When you create an Intelligent Media Management (IMM) project, you must specify a service role for the project. This allows the IMM service to assume the role and access your authorized cloud resources, such as Object Storage Service (OSS). This topic describes how to configure a service role and grant permissions.
When you create a service role, create a project, or change the service role of a project, you must have all the permissions that are granted to that role. Otherwise, the operation fails because of insufficient permissions. Proceed with caution.
Create a service role and grant permissions
Authorize the default service role
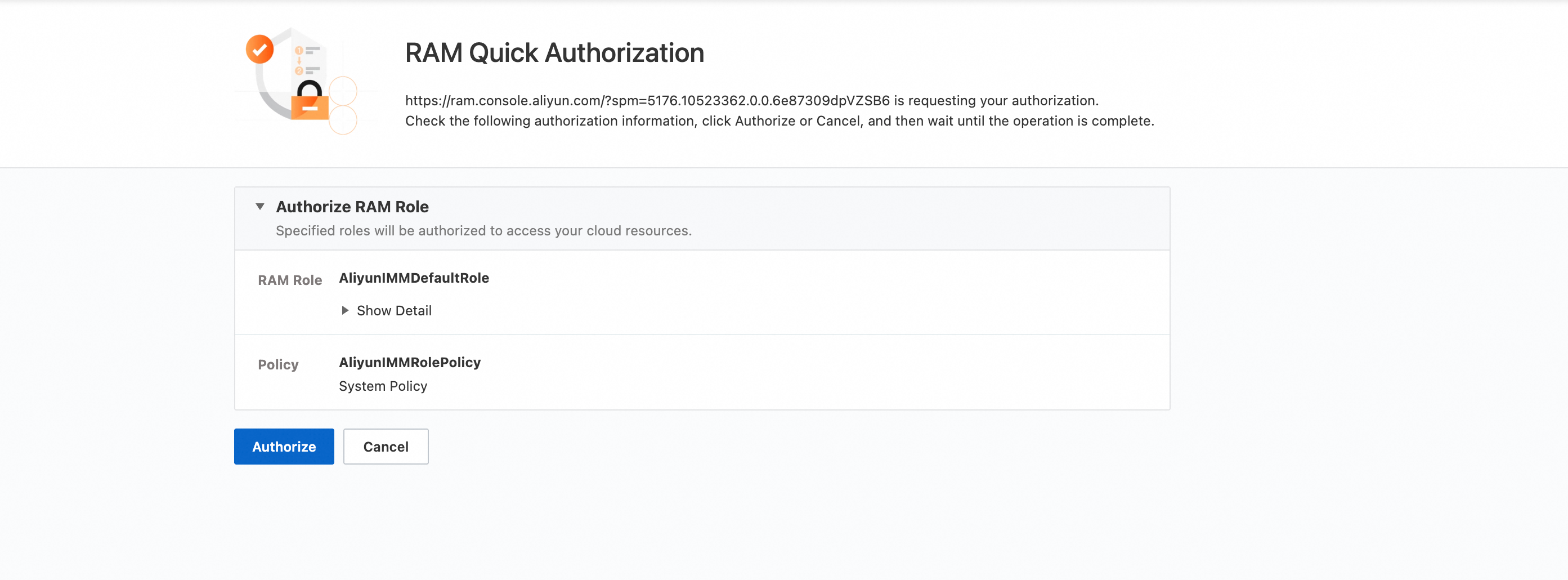
When you create a project for the first time, authorize access to cloud resources as prompted.
On the Cloud Resource Access Authorization page, view the information about the default authorization role AliyunIMMDefaultRole and click Authorize.
After the authorization role is created, you can use the Resource Access Management (RAM) console to configure fine-grained permissions.
Note that the AliyunIMMDefaultRole service role has high-level access permissions to OSS. If a RAM user in your Alibaba Cloud account has IMM permissions such as CreateProject / UpdateProject, that user can attach the AliyunIMMDefaultRole and use the metadata indexing feature to list or analyze your OSS files. To precisely control these permissions, see Create a custom service role.
Create a custom service role
You can use the RAM console to configure a service role and grant permissions. For more information, see Create a service-linked role.
Set Pricipal Type to Cloud Service, select Intelligent Media Management for Pricipal Name.

Click the OK button and enter a Role Name to create the custom service role.
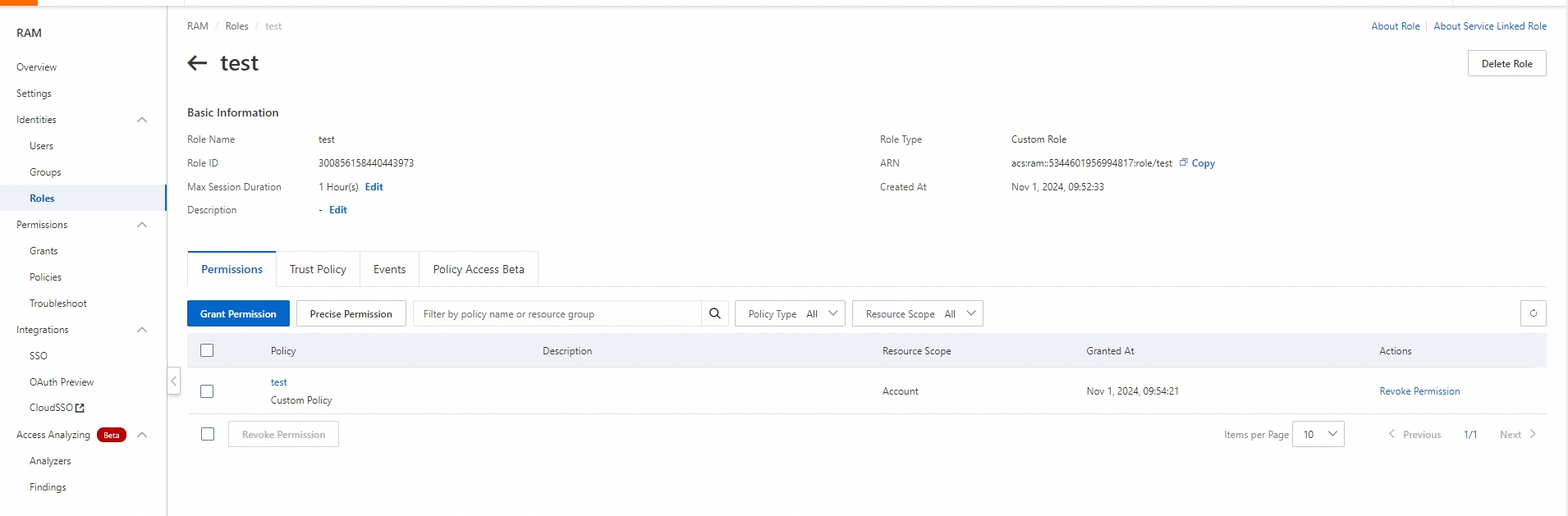
After the role is created in the RAM console, it does not have any permissions. You must grant permissions to this RAM role. At a minimum, grant the required permissions for OSS and Message Service (MNS).
You can create a policy in the RAM console. Use the JSON to create the policy.
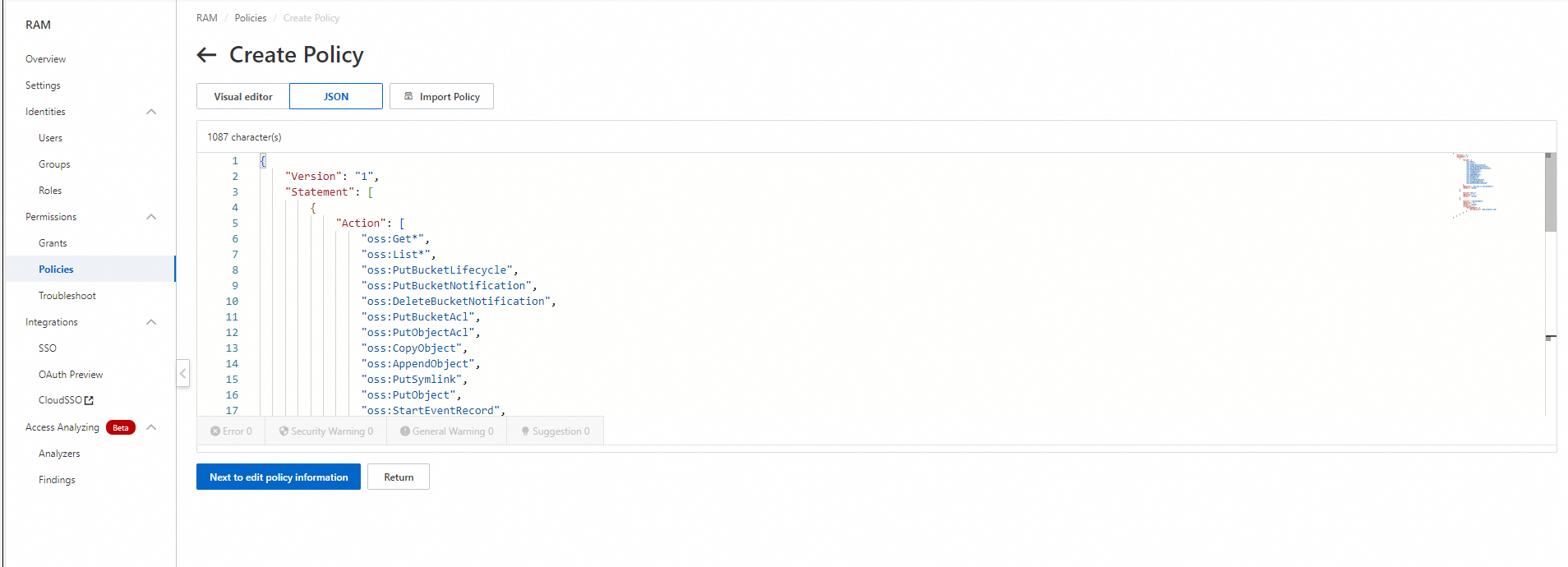
The following policy grants permissions only on the OSS bucket named "my-bucket". When you copy and use this policy, replace the bucket name with your actual bucket name.
{ "Version": "1", "Statement": [ { "Action": [ "oss:Get*", "oss:List*", "oss:PutBucketLifecycle", "oss:PutBucketNotification", "oss:DeleteBucketNotification", "oss:PutBucketAcl", "oss:PutObjectAcl", "oss:CopyObject", "oss:AppendObject", "oss:PutSymlink", "oss:PutObject", "oss:StartEventRecord", "oss:StopEventRecord", "oss:GetEventRecordStatus" ], "Resource": "acs:oss:*:*:my-bucket/*", "Effect": "Allow" }, { "Action":"mns:*", "Resource": "*", "Effect": "Allow" }, { "Action": "ram:PassRole", "Resource": "*", "Effect": "Allow", "Condition": { "StringEquals": { "acs:Service": "imm.aliyuncs.com" } } } ] }Attach the created policy to the service role. For more information, see Grant permissions to a RAM role.
Use the service role
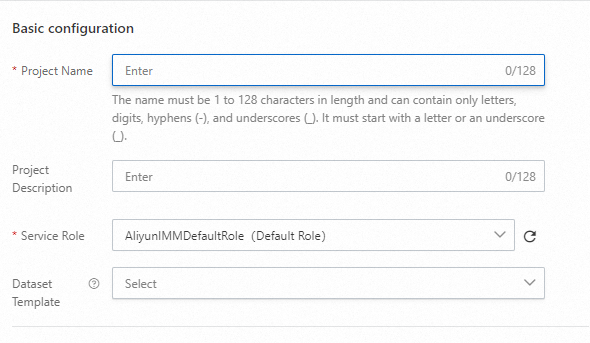
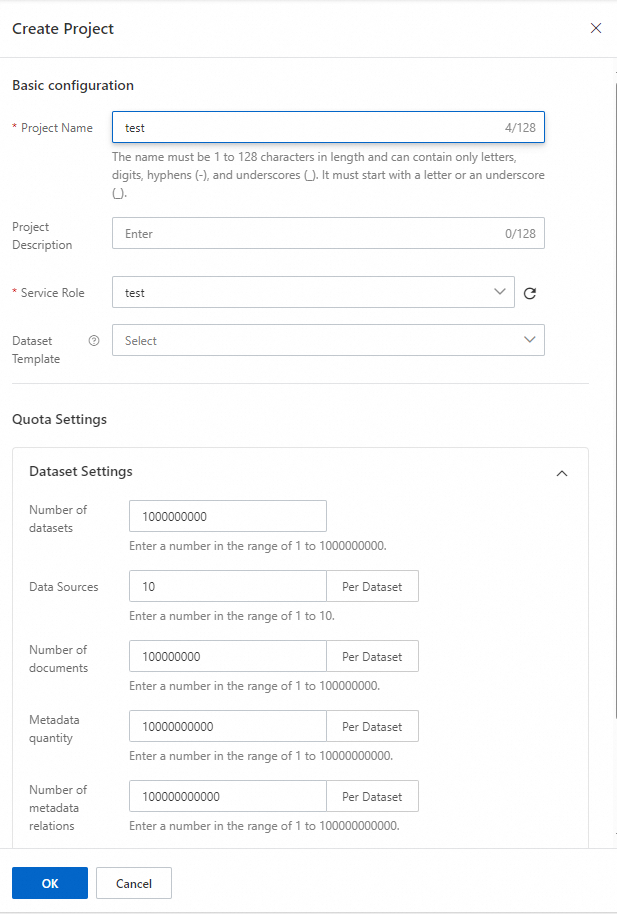
After the service role is created, click the refresh icon next to the service role input box. Then, you can select the new service role to create an Intelligent Media Management project, as shown in the following figure.
(Optional) Modify the permissions of the service role
You can modify the permissions of the role in the RAM console. For more information, see Grant permissions to a RAM role.
When you modify the permissions of the service role, ensure that you grant at least the permissions required for OSS and MNS based on your use case. Otherwise, API calls may fail because of insufficient permissions.