When Security Assertion Markup Language (SAML) is used for single sign-on (SSO), IDaaS passes user identity credentials to the application in the NameID field of the SAMLResponse, or in other assertion fields. Configuring an application user means choosing which value IDaaS uses as those credentials.
The most common choices are IDaaS account name and IDaaS email address.
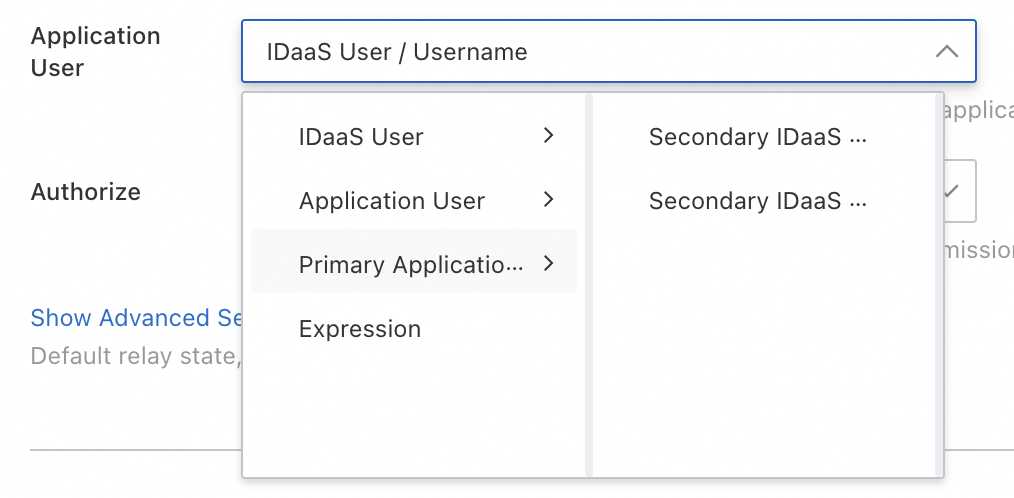
Choose an identity mapping option
IDaaS provides four options. Select the option that matches how usernames are synchronized between IDaaS and your application, and how much per-user control you need.
| Option | How it works | Sub-options | When to use |
|---|---|---|---|
| IDaaS account | Uses the IDaaS account's username or email as identity credentials. No per-user mapping required. | IDaaS account name (Username); IDaaS email address (Email) | Usernames or email addresses are identical in IDaaS and in the application. Recommended for large user bases where per-user mapping is not practical. |
| Application user | An administrator maps each IDaaS account to a specific application account. SSO fails for any account without a mapping. | Application Account | The application uses different identifiers than IDaaS, and the user base is small enough to manage individually. |
| Primary application account | Uses the mapped application account when one exists; falls back to IDaaS credentials when no mapping is configured. | Secondary IDaaS account name (Username); Secondary IDaaS email address (Email) | Most users share identifiers between IDaaS and the application, but a subset require custom mappings. |
| Expression | Derives the identity value from a custom rule—for example, using the prefix of a user's email address as the username. Contact the IDaaS team to configure expressions. | None | The application requires a derived or transformed identifier that none of the above options can produce. |
Configure identity mapping
IDaaS account
Select this option when usernames or email addresses are the same in IDaaS and in the application. IDaaS sends the account's credentials directly—no per-user configuration is needed.
If usernames differ between the two systems, SSO may fail or result in an account mismatch.
Two sub-options are available:
IDaaS account name (Username)
IDaaS email address (Email)
Application user
Select this option when each IDaaS account maps to a different account in the application. An administrator must configure the mapping for every user before they can complete SSO. For example, if the test_user account exists in IDaaS and you want to log on to the application as administrator, you can configure the application user.
If a mapping is missing for a user, that user cannot complete SSO.
One sub-option is available:
Application Account
To add application users, see Add an application user.
Primary application account
Select this option when most users have matching identifiers in IDaaS and the application, but some require a custom mapping. IDaaS uses the configured application account when one exists, and falls back to the IDaaS identity credentials when no mapping is set.
Two sub-options are available:
Secondary IDaaS account name (Username)
Secondary IDaaS email address (Email)
To add application users, see Add an application user.
Expression
Select this option when the application requires a derived identifier—for example, using the prefix of a user's email address as the username. Expressions have no sub-options.
Contact the IDaaS team to configure an expression rule.
Add an application user
This section applies when you select Application User or Primary Application User from the Application User drop-down list on the SSO tab.
Click the Application Account tab, then click Add Application Account.
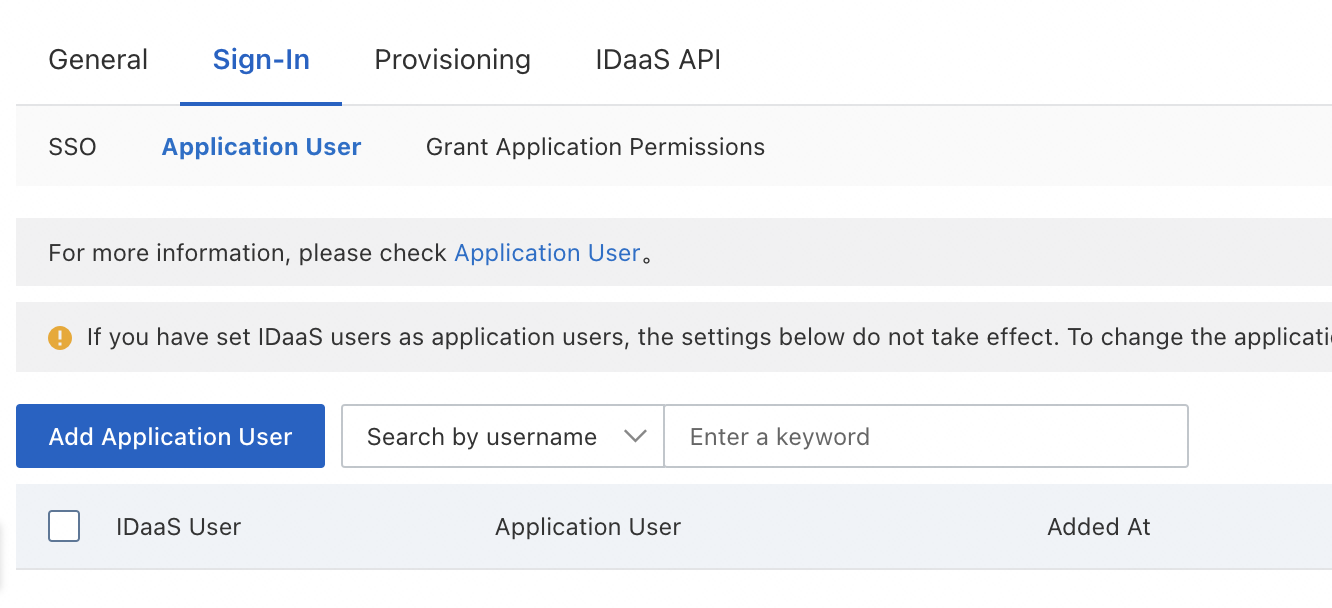
Search for an IDaaS account by entering a keyword such as a username (for example, admin, root, or Jerry), or a mobile number. Click the account in the search results.
Enter the application account to associate with that IDaaS account.
Click Save.
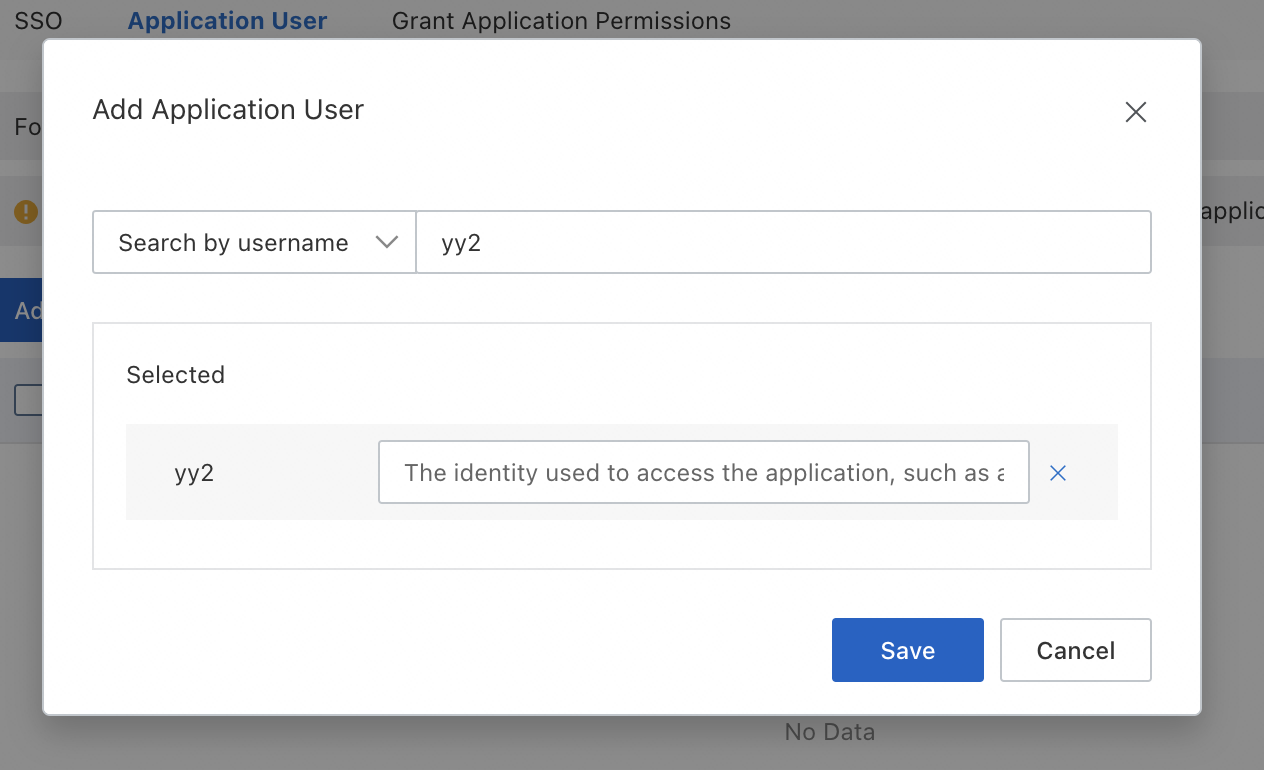
An IDaaS account can have multiple application accounts. When the user initiates an SSO request, they can select which application account to use.