Passwords and one-time passcodes (OTPs) are vulnerable to phishing attacks because they rely on information transmitted over the network that attackers can intercept or steal. WebAuthn eliminates this risk by authenticating users locally on their device using biometric data or a hardware security key — no credentials are ever sent over the network.
IDaaS EIAM (Enterprise Identity Access Management) supports WebAuthn for two scenarios: passwordless sign-in and multi-factor authentication (MFA).
How it works
WebAuthn is part of the FIDO2 (Fast Identity Online 2) standard. When a user signs in, the authenticator on their device generates a cryptographic signature using a private key stored locally. IDaaS EIAM verifies the signature using the corresponding public key — no password is transmitted.
Two types of authenticators are supported:
Cross-platform authenticator (also known as roaming authenticator): an external device that works across multiple computers, such as a YubiKey hardware security key.
Platform authenticator: the authenticator built into the device or browser, such as macOS Touch ID or Windows Hello.
WebAuthn is supported by almost all modern browsers. For browser version compatibility details, see Duo Passwordless.
Logon example
Users can sign in by entering only a username — no password required. The following video shows how to register device information for WebAuthn.
Register an authenticator
Before using WebAuthn to sign in, each user must register an authenticator to their account. Registration takes about 1 minute.
Administrators cannot register or manage authenticators on behalf of users. Each user registers and manages their own authenticators independently.
To register an authenticator:
Sign in to IDaaS EIAM and go to the My Account page.
In the Security Information section, find WebAuthn Authenticator and click Manage.
In the Manage WebAuthn Authenticator panel, click Register New Authenticator.
Follow the on-screen prompts to complete registration.
After registration, the authenticator is active and ready to use for sign-in.
Sign-in scenarios
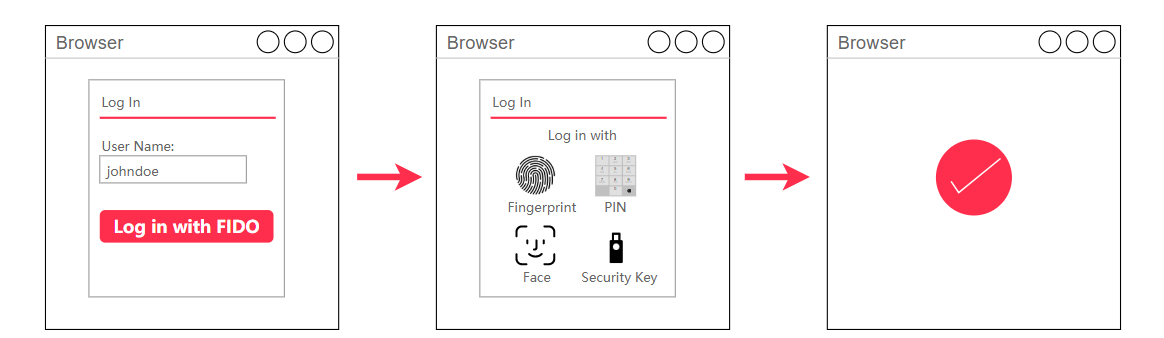
Scenario 1: Passwordless sign-in
Users enter only a username — no password required. IDaaS EIAM then prompts for WebAuthn authentication. This method works with all web applications.
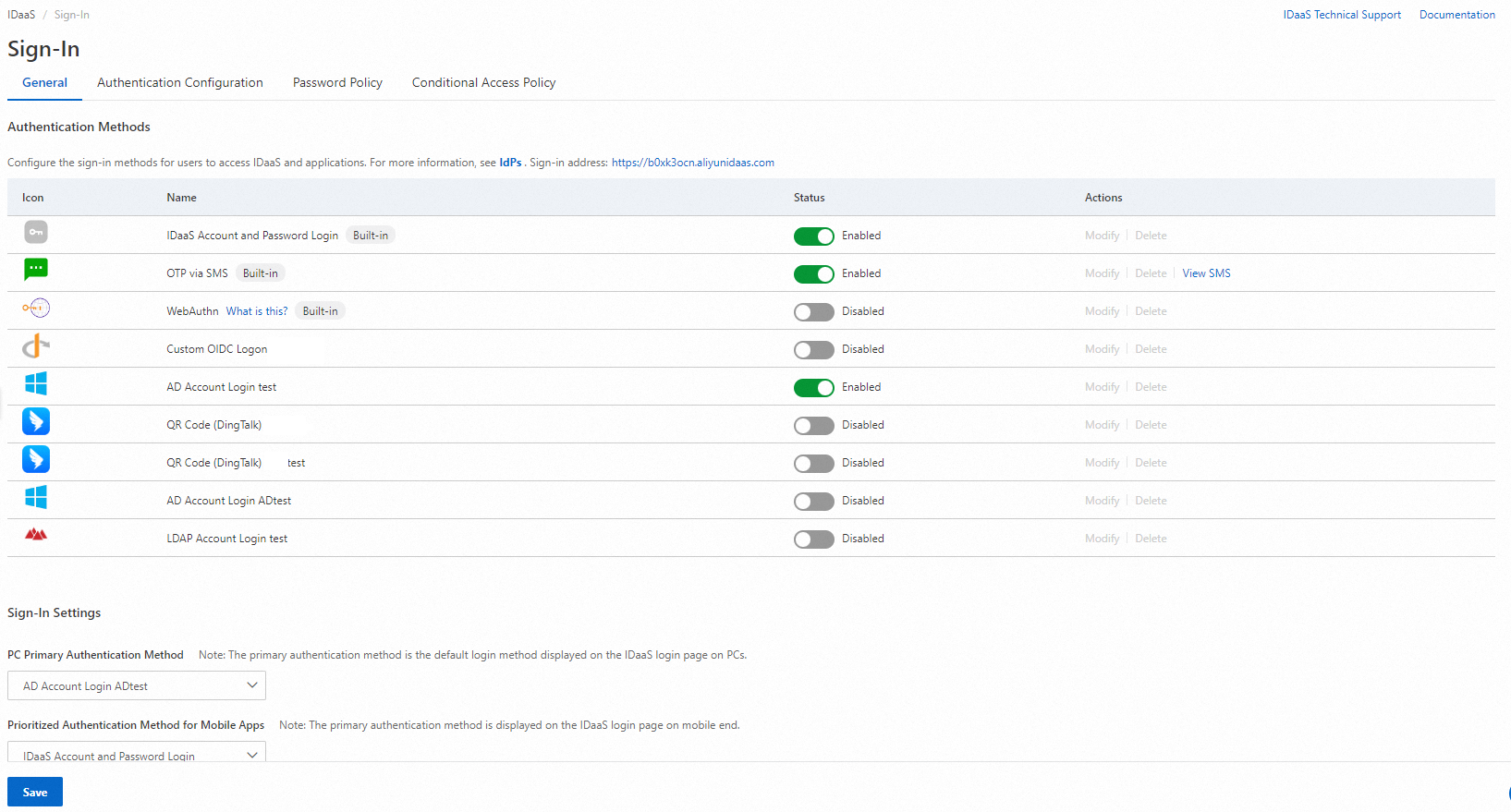
Enable passwordless sign-in:
In the IDaaS EIAM console, go to the Sign-In page and select the General tab.
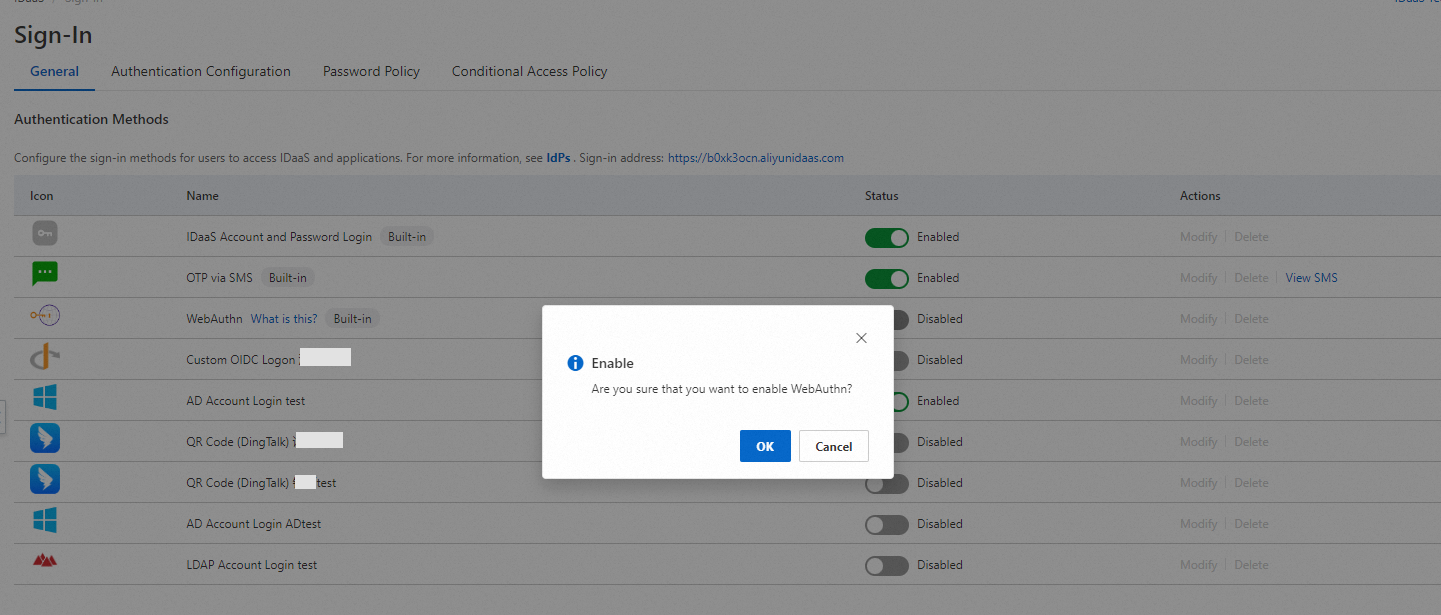
In the Authentication Methods section, find the WebAuthn authenticator method. It is disabled by default.
Enable the method and save.
After enabling, the WebAuthn sign-in option appears on the sign-in page. The following example shows macOS Touch ID being used for passwordless sign-in.
If a user has not registered an authenticator, sign-in fails with an error. Direct the user to register an authenticator first.
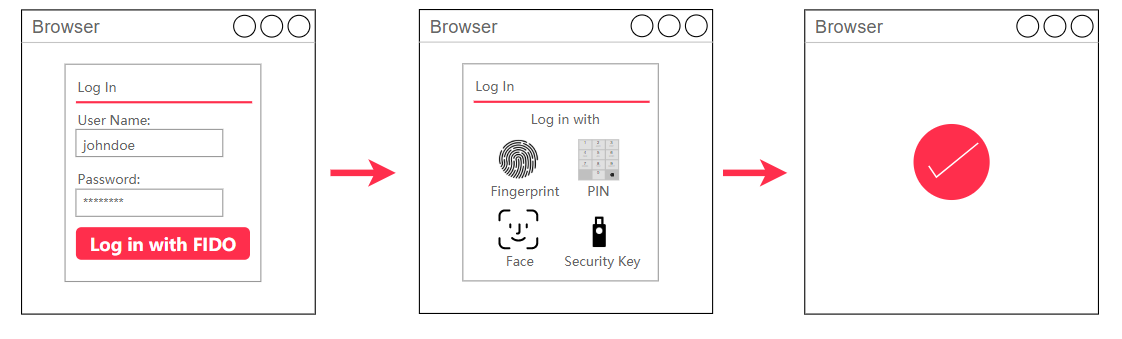
Scenario 2: Multi-factor authentication (MFA)
Users enter their username and password as usual, then verify their identity with WebAuthn as a second factor. This combines password-based and hardware-backed authentication for stronger security.
Enable WebAuthn as an MFA method:
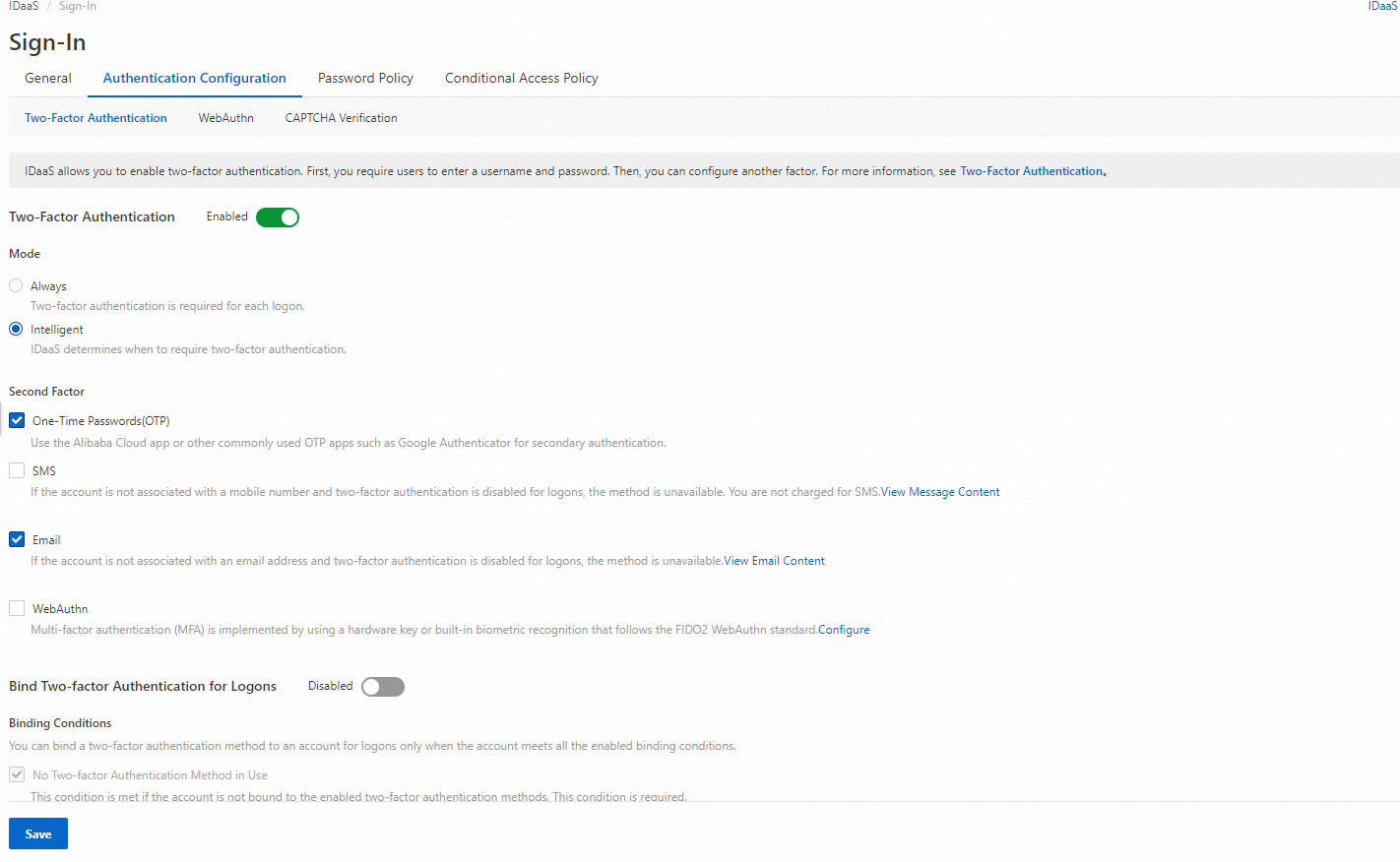
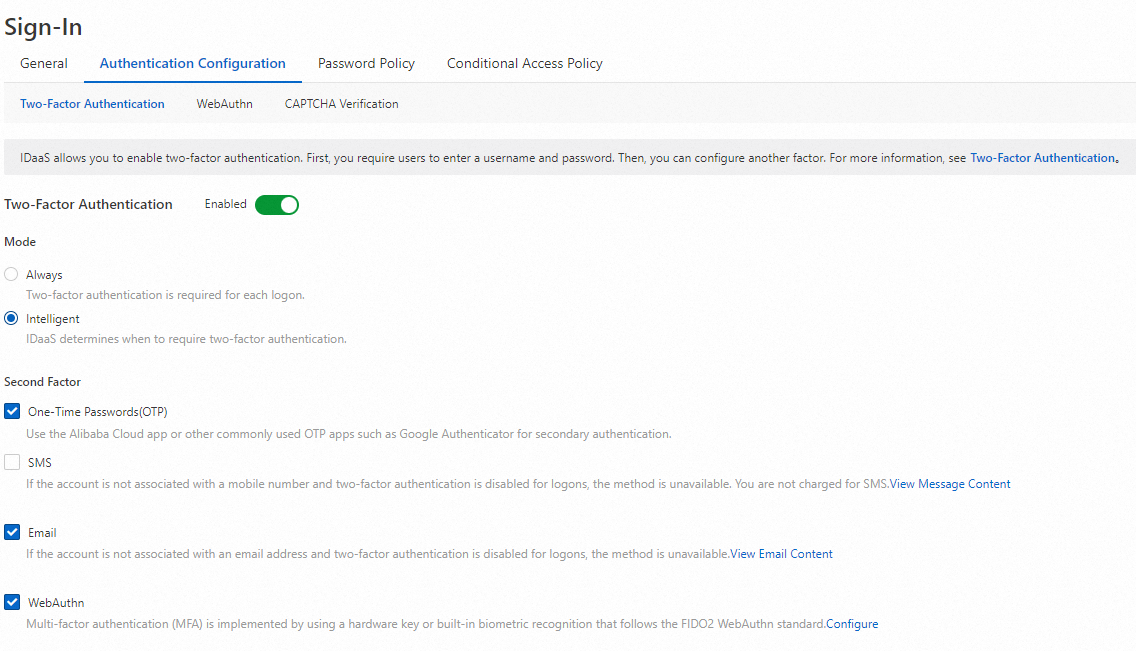
In the IDaaS EIAM console, go to the Sign-In page and select the Authentication Configuration tab.
Click the Two-Factor Authentication tab.
Turn on Two-factor Authentication, select WebAuthn, and click Save.
After saving, users are prompted to complete WebAuthn authentication after entering their username and password. The following example shows macOS Touch ID used for MFA.
Related topics
For more information about WebAuthn, see WebAuthn.
For browser compatibility details, see Duo Passwordless.