Alibaba Cloud IDaaS is an identity product from the Alibaba Cloud security team. It ships with strong security controls already enabled. You don't need to configure protection from scratch — the five measures below are active the moment you create an instance.
What's enabled by default:
Two-factor authentication (2FA) for all end users, with intelligent mode to reduce unnecessary prompts
Risk control for high-impact administrator operations
Manual authorization required for every application
High-complexity password policy
Request signature and data encryption for cross-origin and synchronization scenarios
Note: When availability and security conflict, IDaaS prioritizes security. The default configurations aim for maximum out-of-the-box protection, but cannot guarantee compliance with every industry-specific standard.
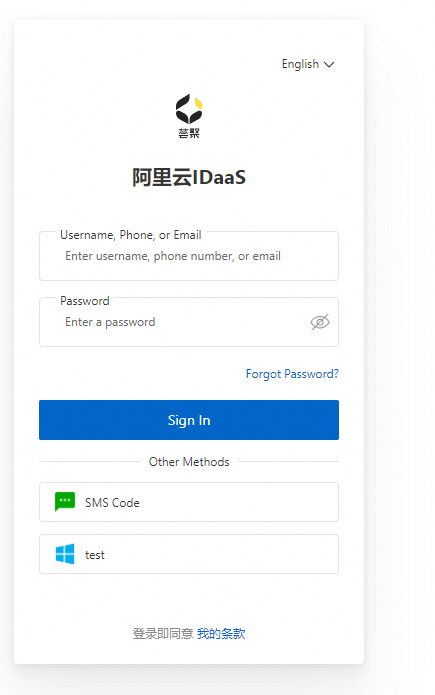
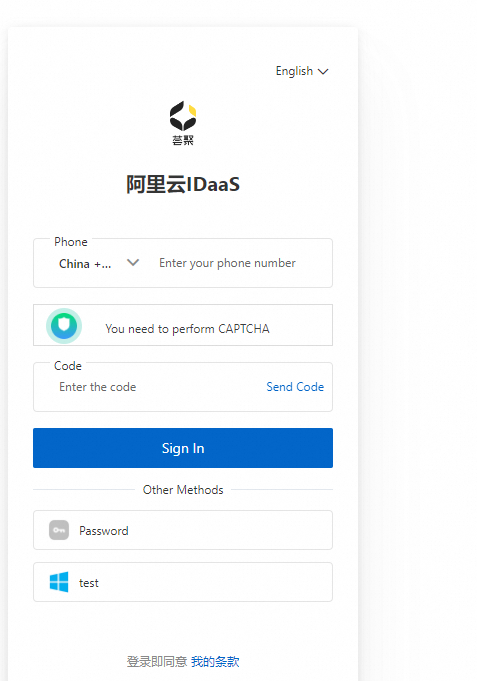
Two-factor authentication
Two-factor authentication (2FA) is enabled by default for all IDaaS instances. After signing in with a password, users must complete a second verification step via SMS or email before accessing any application.
Because all applications connect to IDaaS through single sign-on (SSO), enabling 2FA once protects every connected application automatically.
Intelligent mode
Requiring 2FA on every sign-in can be disruptive for users who work from a consistent environment. Intelligent mode — also enabled by default — evaluates the current device, access environment, and account status to determine whether 2FA is needed for a given session.
When nothing about the context looks suspicious, users can go days without being prompted, with no reduction in security posture.
Risk control for administrator operations
Administrator accounts carry far greater permissions than regular user accounts. A compromised administrator account can cause serious damage, so IDaaS applies Alibaba Cloud's risk control system to key management operations.
When an operation's risk level exceeds a threshold, IDaaS triggers a verification step requiring 2FA with the mobile phone number attached to the Alibaba Cloud account. For sensitive operations performed by a sub-administrator, the owner must also confirm the action.
The following operations are covered by default (10+ total):
Delete an instance
Delete accounts in batches
Delete an application
Key rotation
Manual application authorization
When you connect an application to IDaaS for SSO, no one — including administrators — can access it until an admin explicitly defines the authorization scope. This default enforces the principle of least privilege and prevents unintended access proliferation as you add more applications over time.
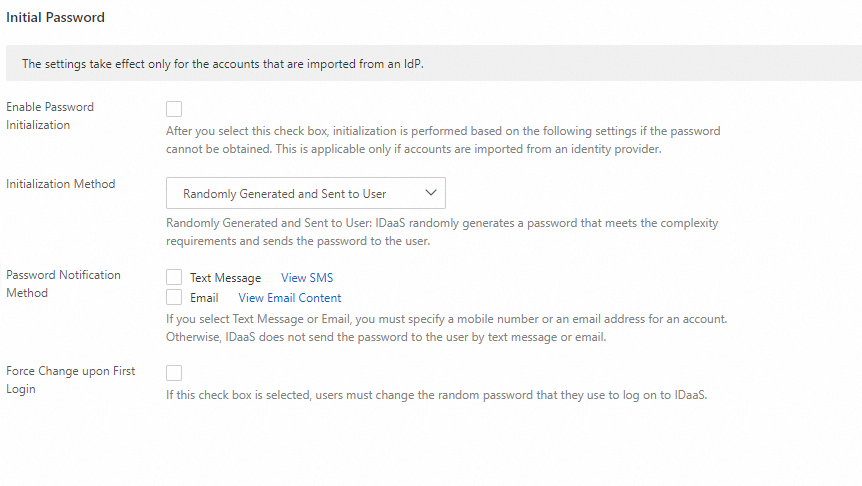
Password policy
IDaaS supports password-based sign-in by default and ships with a high-complexity password policy. The default requirements are:
Must contain an uppercase letter
Must contain a lowercase letter
Must contain a number
Must contain a special character
Cannot contain the account name
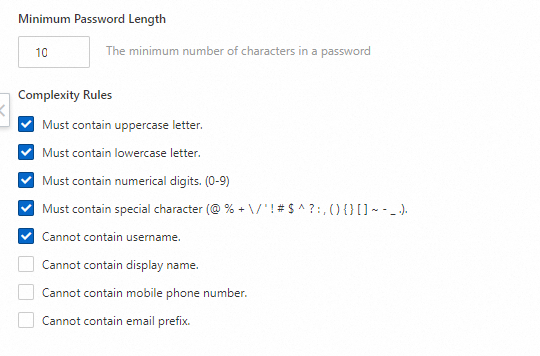
Adjust the policy at any time to balance security requirements with your organization's usability needs.
Request signature and data encryption
HTTPS secures data in transit but cannot guarantee end-to-end integrity at the application layer. IDaaS adds two protection layers on top of HTTPS for cross-origin requests and account synchronization scenarios. Both are enabled by default.
Signature layer: When a cross-origin request is made, the request content is signed with a private key. The receiver verifies the signature using the corresponding public key, confirming the content was not tampered with in transit. This applies to some SSO scenarios and outbound account synchronization.
Encryption layer: Synchronized data is encrypted end-to-end before leaving IDaaS. By default, password information is not synchronized, which helps prevent information leakage from misconfiguration or accidental exposure. Future releases will add full-process encryption for SAML SSO, extending this protection to meet high-security requirements in finance and government sectors.