If you have your own authentication server, you can configure remote authentication to forward user requests to your specified authentication server for validation.
Feature overview
Remote authentication is similar to URL signing. Both are used to protect resources from unauthorized access. Only authorized users can retrieve resources from POPs. Differences between URL signing and remote authentication:
URL signing: After you apply authentication rules that are created for a domain name to POPs, the POPs complete the authentication process.
Remote authentication: You can specify a self-managed authentication server. After POPs receive client requests, the requests are redirected to the specified authentication server.
The following figure shows how remote authentication works.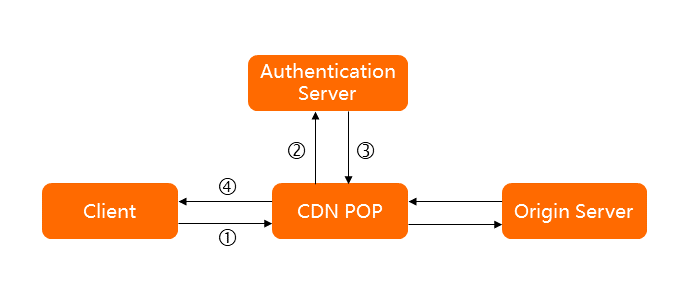
No. | Description |
1 | A client sends a request to a POP. The request carries parameters that are used for authentication. Examples:
|
2 | The POP receives the request, and then redirects the request to the authentication server. You can specify whether the request is processed by the POP before the request is redirected to the authentication server. Examples:
|
3 | The authentication server checks the parameters in the request, and then returns the authentication result to the POP. |
4 | The POP performs the corresponding action based on the authentication result, and then returns data to the client. Examples:
|
Usage notes
After you configure remote authentication, requests that fail the authentication can still reach POPs. However, POPs reject the requests and return an HTTP 403 status code. The requests are recorded in DCDN logs.
In remote authentication, user requests are forwarded to the specified authentication server, and the authentication server verifies the user requests. You are charged for data transfer that is generated when POPs block malicious requests. If clients request resources over HTTPS, you are also charged for HTTPS requests.
Procedure
Log on to the DCDN console.
In the left-side navigation pane, click Domain Names.
On the Domain Names page, find the domain name that you want to manage and click Configure.
In the left-side navigation tree of the domain name, click Access Control.
Click the Remote Authentication tab.
Click OK.
After remote authentication is configured, you can modify the settings of remote authentication or disable remote authentication on the Remote Authentication tab.
Variables
When you add custom parameters, you can select the variables that are provided by CDN. The following table describes the variables.
Variable | Description |
$http_host | The value of the Host header. |
$http_user_agent | The value of the User-Agent header. |
$http_referer | The value of the Referer header. |
$http_content_type | The value of the Content-Type header. |
$http_x_forward_for | The value of the X-Forwarded-For header. |
$remote_addr | The client IP address. |
$scheme | The protocol of the request. |
$server_protocol | The protocol version of the request. |
$uri | The original URI of the request. |
$args | The query string of the request URL. The query string does not include the question mark (?). |
$request_method | The request method. |
$request_uri | The content of uri+'?'+args. |