Use LindormTable's cluster management system to create users, manage their passwords, and control what data they can access.
Prerequisites
Before you begin, ensure that you have:
-
Access to the cluster management system of your Lindorm instance. For more information, see Log on to the cluster management system.
Create a user
-
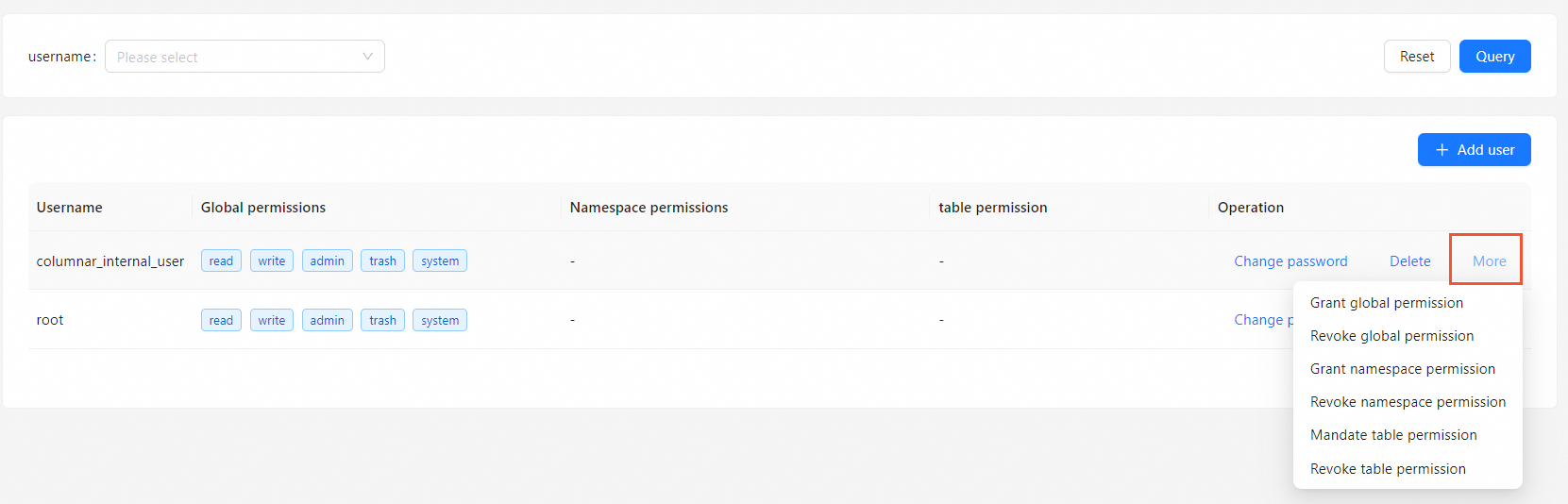
In the left-side navigation pane, choose Data Manager > User Manager.
-
Click + Add user on the right side of the page.
-
In the Add user dialog box, enter a Username and Password.
-
Click OK.
After the user is created, the password is no longer visible in the system. If you forget it, change the password. New users have no permissions by default — grant permissions after creating the account.
Delete a user
-
Find the user you want to delete and click Delete in the Operation column.
-
Click OK.
Change a password
-
In the Operation column for the user, click Change password.
-
In the Change password dialog box, enter a New password.
-
Click OK.
Permission management
Grant permissions to or revoke permissions from a user directly in the cluster management system.
Permission levels
Three permission levels control access to Lindorm resources, from broadest to narrowest: Global, Database (Namespace), and Table. A higher level includes all permissions of the levels below it.
For example, if User 1 is granted the global read and write permissions, User 1 has the read and write permissions on wide tables in all databases in a Lindorm cluster. If User 2 is granted the read and write permissions on Database 1, User 2 has the read and write permissions on all tables in Database 1, including newly created tables in Database 1.
Permissions
The following permissions control what operations a user can perform:
| Permission | Operations | Syntax |
|---|---|---|
| WRITE | Write data to tables | PUT, BATCH, DELETE, INCREMENT, APPEND, and CHECKANDMUTATE |
| READ | Read data from tables; read table descriptor and namespace information | GET, SCAN, and EXIST; GETTABLEDESCRIPTOR, LISTTABLES, and LISTNAMESPACEDESCRIPTORS |
| ADMIN | Data Definition Language (DDL) operations (excluding deleting tables or table data); namespace DDL operations | CREATETABLE, ENABLETABLE, and DISABLETABLE; CREATENAMESPACE |
| TRASH | Operations that prevent accidental deletion of tables or table data | TRUNCATETABLE and DELETETABLE |
| SYSTEM | O&M operations; data migration and synchronization using LTS | COMPACT and FLUSH |
Grant and revoke permissions
-
In the Operation column for the user, click More.
-
From the drop-down list, select the operation:
-
Grant permissions: grant Global, namespace, or table permission to the user.
-
Revoke permissions: revoke Global, namespace, or table permission from the user.
-
-
In the dialog box, select or deselect the permissions and the related scope information.
-
Click OK.