kms:${region}:${account}:key/${key-id} |
| ListAliases | kms:ListAliases | Alias container | acs:kms:${region}:${account}:alias |
| CreateAlias | kms:CreateAlias | Alias and key | Alias: acs:kms:${region}:${account}:alias/${alias-name} and Key: acs:kms:${region}:${account}:key/${key-id} |
| UpdateAlias | kms:UpdateAlias | Alias and key | Alias: acs:kms:${region}:${account}:alias/${alias-name} and Key: acs:kms:${region}:${account}:key/${key-id} |
| DeleteAlias | kms:DeleteAlias | Alias and key | Alias: acs:kms:${region}:${account}:alias/${alias-name} and Key: acs:kms:${region}:${account}:key/${key-id} |
Secret-related API operations
| Operation | Action | Resource type | ARN |
|---|---|---|---|
| CreateSecret | kms:CreateSecret | Secret container | acs:kms:${region}:${account}:secret |
| ListSecrets | kms:ListSecrets | Secret container | acs:kms:${region}:${account}:secret |
| DescribeSecret | kms:DescribeSecret | Secret | acs:kms:${region}:${account}:secret/${secret-name} |
| DeleteSecret | kms:DeleteSecret | Secret | acs:kms:${region}:${account}:secret/${secret-name} |
| UpdateSecret | kms:UpdateSecret | Secret | acs:kms:${region}:${account}:secret/${secret-name} |
| RestoreSecret | kms:RestoreSecret | Secret | acs:kms:${region}:${account}:secret/${secret-name} |
| GetSecretValue | kms:GetSecretValue (always) and kms:Decrypt (only when a self-managed key is used as the encryption key) | Secret | acs:kms:${region}:${account}:secret/${secret-name} |
| PutSecretValue | kms:PutSecretValue (always) and kms:GenerateDataKey (only when a self-managed key is used as the encryption key) | Secret | acs:kms:${region}:${account}:secret/${secret-name} |
| ListSecretVersionIds | kms:ListSecretVersionIds | Secret | acs:kms:${region}:${account}:secret/${secret-name} |
| UpdateSecretVersionStage | kms:UpdateSecretVersionStage | Secret | acs:kms:${region}:${account}:secret/${secret-name} |
| GetRandomPassword | kms:GetRandomPassword | None | None |
Tag-related API operations
| Operation | Action | Resource type | ARN |
|---|---|---|---|
| ListResourceTags | kms:ListResourceTags | Key or secret | Key: acs:kms:${region}:${account}:key/${key-id} or Secret: acs:kms:${region}:${account}:secret/${secret-name} |
| UntagResource | kms:UntagResource | Key or secret | Key: acs:kms:${region}:${account}:key/${key-id} or Secret: acs:kms:${region}:${account}:secret/${secret-name} |
| TagResource | kms:TagResource | Key or secret | Key: acs:kms:${region}:${account}:key/${key-id} or Secret: acs:kms:${region}:${account}:secret/${secret-name} |
Condition
The Condition element is optional. Add condition keys to a RAM policy to enforce additional constraints — RAM authentication succeeds only when all specified conditions are met.
Two types of condition keys are supported:
Common condition keys in
acs:<condition-key>format — for example, useacs:CurrentTimeto restrict a policy to a specific time window. For the full list, see Policy elements.KMS-specific condition keys in
kms:<condition-key>format — for the full list, see Condition keys.
For more information about RAM policy syntax and structure, see Policy structure and syntax.