Agent ID Guard is an identity and access management (IAM) service purpose-built for AI agents. It provides centralized identity registration, dynamic credential management, access control, and audit logging to help you secure agent interactions across your enterprise environment.
Background
As AI agents move from prototypes to production workloads, they introduce a new category of non-human identities (NHIs) that existing IAM solutions were not designed to handle. Unlike traditional applications with predictable access patterns, agents operate autonomously, invoke external services, and make chained API calls that span multiple systems. Cloud-native architectures and microservices compound these challenges by blurring traditional access boundaries.
Without purpose-built identity governance, agent adoption creates three systemic risks:
-
Unmanaged agent sprawl: Organizations lack visibility into how many agents exist, who created them, and what data they access. For example, a team deploys an unregistered data query agent with a code vulnerability that continuously leaks data, but the breach goes undetected until a traffic anomaly alert fires. Security teams have no inventory to trace back to.
-
Privilege escalation: Users gain access to restricted resources through agents with broader permissions than their own roles allow. For example, an employee accesses executive expense records through a reimbursement agent, or an orphaned agent from a departed employee continues to run with full credentials.
-
Credential mismanagement: To simplify configuration, administrators grant agents broad permissions. Developers hard-code API keys and secrets into agent code, making credentials vulnerable to exposure. Without centralized credential governance, rotation and revocation become impractical at scale.
Agent ID Guard addresses these risks by serving as a centralized identity hub and permission authority for all agents in your environment. It covers the full lifecycle of agent identities, from registration through credential management to runtime monitoring.
Core capabilities
Unified identity management
Agent ID Guard provides a dedicated management console where you register and manage all agents. Each agent receives a unique Agent ID that serves as its digital identity across your environment. The Agent ID enables:
-
Identification: Every agent has a traceable identity with a known owner and defined purpose.
-
Access governance: Permissions are defined per Agent ID and enforced consistently.
-
Auditability: All agent activity is linked to a specific Agent ID for investigation and compliance.
Enterprise identity integration
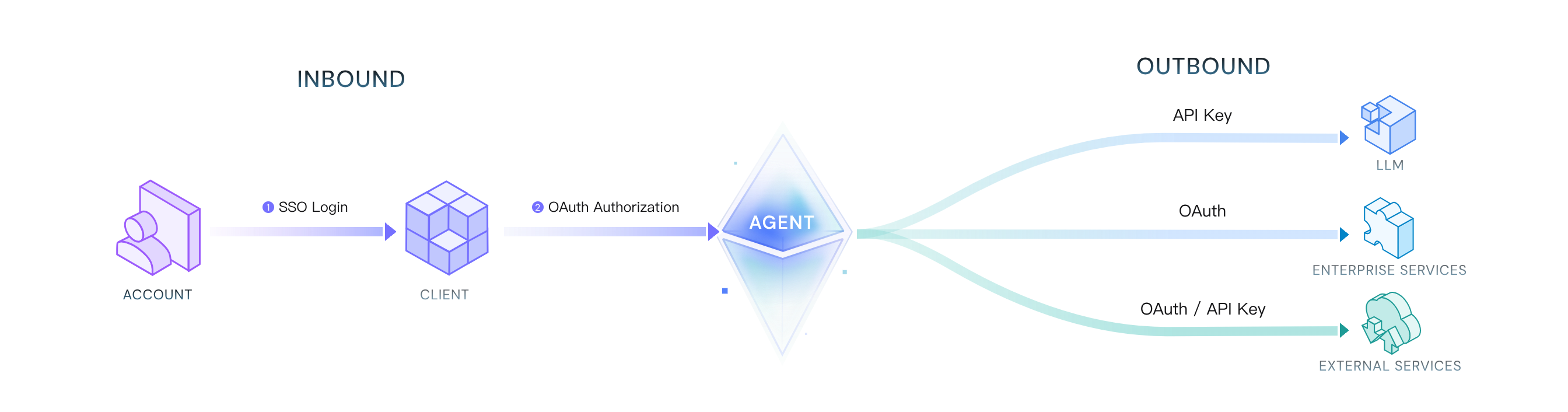
Agent ID Guard integrates with your existing identity providers, including DingTalk, WeCom, Lark, LDAP, and Microsoft Entra ID (Azure AD). This establishes an end-to-end trusted access chain:
User → Client → Agent → Resource
The chain enforces security at each transition:
|
Transition |
Mechanism |
Example |
|
User to Client |
SSO authentication |
User logs in through the corporate IdP. |
|
Client to Agent |
Policy-based access control |
Only HR department members can invoke the onboarding workflow agent. |
|
Agent to Resource |
Least privilege enforcement |
The agent accesses only the downstream resources (LLMs, enterprise services, SaaS) required for its current task. |
|
End-to-end |
OIDC / OAuth 2.0 protocol security |
Token propagation and validation at each step prevent identity spoofing and unauthorized access. |
Dynamic credential management
Agent ID Guard manages the sensitive credentials (API keys, OAuth secrets, tokens) that agents need to access LLMs, third-party SaaS, and internal systems.
-
Encrypted storage: All credentials are encrypted at rest using Key Management Service (KMS).
-
Dynamic delivery: Agents retrieve credentials only when explicitly authorized. Agent code never accesses long-lived raw credentials. At runtime, agents receive only short-lived, scoped temporary tokens through a secure channel.
-
Auditable distribution: All credential distribution is logged and bound to the requesting Agent ID and call context.
End-to-end monitoring and alerting
Agent ID Guard integrates with Simple Log Service (SLS) to provide comprehensive behavior auditing:
|
Log category |
What is recorded |
|
Inbound records |
The user or system that triggers the agent, along with the timestamp and source. |
|
Outbound records |
The downstream services the agent calls, the credentials used, and the operations performed. |
|
Credential audit |
All credential retrieval and usage, associated with the specific Agent ID and call context. |
All events are written to SLS in standardized JSON format. You can search and analyze logs by Agent ID, user identity, timestamp, and resource type.
Architecture
The following diagram shows the business flow of Agent ID Guard, including how users, clients, agents, and downstream resources interact through the identity and credential management layer.
Business flow
Agent types
Agent ID Guard supports two agent types based on their interaction model:
|
Type |
Description |
Access pattern |
|
Autonomous agent |
Operates independently on a preset schedule without user context. Example: an operations agent that periodically restarts services. |
Outbound only |
|
Interactive agent (user-delegated) |
Acts on behalf of a specific user. Requires user authentication before performing tasks such as sending emails or scheduling meetings. |
Inbound and outbound |
Core components
|
Component |
Description |
|
Agent ID |
A unique application identity assigned to each AI agent. Defines the agent's access permissions. Clients must obtain authorization from the Agent ID before accessing agent services. |
|
LLM integration |
Hosts LLM API keys so that developers never access raw credentials directly. The Agent ID retrieves authorized keys through identity authentication at runtime. |
|
Enterprise service (MCP) |
Exposes existing enterprise systems to LLMs through the Model Context Protocol (MCP). Each enterprise service maps to a machine-to-machine (M2M) application with custom resource servers and permissions for secure API exposure. |
|
Client |
The access entry point for interactive agents, such as web or mobile applications. Users authenticate through the client and obtain an access token to invoke agent services. |
|
Credential management service |
A high-availability credential storage system. Encrypts all credentials (API keys, OAuth secrets) with KMS. Only authorized Agent IDs can retrieve credentials, and only as short-lived temporary tokens. |
What to do next
-
Agent ID Guard configuration guide: Step-by-step instructions for registering agents, configuring LLM nodes, and setting up access policies.